新浪微博新注册用户的引导上传用户头像的接口没有防御csrf,通常的用户上传文件是需要交互,利用难度较大.不过html5有一个新特性[CORS](http://www.w3.org/TR/cors),可以实现无交互的上传文件.
存在csrf的地方:
话说有个疑问,为什么我的cookie里会有www.wooyun.org这个字段?????
这个地方的post请求既没有token,也没对refer进行验证.
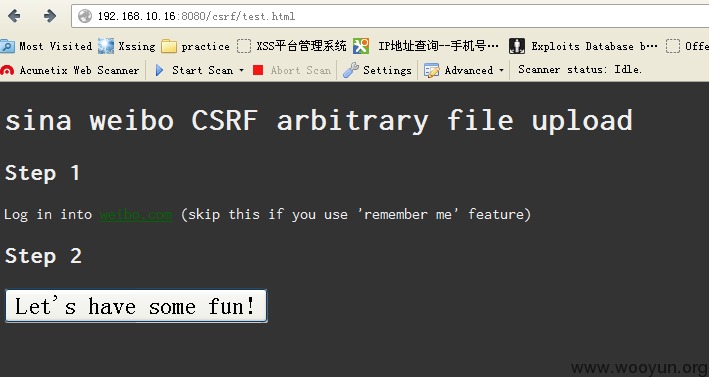
所以构造如下poc
测试浏览器:firefox24.0
当前用户的头像为:

访问poc
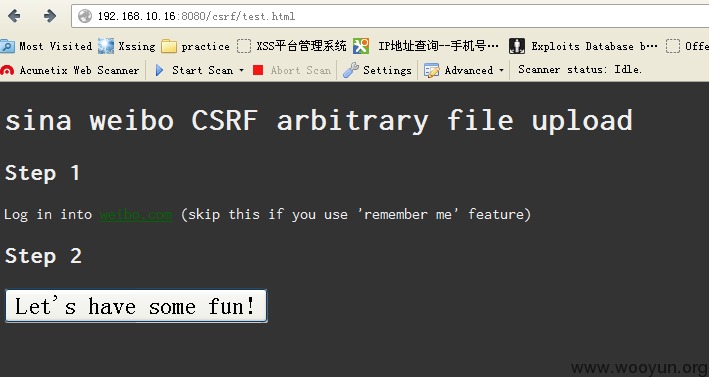
点击havefun。当然,js是可以自动提交的。这里仅仅是演示。
查看头像已经被修改了