漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2014-064680
漏洞标题:江苏省某高校科研项目管理系统存在SQL注入漏洞
相关厂商:江苏省教育厅
漏洞作者: 超耐蘑
提交时间:2014-06-12 18:04
修复时间:2014-07-27 18:06
公开时间:2014-07-27 18:06
漏洞类型:SQL注射漏洞
危害等级:中
自评Rank:10
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2014-06-12: 细节已通知厂商并且等待厂商处理中
2014-06-16: 厂商已经确认,细节仅向厂商公开
2014-06-26: 细节向核心白帽子及相关领域专家公开
2014-07-06: 细节向普通白帽子公开
2014-07-16: 细节向实习白帽子公开
2014-07-27: 细节向公众公开
简要描述:
江苏省某高校科研项目管理系统存在SQL注入漏洞
详细说明:
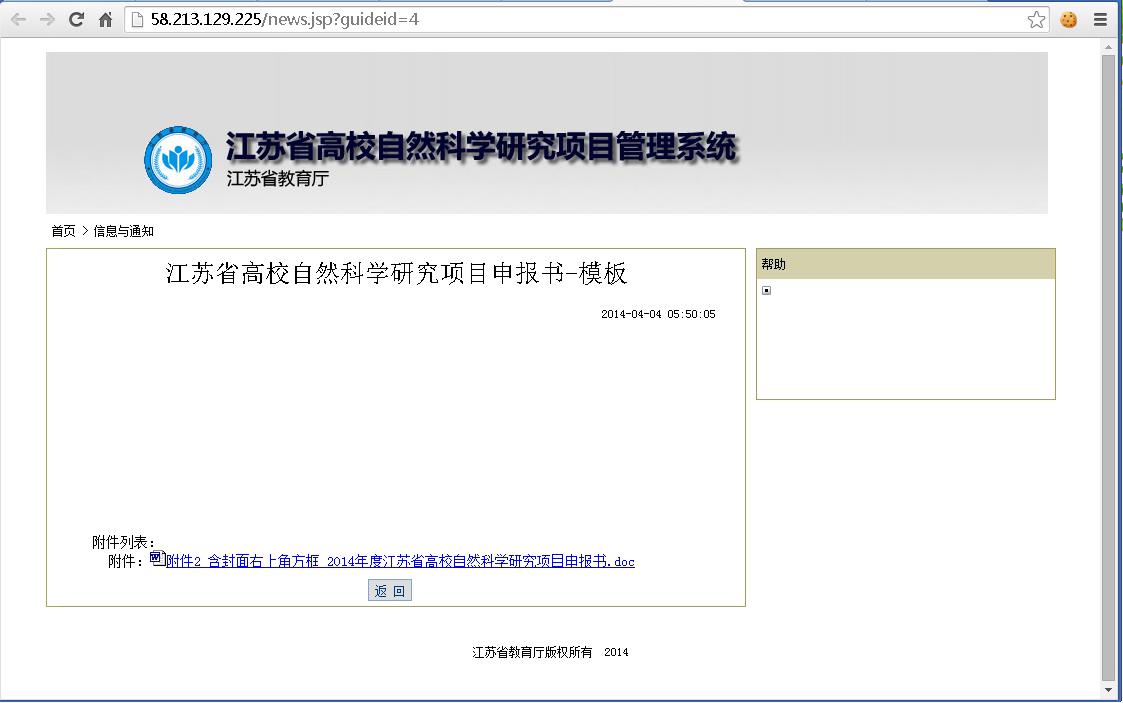
江苏省高校自然科学研究项目管理系统存在SQL注入漏洞
管理系统网址为:http://58.213.129.225/index.jsp
随便点击一个登陆界面滚动的公告,URL为:http://58.213.129.225/news.jsp?guideid=4
看到了数字就习惯性地测试了下,貌似存在sql注入
放到sqlmap里跑了下,果然跑出了数据
漏洞证明:
修复方案:
你们懂得哦
版权声明:转载请注明来源 超耐蘑@乌云
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:10
确认时间:2014-06-16 23:08
厂商回复:
CNVD确认并复现所述情况,已经转由CNCERT下发给江苏分中心处置。
最新状态:
暂无