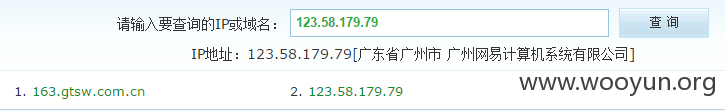
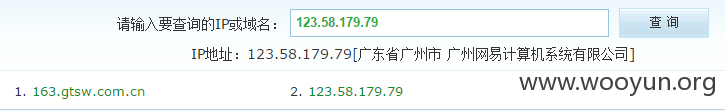
whois查询一下,证明此ip所属于网易
一个LNMP安装完成的界面
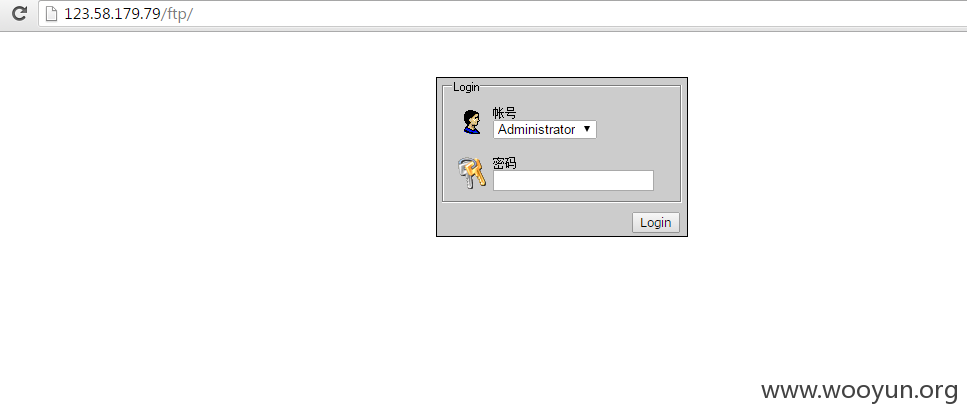
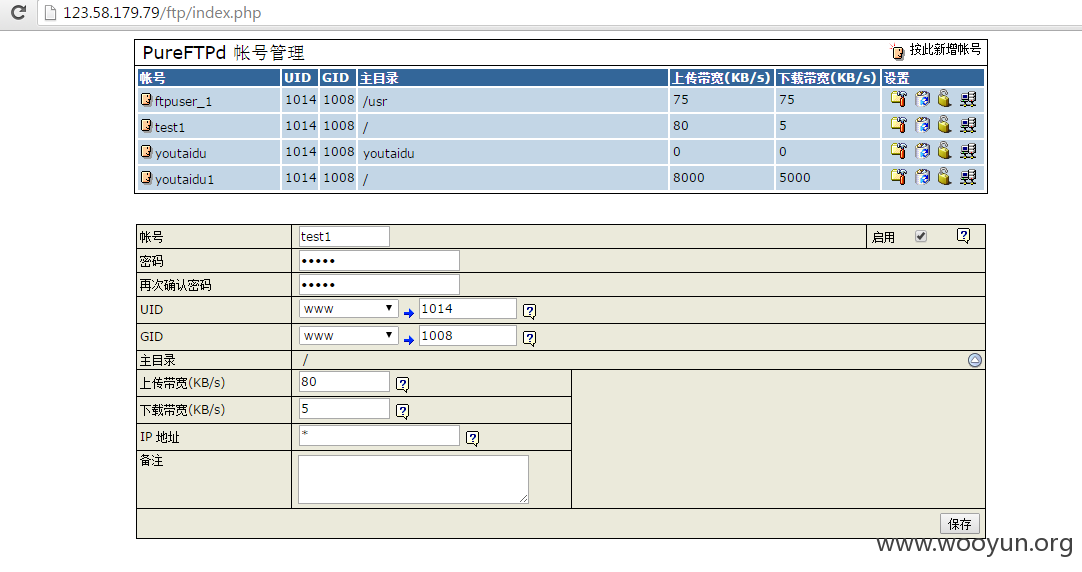
phpinfo和phpmyadmin界面被删除或被改名了,但是lnmp安装会有个pureftpd的选项。
访问看看
