https://github.com/liuhaiween/devopsjumpserver/blob/ccb9acb139d83fc80aaf6ef4e5082bbb3690839f/jumpserver/settings.py
EMAIL_HOST='mail.yy.com'
30 EMAIL_PORT= 25
31 EMAIL_HOST_USER = '[email protected]'
32 EMAIL_HOST_PASSWORD = 'd00779d391617e6'
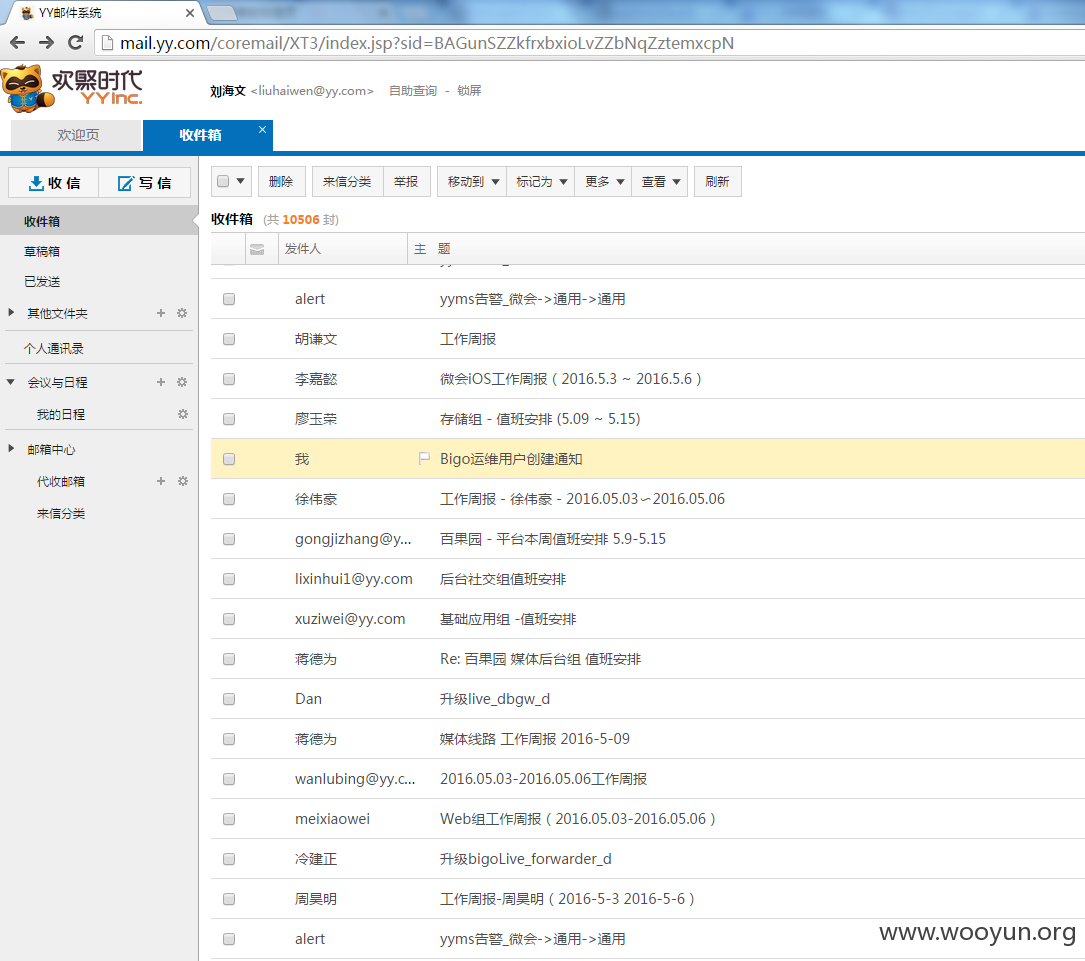
