漏洞概要
关注数(24)
关注此漏洞
漏洞标题:万达某产品公众管理平台Getshell至站点沦陷
提交时间:2014-01-04 14:13
修复时间:2014-02-18 14:14
公开时间:2014-02-18 14:14
漏洞类型:后台弱口令
危害等级:高
自评Rank:12
漏洞状态:厂商已经确认
Tags标签:
无
漏洞详情
披露状态:
2014-01-04: 细节已通知厂商并且等待厂商处理中
2014-01-04: 厂商已经确认,细节仅向厂商公开
2014-01-14: 细节向核心白帽子及相关领域专家公开
2014-01-24: 细节向普通白帽子公开
2014-02-03: 细节向实习白帽子公开
2014-02-18: 细节向公众公开
简要描述:
年关将至,普天同庆,众基友相约婚守,两声漫漫~
详细说明:
由于验证码缺陷可爆破进入系统admin管理员用户,此处不表

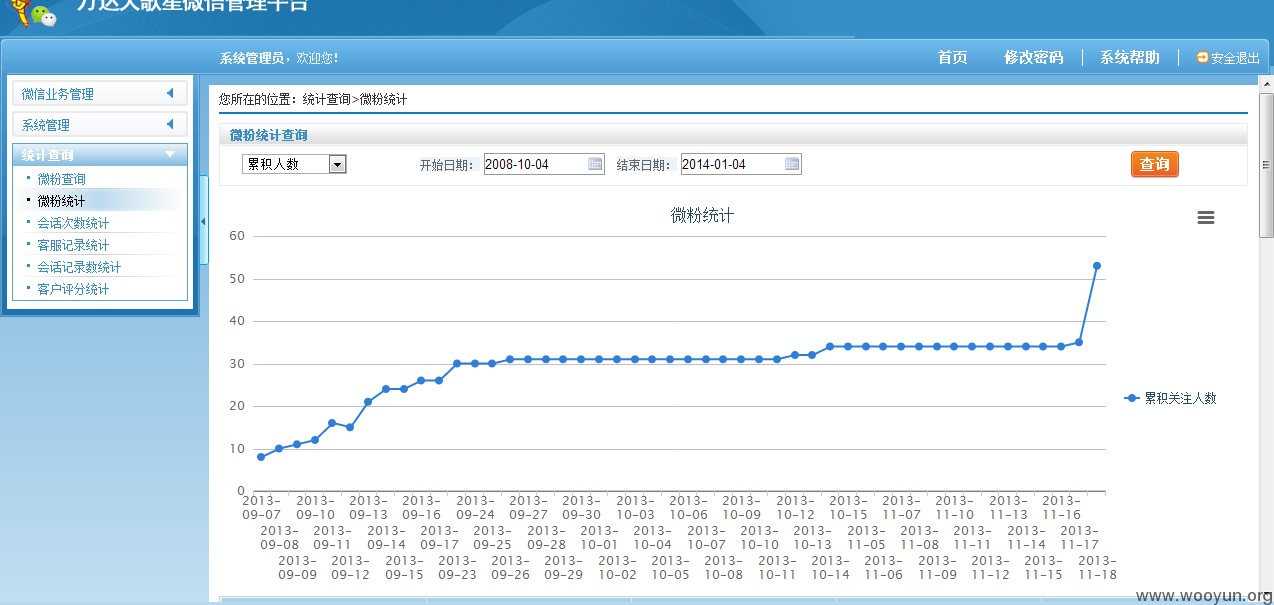
微信管理平台嘛就有管理功能,稍微贴两张图

菜单管理

粉丝统计
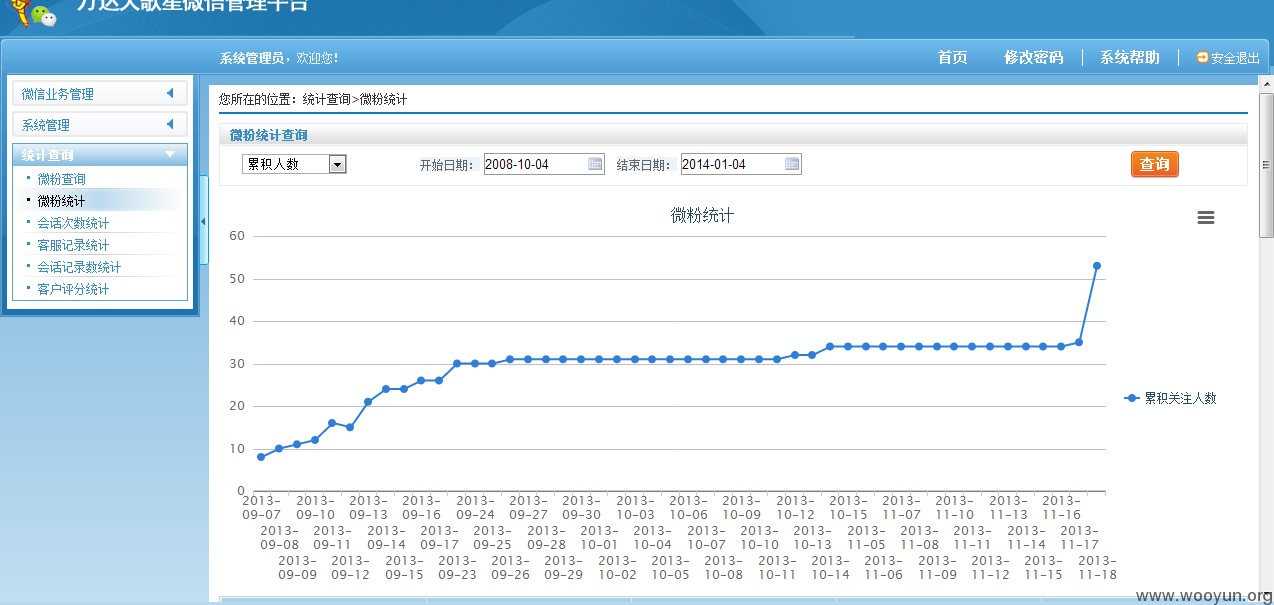
可帮忙运营旗下微信账号呢,设置业务互动流程环节内容!数据未动哦
漏洞证明:
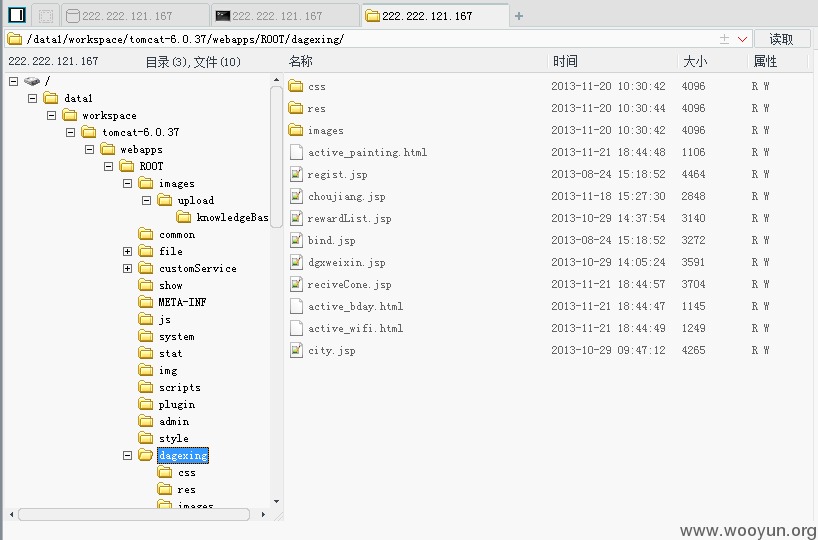
任意文件上传getshell
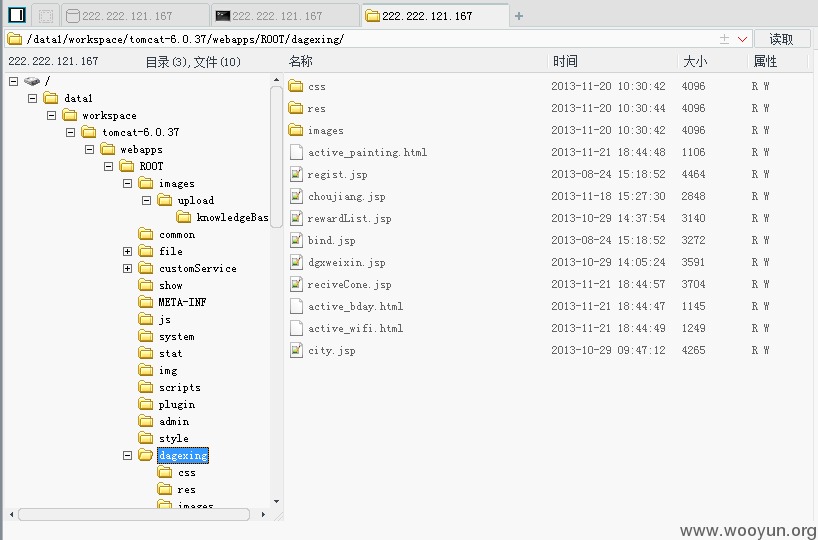
大歌星就在里面呀
命令执行
内往外iP
修复方案:
版权声明:转载请注明来源 zzR@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:12
确认时间:2014-01-04 19:32
厂商回复:
感谢zzR同学的关注与贡献!此洞目测存在,马上整改!
最新状态:
暂无