漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2016-0210113
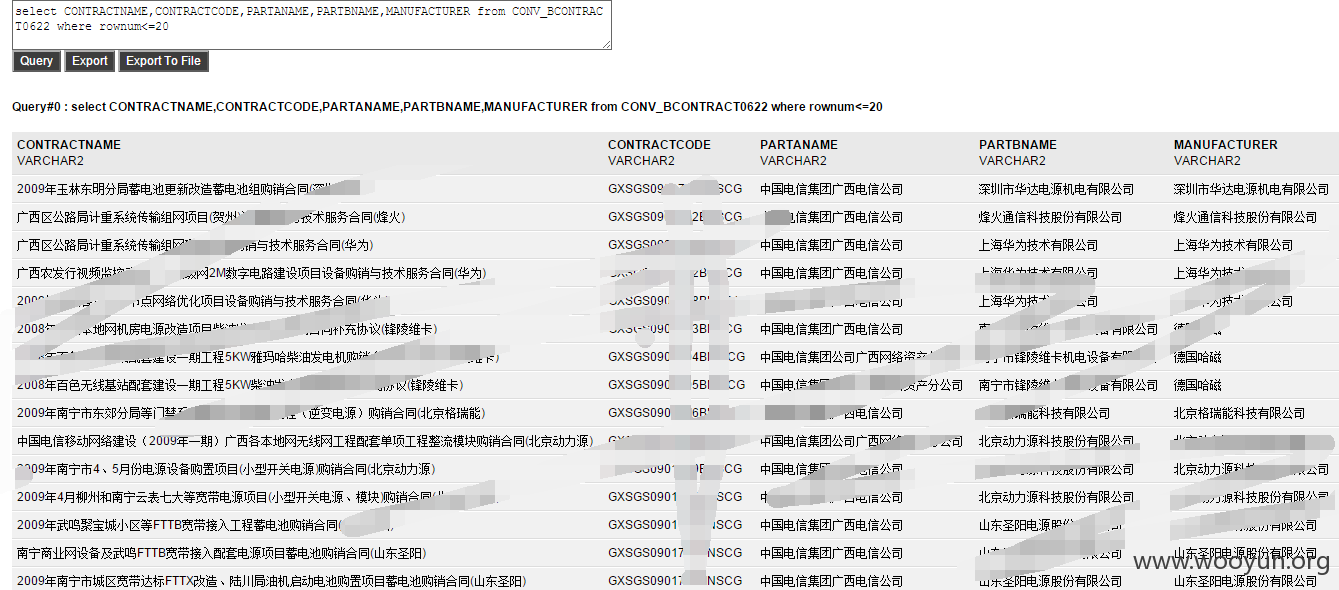
漏洞标题:中国电信海外某平台GetShell涉及大量企业客户合同信息/合作伙伴信息
相关厂商:中国电信
漏洞作者: 路人甲
提交时间:2016-05-18 18:00
修复时间:2016-07-04 10:10
公开时间:2016-07-04 10:10
漏洞类型:系统/服务补丁不及时
危害等级:高
自评Rank:12
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2016-05-18: 细节已通知厂商并且等待厂商处理中
2016-05-20: 厂商已经确认,细节仅向厂商公开
2016-05-30: 细节向核心白帽子及相关领域专家公开
2016-06-09: 细节向普通白帽子公开
2016-06-19: 细节向实习白帽子公开
2016-07-04: 细节向公众公开
简要描述:
...
