漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2016-0214612
漏洞标题:中国移动某运维系统GetShell影响千万数据/200W家庭宽带用户
相关厂商:中国移动
漏洞作者: 路人甲
提交时间:2016-05-31 11:22
修复时间:2016-07-17 16:30
公开时间:2016-07-17 16:30
漏洞类型:系统/服务补丁不及时
危害等级:高
自评Rank:15
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2016-05-31: 细节已通知厂商并且等待厂商处理中
2016-06-02: 厂商已经确认,细节仅向厂商公开
2016-06-12: 细节向核心白帽子及相关领域专家公开
2016-06-22: 细节向普通白帽子公开
2016-07-02: 细节向实习白帽子公开
2016-07-17: 细节向公众公开
简要描述:
2016-5-30
详细说明:
反序列getshell
1.://**.**.**/bea_wls_internal/1.jsp
pass:
*****og*****
jdbc:
jdbc.url=jdbc:oracle:thin:@(DESCRIPTION =(ADDRESS = (PROTOCOL = TCP)(HOST = **.**.**.**)(PORT = 1521))(ADDRESS = (PROTOCOL = TCP)(HOST = **.**.**.**)(PORT = 1521))(LOAD_BALANCE = yes)(FAILOVER = ON)(CONNECT_DATA =(SERVER = DEDICATED)(SERVICE_NAME = ZHDW)(FAILOVER_MODE=(TYPE = SELECT)(METHOD = BASIC)(RETIRES = 20)(DELAY = 15))))
jdb.url.prox=(DESCRIPTION =(ADDRESS = (PROTOCOL = TCP)(HOST = **.**.**.**)(PORT = 1521))(ADDRESS = (PROTOCOL = TCP)(HOST = **.**.**.**)(PORT = 1521))(LOAD_BALANCE = yes)(FAILOVER = ON)(CONNECT_DATA =(SERVER = DEDICATED)(SERVICE_NAME = ZHDW)(FAILOVER_MODE=(TYPE = SELECT)(METHOD = BASIC)(RETIRES = 20)(DELAY = 15))))
jdbc.username=zsyw
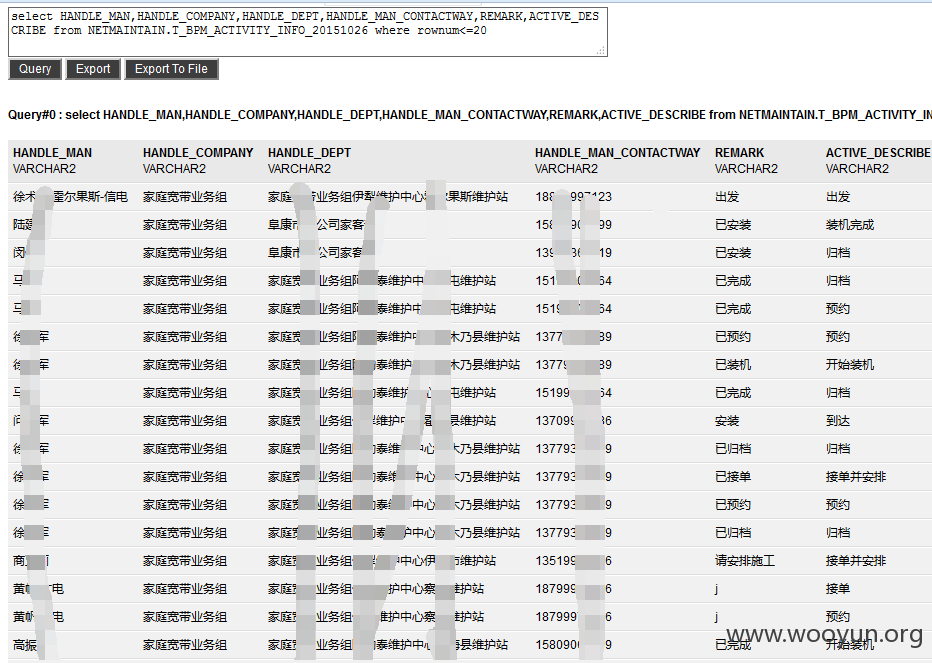
jdbc.password=Zsyw123NETMAINTAIN T_BPM_ACTIVITY_DEAL_INFO 64916789
MOMS PM_HW_CELL_TAIL_H 51478998
NETMAINTAIN WFACTIVITYINST 19809402