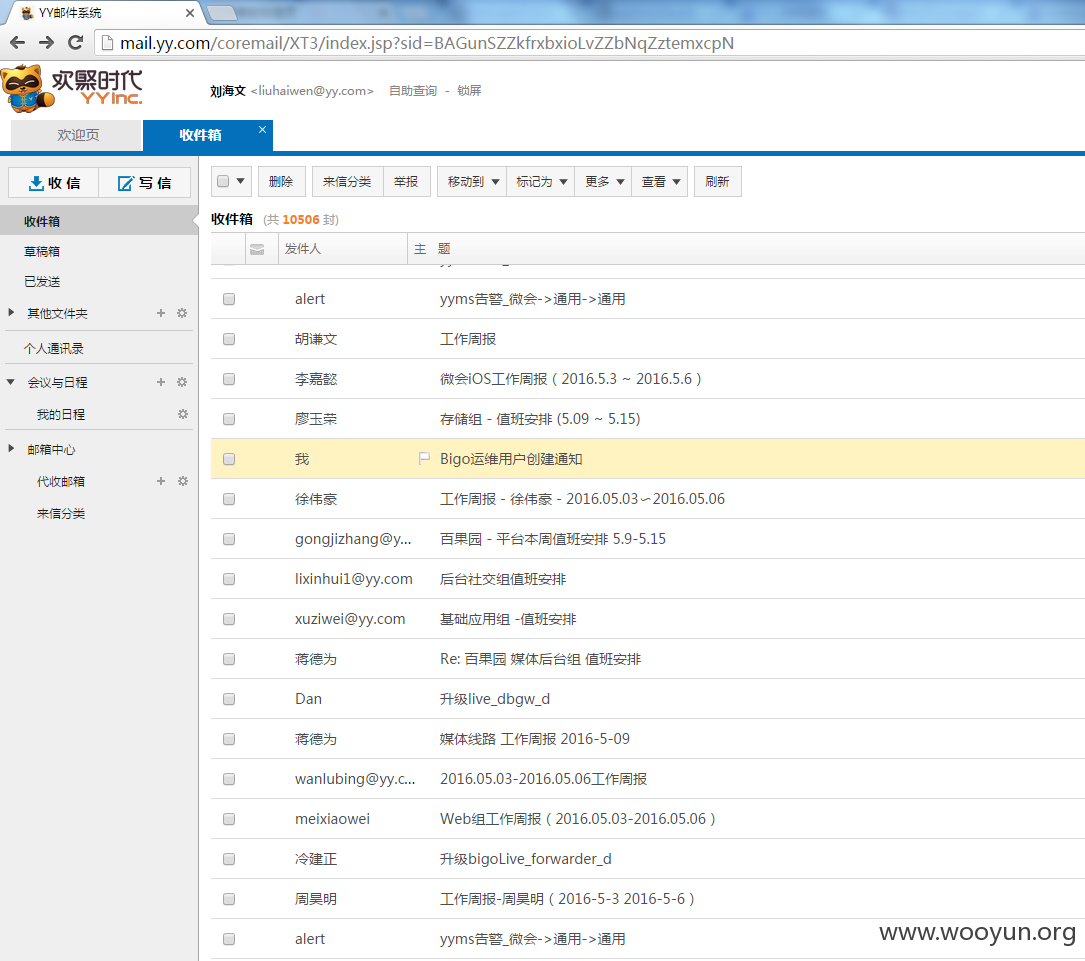
在里面发现了一封有意思的邮件
找了一个外网开放的zabbix 连上去
就不扫描了,可以轻松漫游内网