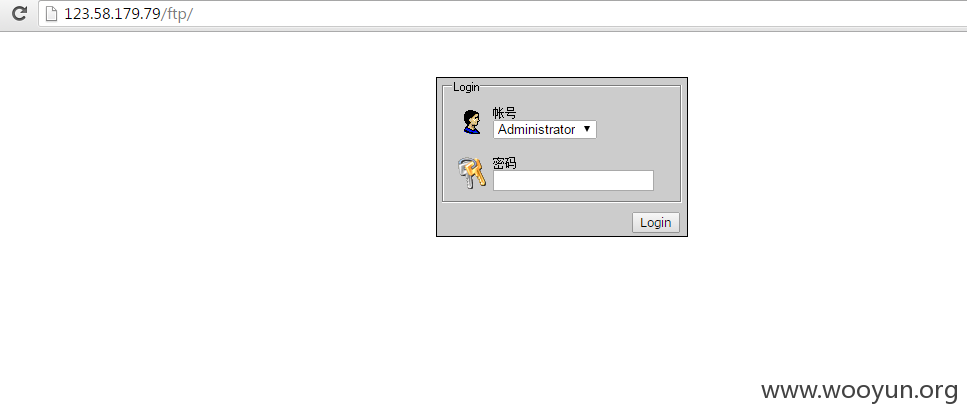
果然没删。
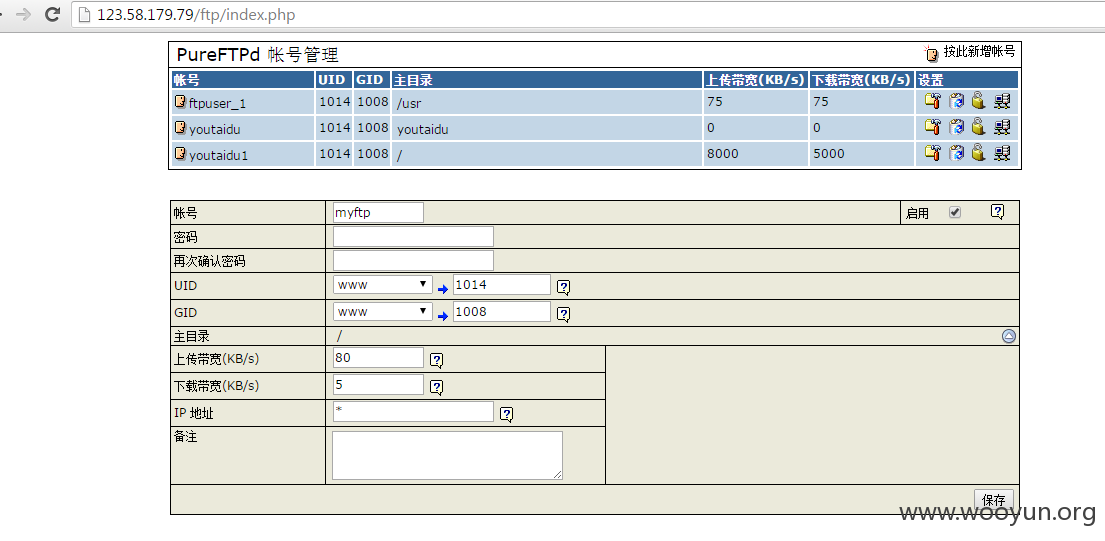
根据经验,这种一键安装的环境,大多都存在弱口令,遂尝试对pureftpd进行爆破。
果不其然,不出1分钟,密码出来了
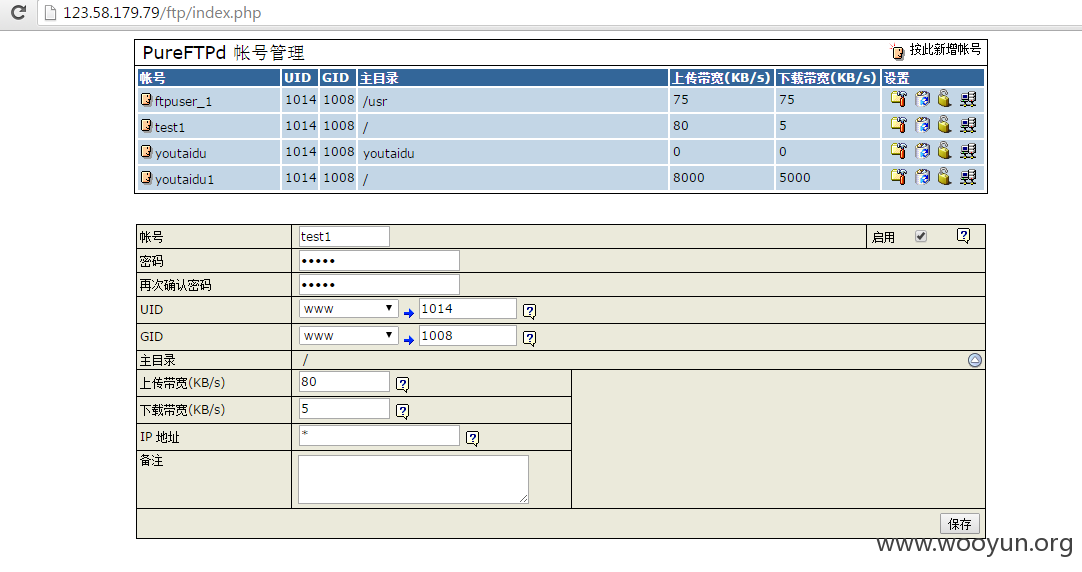
后来发现此密码通杀mysql和ssh。
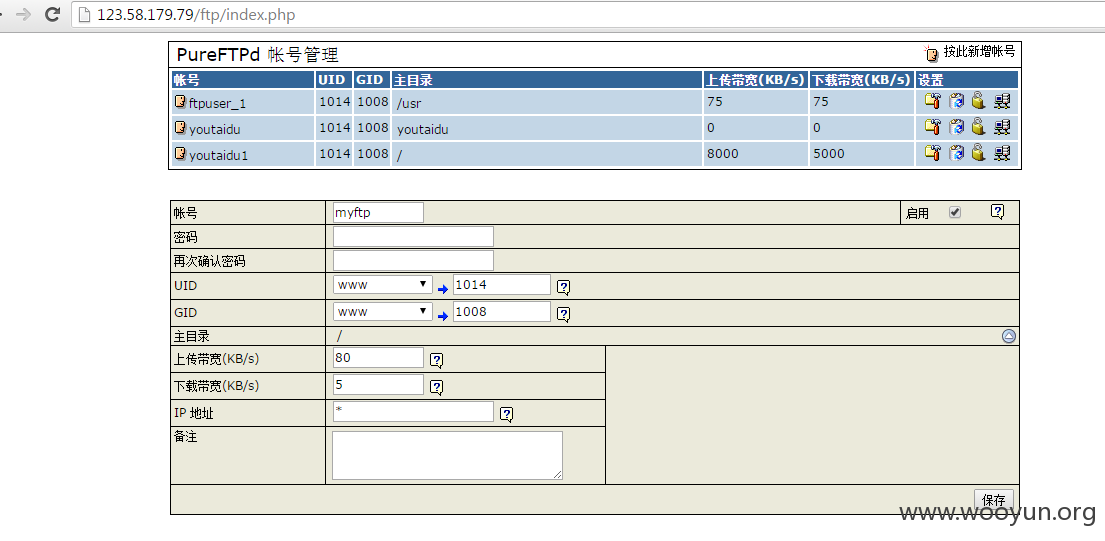