NETMAINTAIN WFTRANSCTRL 16898532
NETMAINTAIN WFTRANSITION 16568610
NETMAINTAIN WF_H_WIPARTICIPANT 8437504
NETMAINTAIN INSPECT_RESULT 8326646
NETMAINTAIN T_BPM_ACTIVITY_INFO 8290795
NETMAINTAIN MID_WIRELESS_PORT 4740206
NETMAINTAIN T_BPM_ACTIVITY_INFO_20151026 4485613
NETMAINTAIN T_WFD_RESSERVICE_MAIN20151215 3328686
MOMS ACTIVE_ALARM 3158766
NETMAINTAIN T_BNS_INTERFACE 2758440
NETMAINTAIN T_BPM_WORKITEM_LOCK 2453948
NETMAINTAIN WFPROCESSINST 2439538
ZSYW T_PLT_USE 2419992
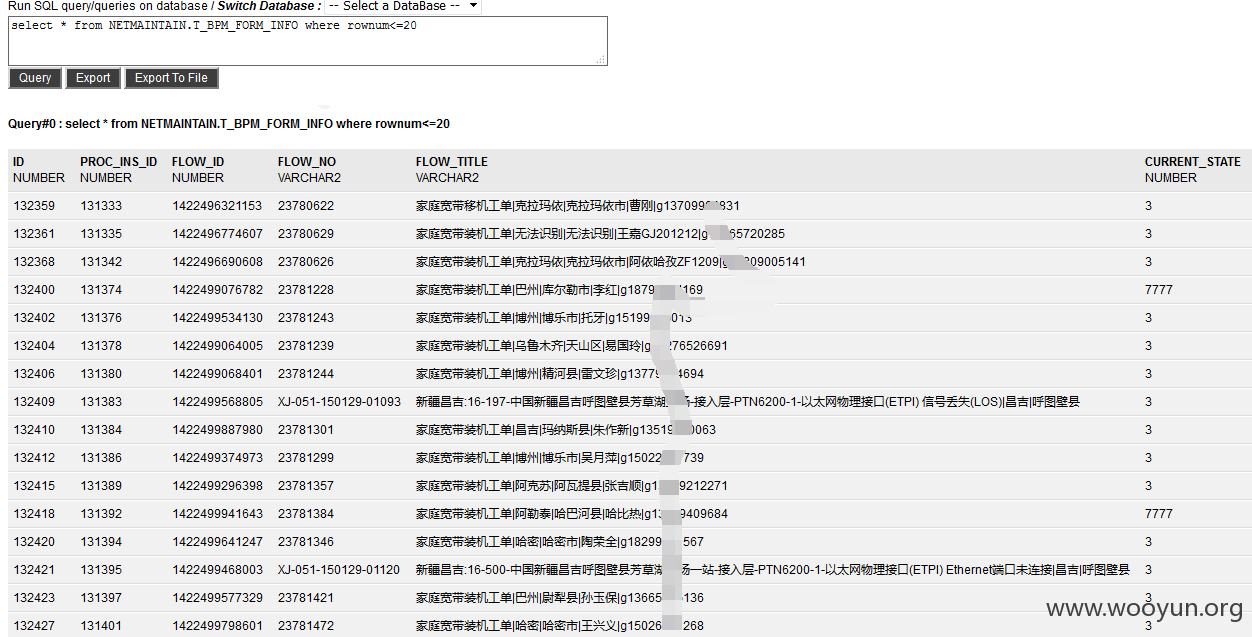
NETMAINTAIN T_BPM_FORM_INFO 2248617
NETMAINTAIN WFWORKITEM 2187745
NETMAINTAIN SMS_MT_TS_NATIVE 2107688
NETMAINTAIN RMS_GX_POLE 1965109
NETMAINTAIN MID_TOR_POLE 1950311
NETMAINTAIN RMS_GX_POLE_SEG 1940090
NETMAINTAIN MID_TOR_POLEWAY_SEG 1933907
NETMAINTAIN T_WFD_RESSERVICE_MAIN 1799087
ZSYW T_PLT_LOGIN 1688467
NETMAINTAIN T_BPM_INTERFACE_JKKT 1575787
NETMAINTAIN GIS_POSITION 1457468
NETMAINTAIN T_BPM_JKKT_TOEOMS_20151129 1405369
NETMAINTAIN WFWIPARTICIPANT 1300017
NETMAINTAIN T_BPM_JKKT_TOEOMS 1208564
NETMAINTAIN T_BPM_INTERDATA_4_MAIN 1203680
NETMAINTAIN T_BNS_JKKT 1201745
NETMAINTAIN T_BPM_FORM_REMIND 1170764
NETMAINTAIN TEMP_JKKT 1162456
NETMAINTAIN TEMP_JKKT_DAY 1092057
NETMAINTAIN SYS_OP_LOG 1055706
NETMAINTAIN COMPLAIN_ALARM 972869
漏洞证明:
NETMAINTAIN T_BPM_ACTIVITY_DEAL_INFO 64916789
MOMS PM_HW_CELL_TAIL_H 51478998
NETMAINTAIN WFACTIVITYINST 19809402