jumpserver

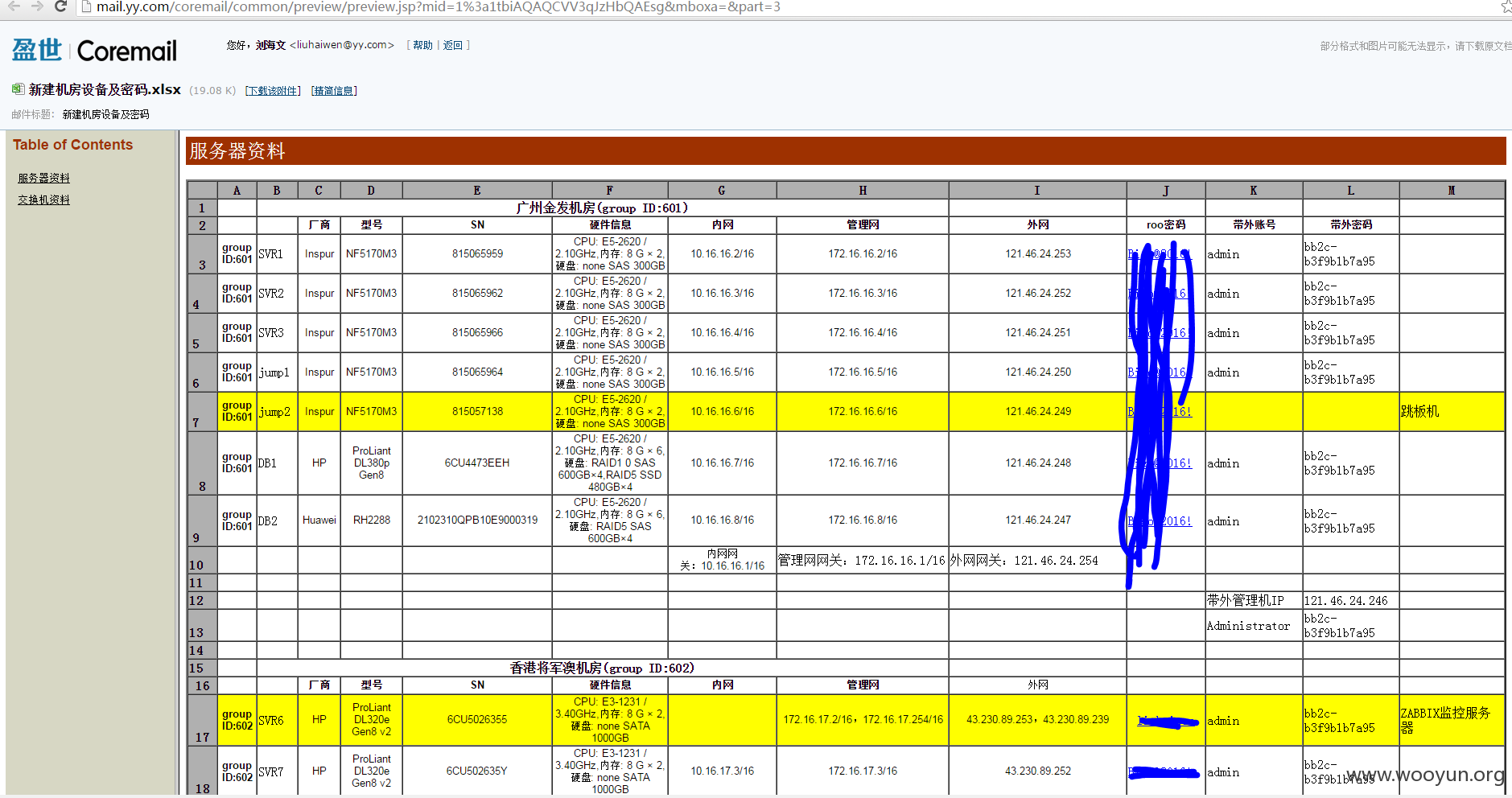
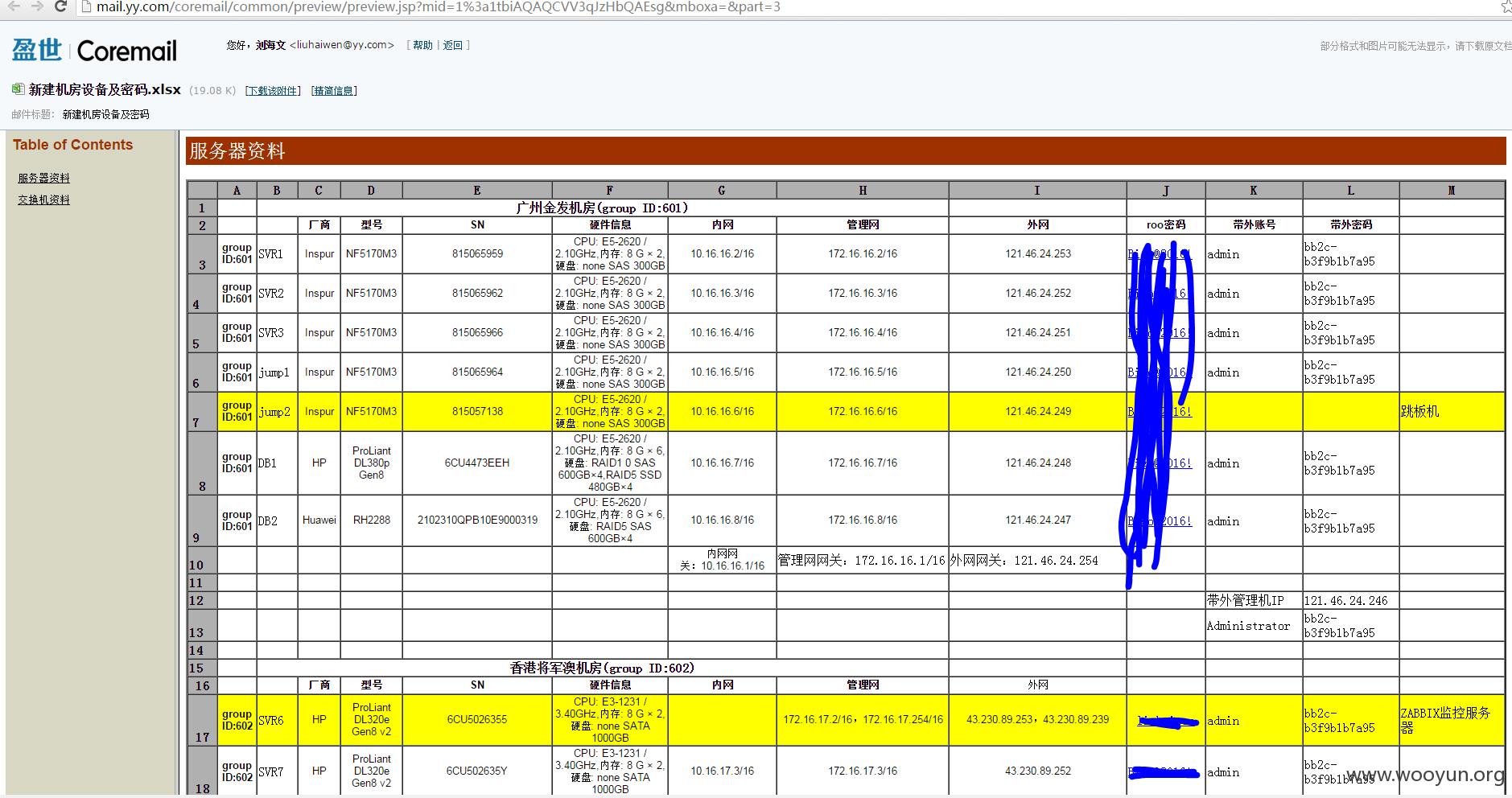