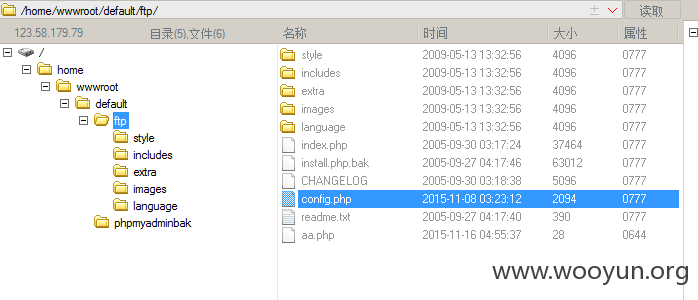
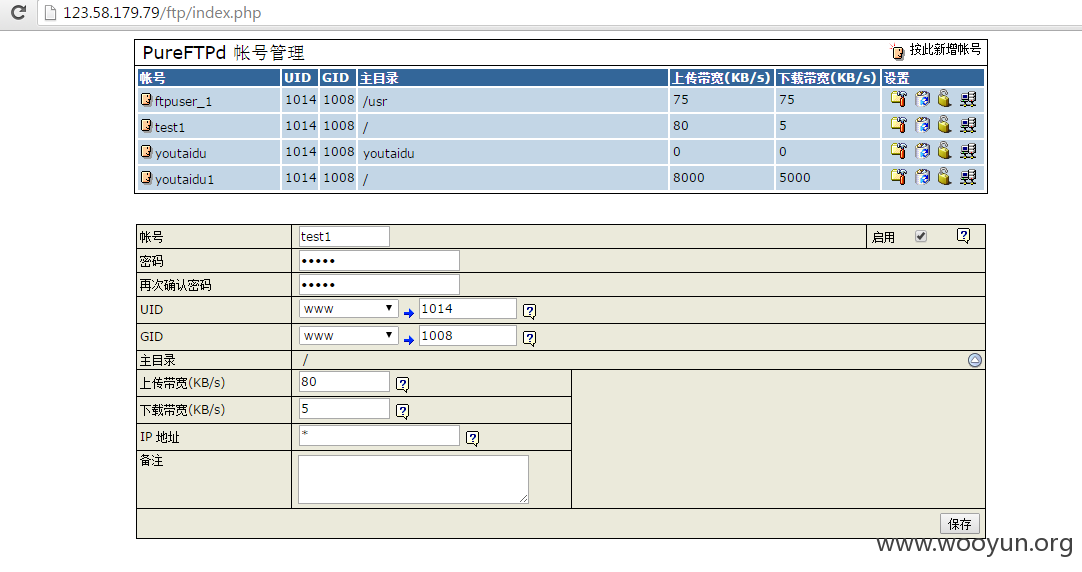
接下来就简单了,添加一个ftp帐号,通过ftp连接,上传shell。
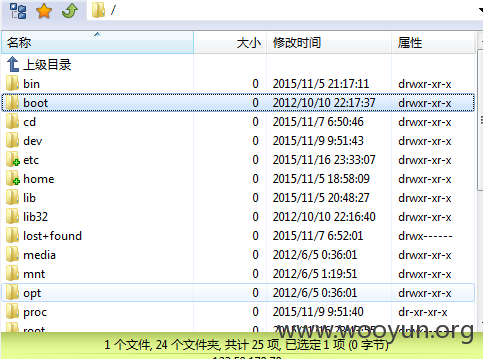
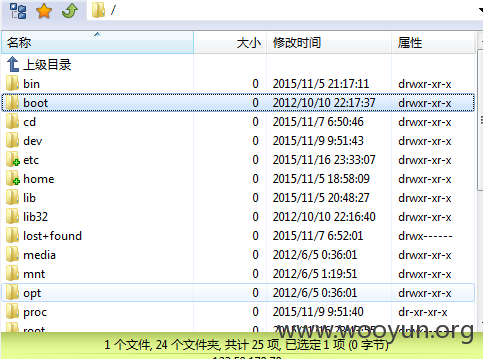
整个服务器的目录文件一目了然
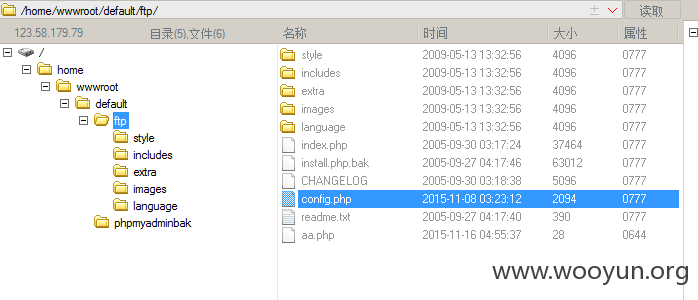