详细说明:
反序列getshell
*****ls_intern*****
mima:
*****m*****
jdbc:
<url>jdbc:oracle:thin:@**.**.**.**:1523:hwcpmis1</url>
<driver-name>oracle.jdbc.OracleDriver</driver-name>
<properties>
<property>
<name>user</name>
<value>project_am</value>
</property>
</properties>
<password-encrypted>{AES}H1V2VRHSMsN7BIfHhTkPlcn71gXeD3I5co5wnLZ2RKEqzOtbPvzew49iQVrzPlrN</password-encrypted>BSENDMAILGJLOG 3165043
CM_TMS_VOUCHER_DETAIL_C_CPMIS 654249
SEDITITEM 124652
CONV_BCONTRACT0622 123952
SLOGINTIMES 86932
CONV_CONTRACT_NEW_OLD 78389
SFLOWTRANUSER 44940
SUSERDEPTLOG 44566
CR020_02_BF430 43164
SOPERLOG 38765
CONV_CONTRACT_ID 31765
SECU_USER 27254
SNEXTFLOW 27052
CONV_BCONTRACT_OVERBAK 25483
CONV_BCONTRACT_BAK 24104
BFLOW 21036
CONV_BCONTRACT_RELATETRADE01 20745
CONV_BCONTRACT_RELATETRADE 20745
CONV_BCONTRACT1 20112
SUSER1 15926
SOAUSER 14878
SOAUSERDEPT 14840
SUSERDEPT1 14671
SUSER_RIGHT 14265
SFLOW_20100819 12547
CFLOW_20100819 11370
SDEPTLOG 11301
SCOND 10845
BFILE 8608
BSERVERLOG 8098
SHARDPARSE 7080
CPURCONTRACTSORT 6177
BCONTRACTTRACK 5954
CR020_02_BF 5905
BTESTFORMSS 5627
SJOBCOSTRELATION 4627
CWX_ROLEUSER 4522
SMSOURCE_CPMIS 4039
BCURRFLOW 3719
CR020_BF 3441
BORDERUSER 3045
BCONTRACTPAY 3029
SFIELD 2806
CONV_BCONTRACT_0602 2788
BFIXASSET 2696
CR020_03_BF 2635
SMATERIALMAN 2263
BCONTRACTPARTB 2210
BHROAUSER 2084
漏洞证明:
BSENDMAILGJLOG 3165043
CM_TMS_VOUCHER_DETAIL_C_CPMIS 654249
SEDITITEM 124652
CONV_BCONTRACT0622 123952
SLOGINTIMES 86932
CONV_CONTRACT_NEW_OLD 78389
SFLOWTRANUSER 44940
SUSERDEPTLOG 44566
CR020_02_BF430 43164
SOPERLOG 38765
CONV_CONTRACT_ID 31765
SECU_USER 27254
SNEXTFLOW 27052
CONV_BCONTRACT_OVERBAK 25483
CONV_BCONTRACT_BAK 24104
BFLOW 21036
CONV_BCONTRACT_RELATETRADE01 20745
CONV_BCONTRACT_RELATETRADE 20745
CONV_BCONTRACT1 20112
SUSER1 15926
SOAUSER 14878
SOAUSERDEPT 14840
SUSERDEPT1 14671
SUSER_RIGHT 14265
SFLOW_20100819 12547
CFLOW_20100819 11370
SDEPTLOG 11301
SCOND 10845
BFILE 8608
BSERVERLOG 8098
SHARDPARSE 7080
CPURCONTRACTSORT 6177
BCONTRACTTRACK 5954
CR020_02_BF 5905
BTESTFORMSS 5627
SJOBCOSTRELATION 4627
CWX_ROLEUSER 4522
SMSOURCE_CPMIS 4039
BCURRFLOW 3719
CR020_BF 3441
BORDERUSER 3045
BCONTRACTPAY 3029
SFIELD 2806
CONV_BCONTRACT_0602 2788
BFIXASSET 2696
CR020_03_BF 2635
SMATERIALMAN 2263
BCONTRACTPARTB 2210
BHROAUSER 2084
修复方案:
更新补丁
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:11
确认时间:2016-05-20 10:01
厂商回复:
CNVD确认所述情况,已经转由CNCERT向中国电信集团公司通报,由其后续协调网站管理部门处置.
最新状态:
暂无