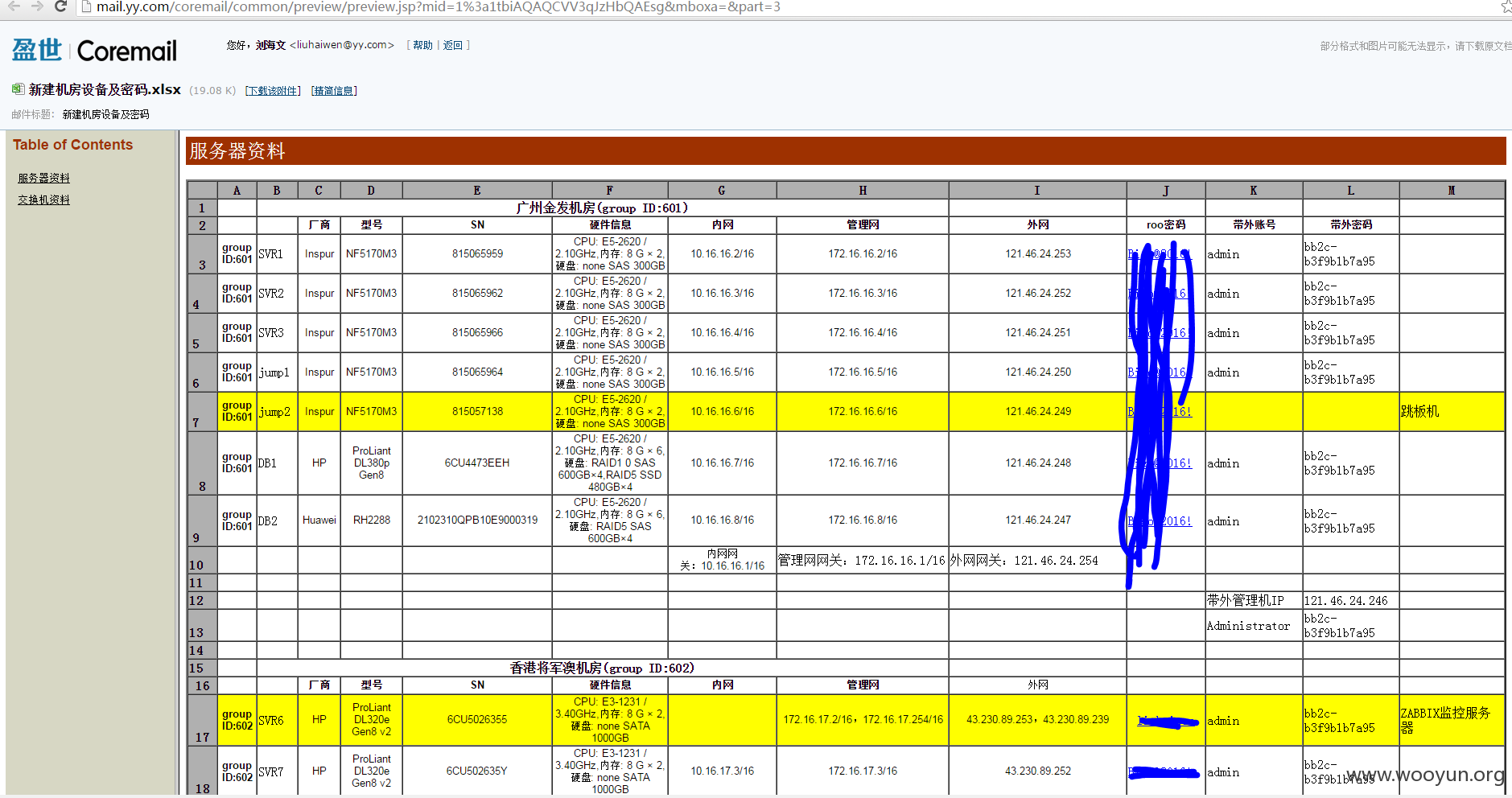
新机房交换机帐号密码
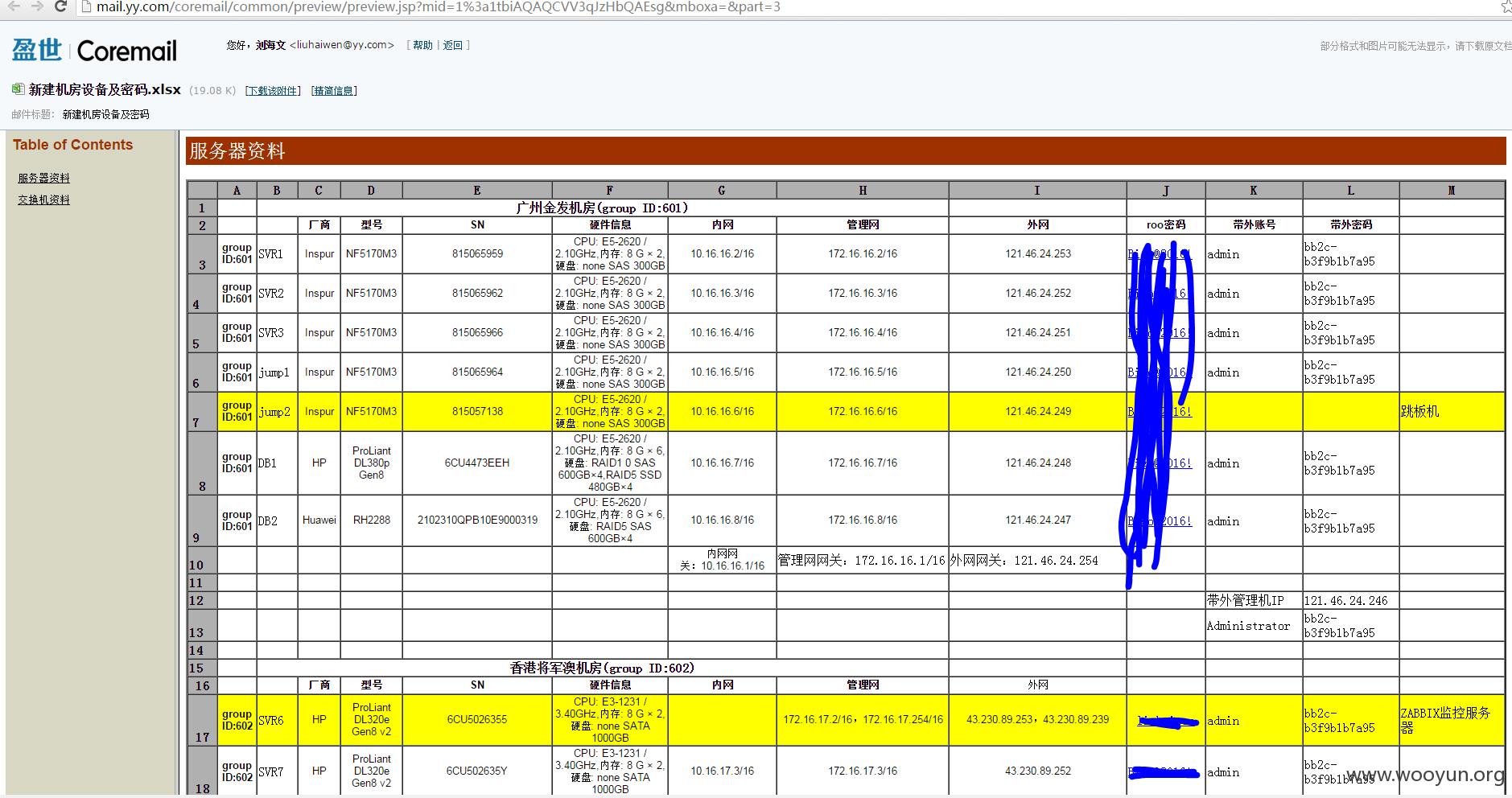