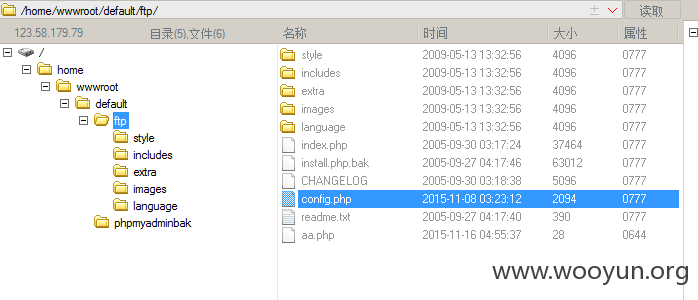
很快找到web目录,上传webshell
由于php安全模式,不允许直接执行命令,但是还有办法。
不过没那个必要,通过webshell查到mysql的密码,mysql密码与ssh密码相同,都是悲剧的qwer1234,通过此密码直接连接ssh。
ssh端口为8822
妥妥的内网
内网就不扫了
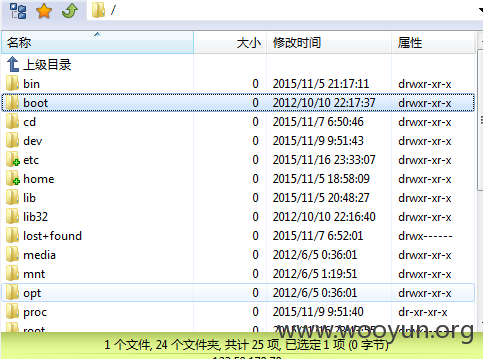
整个服务器的目录文件一目了然
很快找到web目录,上传webshell
妥妥的内网