NETMAINTAIN WFTRANSCTRL 16898532
NETMAINTAIN WFTRANSITION 16568610
NETMAINTAIN WF_H_WIPARTICIPANT 8437504
NETMAINTAIN INSPECT_RESULT 8326646
NETMAINTAIN T_BPM_ACTIVITY_INFO 8290795
NETMAINTAIN MID_WIRELESS_PORT 4740206
NETMAINTAIN T_BPM_ACTIVITY_INFO_20151026 4485613
NETMAINTAIN T_WFD_RESSERVICE_MAIN20151215 3328686
MOMS ACTIVE_ALARM 3158766
NETMAINTAIN T_BNS_INTERFACE 2758440
NETMAINTAIN T_BPM_WORKITEM_LOCK 2453948
NETMAINTAIN WFPROCESSINST 2439538
ZSYW T_PLT_USE 2419992
NETMAINTAIN T_BPM_FORM_INFO 2248617
NETMAINTAIN WFWORKITEM 2187745
NETMAINTAIN SMS_MT_TS_NATIVE 2107688
NETMAINTAIN RMS_GX_POLE 1965109
NETMAINTAIN MID_TOR_POLE 1950311
NETMAINTAIN RMS_GX_POLE_SEG 1940090
NETMAINTAIN MID_TOR_POLEWAY_SEG 1933907
NETMAINTAIN T_WFD_RESSERVICE_MAIN 1799087
ZSYW T_PLT_LOGIN 1688467
NETMAINTAIN T_BPM_INTERFACE_JKKT 1575787
NETMAINTAIN GIS_POSITION 1457468
NETMAINTAIN T_BPM_JKKT_TOEOMS_20151129 1405369
NETMAINTAIN WFWIPARTICIPANT 1300017
NETMAINTAIN T_BPM_JKKT_TOEOMS 1208564
NETMAINTAIN T_BPM_INTERDATA_4_MAIN 1203680
NETMAINTAIN T_BNS_JKKT 1201745
NETMAINTAIN T_BPM_FORM_REMIND 1170764
NETMAINTAIN TEMP_JKKT 1162456
NETMAINTAIN TEMP_JKKT_DAY 1092057
NETMAINTAIN SYS_OP_LOG 1055706
NETMAINTAIN COMPLAIN_ALARM 972869
修复方案:
更新补丁
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:11
确认时间:2016-06-02 16:26
厂商回复:
CNVD确认并复现所述情况,已经转由CNCERT向中国移动集团公司通报,由其后续协调网站管理部门处置.
最新状态:
暂无