与: WooYun: CmsEasy最新版本无限制SQL注射 重复
CmsEasy_5.5_UTF-8_20140420
官方最新包
文件/lib/default/union_act.php
此文件存在多处SQL注入
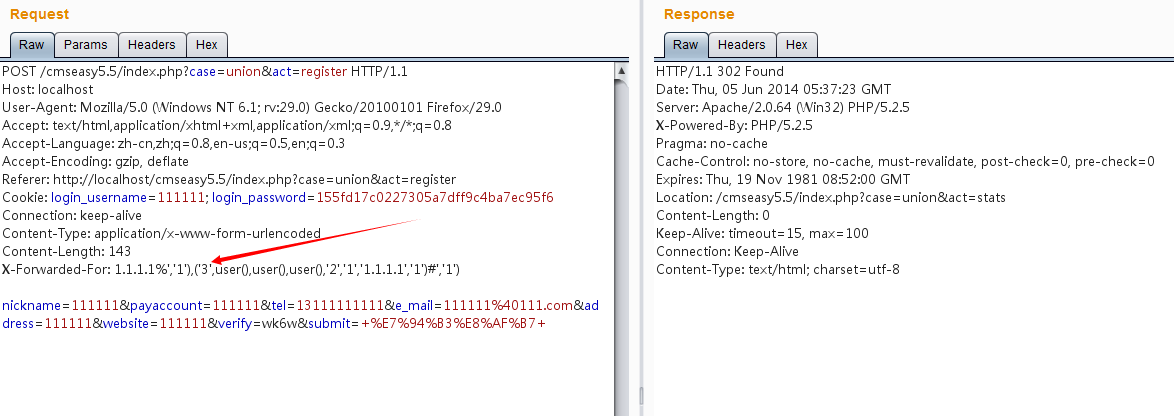
第一处SQL注入,在联盟注册处:
http://localhost/cmseasy5.5/index.php?case=union&act=register
$unionarr['regip'] = front::ip();
我们来看看这里的ip()函数:
这里的正则存在问题,最后一句的(%.+),这里我们在IP后面加上%,然后就能跟上任意内容
那么我们使用1.1.1.1%xxx就能绕过正则进行注入了。
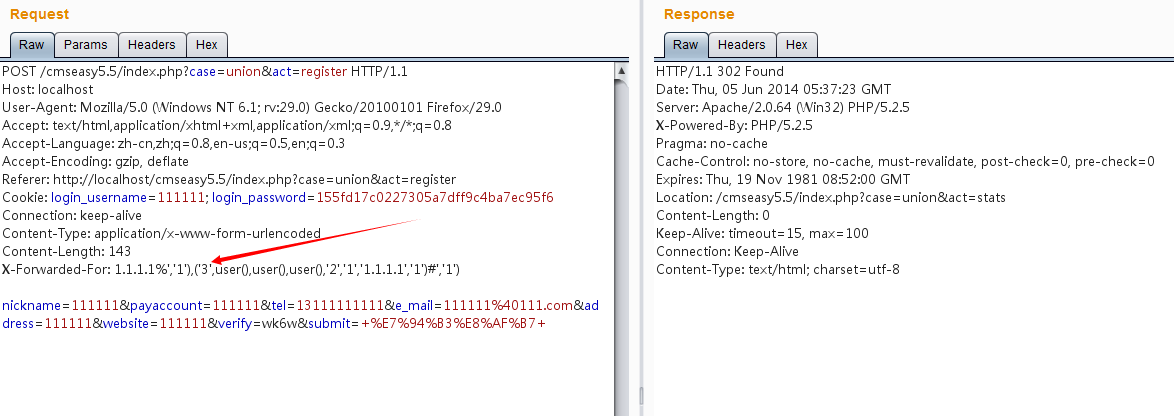
第二处SQL注入:
$useridarr['visitip'] = front::ip();
第一步:
首先注册两个用户111111,222222
他们的userid分别为2,3(因为admin占了一个id)
第二步:
登陆用户111111
然后注册联盟

第三步
抓包,修改头信息,添加:
第四步
登陆用户222222,然后进入会员中心,联盟推广,修改资料

注入内容显示在支付账户和网站地址处