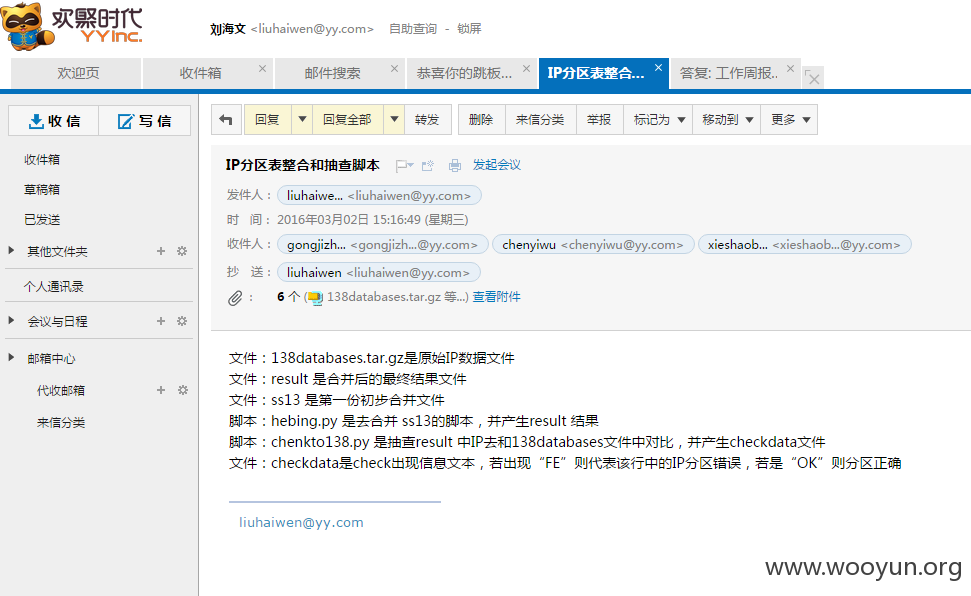
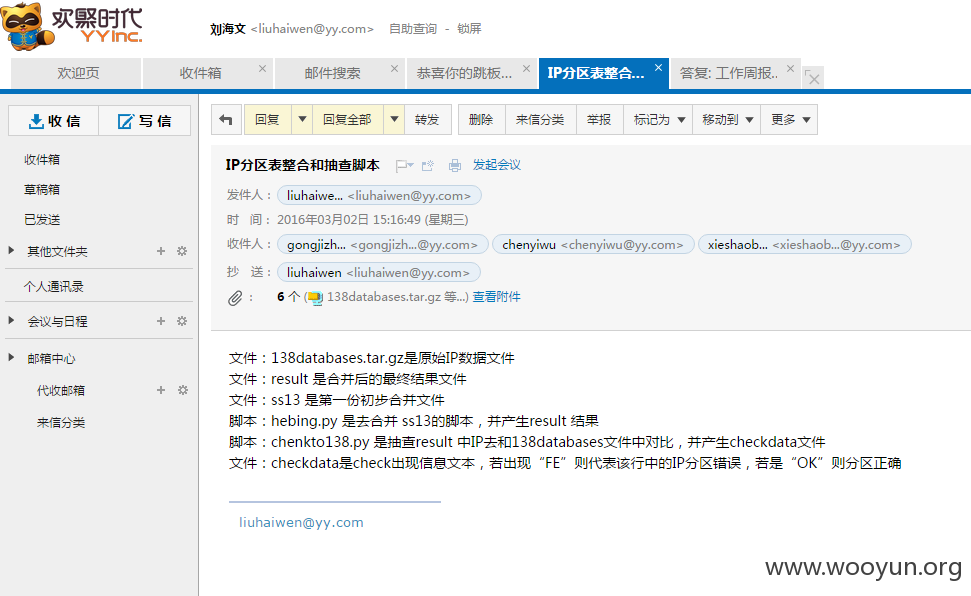
各类敏感信息

未做过多的深入