漏洞概要
关注数(24)
关注此漏洞
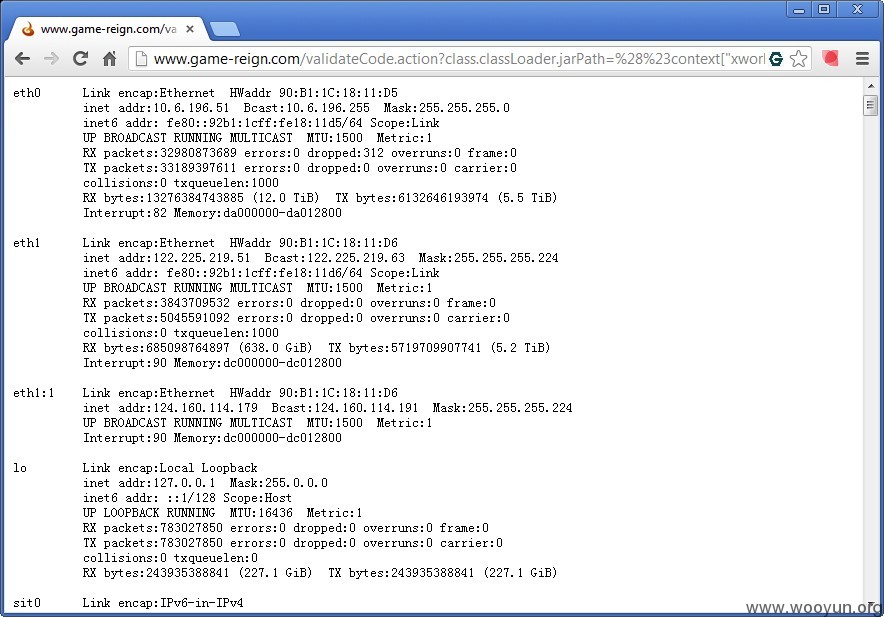
漏洞标题:瑞战公司门户网站 命令执行漏洞
提交时间:2013-07-15 18:20
修复时间:2013-08-29 18:20
公开时间:2013-08-29 18:20
漏洞类型:命令执行
危害等级:高
自评Rank:20
漏洞状态:厂商已经确认
Tags标签:
无
漏洞详情
披露状态:
2013-07-15: 细节已通知厂商并且等待厂商处理中
2013-07-15: 厂商已经确认,细节仅向厂商公开
2013-07-25: 细节向核心白帽子及相关领域专家公开
2013-08-04: 细节向普通白帽子公开
2013-08-14: 细节向实习白帽子公开
2013-08-29: 细节向公众公开
简要描述:
测试发现你们的游戏管理后台也使用了第三方框架,还说准备迟一点报告的;
结果被你们修复了,加油,别忘记了修复这个,隐藏得还是有点深的。
详细说明:
~ 修复速度很快,赞一个!
# 傲视天地GM管理后台
http://gc.astd.cn/AstdGateway/validateCode.action?_dc=1373816329043
# 征战四方GM管理后台
http://gc.zzsf.com/ZzGateway/login.action?login_error=1
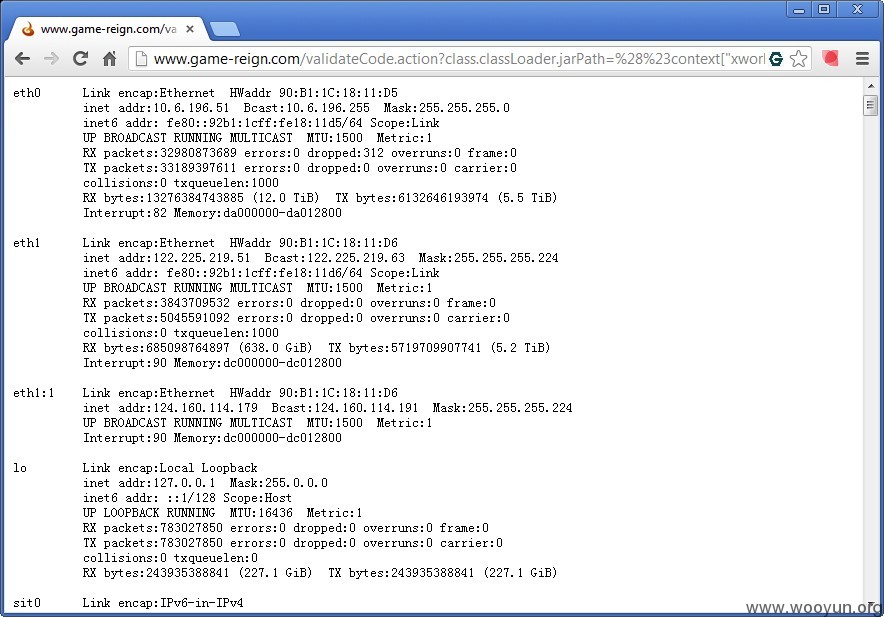
漏洞证明:
修复方案:
版权声明:转载请注明来源 猪猪侠@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:15
确认时间:2013-07-15 18:31
厂商回复:
谢谢猪猪侠!!
最新状态:
暂无